

105 Latest Cyber Security Research Topics in 2024
Home Blog Security 105 Latest Cyber Security Research Topics in 2024
The concept of cybersecurity refers to cracking the security mechanisms that break in dynamic environments. Implementing Cyber Security Project topics and cybersecurity thesis topics helps overcome attacks and take mitigation approaches to security risks and threats in real-time. Undoubtedly, it focuses on events injected into the system, data, and the whole network to attack/disturb it.
The network can be attacked in various ways, including Distributed DoS, Knowledge Disruptions, Computer Viruses / Worms, and many more. Cyber-attacks are still rising, and more are waiting to harm their targeted systems and networks. Detecting Intrusions in cybersecurity has become challenging due to their Intelligence Performance. Therefore, it may negatively affect data integrity, privacy, availability, and security.
This article aims to demonstrate the most current Cyber Security Research Topics for Projects and areas of research currently lacking. We will talk about cyber security research questions, cyber security topics for the project, latest research titles about cyber security.
List of Trending Cyber Security Research Topics in 2024
Digital technology has revolutionized how all businesses, large or small, work, and even governments manage their day-to-day activities, requiring organizations, corporations, and government agencies to utilize computerized systems. To protect data against online attacks or unauthorized access, cybersecurity is a priority. There are many Cyber Security Courses online where you can learn about these topics. With the rapid development of technology comes an equally rapid shift in Cyber Security Research Topics and cybersecurity trends, as data breaches, ransomware, and hacks become almost routine news items. In 2024, these will be the top cybersecurity trends .
A. Exciting Mobile Cyber Security Research Paper Topics
- The significance of continuous user authentication on mobile gadgets.
- The efficacy of different mobile security approaches.
- Detecting mobile phone hacking.
- Assessing the threat of using portable devices to access banking services.
- Cybersecurity and mobile applications.
- The vulnerabilities in wireless mobile data exchange.
- The rise of mobile malware.
- The evolution of Android malware.
- How to know you’ve been hacked on mobile.
- The impact of mobile gadgets on cybersecurity.
B. Top Computer and Software Security Topics to Research
- Learn algorithms for data encryption
- Concept of risk management security
- How to develop the best Internet security software
- What are Encrypting Viruses- How does it work?
- How does a Ransomware attack work?
- Scanning of malware on your PC
- Infiltrating a Mac OS X operating system
- What are the effects of RSA on network security ?
- How do encrypting viruses work?
- DDoS attacks on IoT devices
C. Trending Information Security Research Topics
- Why should people avoid sharing their details on Facebook?
- What is the importance of unified user profiles?
- Discuss Cookies and Privacy
- White hat and black hat hackers
- What are the most secure methods for ensuring data integrity?
- Talk about the implications of Wi-Fi hacking apps on mobile phones
- Analyze the data breaches in 2024
- Discuss digital piracy in 2024
- critical cyber-attack concepts
- Social engineering and its importance
D. Current Network Security Research Topics
- Data storage centralization
- Identify Malicious activity on a computer system.
- Firewall
- Importance of keeping updated Software
- wireless sensor network
- What are the effects of ad-hoc networks
- How can a company network be safe?
- What are Network segmentation and its applications?
- Discuss Data Loss Prevention systems
- Discuss various methods for establishing secure algorithms in a network.
- Talk about two-factor authentication
E. Best Data Security Research Topics
- Importance of backup and recovery
- Benefits of logging for applications
- Understand physical data security
- Importance of Cloud Security
- In computing, the relationship between privacy and data security
- Talk about data leaks in mobile apps
- Discuss the effects of a black hole on a network system.
F. Important Application Security Research Topics
- Detect Malicious Activity on Google Play Apps
- Dangers of XSS attacks on apps
- Discuss SQL injection attacks.
- Insecure Deserialization Effect
- Check Security protocols
G. Cybersecurity Law & Ethics Research Topics
- Strict cybersecurity laws in China
- Importance of the Cybersecurity Information Sharing Act.
- USA, UK, and other countries' cybersecurity laws
- Discuss The Pipeline Security Act in the United States
H. Recent Cyberbullying Topics
- Protecting your Online Identity and Reputation
- Online Safety
- Sexual Harassment and Sexual Bullying
- Dealing with Bullying
- Stress Center for Teens
I. Operational Security Topics
- Identify sensitive data
- Identify possible threats
- Analyze security threats and vulnerabilities
- Appraise the threat level and vulnerability risk
- Devise a plan to mitigate the threats
J. Cybercrime Topics for a Research Paper
- Crime Prevention.
- Criminal Specialization.
- Drug Courts.
- Criminal Courts.
- Criminal Justice Ethics.
- Capital Punishment.
- Community Corrections.
- Criminal Law.
Cyber Security Future Research Topics
- Developing more effective methods for detecting and responding to cyber attacks
- Investigating the role of social media in cyber security
- Examining the impact of cloud computing on cyber security
- Investigating the security implications of the Internet of Things
- Studying the effectiveness of current cyber security measures
- Identifying new cyber security threats and vulnerabilities
- Developing more effective cyber security policies
- Examining the ethical implications of cyber security
Cyber Security Topics For Research Paper
- Cyber security threats and vulnerabilities
- Cyber security incident response and management
- Cyber security risk management
- Cyber security awareness and training
- Cyber security controls and countermeasures
- Cyber security governance
- Cyber security standards
- Cyber security insurance
Top 5 Current Research Topics in Cybersecurity
Below are the latest 5 cybersecurity research topics. They are:
- Artificial Intelligence
- Digital Supply Chains
- Internet of Things
- State-Sponsored Attacks
- Working From Home
Research Area in Cyber Security
The field of cyber security is extensive and constantly evolving. Its research covers a wide range of subjects, including:
- Quantum & Space
- Data Privacy
- Criminology & Law
- AI & IoT Security
- RFID Security
- Authorization Infrastructure
- Digital Forensics
- Autonomous Security
- Social Influence on Social Networks
How to Choose the Best Research Topics in Cyber Security?
A good cybersecurity assignment heading is a skill that not everyone has, and unfortunately, not everyone has one. You might have your teacher provide you with the topics, or you might be asked to come up with your own. If you want more cyber security research topics, you can take references from Certified Ethical Hacker Certification, where you will get more hints on new topics. If you don't know where to start, here are some tips. Follow them to create compelling cybersecurity assignment topics.
1. Brainstorm
In order to select the most appropriate heading for your cybersecurity assignment, you first need to brainstorm ideas. What specific matter do you wish to explore? In this case, come up with relevant topics about the subject and select those relevant to your issue when you use our list of topics. You can also go to cyber security-oriented websites to get some ideas. Using any blog post on the internet can prove helpful if you intend to write a research paper on security threats in 2024. Creating a brainstorming list with all the keywords and cybersecurity concepts you wish to discuss is another great way to start. Once that's done, pick the topics you feel most comfortable handling. Keep in mind to stay away from common topics as much as possible.
2. Understanding the Background
In order to write a cybersecurity assignment, you need to identify two or three research paper topics. Obtain the necessary resources and review them to gain background information on your heading. This will also allow you to learn new terminologies that can be used in your title to enhance it.
3. Write a Single Topic
Make sure the subject of your cybersecurity research paper doesn't fall into either extreme. Make sure the title is neither too narrow nor too broad. Topics on either extreme will be challenging to research and write about.
4. Be Flexible
There is no rule to say that the title you choose is permanent. It is perfectly okay to change your research paper topic along the way. For example, if you find another topic on this list to better suit your research paper, consider swapping it out.
The Layout of Cybersecurity Research Guidance
It is undeniable that usability is one of cybersecurity's most important social issues today. Increasingly, security features have become standard components of our digital environment, which pervade our lives and require both novices and experts to use them. Supported by confidentiality, integrity, and availability concerns, security features have become essential components of our digital environment.
In order to make security features easily accessible to a wider population, these functions need to be highly usable. This is especially true in this context because poor usability typically translates into the inadequate application of cybersecurity tools and functionality, resulting in their limited effectiveness.
Cyber Security Research Topic Writing Tips from Expert
Additionally, a well-planned action plan and a set of useful tools are essential for delving into Cyber Security research topics. Not only do these topics present a vast realm of knowledge and potential innovation, but they also have paramount importance in today's digital age. Addressing the challenges and nuances of these research areas will contribute significantly to the global cybersecurity landscape, ensuring safer digital environments for all. It's crucial to approach these topics with diligence and an open mind to uncover groundbreaking insights.
- Before you begin writing your research paper, make sure you understand the assignment.
- Your Research Paper Should Have an Engaging Topic
- Find reputable sources by doing a little research
- Precisely state your thesis on cybersecurity
- A rough outline should be developed
- Finish your paper by writing a draft
- Make sure that your bibliography is formatted correctly and cites your sources.
Discover the Power of ITIL 4 Foundation - Unleash the Potential of Your Business with this Cost-Effective Solution. Boost Efficiency, Streamline Processes, and Stay Ahead of the Competition. Learn More!
Studies in the literature have identified and recommended guidelines and recommendations for addressing security usability problems to provide highly usable security. The purpose of such papers is to consolidate existing design guidelines and define an initial core list that can be used for future reference in the field of Cyber Security Research Topics.
The researcher takes advantage of the opportunity to provide an up-to-date analysis of cybersecurity usability issues and evaluation techniques applied so far. As a result of this research paper, researchers and practitioners interested in cybersecurity systems who value human and social design elements are likely to find it useful. You can find KnowledgeHut’s Cyber Security courses online and take maximum advantage of them.
Frequently Asked Questions (FAQs)
Businesses and individuals are changing how they handle cybersecurity as technology changes rapidly - from cloud-based services to new IoT devices.
Ideally, you should have read many papers and know their structure, what information they contain, and so on if you want to write something of interest to others.
Inmates having the right to work, transportation of concealed weapons, rape and violence in prison, verdicts on plea agreements, rehab versus reform, and how reliable are eyewitnesses?
The field of cyber security is extensive and constantly evolving. Its research covers various subjects, including Quantum & Space, Data Privacy, Criminology & Law, and AI & IoT Security.

Mrinal Prakash
I am a B.Tech Student who blogs about various topics on cyber security and is specialized in web application security
Avail your free 1:1 mentorship session.
Something went wrong
Upcoming Cyber Security Batches & Dates
| Name | Date | Fee | Know more |
|---|
- Privacy Policy

Home » 500+ Cyber Security Research Topics
500+ Cyber Security Research Topics

Cybersecurity has become an increasingly important topic in recent years as more and more of our lives are spent online. With the rise of the digital age, there has been a corresponding increase in the number and severity of cyber attacks. As such, research into cybersecurity has become critical in order to protect individuals, businesses, and governments from these threats. In this blog post, we will explore some of the most pressing cybersecurity research topics, from the latest trends in cyber attacks to emerging technologies that can help prevent them. Whether you are a cybersecurity professional, a Master’s or Ph.D. student, or simply interested in the field, this post will provide valuable insights into the challenges and opportunities in this rapidly evolving area of study.
Cyber Security Research Topics
Cyber Security Research Topics are as follows:
- The role of machine learning in detecting cyber threats
- The impact of cloud computing on cyber security
- Cyber warfare and its effects on national security
- The rise of ransomware attacks and their prevention methods
- Evaluating the effectiveness of network intrusion detection systems
- The use of blockchain technology in enhancing cyber security
- Investigating the role of cyber security in protecting critical infrastructure
- The ethics of hacking and its implications for cyber security professionals
- Developing a secure software development lifecycle (SSDLC)
- The role of artificial intelligence in cyber security
- Evaluating the effectiveness of multi-factor authentication
- Investigating the impact of social engineering on cyber security
- The role of cyber insurance in mitigating cyber risks
- Developing secure IoT (Internet of Things) systems
- Investigating the challenges of cyber security in the healthcare industry
- Evaluating the effectiveness of penetration testing
- Investigating the impact of big data on cyber security
- The role of quantum computing in breaking current encryption methods
- Developing a secure BYOD (Bring Your Own Device) policy
- The impact of cyber security breaches on a company’s reputation
- The role of cyber security in protecting financial transactions
- Evaluating the effectiveness of anti-virus software
- The use of biometrics in enhancing cyber security
- Investigating the impact of cyber security on the supply chain
- The role of cyber security in protecting personal privacy
- Developing a secure cloud storage system
- Evaluating the effectiveness of firewall technologies
- Investigating the impact of cyber security on e-commerce
- The role of cyber security in protecting intellectual property
- Developing a secure remote access policy
- Investigating the challenges of securing mobile devices
- The role of cyber security in protecting government agencies
- Evaluating the effectiveness of cyber security training programs
- Investigating the impact of cyber security on the aviation industry
- The role of cyber security in protecting online gaming platforms
- Developing a secure password management system
- Investigating the challenges of securing smart homes
- The impact of cyber security on the automotive industry
- The role of cyber security in protecting social media platforms
- Developing a secure email system
- Evaluating the effectiveness of encryption methods
- Investigating the impact of cyber security on the hospitality industry
- The role of cyber security in protecting online education platforms
- Developing a secure backup and recovery strategy
- Investigating the challenges of securing virtual environments
- The impact of cyber security on the energy sector
- The role of cyber security in protecting online voting systems
- Developing a secure chat platform
- Investigating the impact of cyber security on the entertainment industry
- The role of cyber security in protecting online dating platforms
- Artificial Intelligence and Machine Learning in Cybersecurity
- Quantum Cryptography and Post-Quantum Cryptography
- Internet of Things (IoT) Security
- Developing a framework for cyber resilience in critical infrastructure
- Understanding the fundamentals of encryption algorithms
- Cyber security challenges for small and medium-sized businesses
- Developing secure coding practices for web applications
- Investigating the role of cyber security in protecting online privacy
- Network security protocols and their importance
- Social engineering attacks and how to prevent them
- Investigating the challenges of securing personal devices and home networks
- Developing a basic incident response plan for cyber attacks
- The impact of cyber security on the financial sector
- Understanding the role of cyber security in protecting critical infrastructure
- Mobile device security and common vulnerabilities
- Investigating the challenges of securing cloud-based systems
- Cyber security and the Internet of Things (IoT)
- Biometric authentication and its role in cyber security
- Developing secure communication protocols for online messaging platforms
- The importance of cyber security in e-commerce
- Understanding the threats and vulnerabilities associated with social media platforms
- Investigating the role of cyber security in protecting intellectual property
- The basics of malware analysis and detection
- Developing a basic cyber security awareness training program
- Understanding the threats and vulnerabilities associated with public Wi-Fi networks
- Investigating the challenges of securing online banking systems
- The importance of password management and best practices
- Cyber security and cloud computing
- Understanding the role of cyber security in protecting national security
- Investigating the challenges of securing online gaming platforms
- The basics of cyber threat intelligence
- Developing secure authentication mechanisms for online services
- The impact of cyber security on the healthcare sector
- Understanding the basics of digital forensics
- Investigating the challenges of securing smart home devices
- The role of cyber security in protecting against cyberbullying
- Developing secure file transfer protocols for sensitive information
- Understanding the challenges of securing remote work environments
- Investigating the role of cyber security in protecting against identity theft
- The basics of network intrusion detection and prevention systems
- Developing secure payment processing systems
- Understanding the role of cyber security in protecting against ransomware attacks
- Investigating the challenges of securing public transportation systems
- The basics of network segmentation and its importance in cyber security
- Developing secure user access management systems
- Understanding the challenges of securing supply chain networks
- The role of cyber security in protecting against cyber espionage
- Investigating the challenges of securing online educational platforms
- The importance of data backup and disaster recovery planning
- Developing secure email communication protocols
- Understanding the basics of threat modeling and risk assessment
- Investigating the challenges of securing online voting systems
- The role of cyber security in protecting against cyber terrorism
- Developing secure remote access protocols for corporate networks.
- Investigating the challenges of securing artificial intelligence systems
- The role of machine learning in enhancing cyber threat intelligence
- Evaluating the effectiveness of deception technologies in cyber security
- Investigating the impact of cyber security on the adoption of emerging technologies
- The role of cyber security in protecting smart cities
- Developing a risk-based approach to cyber security governance
- Investigating the impact of cyber security on economic growth and innovation
- The role of cyber security in protecting human rights in the digital age
- Developing a secure digital identity system
- Investigating the impact of cyber security on global political stability
- The role of cyber security in protecting the Internet of Things (IoT)
- Developing a secure supply chain management system
- Investigating the challenges of securing cloud-native applications
- The role of cyber security in protecting against insider threats
- Developing a secure software-defined network (SDN)
- Investigating the impact of cyber security on the adoption of mobile payments
- The role of cyber security in protecting against cyber warfare
- Developing a secure distributed ledger technology (DLT) system
- Investigating the impact of cyber security on the digital divide
- The role of cyber security in protecting against state-sponsored attacks
- Developing a secure Internet infrastructure
- Investigating the challenges of securing industrial control systems (ICS)
- Developing a secure quantum communication system
- Investigating the impact of cyber security on global trade and commerce
- Developing a secure decentralized authentication system
- Investigating the challenges of securing edge computing systems
- Developing a secure hybrid cloud system
- Investigating the impact of cyber security on the adoption of smart cities
- The role of cyber security in protecting against cyber propaganda
- Developing a secure blockchain-based voting system
- Investigating the challenges of securing cyber-physical systems (CPS)
- The role of cyber security in protecting against cyber hate speech
- Developing a secure machine learning system
- Investigating the impact of cyber security on the adoption of autonomous vehicles
- The role of cyber security in protecting against cyber stalking
- Developing a secure data-driven decision-making system
- Investigating the challenges of securing social media platforms
- The role of cyber security in protecting against cyberbullying in schools
- Developing a secure open source software ecosystem
- Investigating the impact of cyber security on the adoption of smart homes
- The role of cyber security in protecting against cyber fraud
- Developing a secure software supply chain
- Investigating the challenges of securing cloud-based healthcare systems
- The role of cyber security in protecting against cyber harassment
- Developing a secure multi-party computation system
- Investigating the impact of cyber security on the adoption of virtual and augmented reality technologies.
- Cybersecurity in Cloud Computing Environments
- Cyber Threat Intelligence and Analysis
- Blockchain Security
- Data Privacy and Protection
- Cybersecurity in Industrial Control Systems
- Mobile Device Security
- The importance of cyber security in the digital age
- The ethics of cyber security and privacy
- The role of government in regulating cyber security
- Cyber security threats and vulnerabilities in the healthcare sector
- Understanding the risks associated with social media and cyber security
- The impact of cyber security on e-commerce
- The effectiveness of cyber security awareness training programs
- The role of biometric authentication in cyber security
- The importance of password management in cyber security
- The basics of network security protocols and their importance
- The challenges of securing online gaming platforms
- The role of cyber security in protecting national security
- The impact of cyber security on the legal sector
- The ethics of cyber warfare
- The challenges of securing the Internet of Things (IoT)
- Understanding the basics of malware analysis and detection
- The challenges of securing public transportation systems
- The impact of cyber security on the insurance industry
- The role of cyber security in protecting against ransomware attacks
- The challenges of securing remote work environments
- Understanding the threats and vulnerabilities associated with social engineering attacks
- The impact of cyber security on the education sector
- Investigating the challenges of securing supply chain networks
- The challenges of securing personal devices and home networks
- The importance of secure coding practices for web applications
- The impact of cyber security on the hospitality industry
- The role of cyber security in protecting against identity theft
- The challenges of securing public Wi-Fi networks
- The importance of cyber security in protecting critical infrastructure
- The challenges of securing cloud-based storage systems
- The effectiveness of antivirus software in cyber security
- Developing secure payment processing systems.
- Cybersecurity in Healthcare
- Social Engineering and Phishing Attacks
- Cybersecurity in Autonomous Vehicles
- Cybersecurity in Smart Cities
- Cybersecurity Risk Assessment and Management
- Malware Analysis and Detection Techniques
- Cybersecurity in the Financial Sector
- Cybersecurity in Government Agencies
- Cybersecurity and Artificial Life
- Cybersecurity for Critical Infrastructure Protection
- Cybersecurity in the Education Sector
- Cybersecurity in Virtual Reality and Augmented Reality
- Cybersecurity in the Retail Industry
- Cryptocurrency Security
- Cybersecurity in Supply Chain Management
- Cybersecurity and Human Factors
- Cybersecurity in the Transportation Industry
- Cybersecurity in Gaming Environments
- Cybersecurity in Social Media Platforms
- Cybersecurity and Biometrics
- Cybersecurity and Quantum Computing
- Cybersecurity in 5G Networks
- Cybersecurity in Aviation and Aerospace Industry
- Cybersecurity in Agriculture Industry
- Cybersecurity in Space Exploration
- Cybersecurity in Military Operations
- Cybersecurity and Cloud Storage
- Cybersecurity in Software-Defined Networks
- Cybersecurity and Artificial Intelligence Ethics
- Cybersecurity and Cyber Insurance
- Cybersecurity in the Legal Industry
- Cybersecurity and Data Science
- Cybersecurity in Energy Systems
- Cybersecurity in E-commerce
- Cybersecurity in Identity Management
- Cybersecurity in Small and Medium Enterprises
- Cybersecurity in the Entertainment Industry
- Cybersecurity and the Internet of Medical Things
- Cybersecurity and the Dark Web
- Cybersecurity and Wearable Technology
- Cybersecurity in Public Safety Systems.
- Threat Intelligence for Industrial Control Systems
- Privacy Preservation in Cloud Computing
- Network Security for Critical Infrastructure
- Cryptographic Techniques for Blockchain Security
- Malware Detection and Analysis
- Cyber Threat Hunting Techniques
- Cybersecurity Risk Assessment
- Machine Learning for Cybersecurity
- Cybersecurity in Financial Institutions
- Cybersecurity for Smart Cities
- Cybersecurity in Aviation
- Cybersecurity in the Automotive Industry
- Cybersecurity in the Energy Sector
- Cybersecurity in Telecommunications
- Cybersecurity for Mobile Devices
- Biometric Authentication for Cybersecurity
- Cybersecurity for Artificial Intelligence
- Cybersecurity for Social Media Platforms
- Cybersecurity in the Gaming Industry
- Cybersecurity in the Defense Industry
- Cybersecurity for Autonomous Systems
- Cybersecurity for Quantum Computing
- Cybersecurity for Augmented Reality and Virtual Reality
- Cybersecurity in Cloud-Native Applications
- Cybersecurity for Smart Grids
- Cybersecurity in Distributed Ledger Technology
- Cybersecurity for Next-Generation Wireless Networks
- Cybersecurity for Digital Identity Management
- Cybersecurity for Open Source Software
- Cybersecurity for Smart Homes
- Cybersecurity for Smart Transportation Systems
- Cybersecurity for Cyber Physical Systems
- Cybersecurity for Critical National Infrastructure
- Cybersecurity for Smart Agriculture
- Cybersecurity for Retail Industry
- Cybersecurity for Digital Twins
- Cybersecurity for Quantum Key Distribution
- Cybersecurity for Digital Healthcare
- Cybersecurity for Smart Logistics
- Cybersecurity for Wearable Devices
- Cybersecurity for Edge Computing
- Cybersecurity for Cognitive Computing
- Cybersecurity for Industrial IoT
- Cybersecurity for Intelligent Transportation Systems
- Cybersecurity for Smart Water Management Systems
- The rise of cyber terrorism and its impact on national security
- The impact of artificial intelligence on cyber security
- Analyzing the effectiveness of biometric authentication for securing data
- The impact of social media on cyber security and privacy
- The future of cyber security in the Internet of Things (IoT) era
- The role of machine learning in detecting and preventing cyber attacks
- The effectiveness of encryption in securing sensitive data
- The impact of quantum computing on cyber security
- The rise of cyber bullying and its effects on mental health
- Investigating cyber espionage and its impact on national security
- The effectiveness of cyber insurance in mitigating cyber risks
- The role of blockchain technology in cyber security
- Investigating the effectiveness of cyber security awareness training programs
- The impact of cyber attacks on critical infrastructure
- Analyzing the effectiveness of firewalls in protecting against cyber attacks
- The impact of cyber crime on the economy
- Investigating the effectiveness of multi-factor authentication in securing data
- The future of cyber security in the age of quantum internet
- The impact of big data on cyber security
- The role of cybersecurity in the education system
- Investigating the use of deception techniques in cyber security
- The impact of cyber attacks on the healthcare industry
- The effectiveness of cyber threat intelligence in mitigating cyber risks
- The role of cyber security in protecting financial institutions
- Investigating the use of machine learning in cyber security risk assessment
- The impact of cyber attacks on the transportation industry
- The effectiveness of network segmentation in protecting against cyber attacks
- Investigating the effectiveness of biometric identification in cyber security
- The impact of cyber attacks on the hospitality industry
- The future of cyber security in the era of autonomous vehicles
- The effectiveness of intrusion detection systems in protecting against cyber attacks
- The role of cyber security in protecting small businesses
- Investigating the effectiveness of virtual private networks (VPNs) in securing data
- The impact of cyber attacks on the energy sector
- The effectiveness of cyber security regulations in mitigating cyber risks
- Investigating the use of deception technology in cyber security
- The impact of cyber attacks on the retail industry
- The effectiveness of cyber security in protecting critical infrastructure
- The role of cyber security in protecting intellectual property in the entertainment industry
- Investigating the effectiveness of intrusion prevention systems in protecting against cyber attacks
- The impact of cyber attacks on the aerospace industry
- The future of cyber security in the era of quantum computing
- The effectiveness of cyber security in protecting against ransomware attacks
- The role of cyber security in protecting personal and sensitive data
- Investigating the effectiveness of cloud security solutions in protecting against cyber attacks
- The impact of cyber attacks on the manufacturing industry
- The effective cyber security and the future of e-votingness of cyber security in protecting against social engineering attacks
- Investigating the effectiveness of end-to-end encryption in securing data
- The impact of cyber attacks on the insurance industry
- The future of cyber security in the era of artificial intelligence
- The effectiveness of cyber security in protecting against distributed denial-of-service (DDoS) attacks
- The role of cyber security in protecting against phishing attacks
- Investigating the effectiveness of user behavior analytics
- The impact of emerging technologies on cyber security
- Developing a framework for cyber threat intelligence
- The effectiveness of current cyber security measures
- Cyber security and data privacy in the age of big data
- Cloud security and virtualization technologies
- Cryptography and its role in cyber security
- Cyber security in critical infrastructure protection
- Cyber security in the Internet of Things (IoT)
- Cyber security in e-commerce and online payment systems
- Cyber security and the future of digital currencies
- The impact of social engineering on cyber security
- Cyber security and ethical hacking
- Cyber security challenges in the healthcare industry
- Cyber security and digital forensics
- Cyber security in the financial sector
- Cyber security in the transportation industry
- The impact of artificial intelligence on cyber security risks
- Cyber security and mobile devices
- Cyber security in the energy sector
- Cyber security and supply chain management
- The role of machine learning in cyber security
- Cyber security in the defense sector
- The impact of the Dark Web on cyber security
- Cyber security in social media and online communities
- Cyber security challenges in the gaming industry
- Cyber security and cloud-based applications
- The role of blockchain in cyber security
- Cyber security and the future of autonomous vehicles
- Cyber security in the education sector
- Cyber security in the aviation industry
- The impact of 5G on cyber security
- Cyber security and insider threats
- Cyber security and the legal system
- The impact of cyber security on business operations
- Cyber security and the role of human behavior
- Cyber security in the hospitality industry
- The impact of cyber security on national security
- Cyber security and the use of biometrics
- Cyber security and the role of social media influencers
- The impact of cyber security on small and medium-sized enterprises
- Cyber security and cyber insurance
- The impact of cyber security on the job market
- Cyber security and international relations
- Cyber security and the role of government policies
- The impact of cyber security on privacy laws
- Cyber security in the media and entertainment industry
- The role of cyber security in digital marketing
- Cyber security and the role of cybersecurity professionals
- Cyber security in the retail industry
- The impact of cyber security on the stock market
- Cyber security and intellectual property protection
- Cyber security and online dating
- The impact of cyber security on healthcare innovation
- Cyber security and the future of e-voting
- Cyber security and the role of open source software
- Cyber security and the use of social engineering in cyber attacks
- The impact of cyber security on the aviation industry
- Cyber security and the role of cyber security awareness training
- Cyber security and the role of cybersecurity standards and best practices
- Cyber security in the legal industry
- The impact of cyber security on human rights
- Cyber security and the role of public-private partnerships
- Cyber security and the future of e-learning
- Cyber security and the role of mobile applications
- The impact of cyber security on environmental sustainability
- Cyber security and the role of threat intelligence sharing
- Cyber security and the future of smart homes
- Cyber security and the role of cybersecurity certifications
- The impact of cyber security on international trade
- Cyber security and the role of cyber security auditing
About the author
Muhammad Hassan
Researcher, Academic Writer, Web developer
You may also like

350+ Biology Research Topics

300+ Interesting Research Topics

500+ Psychology Research Paper Topics

500+ Environmental Research Topics

300+ Political Science Research Topics

500+ Music Research Topics
Cyber risk and cybersecurity: a systematic review of data availability
- Open access
- Published: 17 February 2022
- Volume 47 , pages 698–736, ( 2022 )
Cite this article
You have full access to this open access article

- Frank Cremer 1 ,
- Barry Sheehan ORCID: orcid.org/0000-0003-4592-7558 1 ,
- Michael Fortmann 2 ,
- Arash N. Kia 1 ,
- Martin Mullins 1 ,
- Finbarr Murphy 1 &
- Stefan Materne 2
73k Accesses
81 Citations
43 Altmetric
Explore all metrics
Cybercrime is estimated to have cost the global economy just under USD 1 trillion in 2020, indicating an increase of more than 50% since 2018. With the average cyber insurance claim rising from USD 145,000 in 2019 to USD 359,000 in 2020, there is a growing necessity for better cyber information sources, standardised databases, mandatory reporting and public awareness. This research analyses the extant academic and industry literature on cybersecurity and cyber risk management with a particular focus on data availability. From a preliminary search resulting in 5219 cyber peer-reviewed studies, the application of the systematic methodology resulted in 79 unique datasets. We posit that the lack of available data on cyber risk poses a serious problem for stakeholders seeking to tackle this issue. In particular, we identify a lacuna in open databases that undermine collective endeavours to better manage this set of risks. The resulting data evaluation and categorisation will support cybersecurity researchers and the insurance industry in their efforts to comprehend, metricise and manage cyber risks.
Similar content being viewed by others

Systematic Review: Cybersecurity Risk Taxonomy

A Survey of Cybersecurity Risk Management Frameworks

Cybersecurity Risk Management Frameworks in the Oil and Gas Sector: A Systematic Literature Review
Avoid common mistakes on your manuscript.
Introduction
Globalisation, digitalisation and smart technologies have escalated the propensity and severity of cybercrime. Whilst it is an emerging field of research and industry, the importance of robust cybersecurity defence systems has been highlighted at the corporate, national and supranational levels. The impacts of inadequate cybersecurity are estimated to have cost the global economy USD 945 billion in 2020 (Maleks Smith et al. 2020 ). Cyber vulnerabilities pose significant corporate risks, including business interruption, breach of privacy and financial losses (Sheehan et al. 2019 ). Despite the increasing relevance for the international economy, the availability of data on cyber risks remains limited. The reasons for this are many. Firstly, it is an emerging and evolving risk; therefore, historical data sources are limited (Biener et al. 2015 ). It could also be due to the fact that, in general, institutions that have been hacked do not publish the incidents (Eling and Schnell 2016 ). The lack of data poses challenges for many areas, such as research, risk management and cybersecurity (Falco et al. 2019 ). The importance of this topic is demonstrated by the announcement of the European Council in April 2021 that a centre of excellence for cybersecurity will be established to pool investments in research, technology and industrial development. The goal of this centre is to increase the security of the internet and other critical network and information systems (European Council 2021 ).
This research takes a risk management perspective, focusing on cyber risk and considering the role of cybersecurity and cyber insurance in risk mitigation and risk transfer. The study reviews the existing literature and open data sources related to cybersecurity and cyber risk. This is the first systematic review of data availability in the general context of cyber risk and cybersecurity. By identifying and critically analysing the available datasets, this paper supports the research community by aggregating, summarising and categorising all available open datasets. In addition, further information on datasets is attached to provide deeper insights and support stakeholders engaged in cyber risk control and cybersecurity. Finally, this research paper highlights the need for open access to cyber-specific data, without price or permission barriers.
The identified open data can support cyber insurers in their efforts on sustainable product development. To date, traditional risk assessment methods have been untenable for insurance companies due to the absence of historical claims data (Sheehan et al. 2021 ). These high levels of uncertainty mean that cyber insurers are more inclined to overprice cyber risk cover (Kshetri 2018 ). Combining external data with insurance portfolio data therefore seems to be essential to improve the evaluation of the risk and thus lead to risk-adjusted pricing (Bessy-Roland et al. 2021 ). This argument is also supported by the fact that some re/insurers reported that they are working to improve their cyber pricing models (e.g. by creating or purchasing databases from external providers) (EIOPA 2018 ). Figure 1 provides an overview of pricing tools and factors considered in the estimation of cyber insurance based on the findings of EIOPA ( 2018 ) and the research of Romanosky et al. ( 2019 ). The term cyber risk refers to all cyber risks and their potential impact.
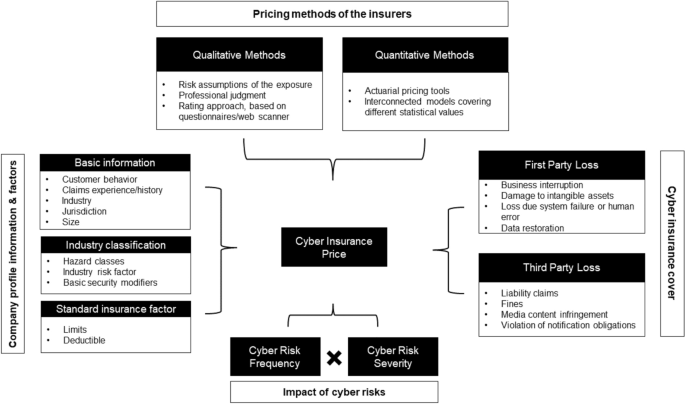
An overview of the current cyber insurance informational and methodological landscape, adapted from EIOPA ( 2018 ) and Romanosky et al. ( 2019 )
Besides the advantage of risk-adjusted pricing, the availability of open datasets helps companies benchmark their internal cyber posture and cybersecurity measures. The research can also help to improve risk awareness and corporate behaviour. Many companies still underestimate their cyber risk (Leong and Chen 2020 ). For policymakers, this research offers starting points for a comprehensive recording of cyber risks. Although in many countries, companies are obliged to report data breaches to the respective supervisory authority, this information is usually not accessible to the research community. Furthermore, the economic impact of these breaches is usually unclear.
As well as the cyber risk management community, this research also supports cybersecurity stakeholders. Researchers are provided with an up-to-date, peer-reviewed literature of available datasets showing where these datasets have been used. For example, this includes datasets that have been used to evaluate the effectiveness of countermeasures in simulated cyberattacks or to test intrusion detection systems. This reduces a time-consuming search for suitable datasets and ensures a comprehensive review of those available. Through the dataset descriptions, researchers and industry stakeholders can compare and select the most suitable datasets for their purposes. In addition, it is possible to combine the datasets from one source in the context of cybersecurity or cyber risk. This supports efficient and timely progress in cyber risk research and is beneficial given the dynamic nature of cyber risks.
Cyber risks are defined as “operational risks to information and technology assets that have consequences affecting the confidentiality, availability, and/or integrity of information or information systems” (Cebula et al. 2014 ). Prominent cyber risk events include data breaches and cyberattacks (Agrafiotis et al. 2018 ). The increasing exposure and potential impact of cyber risk have been highlighted in recent industry reports (e.g. Allianz 2021 ; World Economic Forum 2020 ). Cyberattacks on critical infrastructures are ranked 5th in the World Economic Forum's Global Risk Report. Ransomware, malware and distributed denial-of-service (DDoS) are examples of the evolving modes of a cyberattack. One example is the ransomware attack on the Colonial Pipeline, which shut down the 5500 mile pipeline system that delivers 2.5 million barrels of fuel per day and critical liquid fuel infrastructure from oil refineries to states along the U.S. East Coast (Brower and McCormick 2021 ). These and other cyber incidents have led the U.S. to strengthen its cybersecurity and introduce, among other things, a public body to analyse major cyber incidents and make recommendations to prevent a recurrence (Murphey 2021a ). Another example of the scope of cyberattacks is the ransomware NotPetya in 2017. The damage amounted to USD 10 billion, as the ransomware exploited a vulnerability in the windows system, allowing it to spread independently worldwide in the network (GAO 2021 ). In the same year, the ransomware WannaCry was launched by cybercriminals. The cyberattack on Windows software took user data hostage in exchange for Bitcoin cryptocurrency (Smart 2018 ). The victims included the National Health Service in Great Britain. As a result, ambulances were redirected to other hospitals because of information technology (IT) systems failing, leaving people in need of urgent assistance waiting. It has been estimated that 19,000 cancelled treatment appointments resulted from losses of GBP 92 million (Field 2018 ). Throughout the COVID-19 pandemic, ransomware attacks increased significantly, as working from home arrangements increased vulnerability (Murphey 2021b ).
Besides cyberattacks, data breaches can also cause high costs. Under the General Data Protection Regulation (GDPR), companies are obliged to protect personal data and safeguard the data protection rights of all individuals in the EU area. The GDPR allows data protection authorities in each country to impose sanctions and fines on organisations they find in breach. “For data breaches, the maximum fine can be €20 million or 4% of global turnover, whichever is higher” (GDPR.EU 2021 ). Data breaches often involve a large amount of sensitive data that has been accessed, unauthorised, by external parties, and are therefore considered important for information security due to their far-reaching impact (Goode et al. 2017 ). A data breach is defined as a “security incident in which sensitive, protected, or confidential data are copied, transmitted, viewed, stolen, or used by an unauthorized individual” (Freeha et al. 2021 ). Depending on the amount of data, the extent of the damage caused by a data breach can be significant, with the average cost being USD 392 million Footnote 1 (IBM Security 2020 ).
This research paper reviews the existing literature and open data sources related to cybersecurity and cyber risk, focusing on the datasets used to improve academic understanding and advance the current state-of-the-art in cybersecurity. Furthermore, important information about the available datasets is presented (e.g. use cases), and a plea is made for open data and the standardisation of cyber risk data for academic comparability and replication. The remainder of the paper is structured as follows. The next section describes the related work regarding cybersecurity and cyber risks. The third section outlines the review method used in this work and the process. The fourth section details the results of the identified literature. Further discussion is presented in the penultimate section and the final section concludes.
Related work
Due to the significance of cyber risks, several literature reviews have been conducted in this field. Eling ( 2020 ) reviewed the existing academic literature on the topic of cyber risk and cyber insurance from an economic perspective. A total of 217 papers with the term ‘cyber risk’ were identified and classified in different categories. As a result, open research questions are identified, showing that research on cyber risks is still in its infancy because of their dynamic and emerging nature. Furthermore, the author highlights that particular focus should be placed on the exchange of information between public and private actors. An improved information flow could help to measure the risk more accurately and thus make cyber risks more insurable and help risk managers to determine the right level of cyber risk for their company. In the context of cyber insurance data, Romanosky et al. ( 2019 ) analysed the underwriting process for cyber insurance and revealed how cyber insurers understand and assess cyber risks. For this research, they examined 235 American cyber insurance policies that were publicly available and looked at three components (coverage, application questionnaires and pricing). The authors state in their findings that many of the insurers used very simple, flat-rate pricing (based on a single calculation of expected loss), while others used more parameters such as the asset value of the company (or company revenue) or standard insurance metrics (e.g. deductible, limits), and the industry in the calculation. This is in keeping with Eling ( 2020 ), who states that an increased amount of data could help to make cyber risk more accurately measured and thus more insurable. Similar research on cyber insurance and data was conducted by Nurse et al. ( 2020 ). The authors examined cyber insurance practitioners' perceptions and the challenges they face in collecting and using data. In addition, gaps were identified during the research where further data is needed. The authors concluded that cyber insurance is still in its infancy, and there are still several unanswered questions (for example, cyber valuation, risk calculation and recovery). They also pointed out that a better understanding of data collection and use in cyber insurance would be invaluable for future research and practice. Bessy-Roland et al. ( 2021 ) come to a similar conclusion. They proposed a multivariate Hawkes framework to model and predict the frequency of cyberattacks. They used a public dataset with characteristics of data breaches affecting the U.S. industry. In the conclusion, the authors make the argument that an insurer has a better knowledge of cyber losses, but that it is based on a small dataset and therefore combination with external data sources seems essential to improve the assessment of cyber risks.
Several systematic reviews have been published in the area of cybersecurity (Kruse et al. 2017 ; Lee et al. 2020 ; Loukas et al. 2013 ; Ulven and Wangen 2021 ). In these papers, the authors concentrated on a specific area or sector in the context of cybersecurity. This paper adds to this extant literature by focusing on data availability and its importance to risk management and insurance stakeholders. With a priority on healthcare and cybersecurity, Kruse et al. ( 2017 ) conducted a systematic literature review. The authors identified 472 articles with the keywords ‘cybersecurity and healthcare’ or ‘ransomware’ in the databases Cumulative Index of Nursing and Allied Health Literature, PubMed and Proquest. Articles were eligible for this review if they satisfied three criteria: (1) they were published between 2006 and 2016, (2) the full-text version of the article was available, and (3) the publication is a peer-reviewed or scholarly journal. The authors found that technological development and federal policies (in the U.S.) are the main factors exposing the health sector to cyber risks. Loukas et al. ( 2013 ) conducted a review with a focus on cyber risks and cybersecurity in emergency management. The authors provided an overview of cyber risks in communication, sensor, information management and vehicle technologies used in emergency management and showed areas for which there is still no solution in the literature. Similarly, Ulven and Wangen ( 2021 ) reviewed the literature on cybersecurity risks in higher education institutions. For the literature review, the authors used the keywords ‘cyber’, ‘information threats’ or ‘vulnerability’ in connection with the terms ‘higher education, ‘university’ or ‘academia’. A similar literature review with a focus on Internet of Things (IoT) cybersecurity was conducted by Lee et al. ( 2020 ). The review revealed that qualitative approaches focus on high-level frameworks, and quantitative approaches to cybersecurity risk management focus on risk assessment and quantification of cyberattacks and impacts. In addition, the findings presented a four-step IoT cyber risk management framework that identifies, quantifies and prioritises cyber risks.
Datasets are an essential part of cybersecurity research, underlined by the following works. Ilhan Firat et al. ( 2021 ) examined various cybersecurity datasets in detail. The study was motivated by the fact that with the proliferation of the internet and smart technologies, the mode of cyberattacks is also evolving. However, in order to prevent such attacks, they must first be detected; the dissemination and further development of cybersecurity datasets is therefore critical. In their work, the authors observed studies of datasets used in intrusion detection systems. Khraisat et al. ( 2019 ) also identified a need for new datasets in the context of cybersecurity. The researchers presented a taxonomy of current intrusion detection systems, a comprehensive review of notable recent work, and an overview of the datasets commonly used for assessment purposes. In their conclusion, the authors noted that new datasets are needed because most machine-learning techniques are trained and evaluated on the knowledge of old datasets. These datasets do not contain new and comprehensive information and are partly derived from datasets from 1999. The authors noted that the core of this issue is the availability of new public datasets as well as their quality. The availability of data, how it is used, created and shared was also investigated by Zheng et al. ( 2018 ). The researchers analysed 965 cybersecurity research papers published between 2012 and 2016. They created a taxonomy of the types of data that are created and shared and then analysed the data collected via datasets. The researchers concluded that while datasets are recognised as valuable for cybersecurity research, the proportion of publicly available datasets is limited.
The main contributions of this review and what differentiates it from previous studies can be summarised as follows. First, as far as we can tell, it is the first work to summarise all available datasets on cyber risk and cybersecurity in the context of a systematic review and present them to the scientific community and cyber insurance and cybersecurity stakeholders. Second, we investigated, analysed, and made available the datasets to support efficient and timely progress in cyber risk research. And third, we enable comparability of datasets so that the appropriate dataset can be selected depending on the research area.
Methodology
Process and eligibility criteria.
The structure of this systematic review is inspired by the Preferred Reporting Items for Systematic Reviews and Meta-Analyses (PRISMA) framework (Page et al. 2021 ), and the search was conducted from 3 to 10 May 2021. Due to the continuous development of cyber risks and their countermeasures, only articles published in the last 10 years were considered. In addition, only articles published in peer-reviewed journals written in English were included. As a final criterion, only articles that make use of one or more cybersecurity or cyber risk datasets met the inclusion criteria. Specifically, these studies presented new or existing datasets, used them for methods, or used them to verify new results, as well as analysed them in an economic context and pointed out their effects. The criterion was fulfilled if it was clearly stated in the abstract that one or more datasets were used. A detailed explanation of this selection criterion can be found in the ‘Study selection’ section.
Information sources
In order to cover a complete spectrum of literature, various databases were queried to collect relevant literature on the topic of cybersecurity and cyber risks. Due to the spread of related articles across multiple databases, the literature search was limited to the following four databases for simplicity: IEEE Xplore, Scopus, SpringerLink and Web of Science. This is similar to other literature reviews addressing cyber risks or cybersecurity, including Sardi et al. ( 2021 ), Franke and Brynielsson ( 2014 ), Lagerström (2019), Eling and Schnell ( 2016 ) and Eling ( 2020 ). In this paper, all databases used in the aforementioned works were considered. However, only two studies also used all the databases listed. The IEEE Xplore database contains electrical engineering, computer science, and electronics work from over 200 journals and three million conference papers (IEEE 2021 ). Scopus includes 23,400 peer-reviewed journals from more than 5000 international publishers in the areas of science, engineering, medicine, social sciences and humanities (Scopus 2021 ). SpringerLink contains 3742 journals and indexes over 10 million scientific documents (SpringerLink 2021 ). Finally, Web of Science indexes over 9200 journals in different scientific disciplines (Science 2021 ).
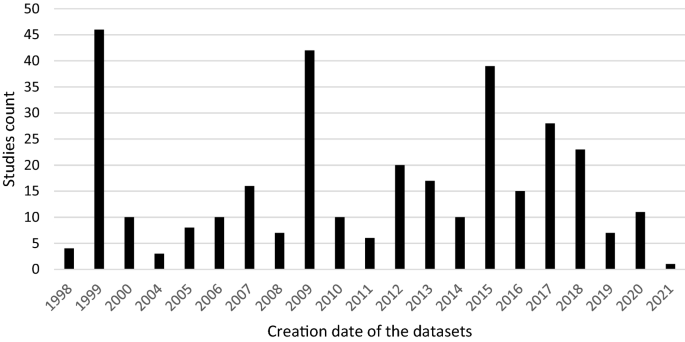
A search string was created and applied to all databases. To make the search efficient and reproducible, the following search string with Boolean operator was used in all databases: cybersecurity OR cyber risk AND dataset OR database. To ensure uniformity of the search across all databases, some adjustments had to be made for the respective search engines. In Scopus, for example, the Advanced Search was used, and the field code ‘Title-ABS-KEY’ was integrated into the search string. For IEEE Xplore, the search was carried out with the Search String in the Command Search and ‘All Metadata’. In the Web of Science database, the Advanced Search was used. The special feature of this search was that it had to be carried out in individual steps. The first search was carried out with the terms cybersecurity OR cyber risk with the field tag Topic (T.S. =) and the second search with dataset OR database. Subsequently, these searches were combined, which then delivered the searched articles for review. For SpringerLink, the search string was used in the Advanced Search under the category ‘Find the resources with all of the words’. After conducting this search string, 5219 studies could be found. According to the eligibility criteria (period, language and only scientific journals), 1581 studies were identified in the databases:
Scopus: 135
Springer Link: 548
Web of Science: 534
An overview of the process is given in Fig. 2 . Combined with the results from the four databases, 854 articles without duplicates were identified.
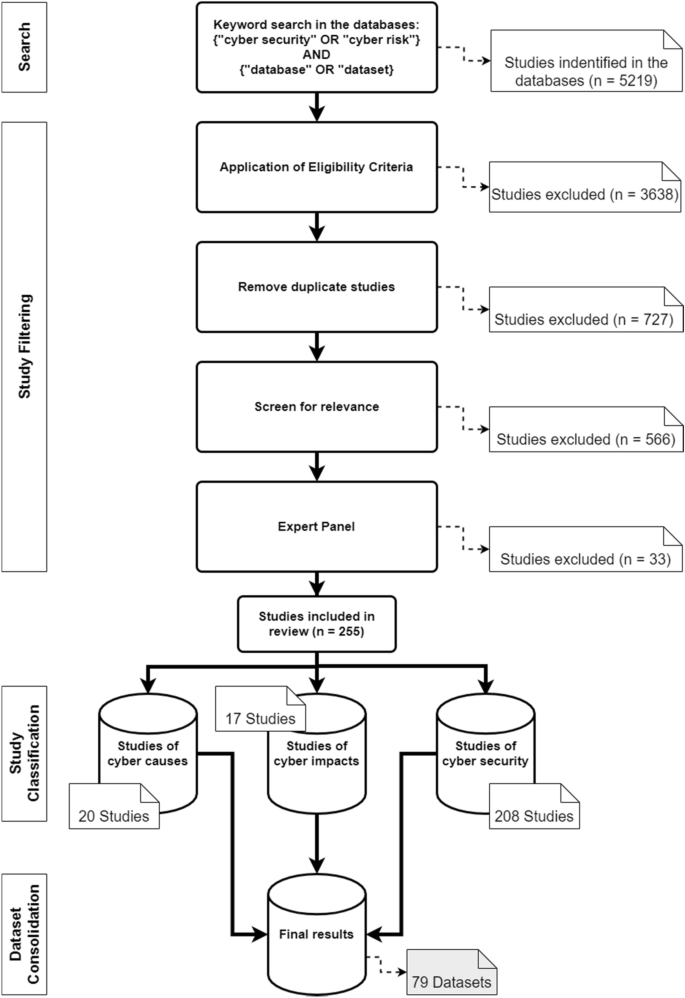
Literature search process and categorisation of the studies
Study selection
In the final step of the selection process, the articles were screened for relevance. Due to a large number of results, the abstracts were analysed in the first step of the process. The aim was to determine whether the article was relevant for the systematic review. An article fulfilled the criterion if it was recognisable in the abstract that it had made a contribution to datasets or databases with regard to cyber risks or cybersecurity. Specifically, the criterion was considered to be met if the abstract used datasets that address the causes or impacts of cyber risks, and measures in the area of cybersecurity. In this process, the number of articles was reduced to 288. The articles were then read in their entirety, and an expert panel of six people decided whether they should be used. This led to a final number of 255 articles. The years in which the articles were published and the exact number can be seen in Fig. 3 .
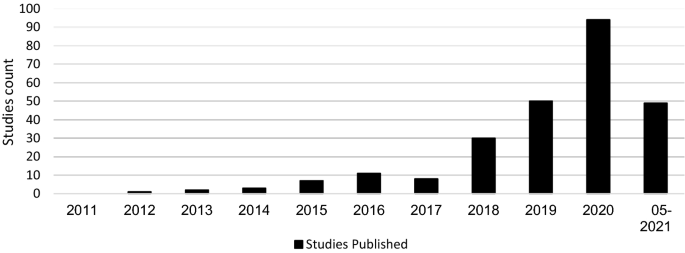
Distribution of studies
Data collection process and synthesis of the results
For the data collection process, various data were extracted from the studies, including the names of the respective creators, the name of the dataset or database and the corresponding reference. It was also determined where the data came from. In the context of accessibility, it was determined whether access is free, controlled, available for purchase or not available. It was also determined when the datasets were created and the time period referenced. The application type and domain characteristics of the datasets were identified.
This section analyses the results of the systematic literature review. The previously identified studies are divided into three categories: datasets on the causes of cyber risks, datasets on the effects of cyber risks and datasets on cybersecurity. The classification is based on the intended use of the studies. This system of classification makes it easier for stakeholders to find the appropriate datasets. The categories are evaluated individually. Although complete information is available for a large proportion of datasets, this is not true for all of them. Accordingly, the abbreviation N/A has been inserted in the respective characters to indicate that this information could not be determined by the time of submission. The term ‘use cases in the literature’ in the following and supplementary tables refers to the application areas in which the corresponding datasets were used in the literature. The areas listed there refer to the topic area on which the researchers conducted their research. Since some datasets were used interdisciplinarily, the listed use cases in the literature are correspondingly longer. Before discussing each category in the next sections, Fig. 4 provides an overview of the number of datasets found and their year of creation. Figure 5 then shows the relationship between studies and datasets in the period under consideration. Figure 6 shows the distribution of studies, their use of datasets and their creation date. The number of datasets used is higher than the number of studies because the studies often used several datasets (Table 1 ).
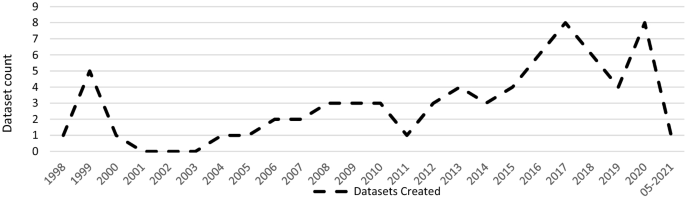
Distribution of dataset results
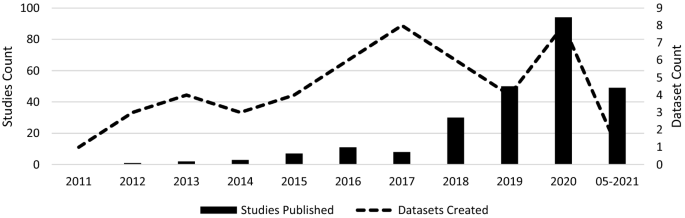
Correlation between the studies and the datasets
Distribution of studies and their use of datasets
Most of the datasets are generated in the U.S. (up to 58.2%). Canada and Australia rank next, with 11.3% and 5% of all the reviewed datasets, respectively.
Additionally, to create value for the datasets for the cyber insurance industry, an assessment of the applicability of each dataset has been provided for cyber insurers. This ‘Use Case Assessment’ includes the use of the data in the context of different analyses, calculation of cyber insurance premiums, and use of the information for the design of cyber insurance contracts or for additional customer services. To reasonably account for the transition of direct hyperlinks in the future, references were directed to the main websites for longevity (nearest resource point). In addition, the links to the main pages contain further information on the datasets and different versions related to the operating systems. The references were chosen in such a way that practitioners get the best overview of the respective datasets.
Case datasets
This section presents selected articles that use the datasets to analyse the causes of cyber risks. The datasets help identify emerging trends and allow pattern discovery in cyber risks. This information gives cybersecurity experts and cyber insurers the data to make better predictions and take appropriate action. For example, if certain vulnerabilities are not adequately protected, cyber insurers will demand a risk surcharge leading to an improvement in the risk-adjusted premium. Due to the capricious nature of cyber risks, existing data must be supplemented with new data sources (for example, new events, new methods or security vulnerabilities) to determine prevailing cyber exposure. The datasets of cyber risk causes could be combined with existing portfolio data from cyber insurers and integrated into existing pricing tools and factors to improve the valuation of cyber risks.
A portion of these datasets consists of several taxonomies and classifications of cyber risks. Aassal et al. ( 2020 ) propose a new taxonomy of phishing characteristics based on the interpretation and purpose of each characteristic. In comparison, Hindy et al. ( 2020 ) presented a taxonomy of network threats and the impact of current datasets on intrusion detection systems. A similar taxonomy was suggested by Kiwia et al. ( 2018 ). The authors presented a cyber kill chain-based taxonomy of banking Trojans features. The taxonomy built on a real-world dataset of 127 banking Trojans collected from December 2014 to January 2016 by a major U.K.-based financial organisation.
In the context of classification, Aamir et al. ( 2021 ) showed the benefits of machine learning for classifying port scans and DDoS attacks in a mixture of normal and attack traffic. Guo et al. ( 2020 ) presented a new method to improve malware classification based on entropy sequence features. The evaluation of this new method was conducted on different malware datasets.
To reconstruct attack scenarios and draw conclusions based on the evidence in the alert stream, Barzegar and Shajari ( 2018 ) use the DARPA2000 and MACCDC 2012 dataset for their research. Giudici and Raffinetti ( 2020 ) proposed a rank-based statistical model aimed at predicting the severity levels of cyber risk. The model used cyber risk data from the University of Milan. In contrast to the previous datasets, Skrjanc et al. ( 2018 ) used the older dataset KDD99 to monitor large-scale cyberattacks using a cauchy clustering method.
Amin et al. ( 2021 ) used a cyberattack dataset from the Canadian Institute for Cybersecurity to identify spatial clusters of countries with high rates of cyberattacks. In the context of cybercrime, Junger et al. ( 2020 ) examined crime scripts, key characteristics of the target company and the relationship between criminal effort and financial benefit. For their study, the authors analysed 300 cases of fraudulent activities against Dutch companies. With a similar focus on cybercrime, Mireles et al. ( 2019 ) proposed a metric framework to measure the effectiveness of the dynamic evolution of cyberattacks and defensive measures. To validate its usefulness, they used the DEFCON dataset.
Due to the rapidly changing nature of cyber risks, it is often impossible to obtain all information on them. Kim and Kim ( 2019 ) proposed an automated dataset generation system called CTIMiner that collects threat data from publicly available security reports and malware repositories. They released a dataset to the public containing about 640,000 records from 612 security reports published between January 2008 and 2019. A similar approach is proposed by Kim et al. ( 2020 ), using a named entity recognition system to extract core information from cyber threat reports automatically. They created a 498,000-tag dataset during their research (Ulven and Wangen 2021 ).
Within the framework of vulnerabilities and cybersecurity issues, Ulven and Wangen ( 2021 ) proposed an overview of mission-critical assets and everyday threat events, suggested a generic threat model, and summarised common cybersecurity vulnerabilities. With a focus on hospitality, Chen and Fiscus ( 2018 ) proposed several issues related to cybersecurity in this sector. They analysed 76 security incidents from the Privacy Rights Clearinghouse database. Supplementary Table 1 lists all findings that belong to the cyber causes dataset.
Impact datasets
This section outlines selected findings of the cyber impact dataset. For cyber insurers, these datasets can form an important basis for information, as they can be used to calculate cyber insurance premiums, evaluate specific cyber risks, formulate inclusions and exclusions in cyber wordings, and re-evaluate as well as supplement the data collected so far on cyber risks. For example, information on financial losses can help to better assess the loss potential of cyber risks. Furthermore, the datasets can provide insight into the frequency of occurrence of these cyber risks. The new datasets can be used to close any data gaps that were previously based on very approximate estimates or to find new results.
Eight studies addressed the costs of data breaches. For instance, Eling and Jung ( 2018 ) reviewed 3327 data breach events from 2005 to 2016 and identified an asymmetric dependence of monthly losses by breach type and industry. The authors used datasets from the Privacy Rights Clearinghouse for analysis. The Privacy Rights Clearinghouse datasets and the Breach level index database were also used by De Giovanni et al. ( 2020 ) to describe relationships between data breaches and bitcoin-related variables using the cointegration methodology. The data were obtained from the Department of Health and Human Services of healthcare facilities reporting data breaches and a national database of technical and organisational infrastructure information. Also in the context of data breaches, Algarni et al. ( 2021 ) developed a comprehensive, formal model that estimates the two components of security risks: breach cost and the likelihood of a data breach within 12 months. For their survey, the authors used two industrial reports from the Ponemon institute and VERIZON. To illustrate the scope of data breaches, Neto et al. ( 2021 ) identified 430 major data breach incidents among more than 10,000 incidents. The database created is available and covers the period 2018 to 2019.
With a direct focus on insurance, Biener et al. ( 2015 ) analysed 994 cyber loss cases from an operational risk database and investigated the insurability of cyber risks based on predefined criteria. For their study, they used data from the company SAS OpRisk Global Data. Similarly, Eling and Wirfs ( 2019 ) looked at a wide range of cyber risk events and actual cost data using the same database. They identified cyber losses and analysed them using methods from statistics and actuarial science. Using a similar reference, Farkas et al. ( 2021 ) proposed a method for analysing cyber claims based on regression trees to identify criteria for classifying and evaluating claims. Similar to Chen and Fiscus ( 2018 ), the dataset used was the Privacy Rights Clearinghouse database. Within the framework of reinsurance, Moro ( 2020 ) analysed cyber index-based information technology activity to see if index-parametric reinsurance coverage could suggest its cedant using data from a Symantec dataset.
Paté-Cornell et al. ( 2018 ) presented a general probabilistic risk analysis framework for cybersecurity in an organisation to be specified. The results are distributions of losses to cyberattacks, with and without considered countermeasures in support of risk management decisions based both on past data and anticipated incidents. The data used were from The Common Vulnerability and Exposures database and via confidential access to a database of cyberattacks on a large, U.S.-based organisation. A different conceptual framework for cyber risk classification and assessment was proposed by Sheehan et al. ( 2021 ). This framework showed the importance of proactive and reactive barriers in reducing companies’ exposure to cyber risk and quantifying the risk. Another approach to cyber risk assessment and mitigation was proposed by Mukhopadhyay et al. ( 2019 ). They estimated the probability of an attack using generalised linear models, predicted the security technology required to reduce the probability of cyberattacks, and used gamma and exponential distributions to best approximate the average loss data for each malicious attack. They also calculated the expected loss due to cyberattacks, calculated the net premium that would need to be charged by a cyber insurer, and suggested cyber insurance as a strategy to minimise losses. They used the CSI-FBI survey (1997–2010) to conduct their research.
In order to highlight the lack of data on cyber risks, Eling ( 2020 ) conducted a literature review in the areas of cyber risk and cyber insurance. Available information on the frequency, severity, and dependency structure of cyber risks was filtered out. In addition, open questions for future cyber risk research were set up. Another example of data collection on the impact of cyberattacks is provided by Sornette et al. ( 2013 ), who use a database of newspaper articles, press reports and other media to provide a predictive method to identify triggering events and potential accident scenarios and estimate their severity and frequency. A similar approach to data collection was used by Arcuri et al. ( 2020 ) to gather an original sample of global cyberattacks from newspaper reports sourced from the LexisNexis database. This collection is also used and applied to the fields of dynamic communication and cyber risk perception by Fang et al. ( 2021 ). To create a dataset of cyber incidents and disputes, Valeriano and Maness ( 2014 ) collected information on cyber interactions between rival states.
To assess trends and the scale of economic cybercrime, Levi ( 2017 ) examined datasets from different countries and their impact on crime policy. Pooser et al. ( 2018 ) investigated the trend in cyber risk identification from 2006 to 2015 and company characteristics related to cyber risk perception. The authors used a dataset of various reports from cyber insurers for their study. Walker-Roberts et al. ( 2020 ) investigated the spectrum of risk of a cybersecurity incident taking place in the cyber-physical-enabled world using the VERIS Community Database. The datasets of impacts identified are presented below. Due to overlap, some may also appear in the causes dataset (Supplementary Table 2).
Cybersecurity datasets
General intrusion detection.
General intrusion detection systems account for the largest share of countermeasure datasets. For companies or researchers focused on cybersecurity, the datasets can be used to test their own countermeasures or obtain information about potential vulnerabilities. For example, Al-Omari et al. ( 2021 ) proposed an intelligent intrusion detection model for predicting and detecting attacks in cyberspace, which was applied to dataset UNSW-NB 15. A similar approach was taken by Choras and Kozik ( 2015 ), who used machine learning to detect cyberattacks on web applications. To evaluate their method, they used the HTTP dataset CSIC 2010. For the identification of unknown attacks on web servers, Kamarudin et al. ( 2017 ) proposed an anomaly-based intrusion detection system using an ensemble classification approach. Ganeshan and Rodrigues ( 2020 ) showed an intrusion detection system approach, which clusters the database into several groups and detects the presence of intrusion in the clusters. In comparison, AlKadi et al. ( 2019 ) used a localisation-based model to discover abnormal patterns in network traffic. Hybrid models have been recommended by Bhattacharya et al. ( 2020 ) and Agrawal et al. ( 2019 ); the former is a machine-learning model based on principal component analysis for the classification of intrusion detection system datasets, while the latter is a hybrid ensemble intrusion detection system for anomaly detection using different datasets to detect patterns in network traffic that deviate from normal behaviour.
Agarwal et al. ( 2021 ) used three different machine learning algorithms in their research to find the most suitable for efficiently identifying patterns of suspicious network activity. The UNSW-NB15 dataset was used for this purpose. Kasongo and Sun ( 2020 ), Feed-Forward Deep Neural Network (FFDNN), Keshk et al. ( 2021 ), the privacy-preserving anomaly detection framework, and others also use the UNSW-NB 15 dataset as part of intrusion detection systems. The same dataset and others were used by Binbusayyis and Vaiyapuri ( 2019 ) to identify and compare key features for cyber intrusion detection. Atefinia and Ahmadi ( 2021 ) proposed a deep neural network model to reduce the false positive rate of an anomaly-based intrusion detection system. Fossaceca et al. ( 2015 ) focused in their research on the development of a framework that combined the outputs of multiple learners in order to improve the efficacy of network intrusion, and Gauthama Raman et al. ( 2020 ) presented a search algorithm based on Support Vector machine to improve the performance of the detection and false alarm rate to improve intrusion detection techniques. Ahmad and Alsemmeari ( 2020 ) targeted extreme learning machine techniques due to their good capabilities in classification problems and handling huge data. They used the NSL-KDD dataset as a benchmark.
With reference to prediction, Bakdash et al. ( 2018 ) used datasets from the U.S. Department of Defence to predict cyberattacks by malware. This dataset consists of weekly counts of cyber events over approximately seven years. Another prediction method was presented by Fan et al. ( 2018 ), which showed an improved integrated cybersecurity prediction method based on spatial-time analysis. Also, with reference to prediction, Ashtiani and Azgomi ( 2014 ) proposed a framework for the distributed simulation of cyberattacks based on high-level architecture. Kirubavathi and Anitha ( 2016 ) recommended an approach to detect botnets, irrespective of their structures, based on network traffic flow behaviour analysis and machine-learning techniques. Dwivedi et al. ( 2021 ) introduced a multi-parallel adaptive technique to utilise an adaption mechanism in the group of swarms for network intrusion detection. AlEroud and Karabatis ( 2018 ) presented an approach that used contextual information to automatically identify and query possible semantic links between different types of suspicious activities extracted from network flows.
Intrusion detection systems with a focus on IoT
In addition to general intrusion detection systems, a proportion of studies focused on IoT. Habib et al. ( 2020 ) presented an approach for converting traditional intrusion detection systems into smart intrusion detection systems for IoT networks. To enhance the process of diagnostic detection of possible vulnerabilities with an IoT system, Georgescu et al. ( 2019 ) introduced a method that uses a named entity recognition-based solution. With regard to IoT in the smart home sector, Heartfield et al. ( 2021 ) presented a detection system that is able to autonomously adjust the decision function of its underlying anomaly classification models to a smart home’s changing condition. Another intrusion detection system was suggested by Keserwani et al. ( 2021 ), which combined Grey Wolf Optimization and Particle Swam Optimization to identify various attacks for IoT networks. They used the KDD Cup 99, NSL-KDD and CICIDS-2017 to evaluate their model. Abu Al-Haija and Zein-Sabatto ( 2020 ) provide a comprehensive development of a new intelligent and autonomous deep-learning-based detection and classification system for cyberattacks in IoT communication networks that leverage the power of convolutional neural networks, abbreviated as IoT-IDCS-CNN (IoT-based Intrusion Detection and Classification System using Convolutional Neural Network). To evaluate the development, the authors used the NSL-KDD dataset. Biswas and Roy ( 2021 ) recommended a model that identifies malicious botnet traffic using novel deep-learning approaches like artificial neural networks gutted recurrent units and long- or short-term memory models. They tested their model with the Bot-IoT dataset.
With a more forensic background, Koroniotis et al. ( 2020 ) submitted a network forensic framework, which described the digital investigation phases for identifying and tracing attack behaviours in IoT networks. The suggested work was evaluated with the Bot-IoT and UINSW-NB15 datasets. With a focus on big data and IoT, Chhabra et al. ( 2020 ) presented a cyber forensic framework for big data analytics in an IoT environment using machine learning. Furthermore, the authors mentioned different publicly available datasets for machine-learning models.
A stronger focus on a mobile phones was exhibited by Alazab et al. ( 2020 ), which presented a classification model that combined permission requests and application programme interface calls. The model was tested with a malware dataset containing 27,891 Android apps. A similar approach was taken by Li et al. ( 2019a , b ), who proposed a reliable classifier for Android malware detection based on factorisation machine architecture and extraction of Android app features from manifest files and source code.
Literature reviews
In addition to the different methods and models for intrusion detection systems, various literature reviews on the methods and datasets were also found. Liu and Lang ( 2019 ) proposed a taxonomy of intrusion detection systems that uses data objects as the main dimension to classify and summarise machine learning and deep learning-based intrusion detection literature. They also presented four different benchmark datasets for machine-learning detection systems. Ahmed et al. ( 2016 ) presented an in-depth analysis of four major categories of anomaly detection techniques, which include classification, statistical, information theory and clustering. Hajj et al. ( 2021 ) gave a comprehensive overview of anomaly-based intrusion detection systems. Their article gives an overview of the requirements, methods, measurements and datasets that are used in an intrusion detection system.
Within the framework of machine learning, Chattopadhyay et al. ( 2018 ) conducted a comprehensive review and meta-analysis on the application of machine-learning techniques in intrusion detection systems. They also compared different machine learning techniques in different datasets and summarised the performance. Vidros et al. ( 2017 ) presented an overview of characteristics and methods in automatic detection of online recruitment fraud. They also published an available dataset of 17,880 annotated job ads, retrieved from the use of a real-life system. An empirical study of different unsupervised learning algorithms used in the detection of unknown attacks was presented by Meira et al. ( 2020 ).
New datasets
Kilincer et al. ( 2021 ) reviewed different intrusion detection system datasets in detail. They had a closer look at the UNS-NB15, ISCX-2012, NSL-KDD and CIDDS-001 datasets. Stojanovic et al. ( 2020 ) also provided a review on datasets and their creation for use in advanced persistent threat detection in the literature. Another review of datasets was provided by Sarker et al. ( 2020 ), who focused on cybersecurity data science as part of their research and provided an overview from a machine-learning perspective. Avila et al. ( 2021 ) conducted a systematic literature review on the use of security logs for data leak detection. They recommended a new classification of information leak, which uses the GDPR principles, identified the most widely publicly available dataset for threat detection, described the attack types in the datasets and the algorithms used for data leak detection. Tuncer et al. ( 2020 ) presented a bytecode-based detection method consisting of feature extraction using local neighbourhood binary patterns. They chose a byte-based malware dataset to investigate the performance of the proposed local neighbourhood binary pattern-based detection method. With a different focus, Mauro et al. ( 2020 ) gave an experimental overview of neural-based techniques relevant to intrusion detection. They assessed the value of neural networks using the Bot-IoT and UNSW-DB15 datasets.
Another category of results in the context of countermeasure datasets is those that were presented as new. Moreno et al. ( 2018 ) developed a database of 300 security-related accidents from European and American sources. The database contained cybersecurity-related events in the chemical and process industry. Damasevicius et al. ( 2020 ) proposed a new dataset (LITNET-2020) for network intrusion detection. The dataset is a new annotated network benchmark dataset obtained from the real-world academic network. It presents real-world examples of normal and under-attack network traffic. With a focus on IoT intrusion detection systems, Alsaedi et al. ( 2020 ) proposed a new benchmark IoT/IIot datasets for assessing intrusion detection system-enabled IoT systems. Also in the context of IoT, Vaccari et al. ( 2020 ) proposed a dataset focusing on message queue telemetry transport protocols, which can be used to train machine-learning models. To evaluate the performance of machine-learning classifiers, Mahfouz et al. ( 2020 ) created a dataset called Game Theory and Cybersecurity (GTCS). A dataset containing 22,000 malware and benign samples was constructed by Martin et al. ( 2019 ). The dataset can be used as a benchmark to test the algorithm for Android malware classification and clustering techniques. In addition, Laso et al. ( 2017 ) presented a dataset created to investigate how data and information quality estimates enable the detection of anomalies and malicious acts in cyber-physical systems. The dataset contained various cyberattacks and is publicly available.
In addition to the results described above, several other studies were found that fit into the category of countermeasures. Johnson et al. ( 2016 ) examined the time between vulnerability disclosures. Using another vulnerabilities database, Common Vulnerabilities and Exposures (CVE), Subroto and Apriyana ( 2019 ) presented an algorithm model that uses big data analysis of social media and statistical machine learning to predict cyber risks. A similar databank but with a different focus, Common Vulnerability Scoring System, was used by Chatterjee and Thekdi ( 2020 ) to present an iterative data-driven learning approach to vulnerability assessment and management for complex systems. Using the CICIDS2017 dataset to evaluate the performance, Malik et al. ( 2020 ) proposed a control plane-based orchestration for varied, sophisticated threats and attacks. The same dataset was used in another study by Lee et al. ( 2019 ), who developed an artificial security information event management system based on a combination of event profiling for data processing and different artificial network methods. To exploit the interdependence between multiple series, Fang et al. ( 2021 ) proposed a statistical framework. In order to validate the framework, the authors applied it to a dataset of enterprise-level security breaches from the Privacy Rights Clearinghouse and Identity Theft Center database. Another framework with a defensive aspect was recommended by Li et al. ( 2021 ) to increase the robustness of deep neural networks against adversarial malware evasion attacks. Sarabi et al. ( 2016 ) investigated whether and to what extent business details can help assess an organisation's risk of data breaches and the distribution of risk across different types of incidents to create policies for protection, detection and recovery from different forms of security incidents. They used data from the VERIS Community Database.
Datasets that have been classified into the cybersecurity category are detailed in Supplementary Table 3. Due to overlap, records from the previous tables may also be included.
This paper presented a systematic literature review of studies on cyber risk and cybersecurity that used datasets. Within this framework, 255 studies were fully reviewed and then classified into three different categories. Then, 79 datasets were consolidated from these studies. These datasets were subsequently analysed, and important information was selected through a process of filtering out. This information was recorded in a table and enhanced with further information as part of the literature analysis. This made it possible to create a comprehensive overview of the datasets. For example, each dataset contains a description of where the data came from and how the data has been used to date. This allows different datasets to be compared and the appropriate dataset for the use case to be selected. This research certainly has limitations, so our selection of datasets cannot necessarily be taken as a representation of all available datasets related to cyber risks and cybersecurity. For example, literature searches were conducted in four academic databases and only found datasets that were used in the literature. Many research projects also used old datasets that may no longer consider current developments. In addition, the data are often focused on only one observation and are limited in scope. For example, the datasets can only be applied to specific contexts and are also subject to further limitations (e.g. region, industry, operating system). In the context of the applicability of the datasets, it is unfortunately not possible to make a clear statement on the extent to which they can be integrated into academic or practical areas of application or how great this effort is. Finally, it remains to be pointed out that this is an overview of currently available datasets, which are subject to constant change.
Due to the lack of datasets on cyber risks in the academic literature, additional datasets on cyber risks were integrated as part of a further search. The search was conducted on the Google Dataset search portal. The search term used was ‘cyber risk datasets’. Over 100 results were found. However, due to the low significance and verifiability, only 20 selected datasets were included. These can be found in Table 2 in the “ Appendix ”.
The results of the literature review and datasets also showed that there continues to be a lack of available, open cyber datasets. This lack of data is reflected in cyber insurance, for example, as it is difficult to find a risk-based premium without a sufficient database (Nurse et al. 2020 ). The global cyber insurance market was estimated at USD 5.5 billion in 2020 (Dyson 2020 ). When compared to the USD 1 trillion global losses from cybercrime (Maleks Smith et al. 2020 ), it is clear that there exists a significant cyber risk awareness challenge for both the insurance industry and international commerce. Without comprehensive and qualitative data on cyber losses, it can be difficult to estimate potential losses from cyberattacks and price cyber insurance accordingly (GAO 2021 ). For instance, the average cyber insurance loss increased from USD 145,000 in 2019 to USD 359,000 in 2020 (FitchRatings 2021 ). Cyber insurance is an important risk management tool to mitigate the financial impact of cybercrime. This is particularly evident in the impact of different industries. In the Energy & Commodities financial markets, a ransomware attack on the Colonial Pipeline led to a substantial impact on the U.S. economy. As a result of the attack, about 45% of the U.S. East Coast was temporarily unable to obtain supplies of diesel, petrol and jet fuel. This caused the average price in the U.S. to rise 7 cents to USD 3.04 per gallon, the highest in seven years (Garber 2021 ). In addition, Colonial Pipeline confirmed that it paid a USD 4.4 million ransom to a hacker gang after the attack. Another ransomware attack occurred in the healthcare and government sector. The victim of this attack was the Irish Health Service Executive (HSE). A ransom payment of USD 20 million was demanded from the Irish government to restore services after the hack (Tidy 2021 ). In the car manufacturing sector, Miller and Valasek ( 2015 ) initiated a cyberattack that resulted in the recall of 1.4 million vehicles and cost manufacturers EUR 761 million. The risk that arises in the context of these events is the potential for the accumulation of cyber losses, which is why cyber insurers are not expanding their capacity. An example of this accumulation of cyber risks is the NotPetya malware attack, which originated in Russia, struck in Ukraine, and rapidly spread around the world, causing at least USD 10 billion in damage (GAO 2021 ). These events highlight the importance of proper cyber risk management.
This research provides cyber insurance stakeholders with an overview of cyber datasets. Cyber insurers can use the open datasets to improve their understanding and assessment of cyber risks. For example, the impact datasets can be used to better measure financial impacts and their frequencies. These data could be combined with existing portfolio data from cyber insurers and integrated with existing pricing tools and factors to better assess cyber risk valuation. Although most cyber insurers have sparse historical cyber policy and claims data, they remain too small at present for accurate prediction (Bessy-Roland et al. 2021 ). A combination of portfolio data and external datasets would support risk-adjusted pricing for cyber insurance, which would also benefit policyholders. In addition, cyber insurance stakeholders can use the datasets to identify patterns and make better predictions, which would benefit sustainable cyber insurance coverage. In terms of cyber risk cause datasets, cyber insurers can use the data to review their insurance products. For example, the data could provide information on which cyber risks have not been sufficiently considered in product design or where improvements are needed. A combination of cyber cause and cybersecurity datasets can help establish uniform definitions to provide greater transparency and clarity. Consistent terminology could lead to a more sustainable cyber market, where cyber insurers make informed decisions about the level of coverage and policyholders understand their coverage (The Geneva Association 2020).
In addition to the cyber insurance community, this research also supports cybersecurity stakeholders. The reviewed literature can be used to provide a contemporary, contextual and categorised summary of available datasets. This supports efficient and timely progress in cyber risk research and is beneficial given the dynamic nature of cyber risks. With the help of the described cybersecurity datasets and the identified information, a comparison of different datasets is possible. The datasets can be used to evaluate the effectiveness of countermeasures in simulated cyberattacks or to test intrusion detection systems.
In this paper, we conducted a systematic review of studies on cyber risk and cybersecurity databases. We found that most of the datasets are in the field of intrusion detection and machine learning and are used for technical cybersecurity aspects. The available datasets on cyber risks were relatively less represented. Due to the dynamic nature and lack of historical data, assessing and understanding cyber risk is a major challenge for cyber insurance stakeholders. To address this challenge, a greater density of cyber data is needed to support cyber insurers in risk management and researchers with cyber risk-related topics. With reference to ‘Open Science’ FAIR data (Jacobsen et al. 2020 ), mandatory reporting of cyber incidents could help improve cyber understanding, awareness and loss prevention among companies and insurers. Through greater availability of data, cyber risks can be better understood, enabling researchers to conduct more in-depth research into these risks. Companies could incorporate this new knowledge into their corporate culture to reduce cyber risks. For insurance companies, this would have the advantage that all insurers would have the same understanding of cyber risks, which would support sustainable risk-based pricing. In addition, common definitions of cyber risks could be derived from new data.
The cybersecurity databases summarised and categorised in this research could provide a different perspective on cyber risks that would enable the formulation of common definitions in cyber policies. The datasets can help companies addressing cybersecurity and cyber risk as part of risk management assess their internal cyber posture and cybersecurity measures. The paper can also help improve risk awareness and corporate behaviour, and provides the research community with a comprehensive overview of peer-reviewed datasets and other available datasets in the area of cyber risk and cybersecurity. This approach is intended to support the free availability of data for research. The complete tabulated review of the literature is included in the Supplementary Material.
This work provides directions for several paths of future work. First, there are currently few publicly available datasets for cyber risk and cybersecurity. The older datasets that are still widely used no longer reflect today's technical environment. Moreover, they can often only be used in one context, and the scope of the samples is very limited. It would be of great value if more datasets were publicly available that reflect current environmental conditions. This could help intrusion detection systems to consider current events and thus lead to a higher success rate. It could also compensate for the disadvantages of older datasets by collecting larger quantities of samples and making this contextualisation more widespread. Another area of research may be the integratability and adaptability of cybersecurity and cyber risk datasets. For example, it is often unclear to what extent datasets can be integrated or adapted to existing data. For cyber risks and cybersecurity, it would be helpful to know what requirements need to be met or what is needed to use the datasets appropriately. In addition, it would certainly be helpful to know whether datasets can be modified to be used for cyber risks or cybersecurity. Finally, the ability for stakeholders to identify machine-readable cybersecurity datasets would be useful because it would allow for even clearer delineations or comparisons between datasets. Due to the lack of publicly available datasets, concrete benchmarks often cannot be applied.
Average cost of a breach of more than 50 million records.
Aamir, M., S.S.H. Rizvi, M.A. Hashmani, M. Zubair, and J. Ahmad. 2021. Machine learning classification of port scanning and DDoS attacks: A comparative analysis. Mehran University Research Journal of Engineering and Technology 40 (1): 215–229. https://doi.org/10.22581/muet1982.2101.19 .
Article Google Scholar
Aamir, M., and S.M.A. Zaidi. 2019. DDoS attack detection with feature engineering and machine learning: The framework and performance evaluation. International Journal of Information Security 18 (6): 761–785. https://doi.org/10.1007/s10207-019-00434-1 .
Aassal, A. El, S. Baki, A. Das, and R.M. Verma. 2020. 2020. An in-depth benchmarking and evaluation of phishing detection research for security needs. IEEE Access 8: 22170–22192. https://doi.org/10.1109/ACCESS.2020.2969780 .
Abu Al-Haija, Q., and S. Zein-Sabatto. 2020. An efficient deep-learning-based detection and classification system for cyber-attacks in IoT communication networks. Electronics 9 (12): 26. https://doi.org/10.3390/electronics9122152 .
Adhikari, U., T.H. Morris, and S.Y. Pan. 2018. Applying Hoeffding adaptive trees for real-time cyber-power event and intrusion classification. IEEE Transactions on Smart Grid 9 (5): 4049–4060. https://doi.org/10.1109/tsg.2017.2647778 .
Agarwal, A., P. Sharma, M. Alshehri, A.A. Mohamed, and O. Alfarraj. 2021. Classification model for accuracy and intrusion detection using machine learning approach. PeerJ Computer Science . https://doi.org/10.7717/peerj-cs.437 .
Agrafiotis, I., J.R.C.. Nurse, M. Goldsmith, S. Creese, and D. Upton. 2018. A taxonomy of cyber-harms: Defining the impacts of cyber-attacks and understanding how they propagate. Journal of Cybersecurity 4: tyy006.
Agrawal, A., S. Mohammed, and J. Fiaidhi. 2019. Ensemble technique for intruder detection in network traffic. International Journal of Security and Its Applications 13 (3): 1–8. https://doi.org/10.33832/ijsia.2019.13.3.01 .
Ahmad, I., and R.A. Alsemmeari. 2020. Towards improving the intrusion detection through ELM (extreme learning machine). CMC Computers Materials & Continua 65 (2): 1097–1111. https://doi.org/10.32604/cmc.2020.011732 .
Ahmed, M., A.N. Mahmood, and J.K. Hu. 2016. A survey of network anomaly detection techniques. Journal of Network and Computer Applications 60: 19–31. https://doi.org/10.1016/j.jnca.2015.11.016 .
Al-Jarrah, O.Y., O. Alhussein, P.D. Yoo, S. Muhaidat, K. Taha, and K. Kim. 2016. Data randomization and cluster-based partitioning for Botnet intrusion detection. IEEE Transactions on Cybernetics 46 (8): 1796–1806. https://doi.org/10.1109/TCYB.2015.2490802 .
Al-Mhiqani, M.N., R. Ahmad, Z.Z. Abidin, W. Yassin, A. Hassan, K.H. Abdulkareem, N.S. Ali, and Z. Yunos. 2020. A review of insider threat detection: Classification, machine learning techniques, datasets, open challenges, and recommendations. Applied Sciences—Basel 10 (15): 41. https://doi.org/10.3390/app10155208 .
Al-Omari, M., M. Rawashdeh, F. Qutaishat, M. Alshira’H, and N. Ababneh. 2021. An intelligent tree-based intrusion detection model for cyber security. Journal of Network and Systems Management 29 (2): 18. https://doi.org/10.1007/s10922-021-09591-y .
Alabdallah, A., and M. Awad. 2018. Using weighted Support Vector Machine to address the imbalanced classes problem of Intrusion Detection System. KSII Transactions on Internet and Information Systems 12 (10): 5143–5158. https://doi.org/10.3837/tiis.2018.10.027 .
Alazab, M., M. Alazab, A. Shalaginov, A. Mesleh, and A. Awajan. 2020. Intelligent mobile malware detection using permission requests and API calls. Future Generation Computer Systems—the International Journal of eScience 107: 509–521. https://doi.org/10.1016/j.future.2020.02.002 .
Albahar, M.A., R.A. Al-Falluji, and M. Binsawad. 2020. An empirical comparison on malicious activity detection using different neural network-based models. IEEE Access 8: 61549–61564. https://doi.org/10.1109/ACCESS.2020.2984157 .
AlEroud, A.F., and G. Karabatis. 2018. Queryable semantics to detect cyber-attacks: A flow-based detection approach. IEEE Transactions on Systems, Man, and Cybernetics: Systems 48 (2): 207–223. https://doi.org/10.1109/TSMC.2016.2600405 .
Algarni, A.M., V. Thayananthan, and Y.K. Malaiya. 2021. Quantitative assessment of cybersecurity risks for mitigating data breaches in business systems. Applied Sciences (switzerland) . https://doi.org/10.3390/app11083678 .
Alhowaide, A., I. Alsmadi, and J. Tang. 2021. Towards the design of real-time autonomous IoT NIDS. Cluster Computing—the Journal of Networks Software Tools and Applications . https://doi.org/10.1007/s10586-021-03231-5 .
Ali, S., and Y. Li. 2019. Learning multilevel auto-encoders for DDoS attack detection in smart grid network. IEEE Access 7: 108647–108659. https://doi.org/10.1109/ACCESS.2019.2933304 .
AlKadi, O., N. Moustafa, B. Turnbull, and K.K.R. Choo. 2019. Mixture localization-based outliers models for securing data migration in cloud centers. IEEE Access 7: 114607–114618. https://doi.org/10.1109/ACCESS.2019.2935142 .
Allianz. 2021. Allianz Risk Barometer. https://www.agcs.allianz.com/content/dam/onemarketing/agcs/agcs/reports/Allianz-Risk-Barometer-2021.pdf . Accessed 15 May 2021.
Almiani, M., A. AbuGhazleh, A. Al-Rahayfeh, S. Atiewi, and Razaque, A. 2020. Deep recurrent neural network for IoT intrusion detection system. Simulation Modelling Practice and Theory 101: 102031. https://doi.org/10.1016/j.simpat.2019.102031
Alsaedi, A., N. Moustafa, Z. Tari, A. Mahmood, and A. Anwar. 2020. TON_IoT telemetry dataset: A new generation dataset of IoT and IIoT for data-driven intrusion detection systems. IEEE Access 8: 165130–165150. https://doi.org/10.1109/access.2020.3022862 .
Alsamiri, J., and K. Alsubhi. 2019. Internet of Things cyber attacks detection using machine learning. International Journal of Advanced Computer Science and Applications 10 (12): 627–634.
Alsharafat, W. 2013. Applying artificial neural network and eXtended classifier system for network intrusion detection. International Arab Journal of Information Technology 10 (3): 230–238.
Google Scholar
Amin, R.W., H.E. Sevil, S. Kocak, G. Francia III., and P. Hoover. 2021. The spatial analysis of the malicious uniform resource locators (URLs): 2016 dataset case study. Information (switzerland) 12 (1): 1–18. https://doi.org/10.3390/info12010002 .
Arcuri, M.C., L.Z. Gai, F. Ielasi, and E. Ventisette. 2020. Cyber attacks on hospitality sector: Stock market reaction. Journal of Hospitality and Tourism Technology 11 (2): 277–290. https://doi.org/10.1108/jhtt-05-2019-0080 .
Arp, D., M. Spreitzenbarth, M. Hubner, H. Gascon, K. Rieck, and C.E.R.T. Siemens. 2014. Drebin: Effective and explainable detection of android malware in your pocket. In Ndss 14: 23–26.
Ashtiani, M., and M.A. Azgomi. 2014. A distributed simulation framework for modeling cyber attacks and the evaluation of security measures. Simulation 90 (9): 1071–1102. https://doi.org/10.1177/0037549714540221 .
Atefinia, R., and M. Ahmadi. 2021. Network intrusion detection using multi-architectural modular deep neural network. Journal of Supercomputing 77 (4): 3571–3593. https://doi.org/10.1007/s11227-020-03410-y .
Avila, R., R. Khoury, R. Khoury, and F. Petrillo. 2021. Use of security logs for data leak detection: A systematic literature review. Security and Communication Networks 2021: 29. https://doi.org/10.1155/2021/6615899 .
Azeez, N.A., T.J. Ayemobola, S. Misra, R. Maskeliunas, and R. Damasevicius. 2019. Network Intrusion Detection with a Hashing Based Apriori Algorithm Using Hadoop MapReduce. Computers 8 (4): 15. https://doi.org/10.3390/computers8040086 .
Bakdash, J.Z., S. Hutchinson, E.G. Zaroukian, L.R. Marusich, S. Thirumuruganathan, C. Sample, B. Hoffman, and G. Das. 2018. Malware in the future forecasting of analyst detection of cyber events. Journal of Cybersecurity . https://doi.org/10.1093/cybsec/tyy007 .
Barletta, V.S., D. Caivano, A. Nannavecchia, and M. Scalera. 2020. Intrusion detection for in-vehicle communication networks: An unsupervised Kohonen SOM approach. Future Internet . https://doi.org/10.3390/FI12070119 .
Barzegar, M., and M. Shajari. 2018. Attack scenario reconstruction using intrusion semantics. Expert Systems with Applications 108: 119–133. https://doi.org/10.1016/j.eswa.2018.04.030 .
Bessy-Roland, Y., A. Boumezoued, and C. Hillairet. 2021. Multivariate Hawkes process for cyber insurance. Annals of Actuarial Science 15 (1): 14–39.
Bhardwaj, A., V. Mangat, and R. Vig. 2020. Hyperband tuned deep neural network with well posed stacked sparse AutoEncoder for detection of DDoS attacks in cloud. IEEE Access 8: 181916–181929. https://doi.org/10.1109/ACCESS.2020.3028690 .
Bhati, B.S., C.S. Rai, B. Balamurugan, and F. Al-Turjman. 2020. An intrusion detection scheme based on the ensemble of discriminant classifiers. Computers & Electrical Engineering 86: 9. https://doi.org/10.1016/j.compeleceng.2020.106742 .
Bhattacharya, S., S.S.R. Krishnan, P.K.R. Maddikunta, R. Kaluri, S. Singh, T.R. Gadekallu, M. Alazab, and U. Tariq. 2020. A novel PCA-firefly based XGBoost classification model for intrusion detection in networks using GPU. Electronics 9 (2): 16. https://doi.org/10.3390/electronics9020219 .
Bibi, I., A. Akhunzada, J. Malik, J. Iqbal, A. Musaddiq, and S. Kim. 2020. A dynamic DL-driven architecture to combat sophisticated android malware. IEEE Access 8: 129600–129612. https://doi.org/10.1109/ACCESS.2020.3009819 .
Biener, C., M. Eling, and J.H. Wirfs. 2015. Insurability of cyber risk: An empirical analysis. The Geneva Papers on Risk and Insurance—Issues and Practice 40 (1): 131–158. https://doi.org/10.1057/gpp.2014.19 .
Binbusayyis, A., and T. Vaiyapuri. 2019. Identifying and benchmarking key features for cyber intrusion detection: An ensemble approach. IEEE Access 7: 106495–106513. https://doi.org/10.1109/ACCESS.2019.2929487 .
Biswas, R., and S. Roy. 2021. Botnet traffic identification using neural networks. Multimedia Tools and Applications . https://doi.org/10.1007/s11042-021-10765-8 .
Bouyeddou, B., F. Harrou, B. Kadri, and Y. Sun. 2021. Detecting network cyber-attacks using an integrated statistical approach. Cluster Computing—the Journal of Networks Software Tools and Applications 24 (2): 1435–1453. https://doi.org/10.1007/s10586-020-03203-1 .
Bozkir, A.S., and M. Aydos. 2020. LogoSENSE: A companion HOG based logo detection scheme for phishing web page and E-mail brand recognition. Computers & Security 95: 18. https://doi.org/10.1016/j.cose.2020.101855 .
Brower, D., and M. McCormick. 2021. Colonial pipeline resumes operations following ransomware attack. Financial Times .
Cai, H., F. Zhang, and A. Levi. 2019. An unsupervised method for detecting shilling attacks in recommender systems by mining item relationship and identifying target items. The Computer Journal 62 (4): 579–597. https://doi.org/10.1093/comjnl/bxy124 .
Cebula, J.J., M.E. Popeck, and L.R. Young. 2014. A Taxonomy of Operational Cyber Security Risks Version 2 .
Chadza, T., K.G. Kyriakopoulos, and S. Lambotharan. 2020. Learning to learn sequential network attacks using hidden Markov models. IEEE Access 8: 134480–134497. https://doi.org/10.1109/ACCESS.2020.3011293 .
Chatterjee, S., and S. Thekdi. 2020. An iterative learning and inference approach to managing dynamic cyber vulnerabilities of complex systems. Reliability Engineering and System Safety . https://doi.org/10.1016/j.ress.2019.106664 .
Chattopadhyay, M., R. Sen, and S. Gupta. 2018. A comprehensive review and meta-analysis on applications of machine learning techniques in intrusion detection. Australasian Journal of Information Systems 22: 27.
Chen, H.S., and J. Fiscus. 2018. The inhospitable vulnerability: A need for cybersecurity risk assessment in the hospitality industry. Journal of Hospitality and Tourism Technology 9 (2): 223–234. https://doi.org/10.1108/JHTT-07-2017-0044 .
Chhabra, G.S., V.P. Singh, and M. Singh. 2020. Cyber forensics framework for big data analytics in IoT environment using machine learning. Multimedia Tools and Applications 79 (23–24): 15881–15900. https://doi.org/10.1007/s11042-018-6338-1 .
Chiba, Z., N. Abghour, K. Moussaid, A. Elomri, and M. Rida. 2019. Intelligent approach to build a Deep Neural Network based IDS for cloud environment using combination of machine learning algorithms. Computers and Security 86: 291–317. https://doi.org/10.1016/j.cose.2019.06.013 .
Choras, M., and R. Kozik. 2015. Machine learning techniques applied to detect cyber attacks on web applications. Logic Journal of the IGPL 23 (1): 45–56. https://doi.org/10.1093/jigpal/jzu038 .
Chowdhury, S., M. Khanzadeh, R. Akula, F. Zhang, S. Zhang, H. Medal, M. Marufuzzaman, and L. Bian. 2017. Botnet detection using graph-based feature clustering. Journal of Big Data 4 (1): 14. https://doi.org/10.1186/s40537-017-0074-7 .
Cost Of A Cyber Incident: Systematic Review And Cross-Validation, Cybersecurity & Infrastructure Agency , 1, https://www.cisa.gov/sites/default/files/publications/CISA-OCE_Cost_of_Cyber_Incidents_Study-FINAL_508.pdf (2020).
D’Hooge, L., T. Wauters, B. Volckaert, and F. De Turck. 2019. Classification hardness for supervised learners on 20 years of intrusion detection data. IEEE Access 7: 167455–167469. https://doi.org/10.1109/access.2019.2953451 .
Damasevicius, R., A. Venckauskas, S. Grigaliunas, J. Toldinas, N. Morkevicius, T. Aleliunas, and P. Smuikys. 2020. LITNET-2020: An annotated real-world network flow dataset for network intrusion detection. Electronics 9 (5): 23. https://doi.org/10.3390/electronics9050800 .
De Giovanni, A.L.D., and M. Pirra. 2020. On the determinants of data breaches: A cointegration analysis. Decisions in Economics and Finance . https://doi.org/10.1007/s10203-020-00301-y .
Deng, L., D. Li, X. Yao, and H. Wang. 2019. Retracted Article: Mobile network intrusion detection for IoT system based on transfer learning algorithm. Cluster Computing 22 (4): 9889–9904. https://doi.org/10.1007/s10586-018-1847-2 .
Donkal, G., and G.K. Verma. 2018. A multimodal fusion based framework to reinforce IDS for securing Big Data environment using Spark. Journal of Information Security and Applications 43: 1–11. https://doi.org/10.1016/j.jisa.2018.10.001 .
Dunn, C., N. Moustafa, and B. Turnbull. 2020. Robustness evaluations of sustainable machine learning models against data Poisoning attacks in the Internet of Things. Sustainability 12 (16): 17. https://doi.org/10.3390/su12166434 .
Dwivedi, S., M. Vardhan, and S. Tripathi. 2021. Multi-parallel adaptive grasshopper optimization technique for detecting anonymous attacks in wireless networks. Wireless Personal Communications . https://doi.org/10.1007/s11277-021-08368-5 .
Dyson, B. 2020. COVID-19 crisis could be ‘watershed’ for cyber insurance, says Swiss Re exec. https://www.spglobal.com/marketintelligence/en/news-insights/latest-news-headlines/covid-19-crisis-could-be-watershed-for-cyber-insurance-says-swiss-re-exec-59197154 . Accessed 7 May 2020.
EIOPA. 2018. Understanding cyber insurance—a structured dialogue with insurance companies. https://www.eiopa.europa.eu/sites/default/files/publications/reports/eiopa_understanding_cyber_insurance.pdf . Accessed 28 May 2018
Elijah, A.V., A. Abdullah, N.Z. JhanJhi, M. Supramaniam, and O.B. Abdullateef. 2019. Ensemble and deep-learning methods for two-class and multi-attack anomaly intrusion detection: An empirical study. International Journal of Advanced Computer Science and Applications 10 (9): 520–528.
Eling, M., and K. Jung. 2018. Copula approaches for modeling cross-sectional dependence of data breach losses. Insurance Mathematics & Economics 82: 167–180. https://doi.org/10.1016/j.insmatheco.2018.07.003 .
Eling, M., and W. Schnell. 2016. What do we know about cyber risk and cyber risk insurance? Journal of Risk Finance 17 (5): 474–491. https://doi.org/10.1108/jrf-09-2016-0122 .
Eling, M., and J. Wirfs. 2019. What are the actual costs of cyber risk events? European Journal of Operational Research 272 (3): 1109–1119. https://doi.org/10.1016/j.ejor.2018.07.021 .
Eling, M. 2020. Cyber risk research in business and actuarial science. European Actuarial Journal 10 (2): 303–333.
Elmasry, W., A. Akbulut, and A.H. Zaim. 2019. Empirical study on multiclass classification-based network intrusion detection. Computational Intelligence 35 (4): 919–954. https://doi.org/10.1111/coin.12220 .
Elsaid, S.A., and N.S. Albatati. 2020. An optimized collaborative intrusion detection system for wireless sensor networks. Soft Computing 24 (16): 12553–12567. https://doi.org/10.1007/s00500-020-04695-0 .
Estepa, R., J.E. Díaz-Verdejo, A. Estepa, and G. Madinabeitia. 2020. How much training data is enough? A case study for HTTP anomaly-based intrusion detection. IEEE Access 8: 44410–44425. https://doi.org/10.1109/ACCESS.2020.2977591 .
European Council. 2021. Cybersecurity: how the EU tackles cyber threats. https://www.consilium.europa.eu/en/policies/cybersecurity/ . Accessed 10 May 2021
Falco, G. et al. 2019. Cyber risk research impeded by disciplinary barriers. Science (American Association for the Advancement of Science) 366 (6469): 1066–1069.
Fan, Z.J., Z.P. Tan, C.X. Tan, and X. Li. 2018. An improved integrated prediction method of cyber security situation based on spatial-time analysis. Journal of Internet Technology 19 (6): 1789–1800. https://doi.org/10.3966/160792642018111906015 .
Fang, Z.J., M.C. Xu, S.H. Xu, and T.Z. Hu. 2021. A framework for predicting data breach risk: Leveraging dependence to cope with sparsity. IEEE Transactions on Information Forensics and Security 16: 2186–2201. https://doi.org/10.1109/tifs.2021.3051804 .
Farkas, S., O. Lopez, and M. Thomas. 2021. Cyber claim analysis using Generalized Pareto regression trees with applications to insurance. Insurance: Mathematics and Economics 98: 92–105. https://doi.org/10.1016/j.insmatheco.2021.02.009 .
Farsi, H., A. Fanian, and Z. Taghiyarrenani. 2019. A novel online state-based anomaly detection system for process control networks. International Journal of Critical Infrastructure Protection 27: 11. https://doi.org/10.1016/j.ijcip.2019.100323 .
Ferrag, M.A., L. Maglaras, S. Moschoyiannis, and H. Janicke. 2020. Deep learning for cyber security intrusion detection: Approaches, datasets, and comparative study. Journal of Information Security and Applications 50: 19. https://doi.org/10.1016/j.jisa.2019.102419 .
Field, M. 2018. WannaCry cyber attack cost the NHS £92m as 19,000 appointments cancelled. https://www.telegraph.co.uk/technology/2018/10/11/wannacry-cyber-attack-cost-nhs-92m-19000-appointments-cancelled/ . Accessed 9 May 2018.
FitchRatings. 2021. U.S. Cyber Insurance Market Update (Spike in Claims Leads to Decline in 2020 Underwriting Performance). https://www.fitchratings.com/research/insurance/us-cyber-insurance-market-update-spike-in-claims-leads-to-decline-in-2020-underwriting-performance-26-05-2021 .
Fossaceca, J.M., T.A. Mazzuchi, and S. Sarkani. 2015. MARK-ELM: Application of a novel Multiple Kernel Learning framework for improving the robustness of network intrusion detection. Expert Systems with Applications 42 (8): 4062–4080. https://doi.org/10.1016/j.eswa.2014.12.040 .
Franke, U., and J. Brynielsson. 2014. Cyber situational awareness–a systematic review of the literature. Computers & security 46: 18–31.
Freeha, K., K.J. Hwan, M. Lars, and M. Robin. 2021. Data breach management: An integrated risk model. Information & Management 58 (1): 103392. https://doi.org/10.1016/j.im.2020.103392 .
Ganeshan, R., and P. Rodrigues. 2020. Crow-AFL: Crow based adaptive fractional lion optimization approach for the intrusion detection. Wireless Personal Communications 111 (4): 2065–2089. https://doi.org/10.1007/s11277-019-06972-0 .
GAO. 2021. CYBER INSURANCE—Insurers and policyholders face challenges in an evolving market. https://www.gao.gov/assets/gao-21-477.pdf . Accessed 16 May 2021.
Garber, J. 2021. Colonial Pipeline fiasco foreshadows impact of Biden energy policy. https://www.foxbusiness.com/markets/colonial-pipeline-fiasco-foreshadows-impact-of-biden-energy-policy . Accessed 4 May 2021.
Gauthama Raman, M.R., N. Somu, S. Jagarapu, T. Manghnani, T. Selvam, K. Krithivasan, and V.S. Shankar Sriram. 2020. An efficient intrusion detection technique based on support vector machine and improved binary gravitational search algorithm. Artificial Intelligence Review 53 (5): 3255–3286. https://doi.org/10.1007/s10462-019-09762-z .
Gavel, S., A.S. Raghuvanshi, and S. Tiwari. 2021. Distributed intrusion detection scheme using dual-axis dimensionality reduction for Internet of things (IoT). Journal of Supercomputing . https://doi.org/10.1007/s11227-021-03697-5 .
GDPR.EU. 2021. FAQ. https://gdpr.eu/faq/ . Accessed 10 May 2021.
Georgescu, T.M., B. Iancu, and M. Zurini. 2019. Named-entity-recognition-based automated system for diagnosing cybersecurity situations in IoT networks. Sensors (switzerland) . https://doi.org/10.3390/s19153380 .
Giudici, P., and E. Raffinetti. 2020. Cyber risk ordering with rank-based statistical models. AStA Advances in Statistical Analysis . https://doi.org/10.1007/s10182-020-00387-0 .
Goh, J., S. Adepu, K.N. Junejo, and A. Mathur. 2016. A dataset to support research in the design of secure water treatment systems. In CRITIS.
Gong, X.Y., J.L. Lu, Y.F. Zhou, H. Qiu, and R. He. 2021. Model uncertainty based annotation error fixing for web attack detection. Journal of Signal Processing Systems for Signal Image and Video Technology 93 (2–3): 187–199. https://doi.org/10.1007/s11265-019-01494-1 .
Goode, S., H. Hoehle, V. Venkatesh, and S.A. Brown. 2017. USER compensation as a data breach recovery action: An investigation of the sony playstation network breach. MIS Quarterly 41 (3): 703–727.
Guo, H., S. Huang, C. Huang, Z. Pan, M. Zhang, and F. Shi. 2020. File entropy signal analysis combined with wavelet decomposition for malware classification. IEEE Access 8: 158961–158971. https://doi.org/10.1109/ACCESS.2020.3020330 .
Habib, M., I. Aljarah, and H. Faris. 2020. A Modified multi-objective particle swarm optimizer-based Lévy flight: An approach toward intrusion detection in Internet of Things. Arabian Journal for Science and Engineering 45 (8): 6081–6108. https://doi.org/10.1007/s13369-020-04476-9 .
Hajj, S., R. El Sibai, J.B. Abdo, J. Demerjian, A. Makhoul, and C. Guyeux. 2021. Anomaly-based intrusion detection systems: The requirements, methods, measurements, and datasets. Transactions on Emerging Telecommunications Technologies 32 (4): 36. https://doi.org/10.1002/ett.4240 .
Heartfield, R., G. Loukas, A. Bezemskij, and E. Panaousis. 2021. Self-configurable cyber-physical intrusion detection for smart homes using reinforcement learning. IEEE Transactions on Information Forensics and Security 16: 1720–1735. https://doi.org/10.1109/tifs.2020.3042049 .
Hemo, B., T. Gafni, K. Cohen, and Q. Zhao. 2020. Searching for anomalies over composite hypotheses. IEEE Transactions on Signal Processing 68: 1181–1196. https://doi.org/10.1109/TSP.2020.2971438
Hindy, H., D. Brosset, E. Bayne, A.K. Seeam, C. Tachtatzis, R. Atkinson, and X. Bellekens. 2020. A taxonomy of network threats and the effect of current datasets on intrusion detection systems. IEEE Access 8: 104650–104675. https://doi.org/10.1109/ACCESS.2020.3000179 .
Hong, W., D. Huang, C. Chen, and J. Lee. 2020. Towards accurate and efficient classification of power system contingencies and cyber-attacks using recurrent neural networks. IEEE Access 8: 123297–123309. https://doi.org/10.1109/ACCESS.2020.3007609 .
Husák, M., M. Zádník, V. Bartos, and P. Sokol. 2020. Dataset of intrusion detection alerts from a sharing platform. Data in Brief 33: 106530.
IBM Security. 2020. Cost of a Data breach Report. https://www.capita.com/sites/g/files/nginej291/files/2020-08/Ponemon-Global-Cost-of-Data-Breach-Study-2020.pdf . Accessed 19 May 2021.
IEEE. 2021. IEEE Quick Facts. https://www.ieee.org/about/at-a-glance.html . Accessed 11 May 2021.
Kilincer, I.F., F. Ertam, and S. Abdulkadir. 2021. Machine learning methods for cyber security intrusion detection: Datasets and comparative study. Computer Networks 188: 107840. https://doi.org/10.1016/j.comnet.2021.107840 .
Jaber, A.N., and S. Ul Rehman. 2020. FCM-SVM based intrusion detection system for cloud computing environment. Cluster Computing—the Journal of Networks Software Tools and Applications 23 (4): 3221–3231. https://doi.org/10.1007/s10586-020-03082-6 .
Jacobs, J., S. Romanosky, B. Edwards, M. Roytman, and I. Adjerid. 2019. Exploit prediction scoring system (epss). arXiv:1908.04856
Jacobsen, A. et al. 2020. FAIR principles: Interpretations and implementation considerations. Data Intelligence 2 (1–2): 10–29. https://doi.org/10.1162/dint_r_00024 .
Jahromi, A.N., S. Hashemi, A. Dehghantanha, R.M. Parizi, and K.K.R. Choo. 2020. An enhanced stacked LSTM method with no random initialization for malware threat hunting in safety and time-critical systems. IEEE Transactions on Emerging Topics in Computational Intelligence 4 (5): 630–640. https://doi.org/10.1109/TETCI.2019.2910243 .
Jang, S., S. Li, and Y. Sung. 2020. FastText-based local feature visualization algorithm for merged image-based malware classification framework for cyber security and cyber defense. Mathematics 8 (3): 13. https://doi.org/10.3390/math8030460 .
Javeed, D., T.H. Gao, and M.T. Khan. 2021. SDN-enabled hybrid DL-driven framework for the detection of emerging cyber threats in IoT. Electronics 10 (8): 16. https://doi.org/10.3390/electronics10080918 .
Johnson, P., D. Gorton, R. Lagerstrom, and M. Ekstedt. 2016. Time between vulnerability disclosures: A measure of software product vulnerability. Computers & Security 62: 278–295. https://doi.org/10.1016/j.cose.2016.08.004 .
Johnson, P., R. Lagerström, M. Ekstedt, and U. Franke. 2018. Can the common vulnerability scoring system be trusted? A Bayesian analysis. IEEE Transactions on Dependable and Secure Computing 15 (6): 1002–1015. https://doi.org/10.1109/TDSC.2016.2644614 .
Junger, M., V. Wang, and M. Schlömer. 2020. Fraud against businesses both online and offline: Crime scripts, business characteristics, efforts, and benefits. Crime Science 9 (1): 13. https://doi.org/10.1186/s40163-020-00119-4 .
Kalutarage, H.K., H.N. Nguyen, and S.A. Shaikh. 2017. Towards a threat assessment framework for apps collusion. Telecommunication Systems 66 (3): 417–430. https://doi.org/10.1007/s11235-017-0296-1 .
Kamarudin, M.H., C. Maple, T. Watson, and N.S. Safa. 2017. A LogitBoost-based algorithm for detecting known and unknown web attacks. IEEE Access 5: 26190–26200. https://doi.org/10.1109/ACCESS.2017.2766844 .
Kasongo, S.M., and Y.X. Sun. 2020. A deep learning method with wrapper based feature extraction for wireless intrusion detection system. Computers & Security 92: 15. https://doi.org/10.1016/j.cose.2020.101752 .
Keserwani, P.K., M.C. Govil, E.S. Pilli, and P. Govil. 2021. A smart anomaly-based intrusion detection system for the Internet of Things (IoT) network using GWO–PSO–RF model. Journal of Reliable Intelligent Environments 7 (1): 3–21. https://doi.org/10.1007/s40860-020-00126-x .
Keshk, M., E. Sitnikova, N. Moustafa, J. Hu, and I. Khalil. 2021. An integrated framework for privacy-preserving based anomaly detection for cyber-physical systems. IEEE Transactions on Sustainable Computing 6 (1): 66–79. https://doi.org/10.1109/TSUSC.2019.2906657 .
Khan, I.A., D.C. Pi, A.K. Bhatia, N. Khan, W. Haider, and A. Wahab. 2020. Generating realistic IoT-based IDS dataset centred on fuzzy qualitative modelling for cyber-physical systems. Electronics Letters 56 (9): 441–443. https://doi.org/10.1049/el.2019.4158 .
Khraisat, A., I. Gondal, P. Vamplew, J. Kamruzzaman, and A. Alazab. 2020. Hybrid intrusion detection system based on the stacking ensemble of C5 decision tree classifier and one class support vector machine. Electronics 9 (1): 18. https://doi.org/10.3390/electronics9010173 .
Khraisat, A., I. Gondal, P. Vamplew, and J. Kamruzzaman. 2019. Survey of intrusion detection systems: Techniques, datasets and challenges. Cybersecurity 2 (1): 20. https://doi.org/10.1186/s42400-019-0038-7 .
Kilincer, I.F., F. Ertam, and A. Sengur. 2021. Machine learning methods for cyber security intrusion detection: Datasets and comparative study. Computer Networks 188: 16. https://doi.org/10.1016/j.comnet.2021.107840 .
Kim, D., and H.K. Kim. 2019. Automated dataset generation system for collaborative research of cyber threat analysis. Security and Communication Networks 2019: 10. https://doi.org/10.1155/2019/6268476 .
Kim, G., C. Lee, J. Jo, and H. Lim. 2020. Automatic extraction of named entities of cyber threats using a deep Bi-LSTM-CRF network. International Journal of Machine Learning and Cybernetics 11 (10): 2341–2355. https://doi.org/10.1007/s13042-020-01122-6 .
Kirubavathi, G., and R. Anitha. 2016. Botnet detection via mining of traffic flow characteristics. Computers & Electrical Engineering 50: 91–101. https://doi.org/10.1016/j.compeleceng.2016.01.012 .
Kiwia, D., A. Dehghantanha, K.K.R. Choo, and J. Slaughter. 2018. A cyber kill chain based taxonomy of banking Trojans for evolutionary computational intelligence. Journal of Computational Science 27: 394–409. https://doi.org/10.1016/j.jocs.2017.10.020 .
Koroniotis, N., N. Moustafa, and E. Sitnikova. 2020. A new network forensic framework based on deep learning for Internet of Things networks: A particle deep framework. Future Generation Computer Systems 110: 91–106. https://doi.org/10.1016/j.future.2020.03.042 .
Kruse, C.S., B. Frederick, T. Jacobson, and D. Kyle Monticone. 2017. Cybersecurity in healthcare: A systematic review of modern threats and trends. Technology and Health Care 25 (1): 1–10.
Kshetri, N. 2018. The economics of cyber-insurance. IT Professional 20 (6): 9–14. https://doi.org/10.1109/MITP.2018.2874210 .
Kumar, R., P. Kumar, R. Tripathi, G.P. Gupta, T.R. Gadekallu, and G. Srivastava. 2021. SP2F: A secured privacy-preserving framework for smart agricultural Unmanned Aerial Vehicles. Computer Networks . https://doi.org/10.1016/j.comnet.2021.107819 .
Kumar, R., and R. Tripathi. 2021. DBTP2SF: A deep blockchain-based trustworthy privacy-preserving secured framework in industrial internet of things systems. Transactions on Emerging Telecommunications Technologies 32 (4): 27. https://doi.org/10.1002/ett.4222 .
Laso, P.M., D. Brosset, and J. Puentes. 2017. Dataset of anomalies and malicious acts in a cyber-physical subsystem. Data in Brief 14: 186–191. https://doi.org/10.1016/j.dib.2017.07.038 .
Lee, J., J. Kim, I. Kim, and K. Han. 2019. Cyber threat detection based on artificial neural networks using event profiles. IEEE Access 7: 165607–165626. https://doi.org/10.1109/ACCESS.2019.2953095 .
Lee, S.J., P.D. Yoo, A.T. Asyhari, Y. Jhi, L. Chermak, C.Y. Yeun, and K. Taha. 2020. IMPACT: Impersonation attack detection via edge computing using deep Autoencoder and feature abstraction. IEEE Access 8: 65520–65529. https://doi.org/10.1109/ACCESS.2020.2985089 .
Leong, Y.-Y., and Y.-C. Chen. 2020. Cyber risk cost and management in IoT devices-linked health insurance. The Geneva Papers on Risk and Insurance—Issues and Practice 45 (4): 737–759. https://doi.org/10.1057/s41288-020-00169-4 .
Levi, M. 2017. Assessing the trends, scale and nature of economic cybercrimes: overview and Issues: In Cybercrimes, cybercriminals and their policing, in crime, law and social change. Crime, Law and Social Change 67 (1): 3–20. https://doi.org/10.1007/s10611-016-9645-3 .
Li, C., K. Mills, D. Niu, R. Zhu, H. Zhang, and H. Kinawi. 2019a. Android malware detection based on factorization machine. IEEE Access 7: 184008–184019. https://doi.org/10.1109/ACCESS.2019.2958927 .
Li, D.Q., and Q.M. Li. 2020. Adversarial deep ensemble: evasion attacks and defenses for malware detection. IEEE Transactions on Information Forensics and Security 15: 3886–3900. https://doi.org/10.1109/tifs.2020.3003571 .
Li, D.Q., Q.M. Li, Y.F. Ye, and S.H. Xu. 2021. A framework for enhancing deep neural networks against adversarial malware. IEEE Transactions on Network Science and Engineering 8 (1): 736–750. https://doi.org/10.1109/tnse.2021.3051354 .
Li, R.H., C. Zhang, C. Feng, X. Zhang, and C.J. Tang. 2019b. Locating vulnerability in binaries using deep neural networks. IEEE Access 7: 134660–134676. https://doi.org/10.1109/access.2019.2942043 .
Li, X., M. Xu, P. Vijayakumar, N. Kumar, and X. Liu. 2020. Detection of low-frequency and multi-stage attacks in industrial Internet of Things. IEEE Transactions on Vehicular Technology 69 (8): 8820–8831. https://doi.org/10.1109/TVT.2020.2995133 .
Liu, H.Y., and B. Lang. 2019. Machine learning and deep learning methods for intrusion detection systems: A survey. Applied Sciences—Basel 9 (20): 28. https://doi.org/10.3390/app9204396 .
Lopez-Martin, M., B. Carro, and A. Sanchez-Esguevillas. 2020. Application of deep reinforcement learning to intrusion detection for supervised problems. Expert Systems with Applications . https://doi.org/10.1016/j.eswa.2019.112963 .
Loukas, G., D. Gan, and Tuan Vuong. 2013. A review of cyber threats and defence approaches in emergency management. Future Internet 5: 205–236.
Luo, C.C., S. Su, Y.B. Sun, Q.J. Tan, M. Han, and Z.H. Tian. 2020. A convolution-based system for malicious URLs detection. CMC—Computers Materials Continua 62 (1): 399–411.
Mahbooba, B., M. Timilsina, R. Sahal, and M. Serrano. 2021. Explainable artificial intelligence (XAI) to enhance trust management in intrusion detection systems using decision tree model. Complexity 2021: 11. https://doi.org/10.1155/2021/6634811 .
Mahdavifar, S., and A.A. Ghorbani. 2020. DeNNeS: Deep embedded neural network expert system for detecting cyber attacks. Neural Computing & Applications 32 (18): 14753–14780. https://doi.org/10.1007/s00521-020-04830-w .
Mahfouz, A., A. Abuhussein, D. Venugopal, and S. Shiva. 2020. Ensemble classifiers for network intrusion detection using a novel network attack dataset. Future Internet 12 (11): 1–19. https://doi.org/10.3390/fi12110180 .
Maleks Smith, Z., E. Lostri, and J.A. Lewis. 2020. The hidden costs of cybercrime. https://www.mcafee.com/enterprise/en-us/assets/reports/rp-hidden-costs-of-cybercrime.pdf . Accessed 16 May 2021.
Malik, J., A. Akhunzada, I. Bibi, M. Imran, A. Musaddiq, and S.W. Kim. 2020. Hybrid deep learning: An efficient reconnaissance and surveillance detection mechanism in SDN. IEEE Access 8: 134695–134706. https://doi.org/10.1109/ACCESS.2020.3009849 .
Manimurugan, S. 2020. IoT-Fog-Cloud model for anomaly detection using improved Naive Bayes and principal component analysis. Journal of Ambient Intelligence and Humanized Computing . https://doi.org/10.1007/s12652-020-02723-3 .
Martin, A., R. Lara-Cabrera, and D. Camacho. 2019. Android malware detection through hybrid features fusion and ensemble classifiers: The AndroPyTool framework and the OmniDroid dataset. Information Fusion 52: 128–142. https://doi.org/10.1016/j.inffus.2018.12.006 .
Mauro, M.D., G. Galatro, and A. Liotta. 2020. Experimental review of neural-based approaches for network intrusion management. IEEE Transactions on Network and Service Management 17 (4): 2480–2495. https://doi.org/10.1109/TNSM.2020.3024225 .
McLeod, A., and D. Dolezel. 2018. Cyber-analytics: Modeling factors associated with healthcare data breaches. Decision Support Systems 108: 57–68. https://doi.org/10.1016/j.dss.2018.02.007 .
Meira, J., R. Andrade, I. Praca, J. Carneiro, V. Bolon-Canedo, A. Alonso-Betanzos, and G. Marreiros. 2020. Performance evaluation of unsupervised techniques in cyber-attack anomaly detection. Journal of Ambient Intelligence and Humanized Computing 11 (11): 4477–4489. https://doi.org/10.1007/s12652-019-01417-9 .
Miao, Y., J. Ma, X. Liu, J. Weng, H. Li, and H. Li. 2019. Lightweight fine-grained search over encrypted data in Fog computing. IEEE Transactions on Services Computing 12 (5): 772–785. https://doi.org/10.1109/TSC.2018.2823309 .
Miller, C., and C. Valasek. 2015. Remote exploitation of an unaltered passenger vehicle. Black Hat USA 2015 (S 91).
Mireles, J.D., E. Ficke, J.H. Cho, P. Hurley, and S.H. Xu. 2019. Metrics towards measuring cyber agility. IEEE Transactions on Information Forensics and Security 14 (12): 3217–3232. https://doi.org/10.1109/tifs.2019.2912551 .
Mishra, N., and S. Pandya. 2021. Internet of Things applications, security challenges, attacks, intrusion detection, and future visions: A systematic review. IEEE Access . https://doi.org/10.1109/ACCESS.2021.3073408 .
Monshizadeh, M., V. Khatri, B.G. Atli, R. Kantola, and Z. Yan. 2019. Performance evaluation of a combined anomaly detection platform. IEEE Access 7: 100964–100978. https://doi.org/10.1109/ACCESS.2019.2930832 .
Moreno, V.C., G. Reniers, E. Salzano, and V. Cozzani. 2018. Analysis of physical and cyber security-related events in the chemical and process industry. Process Safety and Environmental Protection 116: 621–631. https://doi.org/10.1016/j.psep.2018.03.026 .
Moro, E.D. 2020. Towards an economic cyber loss index for parametric cover based on IT security indicator: A preliminary analysis. Risks . https://doi.org/10.3390/risks8020045 .
Moustafa, N., E. Adi, B. Turnbull, and J. Hu. 2018. A new threat intelligence scheme for safeguarding industry 4.0 systems. IEEE Access 6: 32910–32924. https://doi.org/10.1109/ACCESS.2018.2844794 .
Moustakidis, S., and P. Karlsson. 2020. A novel feature extraction methodology using Siamese convolutional neural networks for intrusion detection. Cybersecurity . https://doi.org/10.1186/s42400-020-00056-4 .
Mukhopadhyay, A., S. Chatterjee, K.K. Bagchi, P.J. Kirs, and G.K. Shukla. 2019. Cyber Risk Assessment and Mitigation (CRAM) framework using Logit and Probit models for cyber insurance. Information Systems Frontiers 21 (5): 997–1018. https://doi.org/10.1007/s10796-017-9808-5 .
Murphey, H. 2021a. Biden signs executive order to strengthen US cyber security. https://www.ft.com/content/4d808359-b504-4014-85f6-68e7a2851bf1?accessToken=zwAAAXl0_ifgkc9NgINZtQRAFNOF9mjnooUb8Q.MEYCIQDw46SFWsMn1iyuz3kvgAmn6mxc0rIVfw10Lg1ovJSfJwIhAK2X2URzfSqHwIS7ddRCvSt2nGC2DcdoiDTG49-4TeEt&sharetype=gift?token=fbcd6323-1ecf-4fc3-b136-b5b0dd6a8756 . Accessed 7 May 2021.
Murphey, H. 2021b. Millions of connected devices have security flaws, study shows. https://www.ft.com/content/0bf92003-926d-4dee-87d7-b01f7c3e9621?accessToken=zwAAAXnA7f2Ikc8L-SADkm1N7tOH17AffD6WIQ.MEQCIDjBuROvhmYV0Mx3iB0cEV7m5oND1uaCICxJu0mzxM0PAiBam98q9zfHiTB6hKGr1gGl0Azt85yazdpX9K5sI8se3Q&sharetype=gift?token=2538218d-77d9-4dd3-9649-3cb556a34e51 . Accessed 6 May 2021.
Murugesan, V., M. Shalinie, and M.H. Yang. 2018. Design and analysis of hybrid single packet IP traceback scheme. IET Networks 7 (3): 141–151. https://doi.org/10.1049/iet-net.2017.0115 .
Mwitondi, K.S., and S.A. Zargari. 2018. An iterative multiple sampling method for intrusion detection. Information Security Journal 27 (4): 230–239. https://doi.org/10.1080/19393555.2018.1539790 .
Neto, N.N., S. Madnick, A.M.G. De Paula, and N.M. Borges. 2021. Developing a global data breach database and the challenges encountered. ACM Journal of Data and Information Quality 13 (1): 33. https://doi.org/10.1145/3439873 .
Nurse, J.R.C., L. Axon, A. Erola, I. Agrafiotis, M. Goldsmith, and S. Creese. 2020. The data that drives cyber insurance: A study into the underwriting and claims processes. In 2020 International conference on cyber situational awareness, data analytics and assessment (CyberSA), 15–19 June 2020.
Oliveira, N., I. Praca, E. Maia, and O. Sousa. 2021. Intelligent cyber attack detection and classification for network-based intrusion detection systems. Applied Sciences—Basel 11 (4): 21. https://doi.org/10.3390/app11041674 .
Page, M.J. et al. 2021. The PRISMA 2020 statement: An updated guideline for reporting systematic reviews. Systematic Reviews 10 (1): 89. https://doi.org/10.1186/s13643-021-01626-4 .
Pajouh, H.H., R. Javidan, R. Khayami, A. Dehghantanha, and K.R. Choo. 2019. A two-layer dimension reduction and two-tier classification model for anomaly-based intrusion detection in IoT backbone networks. IEEE Transactions on Emerging Topics in Computing 7 (2): 314–323. https://doi.org/10.1109/TETC.2016.2633228 .
Parra, G.D., P. Rad, K.K.R. Choo, and N. Beebe. 2020. Detecting Internet of Things attacks using distributed deep learning. Journal of Network and Computer Applications 163: 13. https://doi.org/10.1016/j.jnca.2020.102662 .
Paté-Cornell, M.E., M. Kuypers, M. Smith, and P. Keller. 2018. Cyber risk management for critical infrastructure: A risk analysis model and three case studies. Risk Analysis 38 (2): 226–241. https://doi.org/10.1111/risa.12844 .
Pooser, D.M., M.J. Browne, and O. Arkhangelska. 2018. Growth in the perception of cyber risk: evidence from U.S. P&C Insurers. The Geneva Papers on Risk and Insurance—Issues and Practice 43 (2): 208–223. https://doi.org/10.1057/s41288-017-0077-9 .
Pu, G., L. Wang, J. Shen, and F. Dong. 2021. A hybrid unsupervised clustering-based anomaly detection method. Tsinghua Science and Technology 26 (2): 146–153. https://doi.org/10.26599/TST.2019.9010051 .
Qiu, J., W. Luo, L. Pan, Y. Tai, J. Zhang, and Y. Xiang. 2019. Predicting the impact of android malicious samples via machine learning. IEEE Access 7: 66304–66316. https://doi.org/10.1109/ACCESS.2019.2914311 .
Qu, X., L. Yang, K. Guo, M. Sun, L. Ma, T. Feng, S. Ren, K. Li, and X. Ma. 2020. Direct batch growth hierarchical self-organizing mapping based on statistics for efficient network intrusion detection. IEEE Access 8: 42251–42260. https://doi.org/10.1109/ACCESS.2020.2976810 .
Rahman, Md.S., S. Halder, Md. Ashraf Uddin, and U.K. Acharjee. 2021. An efficient hybrid system for anomaly detection in social networks. Cybersecurity 4 (1): 10. https://doi.org/10.1186/s42400-021-00074-w .
Ramaiah, M., V. Chandrasekaran, V. Ravi, and N. Kumar. 2021. An intrusion detection system using optimized deep neural network architecture. Transactions on Emerging Telecommunications Technologies 32 (4): 17. https://doi.org/10.1002/ett.4221 .
Raman, M.R.G., K. Kannan, S.K. Pal, and V.S.S. Sriram. 2016. Rough set-hypergraph-based feature selection approach for intrusion detection systems. Defence Science Journal 66 (6): 612–617. https://doi.org/10.14429/dsj.66.10802 .
Rathore, S., J.H. Park. 2018. Semi-supervised learning based distributed attack detection framework for IoT. Applied Soft Computing 72: 79–89. https://doi.org/10.1016/j.asoc.2018.05.049 .
Romanosky, S., L. Ablon, A. Kuehn, and T. Jones. 2019. Content analysis of cyber insurance policies: How do carriers price cyber risk? Journal of Cybersecurity (oxford) 5 (1): tyz002.
Sarabi, A., P. Naghizadeh, Y. Liu, and M. Liu. 2016. Risky business: Fine-grained data breach prediction using business profiles. Journal of Cybersecurity 2 (1): 15–28. https://doi.org/10.1093/cybsec/tyw004 .
Sardi, Alberto, Alessandro Rizzi, Enrico Sorano, and Anna Guerrieri. 2021. Cyber risk in health facilities: A systematic literature review. Sustainability 12 (17): 7002.
Sarker, Iqbal H., A.S.M. Kayes, Shahriar Badsha, Hamed Alqahtani, Paul Watters, and Alex Ng. 2020. Cybersecurity data science: An overview from machine learning perspective. Journal of Big Data 7 (1): 41. https://doi.org/10.1186/s40537-020-00318-5 .
Scopus. 2021. Factsheet. https://www.elsevier.com/__data/assets/pdf_file/0017/114533/Scopus_GlobalResearch_Factsheet2019_FINAL_WEB.pdf . Accessed 11 May 2021.
Sentuna, A., A. Alsadoon, P.W.C. Prasad, M. Saadeh, and O.H. Alsadoon. 2021. A novel Enhanced Naïve Bayes Posterior Probability (ENBPP) using machine learning: Cyber threat analysis. Neural Processing Letters 53 (1): 177–209. https://doi.org/10.1007/s11063-020-10381-x .
Shaukat, K., S.H. Luo, V. Varadharajan, I.A. Hameed, S. Chen, D.X. Liu, and J.M. Li. 2020. Performance comparison and current challenges of using machine learning techniques in cybersecurity. Energies 13 (10): 27. https://doi.org/10.3390/en13102509 .
Sheehan, B., F. Murphy, M. Mullins, and C. Ryan. 2019. Connected and autonomous vehicles: A cyber-risk classification framework. Transportation Research Part a: Policy and Practice 124: 523–536. https://doi.org/10.1016/j.tra.2018.06.033 .
Sheehan, B., F. Murphy, A.N. Kia, and R. Kiely. 2021. A quantitative bow-tie cyber risk classification and assessment framework. Journal of Risk Research 24 (12): 1619–1638.
Shlomo, A., M. Kalech, and R. Moskovitch. 2021. Temporal pattern-based malicious activity detection in SCADA systems. Computers & Security 102: 17. https://doi.org/10.1016/j.cose.2020.102153 .
Singh, K.J., and T. De. 2020. Efficient classification of DDoS attacks using an ensemble feature selection algorithm. Journal of Intelligent Systems 29 (1): 71–83. https://doi.org/10.1515/jisys-2017-0472 .
Skrjanc, I., S. Ozawa, T. Ban, and D. Dovzan. 2018. Large-scale cyber attacks monitoring using Evolving Cauchy Possibilistic Clustering. Applied Soft Computing 62: 592–601. https://doi.org/10.1016/j.asoc.2017.11.008 .
Smart, W. 2018. Lessons learned review of the WannaCry Ransomware Cyber Attack. https://www.england.nhs.uk/wp-content/uploads/2018/02/lessons-learned-review-wannacry-ransomware-cyber-attack-cio-review.pdf . Accessed 7 May 2021.
Sornette, D., T. Maillart, and W. Kröger. 2013. Exploring the limits of safety analysis in complex technological systems. International Journal of Disaster Risk Reduction 6: 59–66. https://doi.org/10.1016/j.ijdrr.2013.04.002 .
Sovacool, B.K. 2008. The costs of failure: A preliminary assessment of major energy accidents, 1907–2007. Energy Policy 36 (5): 1802–1820. https://doi.org/10.1016/j.enpol.2008.01.040 .
SpringerLink. 2021. Journal Search. https://rd.springer.com/search?facet-content-type=%22Journal%22 . Accessed 11 May 2021.
Stojanovic, B., K. Hofer-Schmitz, and U. Kleb. 2020. APT datasets and attack modeling for automated detection methods: A review. Computers & Security 92: 19. https://doi.org/10.1016/j.cose.2020.101734 .
Subroto, A., and A. Apriyana. 2019. Cyber risk prediction through social media big data analytics and statistical machine learning. Journal of Big Data . https://doi.org/10.1186/s40537-019-0216-1 .
Tan, Z., A. Jamdagni, X. He, P. Nanda, R.P. Liu, and J. Hu. 2015. Detection of denial-of-service attacks based on computer vision techniques. IEEE Transactions on Computers 64 (9): 2519–2533. https://doi.org/10.1109/TC.2014.2375218 .
Tidy, J. 2021. Irish cyber-attack: Hackers bail out Irish health service for free. https://www.bbc.com/news/world-europe-57197688 . Accessed 6 May 2021.
Tuncer, T., F. Ertam, and S. Dogan. 2020. Automated malware recognition method based on local neighborhood binary pattern. Multimedia Tools and Applications 79 (37–38): 27815–27832. https://doi.org/10.1007/s11042-020-09376-6 .
Uhm, Y., and W. Pak. 2021. Service-aware two-level partitioning for machine learning-based network intrusion detection with high performance and high scalability. IEEE Access 9: 6608–6622. https://doi.org/10.1109/ACCESS.2020.3048900 .
Ulven, J.B., and G. Wangen. 2021. A systematic review of cybersecurity risks in higher education. Future Internet 13 (2): 1–40. https://doi.org/10.3390/fi13020039 .
Vaccari, I., G. Chiola, M. Aiello, M. Mongelli, and E. Cambiaso. 2020. MQTTset, a new dataset for machine learning techniques on MQTT. Sensors 20 (22): 17. https://doi.org/10.3390/s20226578 .
Valeriano, B., and R.C. Maness. 2014. The dynamics of cyber conflict between rival antagonists, 2001–11. Journal of Peace Research 51 (3): 347–360. https://doi.org/10.1177/0022343313518940 .
Varghese, J.E., and B. Muniyal. 2021. An Efficient IDS framework for DDoS attacks in SDN environment. IEEE Access 9: 69680–69699. https://doi.org/10.1109/ACCESS.2021.3078065 .
Varsha, M. V., P. Vinod, K.A. Dhanya. 2017 Identification of malicious android app using manifest and opcode features. Journal of Computer Virology and Hacking Techniques 13 (2): 125–138. https://doi.org/10.1007/s11416-016-0277-z
Velliangiri, S., and H.M. Pandey. 2020. Fuzzy-Taylor-elephant herd optimization inspired Deep Belief Network for DDoS attack detection and comparison with state-of-the-arts algorithms. Future Generation Computer Systems—the International Journal of Escience 110: 80–90. https://doi.org/10.1016/j.future.2020.03.049 .
Verma, A., and V. Ranga. 2020. Machine learning based intrusion detection systems for IoT applications. Wireless Personal Communications 111 (4): 2287–2310. https://doi.org/10.1007/s11277-019-06986-8 .
Vidros, S., C. Kolias, G. Kambourakis, and L. Akoglu. 2017. Automatic detection of online recruitment frauds: Characteristics, methods, and a public dataset. Future Internet 9 (1): 19. https://doi.org/10.3390/fi9010006 .
Vinayakumar, R., M. Alazab, K.P. Soman, P. Poornachandran, A. Al-Nemrat, and S. Venkatraman. 2019. Deep learning approach for intelligent intrusion detection system. IEEE Access 7: 41525–41550. https://doi.org/10.1109/access.2019.2895334 .
Walker-Roberts, S., M. Hammoudeh, O. Aldabbas, M. Aydin, and A. Dehghantanha. 2020. Threats on the horizon: Understanding security threats in the era of cyber-physical systems. Journal of Supercomputing 76 (4): 2643–2664. https://doi.org/10.1007/s11227-019-03028-9 .
Web of Science. 2021. Web of Science: Science Citation Index Expanded. https://clarivate.com/webofsciencegroup/solutions/webofscience-scie/ . Accessed 11 May 2021.
World Economic Forum. 2020. WEF Global Risk Report. http://www3.weforum.org/docs/WEF_Global_Risk_Report_2020.pdf . Accessed 13 May 2020.
Xin, Y., L. Kong, Z. Liu, Y. Chen, Y. Li, H. Zhu, M. Gao, H. Hou, and C. Wang. 2018. Machine learning and deep learning methods for cybersecurity. IEEE Access 6: 35365–35381. https://doi.org/10.1109/ACCESS.2018.2836950 .
Xu, C., J. Zhang, K. Chang, and C. Long. 2013. Uncovering collusive spammers in Chinese review websites. In Proceedings of the 22nd ACM international conference on Information & Knowledge Management.
Yang, J., T. Li, G. Liang, W. He, and Y. Zhao. 2019. A Simple recurrent unit model based intrusion detection system with DCGAN. IEEE Access 7: 83286–83296. https://doi.org/10.1109/ACCESS.2019.2922692 .
Yuan, B.G., J.F. Wang, D. Liu, W. Guo, P. Wu, and X.H. Bao. 2020. Byte-level malware classification based on Markov images and deep learning. Computers & Security 92: 12. https://doi.org/10.1016/j.cose.2020.101740 .
Zhang, S., X.M. Ou, and D. Caragea. 2015. Predicting cyber risks through national vulnerability database. Information Security Journal 24 (4–6): 194–206. https://doi.org/10.1080/19393555.2015.1111961 .
Zhang, Y., P. Li, and X. Wang. 2019. Intrusion detection for IoT based on improved genetic algorithm and deep belief network. IEEE Access 7: 31711–31722.
Zheng, Muwei, Hannah Robbins, Zimo Chai, Prakash Thapa, and Tyler Moore. 2018. Cybersecurity research datasets: taxonomy and empirical analysis. In 11th {USENIX} workshop on cyber security experimentation and test ({CSET} 18).
Zhou, X., W. Liang, S. Shimizu, J. Ma, and Q. Jin. 2021. Siamese neural network based few-shot learning for anomaly detection in industrial cyber-physical systems. IEEE Transactions on Industrial Informatics 17 (8): 5790–5798. https://doi.org/10.1109/TII.2020.3047675 .
Zhou, Y.Y., G. Cheng, S.Q. Jiang, and M. Dai. 2020. Building an efficient intrusion detection system based on feature selection and ensemble classifier. Computer Networks 174: 17. https://doi.org/10.1016/j.comnet.2020.107247 .
Download references
Open Access funding provided by the IReL Consortium.
Author information
Authors and affiliations.
University of Limerick, Limerick, Ireland
Frank Cremer, Barry Sheehan, Arash N. Kia, Martin Mullins & Finbarr Murphy
TH Köln University of Applied Sciences, Cologne, Germany
Michael Fortmann & Stefan Materne
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Barry Sheehan .
Ethics declarations
Conflict of interest.
On behalf of all authors, the corresponding author states that there is no conflict of interest.
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Below is the link to the electronic supplementary material.
Supplementary file1 (PDF 334 kb)
Supplementary file1 (docx 418 kb), rights and permissions.
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/ .
Reprints and permissions
About this article
Cremer, F., Sheehan, B., Fortmann, M. et al. Cyber risk and cybersecurity: a systematic review of data availability. Geneva Pap Risk Insur Issues Pract 47 , 698–736 (2022). https://doi.org/10.1057/s41288-022-00266-6
Download citation
Received : 15 June 2021
Accepted : 20 January 2022
Published : 17 February 2022
Issue Date : July 2022
DOI : https://doi.org/10.1057/s41288-022-00266-6
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Cyber insurance
- Systematic review
- Cybersecurity
- Find a journal
- Publish with us
- Track your research
75 Cyber Security Research Topics in 2024
Introduction to Cybersecurity Research
Cybersecurity research aims to protect computer systems, networks, and data from unauthorised access, theft, or damage. It involves studying and developing methods and techniques to identify, understand, and mitigate cyber threats and vulnerabilities.
The field can be divided into theoretical and applied research and faces challenges such as
- Increasing complexity
- New forms of malware
- The growing sophistication of cyber attacks
On a daily basis, approximately 2,200 cyber attacks occur, with an average of one cyber attack happening every 39 seconds. This is the reason why researchers must stay up-to-date and collaborate with others in the field.
In this article, let’s discuss the different cybersecurity research topics and how they will help you become an expert in the field.

Check out our free technology courses to get an edge over the competition.
Here are some of the latest research topics in cyber security –
Emerging Cyber Threats and Vulnerabilities in 2024
Continual technological advancements lead to changes in cybersecurity trends, with data breaches, ransomware, and hacks becoming more prevalent.
- Cyber Attacks and Their Countermeasures – Discuss – This research paper will discuss various cyber attacks and their corresponding countermeasures. It aims to provide insights on how organisations can better protect themselves from cyber threats.
- Is Cryptography Necessary for Cybersecurity Applications? – Explore the role of cryptography in ensuring the confidentiality, integrity, and availability of data and information in cybersecurity. It would examine the various cryptographic techniques used in cybersecurity and their effectiveness in protecting against cyber threats.
Here are some other cyber security topics that you may consider –
- Discuss the Application of Cyber Security for Cloud-based Applications
- Data Analytics Tools in Cybersecurity
- Malware Analysis
- What Are the Behavioural Aspects of Cyber Security?
- Role of Cyber Security on Intelligent Transporation Systems
- How to Stop and Spot Different Types of Malware?
Check Out upGrad’s Software Development Courses to upskill yourself.
Machine Learning and AI in Cybersecurity Research
Machine learning and AI are research topics in cybersecurity, aiming to develop algorithms for threat detection, enhance intelligence and automate risk mitigation. However, security risks like adversarial attacks require attention.

- Using AI/ML to Analyse Cyber Threats – This cyber security research paper analyses cyber threats and could include an overview of the current state of cyber threats and how AI/ML can help with threat detection and response. The paper could also discuss the challenges and limitations of using AI/ML in cybersecurity and potential areas for further research.
Here are some other topics to consider –
- Developing Cognitive Systems for Cyber Threat Detection and Response
- Developing Distributed Ai Systems to Enhance Cybersecurity
- Developing Deep Learning Architectures for Cyber Defence
- Exploring the Use of Computational Intelligence and Neuroscience in Enhancing Security and Privacy
- How is Cyber Security Relevant for Everyone? Discuss
- Discuss the Importance of Network Traffic Analysis
- How to Build an App to Break Ceasar Cipher
You can check out the Advanced Certificate Programme in Cyber Security course by upGrad, which will help students become experts in cyber security.
IoT Security and Privacy
IoT security and privacy research aim to develop secure and privacy-preserving architectures, protocols, and algorithms for IoT devices, including encryption, access control, and secure communication. The challenge is to balance security with usability while addressing the risk of cyber-attacks and compromised privacy.
- Service Orchestration and Routing for IoT – It may focus on developing efficient and secure methods for managing and routing traffic between IoT devices and services. The paper may explore different approaches for optimising service orchestration.
- Efficient Resource Management, Energy Harvesting, and Power Consumption in IoT – This paper may focus on developing strategies to improve energy use efficiency in IoT devices. This may involve investigating the use of energy harvesting technologies, optimising resource allocation and management, and exploring methods to reduce power consumption.
Here are some other cyber security project topics to consider –
- Computation and Communication Gateways for IoT
- The Miniaturisation of Sensors, Cpus, and Networks in IoT
- Big Data Analytics in IoT
- Semantic Technologies in IoT
- Virtualisation in IoT
- Privacy, Security, Trust, Identity, and Anonymity in IoT
- Heterogeneity, Dynamics, and Scale in IoT
- Consequences of Leaving Unlocked Devices Unattended
Explore our Popular Software Engineering Courses
| View All our Courses Below | |
Blockchain Security: Research Challenges and Opportunities
Blockchain security research aims to develop secure and decentralised architectures, consensus algorithms, and privacy-preserving techniques while addressing challenges such as smart contract security and consensus manipulation. Opportunities include transparent supply chain management and decentralised identity management.
- Advanced Cryptographic Technologies in the Blockchain – Explore the latest advancements and emerging trends in cryptographic techniques used in blockchain-based systems. It could also analyse the security and privacy implications of these technologies and discuss their potential impact.
- Applications of Smart Contracts in Blockchain – Explore the various use cases and potential benefits of using smart contracts to automate and secure business processes. It could also examine the challenges and limitations of smart contracts and propose potential solutions for these issues.
Here are some other topics –
- Ensuring Data Consistency, Transparency, and Privacy in the Blockchain
- Emerging Blockchain Models for Digital Currencies
- Blockchain for Advanced Information Governance Models
- The Role of Blockchain in Future Wireless Mobile Networks
- Law and Regulation Issues in the Blockchain
- Transaction Processing and Modification in the Blockchain
- Collaboration of Big Data With Blockchain Networks
Cloud Security: Trends and Innovations in Research
Cloud security research aims to develop innovative techniques and technologies for securing cloud computing environments, including threat detection with AI, SECaaS, encryption and access control, secure backup and disaster recovery, container security, and blockchain-based solutions. The goal is to ensure the security, privacy, and integrity of cloud-based data and applications for organisations.
- Posture Management in Cloud Security – Discuss the importance of identifying and addressing vulnerabilities in cloud-based systems and strategies for maintaining a secure posture over time. This could include topics such as threat modelling, risk assessment, access control, and continuous monitoring.
- Are Cloud Services 100% Secure?
- What is the Importance of Cloud Security?
- Cloud Security Service to Identify Unauthorised User Behaviour
- Preventing Theft-of-service Attacks and Ensuring Cloud Security on Virtual Machines
- Security Requirements for Cloud Computing
- Privacy and Security of Cloud Computing
Explore Our Software Development Free Courses
Cybercrime Investigations and Forensics
Cybercrime investigations and forensics involve analysing digital evidence to identify and prosecute cybercriminals, including developing new data recovery, analysis, and preservation techniques. Research also focuses on identifying cybercriminals and improving legal and regulatory frameworks for prosecuting cybercrime.
- Black Hat and White Hat Hacking: Comparison and Contrast – Explore the similarities and differences between these two approaches to hacking. It would examine the motivations and methods of both types of hackers and their impact on cybersecurity.
- Legal Requirements for Computer Forensics Laboratories
- Wireless Hacking Techniques: Emerging Technologies and Mitigation Strategies
- Cyber Crime: Current Issues and Threats
- Computer Forensics in Law Enforcement: Importance and Challenges
- Basic Procedures for Computer Forensics and Investigations
- Digital Forensic Examination of Counterfeit Documents: Techniques and Tools
- Cybersecurity and Cybercrime: Understanding the Nature and Scope
An integral part of cybercrime investigation is to learn software development. Become experts in this field with the help of upGrad’s Executive Post Graduate Programme in Software Development – Specialisation in Full Stack Development .
Cybersecurity Policy and Regulations
Cybersecurity policy and regulations research aims to develop laws, regulations, and guidelines to ensure the security and privacy of digital systems and data, including addressing gaps in existing policies, promoting international cooperation, and developing standards and best practices for cybersecurity. The goal is to protect digital systems and data while promoting innovation and growth in the digital economy.
- The Ethicality of Government Access to Citizens’ Data – Explore the ethical considerations surrounding government access to citizens’ data for surveillance and security purposes, analysing the potential risks and benefits and the legal and social implications of such access.
- The Moral Permissibility of Using Music Streaming Services – Explore the ethical implications of using music streaming services, examining issues such as intellectual property rights, artist compensation, and the environmental impact of streaming.
- Real Name Requirements on Internet Forums
- Restrictions to Prevent Domain Speculation
- Regulating Adult Content Visibility on the Internet
- Justification for Illegal Downloading
- Adapting Law Enforcement to Online Technologies
- Balancing Data Privacy With Convenience and Centralisation
- Understanding the Nature and Dangers of Cyber Terrorism
Human Factors in Cybersecurity
Human factors in cybersecurity research study how human behaviour impacts cybersecurity, including designing interfaces, developing security training, addressing user error and negligence, and examining cybersecurity’s social and cultural aspects. The goal is to improve security by mitigating human-related security risks.
- Review the Human Factors in Cybersecurity – It explores various human factors such as awareness, behaviour, training, and culture and their influence on cybersecurity, offering insights and recommendations for improving cybersecurity outcomes.
- Integrating Human Factors in Cybersecurity for Better Risk Management
- Address the Human Factors in Cybersecurity Leadership
- Human Factors in IoT Security
- Internal Vulnerabilities: the Human Factor in It Security
- Cyber Security Human Factors – the Ultimate List of Statistics and Data
In-Demand Software Development Skills
Cybersecurity Education and Awareness
Cybersecurity education and awareness aims to educate individuals and organisations about potential cybersecurity threats and best practices to prevent cyber attacks. It involves promoting safe online behaviour, training on cybersecurity protocols, and raising awareness about emerging cyber threats.
- Identifying Phishing Attacks – This research paper explores various techniques and tools to identify and prevent phishing attacks, which are common types of cyber attacks that rely on social engineering tactics to trick victims into divulging sensitive information or installing malware on their devices.
- Risks of Password Reuse for Personal and Professional Accounts – Investigate the risks associated with reusing the same password across different personal and professional accounts, such as the possibility of credential stuffing attacks and the impact of compromised accounts on organisational security.
- Effective Defence Against Ransomware
- Information Access Management: Privilege and Need-to-know Access
- Protecting Sensitive Data on Removable Media
- Recognising Social Engineering Attacks
- Preventing Unauthorised Access to Secure Areas: Detecting Piggybacking and Tailgating
- E-mail Attack and Its Characteristics
- Safe Wifi Practice: Understanding VPN
With the increasing use of digital systems and networks, avoiding potential cyber-attacks is more important than ever. The 75 research topics outlined in this list offer a glimpse into the different dimensions of this important field. By focusing on these areas, researchers can make significant contributions to enhancing the security and safety of individuals, organisations, and society as a whole.
upGrad’s Master of Science in Computer Science program is one of the top courses students can complete to become experts in the field of tech and cyber security. The program covers topics such as Java Programming and other forms of software engineering which will help students understand the latest technologies and techniques used in cyber security.
The program also includes hands-on projects and case studies to ensure students have practical experience in applying these concepts. Graduates will be well-equipped to take on challenging roles in the rapidly growing field of cyber security.

Pavan Vadapalli
Something went wrong
Our Trending Software Engineering Courses
- Master of Science in Computer Science from LJMU
- Executive PG Program in Software Development Specialisation in Full Stack Development from IIIT-B
- Advanced Certificate Programme in Cyber Security from IIITB
- Full Stack Software Development Bootcamp
- Software Engineering Bootcamp from upGrad
Popular Software Development Skills
- React Courses
- Javascript Courses
- Core Java Courses
- Data Structures Courses
- ReactJS Courses
- NodeJS Courses
- Blockchain Courses
- SQL Courses
- Full Stack Development Courses
- Big Data Courses
- Devops Courses
- NFT Courses
- Cyber Security Courses
- Cloud Computing Courses
- Database Design Courses
- Crypto Courses
- Python Courses
Our Popular Software Engineering Courses
Frequently Asked Questions (FAQs)
Artificial intelligence (AI) has proved to be an effective tool in cyber defence. AI is anticipated to gain even more prominence in 2024, mainly in monitoring, resource and threat analysis, and quick response capabilities.
One area of focus is the development of secure quantum and space communications to address the increasing use of quantum technologies and space travel. Another area of research is improving data privacy.
The approach to cybersecurity is expected to change from defending against attacks to acknowledging and managing ongoing cyber risks. The focus will be on improving resilience and recovering from potential cyber incidents.
Related Programs View All

Master's Program
9-day On-Campus Immersion
View Program

Executive PG Program
IIIT-B Alumni Status

Master's Degree
40000+ Enrolled Learners

Job Assistance
Certification
32-Hr Training by Dustin Brimberry
Question Bank with 300+ Practice Qs
45 Hrs Live Expert-Led Training
Microsoft-Approved Curriculum
159+ Hours of Live Sessions
126+ Hours of Live Sessions
Fully Online
13+ Hrs Instructor-Led Sessions
Live Doubt-Solving Sessions

2 Unique Specialisations
300+ Hiring Partners
20+ Hrs Instructor-Led Sessions
16 Hrs Live Expert-Led Training
CLF-C02 Exam Prep Support

24 Hrs Live Expert-Led Training
4 Real-World Capstone Projects
17+ Hrs Instructor-Led Training
3 Real-World Capstone Projects
289 Hours of Self-Paced Learning
10+ Capstone Projects
490+ Hours Self-Paced Learning
4 Real-World Projects
690+ Hours Self-Paced Learning
Cloud Labs-Enabled Learning
288 Hours Self-Paced Learning
9 Capstone Projects
40 Hrs Live Expert-Led Sessions
2 Mock Exams, 9 Assessments

Executive PG Certification
GenAI integrated curriculum

Job Prep Support
Instructor-Led Sessions
Hands-on UI/UX
16 Hrs Live Expert-Led Sessions
12 Hrs Hand-On Practice
30+ Hrs Live Expert-Led Sessions
24+ Hrs Hands-On with Open Stack
2 Days Live, Expert-Led Sessions
34+ Hrs Instructor-Led Sessions
10 Real-World Live Projects
24 Hrs Live Expert-Led Sessions
16 Hrs Hand-On Practice
8 Hrs Instructor-Led Training
Case-Study Based Discussions
40 Hrs Instructor-Led Sessions
Hands-On Practice, Exam Support
24-Hrs Live Expert-Led Sessions
Regular Doubt-Clearing Sessions
Extensive Exam Prep Support
6 Hrs Live Expert-Led Sessions
440+ Hours Self-Paced Learning
400 Hours of Cloud Labs
15-Hrs Live Expert-Led Sessions
32 Hrs Live Expert-Led Sessions
28 Hrs Hand-On Practice
Mentorship by Industry Experts
24 Hrs Live Trainer-Led Sessions
Mentorship by Certified Trainers
GenAI Integrated Curriculum
Full Access to Digital Resources
16 Hrs Live Instructor-Led Sessions
80+ Hrs Hands-On with Cloud Labs
160+ Hours Live Instructor-Led Sessions
Hackathons and Mock Interviews
31+ Hrs Instructor-Led Sessions
120+ Hrs of Cloud Labs Access
35+ Hrs Instructor-Led Sessions
6 Real-World Live Projects
24+ Hrs Instructor-Led Training
Self-Paced Course by Nikolai Schuler
40 Hrs Live, Expert-Led Sessions
Access Digital Resources Library
300+ Hrs Live Expert-Led Training
90 Hrs Doubt Clearing Sessions
56 Hours Instructor-Led Sessions
82 Hrs Live Expert-Led Sessions
22 Hrs Live, Expert-Led Sessions
CISA Job Practice Exams
2 High-Quality Practice Exams
Explore Free Courses
Learn more about the education system, top universities, entrance tests, course information, and employment opportunities in Canada through this course.
Advance your career in the field of marketing with Industry relevant free courses
Build your foundation in one of the hottest industry of the 21st century
Master industry-relevant skills that are required to become a leader and drive organizational success
Build essential technical skills to move forward in your career in these evolving times
Get insights from industry leaders and career counselors and learn how to stay ahead in your career
Kickstart your career in law by building a solid foundation with these relevant free courses.
Stay ahead of the curve and upskill yourself on Generative AI and ChatGPT
Build your confidence by learning essential soft skills to help you become an Industry ready professional.
Learn more about the education system, top universities, entrance tests, course information, and employment opportunities in USA through this course.
Suggested Tutorials

Explore Python programming with this concise tutorial, covering basics to advanced concepts for beginners and enthusiasts alike.

Introduction to C Programming, Learn all the C programming language concepts in this tutorial.
Suggested Blogs
![cyber attacks research paper topics Must Read 50 OOPs Interview Questions & Answers For Freshers & Experienced [2024]](https://www.upgrad.com/__khugblog-next/image/?url=https%3A%2F%2Fd14b9ctw0m6fid.cloudfront.net%2Fugblog%2Fwp-content%2Fuploads%2F2020%2F08%2F952-OOPS-Interview-Questions.png&w=3840&q=75)
by Rohan Vats
04 Jul 2024
by Pavan Vadapalli
![cyber attacks research paper topics 33 Best Computer Science Project Ideas & Topics For Beginners [Latest 2024]](https://www.upgrad.com/__khugblog-next/image/?url=https%3A%2F%2Fd14b9ctw0m6fid.cloudfront.net%2Fugblog%2Fwp-content%2Fuploads%2F2020%2F09%2F909-Banner.png&w=3840&q=75)
03 Jul 2024
02 Jul 2024
![cyber attacks research paper topics Top 58 Coding Interview Questions & Answers 2024 [For Freshers & Experienced]](https://www.upgrad.com/__khugblog-next/image/?url=https%3A%2F%2Fd14b9ctw0m6fid.cloudfront.net%2Fugblog%2Fwp-content%2Fuploads%2F2021%2F08%2F2239.png&w=3840&q=75)
26 Jun 2024
24 Jun 2024
by Rohit Sharma
13 Jun 2024
![cyber attacks research paper topics Software Engineer / Developer Salary in India in 2024 [For Freshers & Experienced]](https://www.upgrad.com/__khugblog-next/image/?url=https%3A%2F%2Fd14b9ctw0m6fid.cloudfront.net%2Fugblog%2Fwp-content%2Fuploads%2F2020%2F05%2F482.png&w=3840&q=75)
28 May 2024
Thank you for visiting nature.com. You are using a browser version with limited support for CSS. To obtain the best experience, we recommend you use a more up to date browser (or turn off compatibility mode in Internet Explorer). In the meantime, to ensure continued support, we are displaying the site without styles and JavaScript.
- View all journals
- Explore content
- About the journal
- Publish with us
- Sign up for alerts
- Open access
- Published: 17 May 2023
A holistic and proactive approach to forecasting cyber threats
- Zaid Almahmoud 1 ,
- Paul D. Yoo 1 ,
- Omar Alhussein 2 ,
- Ilyas Farhat 3 &
- Ernesto Damiani 4 , 5
Scientific Reports volume 13 , Article number: 8049 ( 2023 ) Cite this article
5945 Accesses
9 Citations
2 Altmetric
Metrics details
- Computer science
- Information technology
Traditionally, cyber-attack detection relies on reactive, assistive techniques, where pattern-matching algorithms help human experts to scan system logs and network traffic for known virus or malware signatures. Recent research has introduced effective Machine Learning (ML) models for cyber-attack detection, promising to automate the task of detecting, tracking and blocking malware and intruders. Much less effort has been devoted to cyber-attack prediction, especially beyond the short-term time scale of hours and days. Approaches that can forecast attacks likely to happen in the longer term are desirable, as this gives defenders more time to develop and share defensive actions and tools. Today, long-term predictions of attack waves are mostly based on the subjective perceptiveness of experienced human experts, which can be impaired by the scarcity of cyber-security expertise. This paper introduces a novel ML-based approach that leverages unstructured big data and logs to forecast the trend of cyber-attacks at a large scale, years in advance. To this end, we put forward a framework that utilises a monthly dataset of major cyber incidents in 36 countries over the past 11 years, with new features extracted from three major categories of big data sources, namely the scientific research literature, news, blogs, and tweets. Our framework not only identifies future attack trends in an automated fashion, but also generates a threat cycle that drills down into five key phases that constitute the life cycle of all 42 known cyber threats.
Similar content being viewed by others
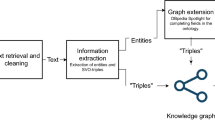
Knowledge mining of unstructured information: application to cyber domain

Machine learning partners in criminal networks
A novel hybrid feature selection and ensemble-based machine learning approach for botnet detection
Introduction.
Running a global technology infrastructure in an increasingly de-globalised world raises unprecedented security issues. In the past decade, we have witnessed waves of cyber-attacks that caused major damage to governments, organisations and enterprises, affecting their bottom lines 1 . Nevertheless, cyber-defences remained reactive in nature, involving significant overhead in terms of execution time. This latency is due to the complex pattern-matching operations required to identify the signatures of polymorphic malware 2 , which shows different behaviour each time it is run. More recently, ML-based models were introduced relying on anomaly detection algorithms. Although these models have shown a good capability to detect unknown attacks, they may classify benign behaviour as abnormal 3 , giving rise to a false alarm.
We argue that data availability can enable a proactive defense, acting before a potential threat escalates into an actual incident. Concerning non-cyber threats, including terrorism and military attacks, proactive approaches alleviate, delay, and even prevent incidents from arising in the first place. Massive software programs are available to assess the intention, potential damages, attack methods, and alternative options for a terrorist attack 4 . We claim that cyber-attacks should be no exception, and that nowadays we have the capabilities to carry out proactive, low latency cyber-defenses based on ML 5 .
Indeed, ML models can provide accurate and reliable forecasts. For example, ML models such as AlphaFold2 6 and RoseTTAFold 7 can predict a protein’s three-dimensional structure from its linear sequence. Cyber-security data, however, poses its unique challenges. Cyber-incidents are highly sensitive events and are usually kept confidential since they affect the involved organisations’ reputation. It is often difficult to keep track of these incidents, because they can go unnoticed even by the victim. It is also worth mentioning that pre-processing cyber-security data is challenging, due to characteristics such as lack of structure, diversity in format, and high rates of missing values which distort the findings.
When devising a ML-based method, one can rely on manual feature identification and engineering, or try and learn the features from raw data. In the context of cyber-incidents, there are many factors ( i.e. , potential features) that could lead to the occurrence of an attack. Wars and political conflicts between countries often lead to cyber-warfare 8 , 9 . The number of mentions of a certain attack appearing in scientific articles may correlate well with the actual incident rate. Also, cyber-attacks often take place on holidays, anniversaries and other politically significant dates 5 . Finding the right features out of unstructured big data is one of the key strands of our proposed framework.
The remainder of the paper is structured as follows. The “ Literature review ” section presents an overview of the related work and highlights the research gaps and our contributions. The “ Methods ” section describes the framework design, including the construction of the dataset and the building of the model. The “ Results ” section presents the validation results of our model, the trend analysis and forecast, and a detailed description of the developed threat cycle. Lastly, the “ Discussion ” section offers a critical evaluation of our work, highlighting its strengths and limitations, and provides recommendations for future research.
Literature review
In recent years, the literature has extensively covered different cyber threats across various application domains, and researchers have proposed several solutions to mitigate these threats. In the Social Internet of Vehicles (SIoV), one of the primary concerns is the interception and tampering of sensitive information by attackers 10 . To address this, a secure authentication protocol has been proposed that utilises confidential computing environments to ensure the privacy of vehicle-generated data. Another application domain that has been studied is the privacy of image data, specifically lane images in rural areas 11 . The proposed methodology uses Error Level Analysis (ELA) and artificial neural network (ANN) algorithms to classify lane images as genuine or fake, with the U-Net model for lane detection in bona fide images. The final images are secured using the proxy re-encryption technique with RSA and ECC algorithms, and maintained using fog computing to protect against forgery.
Another application domain that has been studied is the security of Wireless Mesh Networks (WMNs) in the context of the Internet of Things (IoT) 12 . WMNs rely on cooperative forwarding, making them vulnerable to various attacks, including packet drop/modification, badmouthing, on-off, and collusion attacks. To address this, a novel trust mechanism framework has been proposed that differentiates between legitimate and malicious nodes using direct and indirect trust computation. The framework utilises a two-hop mechanism to observe the packet forwarding behaviour of neighbours, and a weighted D-S theory to aggregate recommendations from different nodes. While these solutions have shown promising results in addressing cyber threats, it is important to anticipate the type of threat that may arise to ensure that the solutions can be effectively deployed. By proactively identifying and anticipating cyber threats, organisations can better prepare themselves to protect their systems and data from potential attacks.
While we are relatively successful in detecting and classifying cyber-attacks when they occur 13 , 14 , 15 , there has been a much more limited success in predicting them. Some studies exist on short-term predictive capability 16 , 17 , 18 , 19 , 20 , 21 , 22 , 23 , 24 , 25 , 26 , such as predicting the number or source of attacks to be expected in the next hours or days. The majority of this work performs the prediction in restricted settings ( e.g. , against a specific entity or organisation) where historical data are available 18 , 19 , 25 . Forecasting attack occurrences has been attempted by using statistical methods, especially when parametric data distributions could be assumed 16 , 17 , as well as by using ML models 20 . Other methods adopt a Bayesian setting and build event graphs suitable for estimating the conditional probability of an attack following a given chain of events 21 . Such techniques rely on libraries of predefined attack graphs: they can identify the known attack most likely to happen, but are helpless against never-experienced-before, zero-day attacks.
Other approaches try to identify potential attackers by using network entity reputation and scoring 26 . A small but growing body of research explores the fusion of heterogeneous features (warning signals) to forecast cyber-threats using ML. Warning signs may include the number of mentions of a victim organisation on Twitter 18 , mentions in news articles about the victim entity 19 , and digital traces from dark web hacker forums 20 . Our literature review is summarised in Table 1 .
Forecasting the cyber-threats that will most likely turn into attacks in the medium and long term is of significant importance. It not only gives to cyber-security agencies the time to evaluate the existing defence measures, but also assists them in identifying areas where to develop preventive solutions. Long-term prediction of cyber-threats, however, still relies on the subjective perceptions of human security experts 27 , 28 . Unlike a fully automated procedure based on quantitative metrics, the human-based approach is prone to bias based on scientific or technical interests 29 . Also, quantitative predictions are crucial to scientific objectivity 30 . In summary, we highlight the following research gaps:
Current research primarily focuses on detecting ( i.e. , reactive) rather than predicting cyber-attacks ( i.e. , proactive).
Available predictive methods for cyber-attacks are mostly limited to short-term predictions.
Current predictive methods for cyber-attacks are limited to restricted settings ( e.g. , a particular network or system).
Long-term prediction of cyber-attacks is currently performed by human experts, whose judgement is subjective and prone to bias and disagreement.
Research contributions
Our objective is to fill these research gaps by a proactive, long-term, and holistic approach to attack prediction. The proposed framework gives cyber-security agencies sufficient time to evaluate existing defence measures while also providing objective and accurate representation of the forecast. Our study is aimed at predicting the trend of cyber-attacks up to three years in advance, utilising big data sources and ML techniques. Our ML models are learned from heterogeneous features extracted from massive, unstructured data sources, namely, Hackmageddon 9 , Elsevier 31 , Twitter 32 , and Python APIs 33 . Hackmageddon provides more than 15, 000 records of global cyber-incidents since the year 2011, while Elsevier API offers access to the Scopus database, the largest abstract and citation database of peer-reviewed literature with over 27,000,000 documents 34 . The number of relevant tweets we collected is around 9 million. Our study covers 36 countries and 42 major attack types. The proposed framework not only provides the forecast and categorisation of the threats, but also generates a threat life-cycle model, whose the five key phases underlie the life cycle of all 42 known cyber-threats. The key contribution of this study consists of the following:
A novel dataset is constructed using big unstructured data ( i.e. , Hackmageddon) including news and government advisories, in addition to Elsevier, Twitter, and Python API. The dataset comprises monthly counts of cyber-attacks and other unique features, covering 42 attack types across 36 countries.
Our proactive approach offers long-term forecasting by predicting threats up to 3 years in advance.
Our approach is holistic in nature, as it does not limit itself to specific entities or regions. Instead, it provides projections of attacks across 36 countries situated in diverse parts of the world.
Our approach is completely automated and quantitative, effectively addressing the issue of bias in human predictions and providing a precise forecast.
By analysing past and predicted future data, we have classified threats into four main groups and provided a forecast of 42 attacks until 2025.
The first threat cycle is proposed, which delineates the distinct phases in the life cycle of 42 cyber-attack types.
The framework of forecasting cyber threats
The architecture of our framework for forecasting cyber threats is illustrated in Fig. 1 . As seen in the Data Sources component (l.h.s), to harness all the relevant data and extract meaningful insights, our framework utilises various sources of unstructured data. One of our main sources is Hackmageddon, which includes massive textual data on major cyber-attacks (approx. 15,334 incidents) dating back to July 2011. We refer to the monthly number of attacks in the list as the Number of Incidents (NoI). Also, Elsevier’s Application Programming Interface (API) gives access to a very large corpus of scientific articles and data sets from thousands of sources. Utilising this API, we obtained the Number of Mentions (NoM) ( e.g. , monthly) of each attack that appeared in the scientific publications. This NoM data is of particular importance as it can be used as the ground truth for attack types that do not appear in Hackmageddon. During the preliminary research phase, we examined all the potentially relevant features and noticed that wars/political conflicts are highly correlated to the number of cyber-events. These data were then extracted via Twitter API as Armed Conflict Areas/Wars (ACA). Lastly, as attacks often take place around holidays, Python’s holidays package was used to obtain the number of public holidays per month for each country, which is referred to as Public Holidays (PH).
To ensure the accuracy and quality of Hackmageddon data, we validated it using the statistics from official sources across government, academia, research institutes and technology organisations. For a ransomware example, the Cybersecurity & Infrastructure Security Agency stated in their 2021 trend report that cybersecurity authorities in the United States, Australia, and the United Kingdom observed an increase in sophisticated, high-impact ransomware incidents against critical infrastructure organisations globally 35 . The WannaCry attack in the dataset was also validated with Ghafur et al ’s 1 statement in their article: “WannaCry ransomware attack was a global epidemic that took place in May 2017”.
An example of an entry in the Hackmageddon dataset is shown in Table 2 . Each entry includes the incident date, the description of the attack, the attack type, and the target country. Data pre-processing (Fig. 1 ) focused on noise reduction through imputing missing values ( e.g. , countries), which were often observed in the earlier years. We were able to impute these values from the description column or occasionally, by looking up the entity location using Google.
The textual data were quantified via our Word Frequency Counter (WFC), which counted the number of each attack type per month as in Table 3 . Cumulative Aggregation (CA) obtained the number of attacks for all countries combined and an example of a data entry after transformation includes the month, and the number of attacks against each country (and all countries combined) for each attack type. By adding features such as NoM, ACA, and PH, we ended up having additional features that we appended to the dataset as shown in Table 4 . Our final dataset covers 42 common types of attacks in 36 countries. The full list of attacks is provided in Table 5 . The list of the countries is given in Supplementary Table S1 .
To analyse and investigate the main characteristics of our data, an exploratory analysis was conducted focusing on the visualisation and identification of key patterns such as trend and seasonality, correlated features, missing data and outliers. For seasonal data, we smoothed out the seasonality so that we could identify the trend while removing the noise in the time series 36 . The smoothing type and constants were optimised along with the ML model (see Optimisation for details). We applied Stochastic selection of Features (SoF) to find the subset of features that minimises the prediction error, and compared the univariate against the multivariate approach.
For the modelling, we built a Bayesian encoder-decoder Long Short-Term Memory (B-LSTM) network. B-LSTM models have been proposed to predict “perfect wave” events like the onset of stock market “bear” periods on the basis of multiple warning signs, each having different time dynamics 37 . Encoder-decoder architectures can manage inputs and outputs that both consist of variable-length sequences. The encoder stage encodes a sequence into a fixed-length vector representation (known as the latent representation). The decoder prompts the latent representation to predict a sequence. By applying an efficient latent representation, we train the model to consider all the useful warning information from the input sequence - regardless of its position - and disregard the noise.
Our Bayesian variation of the encoder-decoder LSTM network considers the weights of the model as random variables. This way, we extract epistemic uncertainty via (approximate) Bayesian inference, which quantifies the prediction error due to insufficient information 38 . This is an important parameter, as epistemic uncertainty can be reduced by better intelligence, i.e. , by acquiring more samples and new informative features. Details are provided in “ Bayesian long short-term memory ” section.
Our overall analytical platform learns an operational model for each attack type. Here, we evaluated the model’s performance in predicting the threat trend 36 months in advance. A newly modified symmetric Mean Absolute Percentage Error (M-SMAPE) was devised as the evaluation metric, where we added a penalty term that accounts for the trend direction. More details are provided in the “ Evaluation metrics ” section.
Feature extraction
Below, we provide the details of the process that transforms raw data into numerical features, obtaining the ground truth NoI and the additional features NoM, ACA and PH.
NoI: The number of daily incidents in Hackmageddon was transformed from the purely unstructured daily description of attacks along with the attack and country columns, to the monthly count of incidents for each attack in each country. Within the description, multiple related attacks may appear, which are not necessarily in the attack column. Let \(E_{x_i}\) denote the set of entries during the month \(x_i\) in Hackmageddon dataset. Let \(a_j\) and \(c_k\) denote the j th attack and k th country. Then NoI can be expressed as follows:
where \(Z(a_j,c_k,e)\) is a function that evaluates to 1 if \(a_j\) appears either in the description or in the attack columns of entry e and \(c_k\) appears in the country column of e . Otherwise, the function evaluates to 0. Next, we performed CA to obtain the monthly count of attacks in all countries combined for each attack type as follows:
NoM: We wrote a Python script to query Elsevier API for the number of mentions of each attack during each month 31 . The search covers the title, abstract and keywords of published research papers that are stored in Scopus database 39 . Let \(P_{x_i}\) denote the set of research papers in Scopus published during the month \(x_i\) . Also, let \(W_{p}\) denote the set of words in the title, abstract and keywords of research paper p . Then NoM can be expressed as follows:
where \(U(w,a_j)\) evaluates to 1 if \(w=a_j\) , and to 0 otherwise.
ACA: Using Twitter API in Python 32 , we wrote a query to obtain the number of tweets with keywords related to political conflicts or military attacks associated with each country during each month. The keywords used for each country are summarised in Supplementary Table S2 , representing our query. Formally, let \(T_{x_i}\) denote the set of all tweets during the month \(x_i\) . Then ACA can be expressed as follows:
where \(Q(t,c_k)\) evaluates to 1 if the query in Supplementary Table S2 evaluates to 1 given t and \(c_k\) . Otherwise, it evaluates to 0.
PH: We used the Python holidays library 33 to count the number of days that are considered public holidays in each country during each month. More formally, this can be expressed as follows:
where \(H(d,c_k)\) evaluates to 1 if the day d in the country \(c_k\) is a public holiday, and to 0 otherwise. In ( 4 ) and ( 5 ), CA was used to obtain the count for all countries combined as in ( 2 ).
Data integration
Based on Eqs. ( 1 )–( 5 ), we obtain the following columns for each month:
NoI_C: The number of incidents for each attack type in each country ( \(42 \times 36\) columns) [Hackmageddon].
NoI: The total number of incidents for each attack type (42 columns) [Hackmageddon].
NoM: The number of mentions of each attack type in research articles (42 columns) [Elsevier].
ACA_C: The number of tweets about wars and conflicts related to each country (36 columns) [Twitter].
ACA: The total number of tweets about wars and conflicts (1 column) [Twitter].
PH_C: The number of public holidays in each country (36 columns) [Python].
PH: The total number of public holidays (1 column) [Python].
In the aforementioned list of columns, the name enclosed within square brackets denotes the source of data. By matching and combining these columns, we derive our monthly dataset, wherein each row represents a distinct month. A concrete example can be found in Tables 3 and 4 , which, taken together, constitute a single observation in our dataset. The dataset can be expanded through the inclusion of other monthly features as supplementary columns. Additionally, the dataset may be augmented with further samples as additional monthly records become available. Some suggestions for extending the dataset are provided in the “ Discussion ” section.
Data smoothing
We tested multiple smoothing methods and selected the one that resulted in the model with the lowest M-SMAPE during the hyper-parameter optimisation process. The methods we tested include exponential smoothing (ES), double exponential smoothing (DES) and no smoothing (NS). Let \(\alpha \) be the smoothing constant. Then the ES formula is:
where \(D(x_{i})\) denotes the original data at month \(x_{i}\) . For the DES formula, let \(\alpha \) and \(\beta \) be the smoothing constants. We first define the level \(l(x_{i})\) and the trend \(\tau (x_{i})\) as follows:
then, DES is expressed as follows:
The smoothing constants ( \(\alpha \) and \(\beta \) ) in the aforementioned methods are chosen as the predictive results of the ML model that gives the lowest M-SMAPE during the hyper-parameter optimisation process. Supplementary Fig. S5 depicts an example for the DES result.
Bayesian long short-term memory
LSTM is a type of recurrent neural network (RNN) that uses lagged observations to forecast the future time steps 30 . It was introduced as a solution to the so-called vanishing/exploding gradient problem of traditional RNNs 40 , where the partial derivative of the loss function may suddenly approach zero at some point of the training. In LSTM, the input is passed to the network cell, which combines it with the hidden state and cell state values from previous time steps to produce the next states. The hidden state can be thought of as a short-term memory since it stores information from recent periods in a weighted manner. On the other hand, the cell state is meant to remember all the past information from previous intervals and store them in the LSTM cell. The cell state thus represents the long-term memory.
LSTM networks are well-suited for time-series forecasting, due to their proficiency in retaining both long-term and short-term temporal dependencies 41 , 42 . By leveraging their ability to capture these dependencies within cyber-attack data, LSTM networks can effectively recognise recurring patterns in the attack time-series. Moreover, the LSTM model is capable of learning intricate temporal patterns in the data and can uncover inter-correlations between various variables, making it a compelling option for multivariate time-series analysis 43 .
Given a sequence of LSTM cells, each processing a single time-step from the past, the final hidden state is encoded into a fixed-length vector. Then, a decoder uses this vector to forecast future values. Using such architecture, we can map a sequence of time steps to another sequence of time steps, where the number of steps in each sequence can be set as needed. This technique is referred to as encoder-decoder architecture.
Because we have relatively short sequences within our refined data ( e.g. , 129 monthly data points over the period from July 2011 to March 2022), it is crucial to extract the source of uncertainty, known as epistemic uncertainty 44 , which is caused by lack of knowledge. In principle, epistemic uncertainty can be reduced with more knowledge either in the form of new features or more samples. Deterministic (non-stochastic) neural network models are not adequate to this task as they provide point estimates of model parameters. Rather, we utilise a Bayesian framework to capture epistemic uncertainty. Namely, we adopt the Monte Carlo dropout method proposed by Gal et al. 45 , who showed that the use of non-random dropout neurons during ML training (and inference) provides a Bayesian approximation of the deep Gaussian processes. Specifically, during the training of our LSTM encoder-decoder network, we applied the same dropout mask at every time-step (rather than applying a dropout mask randomly from time-step to time-step). This technique, known as recurrent dropout is readily available in Keras 46 . During the inference phase, we run trained model multiple times with recurrent dropout to produce a distribution of predictive results. Such prediction is shown in Fig. 4 .
Figure 2 shows our encoder-decoder B-LSTM architecture. The hidden state and cell state are denoted respectively by \(h_{i}\) and \(C_{i}\) , while the input is denoted by \(X_{i}\) . Here, the length of the input sequence (lag) is a hyper-parameter tuned to produce the optimal model, where the output is a single time-step. The number of cells ( i.e. , the depth of each layer) is tuned as a hyper-parameter in the range between 25 and 200 cells. Moreover, we used one or two layers, tuning the number of layers to each attack type. For the univariate model we used a standard Rectified Linear Unit (ReLU) activation function, while for the multivariate model we used a Leaky ReLU. Standard ReLU computes the function \(f(x)=max(0,x)\) , thresholding the activation at zero. In the multivariate case, zero-thresholding may generate the same ReLU output for many input vectors, making the model convergence slower 47 . With Leaky ReLU, instead of defining ReLU as zero when \(x < 0\) , we introduce a negative slope \(\alpha =0.2\) . Additionally, we used recurrent dropout ( i.e. , arrows in red as shown in Fig. 2 ), where the probability of dropping out is another hyper-parameter that we tune as described above, following Gal’s method 48 . The tuned dropout value is maintained during the testing and prediction as previously mentioned. Once the final hidden vector \(h_{0}\) is produced by the encoder, the Repeat Vector layer is used as an adapter to reshape it from the bi-dimensional output of the encoder ( e.g. , \(h_{0}\) ) to the three-dimensional input expected by the decoder. The decoder processes the input and produces the hidden state, which is then passed to a dense layer to produce the final output.
Each time-step corresponds to a month in our model. Since the model is learnt to predict a single time-step (single month), we use a sliding window during the prediction phase to forecast 36 (monthly) data points. In other words, we predict a single month at each step, and the predicted value is fed back for the prediction of the following month. This concept is illustrated in the table shown in Fig. 2 . Utilising a single time-step in the model’s output minimises the size of the sliding window, which in turn allows for training with as many observations as possible with such limited data.
The difference between the univariate and multivariate B-LSTMs is that the latter carries additional features in each time-step. Thus, instead of passing a scalar input value to the network, we pass a vector of features including the ground truth at each time-step. The model predicts a vector of features as an output, from which we retrieve the ground truth, and use it along with the other predicted features as an input to predict the next time-step.
Evaluation metrics
The evaluation metric SMAPE is a percentage (or relative) error based accuracy measure that judges the prediction performance purely on how far the predicted value is from the actual value 49 . It is expressed by the following formula:
where \(F_{t}\) and \(A_{t}\) denote the predicted and actual values at time t . This metric returns a value between 0% and 100%. Given that our data has zero values in some months ( e.g. , emerging threats), the issue of division by zero may arise, a problem that often emerges when using standard MAPE (Mean Absolute Percentage Error). We find SMAPE to be resilient to this problem, since it has both the actual and predicted values in the denominator.
Recall that our model aims to predict a curve (corresponding to multiple time steps). Using plain SMAPE as the evaluation metric, the “best” model may turn out to be simply a straight line passing through the same points of the fluctuating actual curve. However, this is undesired in our case since our priority is to predict the trend direction (or slope) over its intensity or value at a certain point. We hence add a penalty term to SMAPE that we apply when the height of the predicted curve is relatively smaller than that of the actual curve. This yields the modified SMAPE (M-SMAPE). More formally, let I ( V ) be the height of the curve V , calculated as follows:
where n is the curve width or the number of data points. Let A and F denote the actual and predicted curves. We define M-SMAPE as follows:
where \(\gamma \) is a penalty constant between 0 and 1, and d is another constant \(\ge \) 1. In our experiment, we set \(\gamma \) to 0.3, and d to 3, as we found these to be reasonable values by trial and error. We note that the range of possible values of M-SMAPE is between 0% and (100 + 100 \(\gamma \) )% after this modification. By running multiple experiments we found out that the modified evaluation metric is more suitable for our scenario, and therefore was adopted for the model’s evaluation.
Optimisation
On average, our model was trained on around 67% of the refined data, which is equivalent to approximately 7.2 years. We kept the rest, approximately 33% (3 years + lag period), for validation. These percentages may slightly differ for different attack types depending on the optimal lag period selected.
For hyper-parameter optimisation, we performed a random search with 60 iterations, to obtain the set of features, smoothing methods and constants, and model’s hyper-parameters that results in the model with the lowest M-SMAPE. Random search is a simple and efficient technique for hyper-parameter optimisation, with advantages including efficiency, flexibility, robustness, and scalability. The technique has been studied extensively in the literature and was found to be superior to grid search in many cases 50 . For each set of hyper-parameters, the model was trained using the mean squared error (MSE) as the loss function, and while using ADAM as the optimisation algorithm 51 . Then, the model was validated by forecasting 3 years while using M-SMAPE as the evaluation metric, and the average performance was recorded over 3 different seeds. Once the set of hyper-parameters with the minimum M-SMAPE was obtained, we used it to train the model on the full data, after which we predicted the trend for the next 3 years (until March, 2025).
The first group of hyper-parameters is the subset of features in the case of the multivariate model. Here, we experimented with each of the 3 features separately (NoM, ACA or PH) along with the ground truth (NoI), in addition to the combination of all features. The second group is the smoothing methods and constants. The set of methods includes ES, DES and NS, as previously discussed. The set of values for the smoothing constant \(\alpha \) ranges from 0.05 to 0.7 while the set of values for the smoothing constant \(\beta \) (for DES) ranges from 0.3 to 0.7. Next is the optimisation of the lag period with values that range from 1 to 12 months. This is followed by the model’s hyper-parameters which include the learning rate with values that range from \(6\times 10^{-4}\) to \(1\times 10^{-2}\) , the number of epochs with values between 30 and 200, the number of layers in the range 1 to 2, the number of units in the range 25 to 200, and the recurrent dropout value between 0.2 and 0.5. The range of these values was obtained from the literature and the online code repositories 52 .
Validation and comparative analysis
The results of our model’s validation are provided in Fig. 3 and Table 5 . As shown in Fig. 3 , the predicted data points are well aligned with the ground truth. Our models successfully predicted the next 36 months of all the attacks’ trends with an average M-SMAPE of 0.25. Table 5 summarises the validation results of univariate and multivariate approaches using B-LSTM. The results show that with approximately 69% of all the attack types, the multivariate approach outperformed the univariate approach. As seen in Fig. 3 , the threats that have a consistent increasing or emerging trend seemed to be more suitable for the univariate approach, while threats that have a fluctuating or decreasing trend showed less validation error when using the multivariate approach. The feature of ACA resulted in the best model for 33% of all the attack types, which makes it among the three most informative features that can boost the prediction performance. The PH accounts for 17% of all the attacks followed by NoM that accounts for 12%.
We additionally compared the performance of the proposed model B-LSTM with other models namely LSTM and ARIMA. The comparison covers the univariate and multivariate approaches of LSTM and B-LSTM, with two features in the case of multivariate approach namely NoI and NoM. The comparison is in terms of the Mean Absolute Percentage Error (MAPE) when predicting four common attack types, namely DDoS, Password Attack, Malware, and Ransomware. A comparison table is provided in Supplementary Table S3 . The results illustrate the superiority of the B-LSTM model for most of the attack types.
Trends analysis
The forecast of each attack trend until the end of the first quarter of 2025 is given in Supplementary Figs. S1 – S4 . By visualising the historical data of each attack as well as the prediction for the next three years, we were able to analyse the overall trend of each attack. The attacks generally follow 4 types of trends: (1) rapidly increasing, (2) overall increasing, (3) emerging and (4) decreasing. The names of attacks for each category are provided in Fig. 4 .
The first trend category is the rapidly increasing trend (Fig. 4 a—approximately 40% of the attacks belong to this trend. We can see that the attacks belonging to this category have increased dramatically over the past 11 years. Based on the model’s prediction, some of these attacks will exhibit a steep growth until 2025. Examples include session hijacking, supply chain, account hijacking, zero-day and botnet. Some of the attacks under this category have reached their peak, have recently started stabilising, and will probably remain steady over the next 3 years. Examples include malware, targeted attack, dropper and brute force attack. Some attacks in this category, after a recent increase, are likely to level off in the next coming years. These are password attack, DNS spoofing and vulnerability-related attacks.
The second trend category is the overall increasing trend as seen in Fig. 4 b. Approximately 31% of the attacks seem to follow this trend. The attacks under this category have a slower rate of increase over the years compared to the attacks in the first category, with occasional fluctuations as can be observed in the figure. Although some of the attacks show a slight recent decline ( e.g. , malvertising, keylogger and URL manipulation), malvertising and keylogger are likely to recover and return to a steady state while URL manipulation is projected to continue a smooth decline. Other attacks typical of “cold” cyber-warfare like Advanced Persistent Threats (APT) and rootkits are already recovering from a small drop and will likely to rise to a steady state by 2025. Spyware and data breach have already reached their peak and are predicted to decline in the near future.
Next is the emerging trend as shown in Fig. 4 c. These are the attacks that started to grow significantly after the year 2016, although many of them existed much earlier. In our study, around 17% of the attacks follow this trend. Some attacks have been growing steeply and are predicted to continue this trend until 2025. These are Internet of Things (IoT) device attack and deepfake. Other attacks have also been increasing rapidly since 2016, however, are likely to slow down after 2022. These include ransomware and adversarial attacks. Interestingly, some attacks that emerged after 2016 have already reached the peak and recently started a slight decline ( e.g. , cryptojacking and WannaCry ransomware attack). It is likely that WannaCry will become relatively steady in the coming years, however, cryptojacking will probably continue to decline until 2025 thanks to the rise of proof-of-stake consensus mechanisms 53 .
The fourth and last trend category is the decreasing trend (Fig. 4 d—only 12% of the attacks follow this trend. Some attacks in this category peaked around 2012, and have been slowly decreasing since then ( e.g. , SQL Injection and defacement). The drive-by attack also peaked in 2012, however, had other local peaks in 2016 and 2018, after which it declined noticeably. Cross-site scripting (XSS) and pharming had their peak more recently compared to the other attacks, however, have been smoothly declining since then. All the attacks under this category are predicted to become relatively stable from 2023 onward, however, they are unlikely to disappear in the next 3 years.
The threat cycle
This large-scale analysis involving the historical data and the predictions for the next three years enables us to come up with a generalisable model that traces the evolution and adoption of the threats as they pass through successive stages. These stages are named by the launch, growth, maturity, trough and stability/decline. We refer to this model as The Threat Cycle (or TTC), which is depicted in Fig. 5 . In the launch phase, few incidents start appearing for a short period. This is followed by a sharp increase in terms of the number of incidents, growth and visibility as more and more cyber actors learn and adopt this new attack. Usually, the attacks in the launch phase are likely to have many variants as observed in the case of the WannaCry attack in 2017. At some point, the number of incidents reaches a peak where the attack enters the maturity phase, and the curve becomes steady for a while. Via the trough (when the attack experiences a slight decline as new security measures seem to be very effective), some attacks recover and adapt to the security defences, entering the slope of plateau, while others continue to smoothly decline although they do not completely disappear ( i.e. , slope of decline). It is worth noting that the speed of transition between the different phases may vary significantly between the attacks.
As seen in Fig. 5 , the attacks are placed on the cycle based on the slope of their current trend, while considering their historical trend and prediction. In the trough phase, we can see that the attacks will either follow the slope of plateau or the slope of decline. Based on the predicted trend in the blue zone in Fig. 4 , we were able to indicate the future direction for some of the attacks close to the split point of the trough using different colours (blue or red). Brute force, malvertising, the Distributed Denial-of-Service attack (DDoS), insider threat, WannaCry and phishing are denoted in blue meaning that these are likely on their way to the slope of plateau. In the first three phases, it is usually unclear and difficult to predict whether a particular attack will reach the plateau or decline, thus, denoted in grey.
There are some similarities and differences between TTC and the well-known Gartner hype cycle (GHC) 54 . A standard GHC is shown in a vanishing green colour in Fig. 5 . As TTC is specific to cyber threats, it has a much wider peak compared to GHC. Although both GHC and TTC have a trough phase, the threats decline slightly (while significant drop in GHC) as they exit their maturity phase, after which they recover and move to stability (slope of plateau) or decline.
Many of the attacks in the emerging category are observed in the growth phase. These include IoT device attack, deepfake and data poisoning. While ransomwares (except WannaCry) are in the growth phase, WannaCry already reached the trough, and is predicted to follow the slope of plateau. Adversarial attack has just entered the maturity stage, and cryptojacking is about to enter the trough. Although adversarial attack is generally regarded as a growing threat, interestingly, this machine-based prediction and introspection shows that it is maturing. The majority of the rapidly increasing threats are either in the growth or in the maturity phase. The attacks in the growth phase include session hijacking, supply chain, account hijacking, zero-day and botnet. The attacks in the maturity phase include malware, targeted attack, vulnerability-related attacks and Man-In-The-Middle attack (MITM). Some rapidly increasing attacks such as phishing, brute force, and DDoS are in the trough and are predicted to enter the stability. We also observe that most of the attacks in the category of overall increasing threats have passed the growth phase and are mostly branching to the slope of plateau or the slope of decline, while few are still in the maturity phase ( e.g. , spyware). All of the decreasing threats are on the slope of decline. These include XSS, pharming, drive-by, defacement and SQL injection.
Highlights and limitations
This study presents the development of a ML-based proactive approach for long-term prediction of cyber-attacks offering the ability to communicate effectively with the potential attacks and the relevant security measures in an early stage to plan for the future. This approach can contribute to the prevention of an incident by allowing more time to develop optimal defensive actions/tools in a contested cyberspace. Proactive approaches can also effectively reduce uncertainty when prioritising existing security measures or initiating new security solutions. We argue that cyber-security agencies should prioritise their resources to provide the best possible support in preventing fastest-growing attacks that appear in the launch phase of TTC or the attacks in the categories of the rapidly increasing or emerging trend as in Fig. 4 a and c based on the predictions in the coming years.
In addition, our fully automated approach is promising to overcome the well-known issues of human-based analysis, above all expertise scarcity. Given the absence of the possibility of analysing with human’s subjective bias while following a purely quantitative procedure and data, the resulting predictions are expected to have lower degree of subjectivity, leading to consistencies within the subject. By fully automating this analytic process, the results are reproducible and can potentially be explainable with help of the recent advancements in Explainable Artificial Intelligence.
Thanks to the massive data volume and wide geographic coverage of the data sources we utilised, this study covers every facet of today’s cyber-attack scenario. Our holistic approach performs the long-term prediction on the scale of 36 countries, and is not confined to a specific region. Indeed, cyberspace is limitless, and a cyber-attack on critical infrastructure in one country can affect the continent as a whole or even globally. We argue that our Threat Cycle (TTC) provides a sound basis to awareness of and investment in new security measures that could prevent attacks from taking place. We believe that our tool can enable a collective defence effort by sharing the long-term predictions and trend analysis generated via quantitative processes and data and furthering the analysis of its regional and global impacts.
Zero-day attacks exploit a previously unknown vulnerability before the developer has had a chance to release a patch or fix for the problem 55 . Zero-day attacks are particularly dangerous because they can be used to target even the most secure systems and go undetected for extended periods of time. As a result, these attacks can cause significant damage to an organisation’s reputation, financial well-being, and customer trust. Our approach takes the existing research on using ML in the field of zero-day attacks to another level, offering a more proactive solution. By leveraging the power of deep neural networks to analyse complex, high-dimensional data, our approach can help agencies to prepare ahead of time, in-order to prevent the zero-day attack from happening at the first place, a problem that there is no existing fix for it despite our ability to detect it. Our results in Fig. 4 a suggest that zero-day attack is likely to continue a steep growth until 2025. If we know this information, we can proactively invest on solutions to prevent it or slow down its rise in the future, since after all, the ML detection approaches may not be alone sufficient to reduce its effect.
A limitation of our approach is its reliance on a restricted dataset that encompasses data since 2011 only. This is due to the challenges we encountered in accessing confidential and sensitive information. Extending the prediction phase requires the model to make predictions further into the future, where there may be more variability and uncertainty. This could lead to a decrease in prediction accuracy, especially if the underlying data patterns change over time or if there are unforeseen external factors that affect the data. While not always the case, this uncertainty is highlighted by the results of the Bayesian model itself as it expresses this uncertainty through the increase of the confidence interval over time (Fig. 3 a and b). Despite incorporating the Bayesian model to tackle the epistemic uncertainty, our model could benefit substantially from additional data to acquire a comprehensive understanding of past patterns, ultimately improving its capacity to forecast long-term trends. Moreover, an augmented dataset would allow ample opportunity for testing, providing greater confidence in the model’s resilience and capability to generalise.
Further enhancements can be made to the dataset by including pivotal dates (such as anniversaries of political events and war declarations) as a feature, specifically those that experience a high frequency of cyber-attacks. Additionally, augmenting the dataset with digital traces that reflect the attackers’ intentions and motivations obtained from the dark web would be valuable. Other informative features could facilitate short-term prediction, specifically to forecast the on-set of each attack.
Future work
Moving forward, future research can focus on augmenting the dataset with additional samples and informative features to enhance the model’s performance and its ability to forecast the trend in the longer-term. Also, the work opens a new area of research that focuses on prognosticating the disparity between the trend of cyber-attacks and the associated technological solutions and other variables, with the aim of guiding research investment decisions. Subsequently, TTC could be improved by adopting another curve model that can visualise the current development of relevant security measures. The threat trend categories (Fig. 4 ) and TTC (Fig. 5 ) show how attacks will be visible in the next three years and more, however, we do not know where the relevant security measures will be. For example, data poisoning is an AI-targeted adversarial attack that attempts to manipulate the training dataset to control the prediction behaviour of a machine-learned model. From the scientific literature data ( e.g. , Scopus), we could analyse the published articles studying the data poisoning problem and identify the relevant keywords of these articles ( e.g. , Reject on Negative Impact (RONI) and Probability of Sufficiency (PS)). RONI and PS are typical methods used for detecting poisonous data by evaluating the effect of individual data points on the performance of the trained model. Likewise, the features that are informative, discriminating or uncertainty-reducing for knowing how the relevant security measures evolve exist within such online sources in the form of author’s keywords, number of citations, research funding, number of publications, etc .
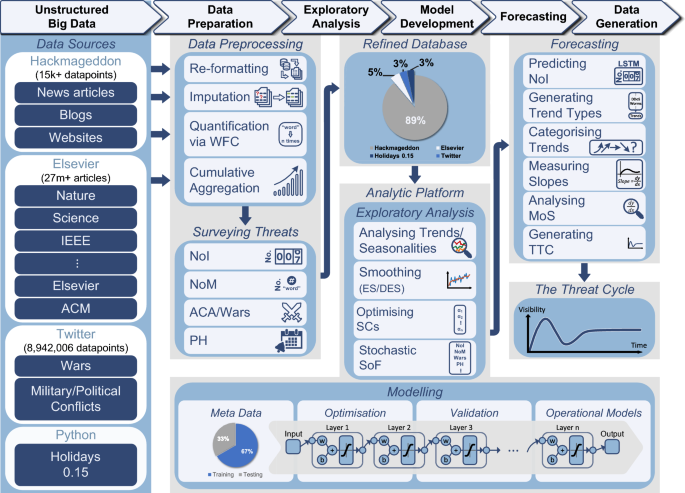
The workflow and architecture of forecasting cyber threats. The ground truth of Number of Incidents (NoI) was extracted from Hackmageddon which has over 15,000 daily records of cyber incidents worldwide over the past 11 years. Additional features were obtained including the Number of Mentions (NoM) of each attack in the scientific literature using Elsevier API which gives access to over 27 million documents. The number of tweets about Armed Conflict Areas/Wars (ACA) was also obtained using Twitter API for each country, with a total of approximately 9 million tweets. Finally, the number of Public Holidays (PH) in each country was obtained using the holidays library in Python. The data preparation phase includes data re-formatting, imputation and quantification using Word Frequency Counter (WFC) to obtain the monthly occurrence of attacks per country and Cumulative Aggregation (CA) to obtain the sum for all countries. The monthly NoM, ACA and PHs were quantified and aggregated using CA. The numerical features were then combined and stored in the refined database. The percentages in the refined database are based on the contribution of each data source. In the exploratory analysis phase, the analytic platform analyses the trend and performs data smoothing using Exponential Smoothing (ES), Double Exponential Smoothing (DES) and No Smoothing (NS). The smoothing methods and Smoothing Constants (SCs) were chosen for each attack followed by the Stochastic Selection of Features (SoF). In the model development phase, the meta data was partitioned into approximately 67% for training and 33% for testing. The models were learned using the encoder-decoder architecture of the Bayesian Long Short-Term Memory (B-LSTM). The optimisation component finds the set of hyper-parameters that minimises the error (i.e., M-SMAPE), which is then used for learning the operational models. In the forecasting phase, we used the operational models to predict the next three years’ NoIs. Analysing the predicted data, trend types were identified and attacks were categorised into four different trends. The slope of each attack was then measured and the Magnitude of Slope (MoS) was analysed. The final output is The Threat Cycle (TTC) illustrating the attacks trend, status, and direction in the next 3 years.
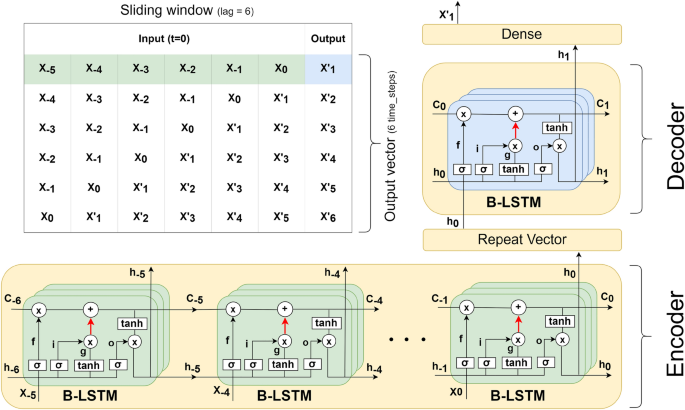
The encoder-decoder architecture of Bayesian Long Short-Term Memory (B-LSTM). \(X_{i}\) stands for the input at time-step i . \(h_{i}\) stands for the hidden state, which stores information from the recent time steps (short-term). \(C_{i}\) stands for the cell state, which stores all processed information from the past (long-term). The number of input time steps in the encoder is a variable tuned as a hyper-parameter, while the output in the decoder is a single time-step. The depth and number of layers are another set of hyper-parameters tuned during the model optimisation. The red arrows indicate a recurrent dropout maintained during the testing and prediction. The figure shows an example for an input with time lag=6 and a single layer. The final hidden state \(h_{0}\) produced by the encoder is passed to the Repeat Vector layer to convert it from 2 dimensional output to 3 dimensional input as expected by the decoder. The decoder processes the input and produces the final hidden state \(h_{1}\) . This hidden state is finally passed to a dense layer to produce the output. The table illustrates the concept of sliding window method used to forecast multiple time steps during the testing and prediction (i.e., using the output at a time-step as an input to forecast the next time-step). Using this concept, we can predict as many time steps as needed. In the table, an output vector of 6 time steps was predicted.
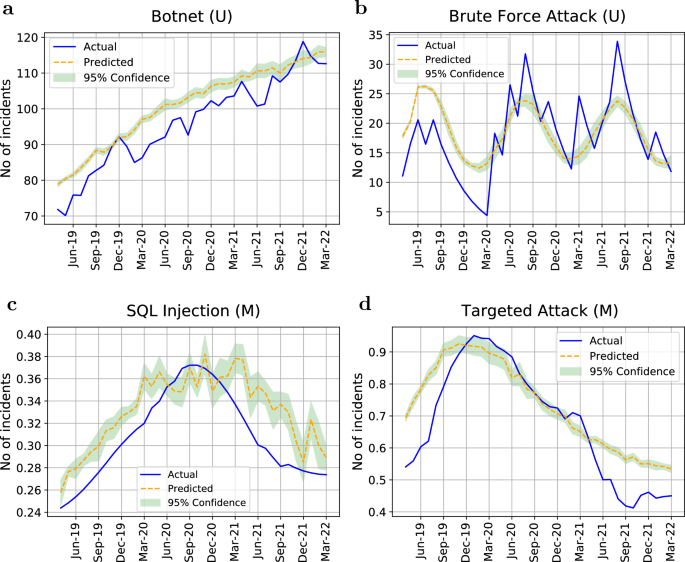
The B-LSTM validation results of predicting the number of attacks from April, 2019 to March, 2022. (U) indicates an univariate model while (M) indicates a multivariate model. ( a ) Botnet attack with M-SMAPE=0.03. ( b ) Brute force attack with M-SMAPE=0.13. ( c ) SQL injection attack with M-SMAPE=0.04 using the feature of NoM. ( d ) Targeted attack with M-SMAPE=0.06 using the feature of NoM. Y axis is normalised in the case of multivariate models to account for the different ranges of feature values.
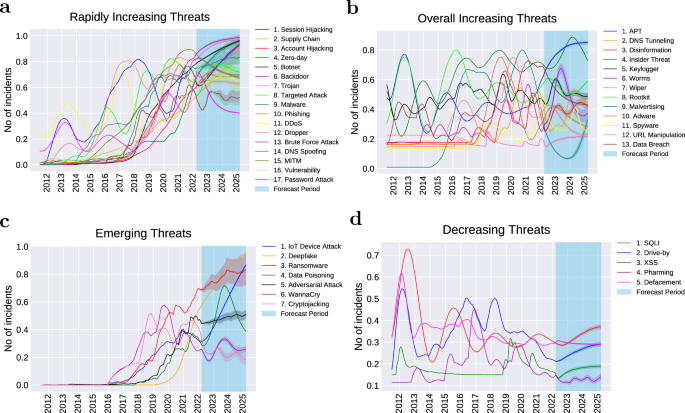
A bird’s eye view of threat trend categories. The period of the trend plots is between July, 2011 and March, 2025, with the period between April, 2022 and March, 2025 forecasted using B-LSTM. ( a ) Among rapidly increasing threats, as observed in the forecast period, some threats are predicted to continue a sharp increase until 2025 while others will probably level off. ( b ) Threats under this category have overall been increasing while fluctuating over the past 11 years. Recently, some of the overall increasing threats slightly declined however many of those are likely to recover and level off by 2025. ( c ) Emerging threats that began to appear and grow sharply after the year 2016, and are expected to continue growing at this increasing rate, while others are likely to slow down or stabilise by 2025. ( d ) Decreasing threats that peaked in the earlier years and have slowly been declining since then. This decreasing group are likely to level off however probably will not disappear in the coming 3 years. The Y axis is normalised to account for the different ranges of values across different attacks. The 95% confidence interval is shown for each threat prediction.
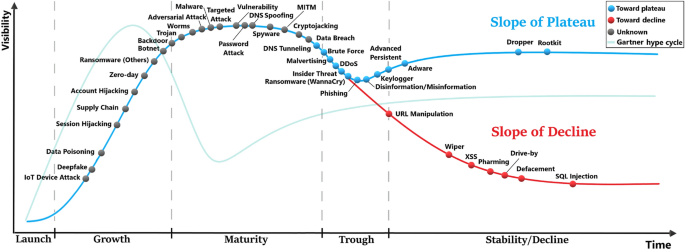
The threat cycle (TTC). The attacks go through 5 stages, namely, launch, growth, maturity trough, and stability/decline. A standard Gartner hype cycle (GHC) is shown with a vanishing green colour for a comparison to TTC. Both GHC and TTC have a peak, however, TTC’s peak is much wider with a slightly less steep curve during the growth stage. Some attacks in TTC do not recover after the trough and slide into the slope of decline. TTC captures the state of each attack in 2022, where the colour of each attack indicates which slope it would follow (e.g., plateau or decreasing) based on the predictive results until 2025. Within the trough stage, the attacks (in blue dot) are likely to arrive at the slope of plateau by 2025. The attacks (in red dot) will probably be on the slope of decline by 2025. The attacks with unknown final destination are coloured in grey.
Data availability
As requested by the journal, the data used in this paper is available to editors and reviewers upon request. The data will be made publicly available and can be accessed at the following link after the paper is published. https://github.com/zaidalmahmoud/Cyber-threat-forecast .
Ghafur, S. et al. A retrospective impact analysis of the wannacry cyberattack on the NHS. NPJ Digit. Med. 2 , 1–7 (2019).
Article Google Scholar
Alrzini, J. R. S. & Pennington, D. A review of polymorphic malware detection techniques. Int. J. Adv. Res. Eng. Technol. 11 , 1238–1247 (2020).
Google Scholar
Lazarevic, A., Ertoz, L., Kumar, V., Ozgur, A. & Srivastava, J. A comparative study of anomaly detection schemes in network intrusion detection. In: Proceedings of the 2003 SIAM International Conference on Data Mining , 25–36 (SIAM, 2003).
Kebir, O., Nouaouri, I., Rejeb, L. & Said, L. B. Atipreta: An analytical model for time-dependent prediction of terrorist attacks. Int. J. Appl. Math. Comput. Sci. 32 , 495–510 (2022).
MATH Google Scholar
Anticipating cyber attacks: There’s no abbottabad in cyber space. Infosecurity Magazine https://www.infosecurity-magazine.com/white-papers/anticipating-cyber-attacks (2015).
Jumper, J. et al. Highly accurate protein structure prediction with alphafold. Nature 596 , 583–589 (2021).
Article ADS CAS PubMed PubMed Central Google Scholar
Baek, M. et al. Accurate prediction of protein structures and interactions using a three-track neural network. Science 373 , 871–876 (2021).
Gibney, E. et al. Where is russia’s cyberwar? researchers decipher its strategy. Nature 603 , 775–776 (2022).
Article ADS CAS PubMed Google Scholar
Passeri, P. Hackmageddon data set. Hackmageddon https://www.hackmageddon.com (2022).
Chen, C.-M. et al. A provably secure key transfer protocol for the fog-enabled social internet of vehicles based on a confidential computing environment. Veh. Commun. 39 , 100567 (2023).
Nagasree, Y. et al. Preserving privacy of classified authentic satellite lane imagery using proxy re-encryption and UAV technologies. Drones 7 , 53 (2023).
Kavitha, A. et al. Security in IoT mesh networks based on trust similarity. IEEE Access 10 , 121712–121724 (2022).
Salih, A., Zeebaree, S. T., Ameen, S., Alkhyyat, A. & Shukur, H. M A survey on the role of artificial intelligence, machine learning and deep learning for cybersecurity attack detection. In: 2021 7th International Engineering Conference “Research and Innovation amid Global Pandemic” (IEC) , 61–66 (IEEE, 2021).
Ren, K., Zeng, Y., Cao, Z. & Zhang, Y. Id-rdrl: A deep reinforcement learning-based feature selection intrusion detection model. Sci. Rep. 12 , 1–18 (2022).
Liu, X. & Liu, J. Malicious traffic detection combined deep neural network with hierarchical attention mechanism. Sci. Rep. 11 , 1–15 (2021).
Werner, G., Yang, S. & McConky, K. Time series forecasting of cyber attack intensity. In Proceedings of the 12th Annual Conference on Cyber and Information Security Research , 1–3 (2017).
Werner, G., Yang, S. & McConky, K. Leveraging intra-day temporal variations to predict daily cyberattack activity. In 2018 IEEE International Conference on Intelligence and Security Informatics (ISI) , 58–63 (IEEE, 2018).
Okutan, A., Yang, S. J., McConky, K. & Werner, G. Capture: cyberattack forecasting using non-stationary features with time lags. In 2019 IEEE Conference on Communications and Network Security (CNS) , 205–213 (IEEE, 2019).
Munkhdorj, B. & Yuji, S. Cyber attack prediction using social data analysis. J. High Speed Netw. 23 , 109–135 (2017).
Goyal, P. et al. Discovering signals from web sources to predict cyber attacks. arXiv preprint arXiv:1806.03342 (2018).
Qin, X. & Lee, W. Attack plan recognition and prediction using causal networks. In 20th Annual Computer Security Applications Conference , 370–379 (IEEE, 2004).
Husák, M. & Kašpar, J. Aida framework: real-time correlation and prediction of intrusion detection alerts. In: Proceedings of the 14th international conference on availability, reliability and security , 1–8 (2019).
Liu, Y. et al. Cloudy with a chance of breach: Forecasting cyber security incidents. In: 24th USENIX Security Symposium (USENIX Security 15) , 1009–1024 (2015).
Malik, J. et al. Hybrid deep learning: An efficient reconnaissance and surveillance detection mechanism in sdn. IEEE Access 8 , 134695–134706 (2020).
Bilge, L., Han, Y. & Dell’Amico, M. Riskteller: Predicting the risk of cyber incidents. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security , 1299–1311 (2017).
Husák, M., Bartoš, V., Sokol, P. & Gajdoš, A. Predictive methods in cyber defense: Current experience and research challenges. Futur. Gener. Comput. Syst. 115 , 517–530 (2021).
Stephens, G. Cybercrime in the year 2025. Futurist 42 , 32 (2008).
Adamov, A. & Carlsson, A. The state of ransomware. Trends and mitigation techniques. In EWDTS , 1–8 (2017).
Shoufan, A. & Damiani, E. On inter-rater reliability of information security experts. J. Inf. Secur. Appl. 37 , 101–111 (2017).
Cha, Y.-O. & Hao, Y. The dawn of metamaterial engineering predicted via hyperdimensional keyword pool and memory learning. Adv. Opt. Mater. 10 , 2102444 (2022).
Article CAS Google Scholar
Elsevier research products apis. Elsevier Developer Portal https://dev.elsevier.com (2022).
Twitter api v2. Developer Platform https://developer.twitter.com/en/docs/twitter-api (2022).
holidays 0.15. PyPI. The Python Package Index https://pypi.org/project/holidays/ (2022).
Visser, M., van Eck, N. J. & Waltman, L. Large-scale comparison of bibliographic data sources: Scopus, web of science, dimensions, crossref, and microsoft academic. Quant. Sci. Stud. 2 , 20–41 (2021).
2021 trends show increased globalized threat of ransomware. Cybersecurity and Infrastructure Security Agency https://www.cisa.gov/uscert/ncas/alerts/aa22-040a (2022).
Lai, K. K., Yu, L., Wang, S. & Huang, W. Hybridizing exponential smoothing and neural network for financial time series predication. In International Conference on Computational Science , 493–500 (Springer, 2006).
Huang, B., Ding, Q., Sun, G. & Li, H. Stock prediction based on Bayesian-lstm. In Proceedings of the 2018 10th International Conference on Machine Learning and Computing , 128–133 (2018).
Mae, Y., Kumagai, W. & Kanamori, T. Uncertainty propagation for dropout-based Bayesian neural networks. Neural Netw. 144 , 394–406 (2021).
Article PubMed Google Scholar
Scopus preview. Scopus https://www.scopus.com/home.uri (2022).
Jia, P., Chen, H., Zhang, L. & Han, D. Attention-lstm based prediction model for aircraft 4-d trajectory. Sci. Rep. 12 (2022).
Chandra, R., Goyal, S. & Gupta, R. Evaluation of deep learning models for multi-step ahead time series prediction. IEEE Access 9 , 83105–83123 (2021).
Gers, F. A., Schmidhuber, J. & Cummins, F. Learning to forget: Continual prediction with lstm. Neural Comput. 12 , 2451–2471 (2000).
Article CAS PubMed Google Scholar
Sagheer, A. & Kotb, M. Unsupervised pre-training of a deep lstm-based stacked autoencoder for multivariate time series forecasting problems. Sci. Rep. 9 , 1–16 (2019).
Article ADS Google Scholar
Swiler, L. P., Paez, T. L. & Mayes, R. L. Epistemic uncertainty quantification tutorial. In Proceedings of the 27th International Modal Analysis Conference (2009).
Gal, Y. & Ghahramani, Z. Dropout as a bayesian approximation: Representing model uncertainty in deep learning. arXiv preprint arXiv:1506.02142v6 (2016).
Chollet, F. Deep Learning with Python , 2 edn. (Manning Publications, 2017).
Xu, J., Li, Z., Du, B., Zhang, M. & Liu, J. Reluplex made more practical: Leaky relu. In 2020 IEEE Symposium on Computers and Communications (ISCC) , 1–7 (IEEE, 2020).
Gal, Y., Hron, J. & Kendall, A. Concrete dropout. Adv. Neural Inf. Process. Syst. 30 (2017).
Shcherbakov, M. V. et al. A survey of forecast error measures. World Appl. Sci. J. 24 , 171–176 (2013).
Bergstra, J. & Bengio, Y. Random search for hyper-parameter optimization. J. Mach. Learn. Res. 13 (2012).
Kingma, D. P. & Ba, J. Adam: A method for stochastic optimization. arXiv preprint arXiv:1412.6980 (2014).
Krizhevsky, A., Sutskever, I. & Hinton, G. E. Imagenet classification with deep convolutional neural networks. Commun. ACM 60 , 84–90 (2017).
Shifferaw, Y. & Lemma, S. Limitations of proof of stake algorithm in blockchain: A review. Zede J. 39 , 81–95 (2021).
Dedehayir, O. & Steinert, M. The hype cycle model: A review and future directions. Technol. Forecast. Soc. Chang. 108 , 28–41 (2016).
Abri, F., Siami-Namini, S., Khanghah, M. A., Soltani, F. M. & Namin, A. S. Can machine/deep learning classifiers detect zero-day malware with high accuracy?. In 2019 IEEE International Conference on Big Data (Big Data) , 3252–3259 (IEEE, 2019).
Download references
Acknowledgements
The authors are grateful to the DASA’s machine learning team for their invaluable discussions and feedback, and special thanks to the EBTIC, British Telecom’s (BT) cyber security team for their constructive criticism on this work.
Author information
Authors and affiliations.
Department of Computer Science and Information Systems, University of London, Birkbeck College, London, United Kingdom
Zaid Almahmoud & Paul D. Yoo
Huawei Technologies Canada, Ottawa, Canada
Omar Alhussein
Department of Electrical and Computer Engineering, University of Waterloo, Waterloo, Canada
Ilyas Farhat
Department of Computer Science, Università degli Studi di Milano, Milan, Italy
Ernesto Damiani
Center for Cyber-Physical Systems (C2PS), Khalifa University, Abu Dhabi, United Arab Emirates
You can also search for this author in PubMed Google Scholar
Contributions
Z.A., P.D.Y, I.F., and E.D. were in charge of the framework design and theoretical analysis of the trend analysis and TTC. Z.A., O.A., and P.D.Y. contributed to the B-LSTM design and experiments. O.A. proposed the concepts of B-LSTM. All of the authors contributed to the discussion of the framework design and experiments, and the writing of this paper. P.D.Y. proposed the big data approach and supervised the whole project.
Corresponding author
Correspondence to Paul D. Yoo .
Ethics declarations
Competing interests.
The authors declare no competing interests.
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Supplementary information., rights and permissions.
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/ .
Reprints and permissions
About this article
Cite this article.
Almahmoud, Z., Yoo, P.D., Alhussein, O. et al. A holistic and proactive approach to forecasting cyber threats. Sci Rep 13 , 8049 (2023). https://doi.org/10.1038/s41598-023-35198-1
Download citation
Received : 21 December 2022
Accepted : 14 May 2023
Published : 17 May 2023
DOI : https://doi.org/10.1038/s41598-023-35198-1
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
This article is cited by
Integrating ai-driven threat intelligence and forecasting in the cyber security exercise content generation lifecycle.
- Alexandros Zacharis
- Vasilios Katos
- Constantinos Patsakis
International Journal of Information Security (2024)
By submitting a comment you agree to abide by our Terms and Community Guidelines . If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.
Quick links
- Explore articles by subject
- Guide to authors
- Editorial policies
Sign up for the Nature Briefing: AI and Robotics newsletter — what matters in AI and robotics research, free to your inbox weekly.
- Search Menu
- Sign in through your institution
- Editor's Choice
- Author Guidelines
- Submission Site
- Open Access
- About Journal of Cybersecurity
- Editorial Board
- Advertising and Corporate Services
- Journals Career Network
- Self-Archiving Policy
- Journals on Oxford Academic
- Books on Oxford Academic

Article Contents
Exposure to cyberattacks and policy attitudes, the mediating role of threat perceptions, experimental method.
- < Previous
Cyberattacks, cyber threats, and attitudes toward cybersecurity policies
- Article contents
- Figures & tables
- Supplementary Data
Keren L G Snider, Ryan Shandler, Shay Zandani, Daphna Canetti, Cyberattacks, cyber threats, and attitudes toward cybersecurity policies, Journal of Cybersecurity , Volume 7, Issue 1, 2021, tyab019, https://doi.org/10.1093/cybsec/tyab019
- Permissions Icon Permissions
Does exposure to cyberattacks influence public support for intrusive cybersecurity policies? How do perceptions of cyber threats mediate this relationship? While past research has demonstrated how exposure to cyberattacks affects political attitudes, the mediating role played by threat perception has been overlooked. This study employs a controlled randomized survey experiment design to test the effect of exposure to lethal and nonlethal cyberattacks on support for different types of cybersecurity policies. One thousand twenty-two Israeli participants are exposed to scripted and simulated television reports of lethal or nonlethal cyberattacks against national infrastructure. Findings suggest that exposure to cyberattacks leads to greater support for stringent cybersecurity regulations, through a mechanism of threat perception. Results also indicate that different types of exposure relate to heightened support for different types of regulatory policies. People exposed to lethal cyberattacks tend to support cybersecurity policies that compel the government to alert citizens about cyberattacks. People who were exposed to nonlethal attacks, on the other hand, tend to support oversight policies at higher levels. More broadly, our research suggests that peoples’ willingness to accept government cybersecurity policies that limit personal civil liberties and privacy depends on the type of cyberattacks to which they were exposed and the perceptions associated with such exposure.
In recent years, the increase in civilian exposure to cyberattacks has been accompanied by heightened demands for governments to introduce comprehensive cybersecurity policies. These demands peaked in the aftermath of the 2021 Colonial Pipeline and SolarWinds cyberattacks, where the US government's lack of access to cybersecurity information in critical industries wrought havoc on the country's national and economic security. In the aftermath of these attacks, lawmakers and the public exhibited newfound enthusiasm for legislation that would mandate cyberattack reporting by private enterprises—accelerating a regulatory trend that has existed for several years [ 1 ]. In 2020, for example, 40 US states and territories introduced more than 280 cybersecurity related bills and resolutions [ 2 , 3 ]. A similar process has taken place in Europe [ 4 ] and in Israel [ 5 , 6 ].
The public willingness to accept government policies and regulations that limit personal civil liberties and privacy is part of a delicate tradeoff between security and privacy. In some ways, privacy is seen as an adequate cost of enhanced personal and societal security in the face of novel threats. However, the public has grown increasingly sensitive to the importance of online privacy, and is keenly aware of the ethical, political, legal, and rights-based dilemmas that revolve around government monitoring of online activity and communications [ 7 , 8 ].
The debate on digital surveillance centers on how and whether authorities should gain access to encrypted materials, and raise key questions concerning the extent of state interference in civic life, and the protection of civil rights in the context of security. Yet what lies at the heart of this willingness to accept government policies and regulations that limit personal civil liberties and privacy via increasing public demand for government intervention in cybersecurity? Does exposure to different types of cyberattacks lead to heightened support for different types of regulatory policies? And does the public differentiate between interventionist and regulatory forms of cybersecurity policies?
To test these questions, we ran a controlled randomized survey experiment that exposed 1022 Israeli participants to simulated video news reports of lethal and nonlethal cyberattacks. We argue that public support for governmental cybersecurity measures rises as a result of exposure to different forms of cyberattacks, and that perceived threat plays a mediating role in this relationship. More specifically, we propose that exposure to initial media reports about cyberattacks is a key to the exposure effect, since at this time the threat is magnified and the public has minimal information about the identity of the attacker and the type of cyberattack that was conducted. Past events show that in many cases, the public internalizes the details of an attack in its immediate aftermath when media reports are heaviest. While later reports in the days and weeks following an attack will include far more detailed information, the damage by this time has already been done and the public is already scared and alert.
Further to this, we suggest that the literature has erroneously pooled together all cyber regulatory policies under a single banner of cybersecurity. We propose that civilian exposure to different types of cyberattacks leads to increased support for different and specific cybersecurity policies. We therefore differentiate between support for policies that focus on alerting the public in cases of cyberattacks and others that call for oversight of cybersecurity. In examining how exposure to cyberattacks influences support for these specific policy positions, we distinguish between the outcome of cyberattacks—lethal attacks that cause lethal consequences as a first- or second-degree outcome of the attack, versus nonlethal attacks that merely involve financial consequences. This more nuanced breakdown of exposure types and policy options can help officials contend with certain policy debates without the need for a one-size-fits-all policy. For example, reservations expressed by conservative/libertarian scholars who are concerned about government intervention in the commercial marketplace need not disqualify all forms of cybersecurity policy [ 9 ]. Likewise, the reservations of those concerned with individual privacy violations need not lead to the denunciation of all policies [ 10 ].
To ground this analysis of how the public responds following exposure to both lethal and nonlethal cyberattacks, we apply theories associated with the literature on terrorism and political violence. These theories offer sophisticated mechanisms that explain how individual exposure to violence translates into political outcomes—including demands for government intervention and policymaking. This approach is especially applicable in the digital realm as cyberattacks track a middle ground between technological breakthroughs that constitute tactical developments and new strategic weapons [ 11 ]. The consequence of such ambiguity is that civilians who are exposed to digital political threats can only identify the outcomes of the attack—i.e. whether it is a lethal or nonlethal cyberattack—while the motivations and identities of attackers often remain veiled, or at least unsettled. In light of these attributional challenges, and reflecting the fact that the public typically operates in a low-information environment, we refrain from declaring that the cyberattacks that appear in our experimental manipulations are cybercrime, cyberterrorism, cyber-vandalism, or any other type of attack. Rather, we refer to all attacks under the general heading of "cyberattacks," leaving all respondents to react to the attacks in a way that they see as appropriate in light of the severity of the reported outcome.
The most common form of cyberattack is cybercrime. Reports of data breaches resulting from cyberattacks by criminal organizations show a growth of more than threefold between 2011 and 2018 [ 12 ]. In the first half of 2019 alone, the United States Treasury Department announced that there had been 3494 successful cyberattacks against financial institutions resulting in colossal financial losses and the capture of personal information relating to hundreds of millions of people [ 13 ]. Cyberattacks executed by terror organizations are a newer phenomenon, albeit one that has captured the popular imagination. While terror organizations predominantly make use of cyberspace for fundraising, propaganda, and recruitment [ 14 , 15 ], a recent development has been the next-generation capacity of cyber strikes to trigger lethal consequences, be it through first- or second-order effects. 1 We acknowledge that scholars have expressed some skepticism about the likelihood of impending destructive cyberterror incidents [ 16–18 ], yet national security officials have regularly predicted that lethal cyberattacks pose a "critical threat" [ 19 ]. In the last decade, the nature of this threat has evolved from the earlier depictions of an apocalyptic cyber "pearl harbor" that would ravage modern society from the shadows [ 20 ], to a more nuanced understanding that cyberattacks, while still posing a threat to critical infrastructure, are more likely to manifest through targeted strikes. For example, in April 2020, Israel narrowly averted a cyberattack targeting civilian water networks that would have killed scores of civilians by adding chlorine to the water supply [ 19 ]. Other physically destructive cyberattacks have caused explosive damage to critical infrastructure [ 21 ], while researchers have experimentally verified the ability of malicious digital actors to hack pacemakers and insulin pumps [ 22 ]. While the lethal stature of cyberattacks is still developing, these incidents establish the bona fides of this impending threat and the importance of understanding how the public responds to this type of event.
The discussion that follows has four parts. We begin by examining the theory of how exposure to violence translates into policy preferences, with a particular focus on the mediating role of threat perception. Second, we discuss the design of our controlled, randomized experiment that exposes participants to television news reports of lethal and nonlethal cyberattacks. Third, we present our main results and consider various mediation models that pertain to the different regulatory subsets. We conclude by discussing the implications of our findings for the study of cybersecurity and cyber threats more generally.
Civilians who are exposed to political violence often suffer from feelings of trauma, anxiety, and helplessness in the face of threatening external forces [ 23–25 ]. These emotional responses—whether caused by acts of cyber or conventional violence—are known to cause shifts in political attitudes. Research has shown how exposure to conventional terrorism, which targets civilians and disrupts their daily routines, has an impact on individuals’ support for attitudes toward peace and compromise with the other [ 26 ], political conservatism [ 27 ], exclusionism [ 28 ] and intragroup relations [ 29 ].
Despite the sizeable literature dealing with the effects of exposure to violence, few studies directly investigate the effects of exposure to destructive cyberattacks. This is despite the growing recognition that these threats have become a very tangible part of modern life. In a complex scenario described in the Tallinn Manual 2.0 on the International Law Applicable to Cyber Warfare, the authors contemplated how new forms of cyberattacks could be used to “acquire the credentials necessary to access the industrial control system of a nuclear power plant… with the intent of threatening to conduct cyber operations against the system in a manner that will cause significant damage or death…” [ 30 ]. Even more recently, reports have acknowledged how cyberterror attacks could immobilize a country's or region's electrical infrastructure [ 31 ], disable military defense systems [ 32 ], and even imperil nuclear stability [ 33 ]. While there is a difference between capability and intent, and we acknowledge that physically destructive cyber threats have remained scarce until now, understanding how civilians respond to such digital cyberattacks will become particularly important as the threat matures.
Studies that directly investigated exposure to digital political violence found that exposure had significant effects on political behavior and attitudes, akin to exposure to conventional political violence [ 34 , 35 ]. In a series of exploratory studies regarding the phenomena of cyberterrorism, Gross et al . [ 34 , 36 ] sought to empirically measure the effects of exposure to cyberterrorism under controlled experimental conditions. Their key finding was that exposure to cyberterrorism was severe enough to generate significant negative emotions and cognitive reactions (threat perceptions) at equivalent levels to those of conventional terror acts. Canetti et al . [ 37 ] found that victims of cyberattacks react by demanding government protection, with psychological distress explaining the relationship between exposure and the demand for government intervention. In a subsequent biologically focused experiment, Canetti et al . measured cortisol levels to show how participants who are exposed to cyberterror attacks and experience higher levels of stress are more likely to support hardline retaliatory policies [ 38 ].
Building on this foundation, other research has sought to refine a more precise psycho-political mechanism that understands how cyberattacks trigger shifts in political attitudes. Research by Shandler et al . [ 39 , 40 ], e.g. found that only lethal cyberattacks cause political consequences akin to conventional political violence, and that only the emotion of anger explained these shifts.
In the current paper, we aim to add to this emerging body of research by examining the topic of cybersecurity preferences in the aftermath of lethal and nonlethal cyberattacks. While one past study by Cheung-Blunden et al . [ 41 ] examined how emotional responses to cyber incidents sway cybersecurity preferences, no research has yet attempted to analyze how different types of cyberattacks affect different kinds of cybersecurity policies. As such, we add much needed nuance to the literature.
For the purpose of considering the effects of exposure to cyberattacks, this research focuses on the "outcome" of a cyberattack rather than the "identity" of the perpetrator or the "classification" of the attack. This is necessary for several reasons that relate to the specific characteristics of cyberspace. First, as introduced above, a new class of cyberattack exemplified by the ransomware epidemic has exhibited characteristics of both cybercrime and cyberterror operations, impeding the classification of cyber incidents into simple categories. Second, attribution in cyberspace is fraught with difficulty, and an age of manipulated information complicates the determination of provenance [ 42–44 ]. Sophisticated cyber operatives working from anywhere in the world can exploit the principle of anonymity that underlies the Internet infrastructure to hide their identity. Though authorities would be able to quickly identify the identity of an attacker behind any major cyberattack [ 42 ], this is essentially impossible for members of the public who are confronted with both structural and technical obstacles that prevent them from rendering an objective judgement about the attack source. This reality of publicly obscured cyber antagonists can be viewed in the timelines of several famous cyber incidents. It took between six months and three years for authorities and private actors to publicly reveal the actors behind the 2017 WannaCry attacks, the 2016 cyber intrusion into the Democratic National Committee's networks, and the 2016 cyberattack against the Bowman Dam in New York [ 45–47 ]. While each of these incidents were eventually attributed to an attack source, and the authorities may well have known the identity of the attacker from an early date, we can see that from the perspective of the public, there was a time lag of several months or years before a name was attached to any attack. Third, state involvement in cyberattacks—either as a direct attacker or via proxies—can add substantial background noise to the perception of an attack, raising the specter of interstate war. There is an interesting debate in the literature about whether states may be deemed capable of conducting cyberterrorism—or whether this is a label that can only be applied to nonstate actors. While the literature is still unsettled on this point, Macdonald, Jarvis and Nouri [ 48 ] found considerable expert support for the proposition that states can engage in cyberterrorism.
It is for these reasons that we choose to follow the lead of the scholars who are beginning to evaluate responses to cyber threats through the prism that is most readily available for the public—specifically, the outcome variable, or in other words, the lethality of the attack [ 33 ]. This focus on outcome rather than attacker is necessary in order to understand the factors that prompt emotional and political responses in the public. While these information asymmetries explain our focus on the outcome of the attack rather than the identity of the attacker, we acknowledge that the people draw inferences about the identity and motivations of attackers based on prior experiences and political orientation [ 49 ]. Liberman and Skitka's vicarious retribution theory [ 50 , 51 ] demonstrates how the public may impute responsibility to unrelated or symbolically related offenders when the identity of an attacker is unclear. Nonetheless, maintaining the highest standards of ecological validity demands that attribution and attack categorization is absent in initial public reports of cyber incidents.
Under this framework, we hypothesize that:
Hypothesis 1: Exposure to (i) lethal or (ii) nonlethal cyberattacks will lead to greater support for adopting cybersecurity policies compared with people who were not exposed to any cyberattack. In other words, exposure to cyberattacks—lethal (LC) or nonlethal (NLC)—will increase support for adopting cybersecurity policies, as compared with a control group.
Hypothesis 2: People who are exposed to lethal cyberattacks (LC) will exhibit to higher support for adopting cybersecurity policies than people who are exposed to nonlethal cyberattacks (NLC).
Civilians are notoriously weak at accurately assessing security threats—a fact that is amplified in the cyber realm due to low cybersecurity knowledge, general cognitive biases in calculating risk, and the distortion of cyber risks by the media, which focuses predominantly on spectacular yet low-likelihood attacks [ 52–54 ]. Perceived risk is partly reliant on the scope of the attack to which people are exposed. Victims of cybercrimes (identity theft and cyber bullying) report moderate or severe emotional distress such as anger, fear, anxiety, mistrust, and loss of confidence [ 55 ]. The effects of conventional terrorism include post-traumatic stress, depression, and anticipatory anxiety [ 56 , 29 ]. In both of these cases, threat perception is a common predictor of political attitudes and behavior. Indeed, the best predictor of hostile out-group attitudes is the perceived threat that out-group members will harm members of the in-group, whether physically, economically or symbolically [ 28 , 57 , 58 ]. In many of the studies cited above, threat perception was found to mediate the relationship between exposure to violence and support for harsh or restrictive policies, especially in conflict-related contexts [ 27 ]. Extending this empirical and theoretical evidence to digital political violence suggests that individuals are likely to respond similarly to cyber threats by supporting strong cybersecurity policies through the interceding influence of heightened threat perception.
A set of early studies compared the level of threat evoked by exposure to different forms of cyber threats, identifying key differences in the how cybercrime and cyberterrorism influenced attitudes toward government policy [ 34 , 36 ]. These studies concluded that direct exposure to cyberterrorism had no effect on support for hardline cybersecurity policies (increased digital surveillance, the introduction of intrusive new regulations), but threat perceptions relating to cyberterrorism successfully predicted support for these policies. Recognizing therefore that threat perception plays a central role in understanding the response to cyberattacks, we predict that
Hypothesis 3: Cyber threat perception will mediate the relationship between individual exposure to cyberattacks and support for cybersecurity policies.
To test our hypotheses, we conducted a controlled survey experiment that exposed respondents to simulated news reports about major cyberattacks. The experimental manipulation relied on professionally produced original video clips that broadcast feature news reports. The lethal treatment group viewed a feature report discussing several lethal cyberattacks that had taken place against Israeli targets, while the nonlethal treatment group broadcast a collection of stories pertaining to nonlethal cyber incidents (see below for additional details about each manipulation). The control group did not watch any news report.
We utilized the medium of video news reports for our experimental manipulation since experiments in recent years have shown how broadcast videos and media reports of major attacks arouse strong emotions among viewers, which in turn trigger reevaluations of policy positions and political attitudes related to issues of security [ 35 , 59 , 60 ]. The rationale behind these finding can be partly explained by Terror Management Theory, which explains how even indirect exposure to violent acts triggers potent emotional reactions as people confront threats to their mortality [ 61 , 62 ]. Just as importantly, news reports are a key avenue by which the public learns about major security incidents, and so this method maintains its ecological validity. Each of the groups completed a pre- and post-survey, answering a series of questions about their attitudes to cybersecurity along with relevant sociodemographic information.
Each of the television news reports was presented as an authentic feature story that appeared on Israeli channel 1 television station. The news reports described the global scale of cyber threats facing the public (i.e. two million malicious web sites launch each month and 60 000 new malware programs appear every day at an annual cost to the global economy of 500 billion dollars). The clips were screened in a feature format using on-camera interviews, voiceover and film footage to describe various cyberattacks. To increase the authenticity of the experience, the reports included interviews with well-known Israeli security experts. To mimic the challenges of cyber attribution, the perpetrators of the attacks described in the videos were not identified and were neutrally referred to as cyber operatives. Each video lasted approximately 3 min.
Lethal Cyber Condition—The television news report described various cyberattacks with lethal consequences that had targeted Israel during the previous years. For example, in one of the featured stories, an attack was revealed to have targeted the servers controlling Israel's electric power grid, cutting off electricity to a hospital and causing deaths. In another story, cyber operatives were said to have attacked a military navigation system, altering the course of a missile so that it killed three Israeli soldiers. A third story concerned the use of malware to infect the pacemaker of the Israeli Defense Minister, and a fourth involved the failure of an emergency call to 10 000 military reserve soldiers due to a cyberattack in which foreign agents changed the last digit of the soldiers’ telephone numbers in the military database. The video's interviews with well-known figures from Israel's security sector emphasized the life-threatening danger posed by cyberattacks.
Nonlethal Cyber Condition—The television news report revealed various nonlethal cyberattacks that had targeted Israel during recent years. For example, the broadcast explained how mobile phone users are made vulnerable to attackers by installing new games and applications, potentially introducing malware that can later access data like personal messages or financial details. Another example concerned the dangers posed by the Internet of Things and featured a story in which all the major credit cards companies suspended their customer support after hundreds of thousands of citizens were fraudulently charged for food purchases by their smart refrigerators. The Israeli experts in this video emphasized the potential financial damage from cyberattacks.
Participants
The online survey experiment was administered in Israel during September 2015 via the Midgam Survey Panel. One thousand twenty-two participants were randomly assigned to the three groups (lethal condition: N = 387; nonlethal condition: N = 374; control group: N = 361). The experimental sample represents a random cross-section of the Jewish Israeli population. The sample is largely representative of the wider population, and balance checks reveal that the treatment distribution is acceptable. We note that due to data collection constraints, the sample does not include ultra-orthodox (religious) respondents due to difficulties in accessing this subgroup through online methods. The mean age of the participants was 41 (SD = 14.81), and gender distribution of 49.96% male and 50.04% female. With respect to political orientation, 44.35% of the sample define themself as right-wing ( N = 452), 38.28% themselves as centrist ( N = 390), and 17.37% as left-wing ( N = 177) (this reflects the right-wing slant of the Israeli population that has been apparent in recent elections). The distribution of education and income levels was similar across the three groups (Education: F(2, 1120) = 0.20, P < 0.82; Income: F(2, 1045) = 0.63, P < 0.53). Sociodemographic characteristics of the participants are presented in Appendix A (Supporting Information), together with experimental balance checks.
The experiment incorporated three primary variables: the predictor variable (exposure to cyberattacks), the dependent variable (support for cybersecurity policies), and the mediator variable (threat perception). Sociodemographic measures were also collected.
Predictor variable—exposure to cyberattacks
Exposure to cyberattacks was operationalized by random assignment to one of the three experimental treatments described above—lethal cyberattacks/nonlethal cyberattacks/control condition.
Dependent variable: support for cybersecurity policies
Support for cybersecurity policies was examined using twelve questions taken from two scales developed by McCallister and Graves [ 63 , 64 ]. After separating out one item that reflected a unique form of cybersecurity policy, the remaining items were subjected to a principal component analysis (PCA), which highlighted different aspects of cybersecurity policy. Our criteria for the factor dimension extraction was an eigenvalue greater than one for number of dimensions, and factor loading greater than 0.35, for dimension assignment. We applied the PCA extraction method with the Varimax rotation to construct orthogonal factors [ 65 ]. This procedure gave rise to two clearly distinguishable cyber policy dimensions. Following this process, we combined the two remaining items that were excluded due to poor loadings (loading < 0.35) to create a third policy dimension with a high correlation between the items ( r = 0.617, P < 0.001) (see Appendix B in the Supporting Information for the PCA and complete list of the items used to construct each scale). The final three measures of cybersecurity policies reflected the breadth of available policy options, which emphasized different levels of government intervention and oversight strategies. The first of these is cybersecurity prevention policy (CPP); the second is cybersecurity alert policy (CAP); and the third is cybersecurity oversight policy (COP).
The cybersecurity prevention policy dimension (CPP) captures the idea that the state should mandate commercial companies to implement minimum levels of cybersecurity to prevent damage. Respondents were asked questions such as: “should the state compel business owners to protect themselves against cyberattacks?” Cronbach's α was within an acceptable range at 0.720.
The cybersecurity oversight policy dimension (COP) refers to the notion that the state should directly intervene to offer cyber protection to its citizens and businesses. Relevant questions for this dimension included “should the state protect its citizens from cyberattacks?” Cronbach's α was within an acceptable range at 0.737.
The cybersecurity alert policy dimension (CAP) relates to the state's presumed responsibility to ensure citizens are alerted when a hack of a cyberattack is discovered. For example, a related question would ask: “should the state alert citizens after a successful attack on critical infrastructure?” As opposed to the prevention policy dimension that relates to measures that must be taken before a cyberattack, the alert policy focuses on the measures to be taken after an attack. Cronbach's α was slightly below acceptable range at 0.632. All questions were measured on a scale ranging from 1 (“completely disagree”) to 6 (“completely agree”).
Mediator: perceptions of cybersecurity threats
Threat perception pertaining to cyber threats was gauged using a five-item scale based on studies conducted in the United States [ 66 ]. Respondents were asked how concerned they feel about the possibility of an actual threat to their security. Respondents answered questions including: “To what extent does the idea of a cyberattack on Israel affect your sense of personal security?” and “To what extent does a cyberattack on Israel threaten the country's critical infrastructure?,” and the answers ranged from 1 (“not at all”) to 6 (“to a very great degree”). The internal consistency of this measure was very high (Alpha = 0.913).
Control variables
Control variables collected included political ideology (assessed through a self-reported five-point scale ranging from 1 [very conservative] to 5 [very liberal]), age, gender, marital status, religiosity, education, and income.
We also measured and controlled for participants’ past exposure to cyberattacks. To measure this variable, we adapted a four-item scale used to measure exposure to terrorism and political violence [ 67 , 35 ]. Items included questions that asked the extent to which the respondents, their friends and their family had ever suffered harm or loss from a cyberattack. Similarly to past studies, we did not calculate the internal reliability for past exposure, given that one type of exposure does not necessarily portend another type.
Preliminary analyses
We begin our analysis by testing the variance between the treatment groups regarding attitudes toward cybersecurity policies, to establish that the experimental conditions produce at least minimal levels of differences in the dependent variables. Hence, we conducted a one-way univariate analysis of variance (ANOVA), in which the different cyber policies were the dependent variables. The results indicated differences between the three groups in support for policies regarding cybersecurity alerts (CAP: F(2, 1020) = 4.61, P < 0.010). No differences between groups were found in support for cybersecurity prevention policy or cybersecurity oversight policy (CPP: F(2, 1020) = 1.35, P < 0.259; COP: F(2, 1020) = 0.94, P < 0.39). We followed the CAP ANOVA analysis with pairwise comparisons using Bonferroni corrections, which revealed that the highest level of support for cybersecurity alerts was expressed by the group exposed to lethal cyberattacks on average, while the other two groups showed lower levels of support for this policy. These results support the conclusion that the differences in cybersecurity policy preferences between the three groups derive from the video stimulus, and not from differences in participants’ sociodemographic characteristics (see Appendix C in the Supporting Information for means and standard deviations of study variables, in all three manipulation groups).
In addition, we tested group differences regarding threat perceptions and found significant differences in threat perceptions between the three groups (F(2, 1020) = 21.68, P < 0.001). The follow up pairwise comparisons with Bonferroni corrections, revealed that participants in both experimental groups (LC and NLC) expressed higher levels of threat perceptions in comparison to participants in the control group. These analyses provide sufficient preliminary support to conduct more complex analyses that integrate multiple effects in this triangle of exposure to cyberattacks, cyber threat perception, and support for cybersecurity policies.
Mediation analysis
To test hypothesis 3, we ran a path analysis model, i.e. a structural equation modeling with observed indicators only. In this model, the exposure was divided into lethal vs control and nonlethal vs control. More specifically, with regard to the mediation effect, the model structure included two pathways from the experimental conditions to support for cybersecurity policies: From the lethal vs control, and from nonlethal vs control through threat perceptions. The latter variable was expected to mediate the effect condition effects on cyber policy positions as proposed in the theory section.
In order to further investigate the mediation mechanism, we constructed an integrative path analysis model [ 53 ]. Running this model enables us to identify direct and indirect effects among all the study variables. We provide modeling results in the following Table 1 and an illustration of the path analysis model in Fig. 1 .

Empirical model results—direct effects of exposure to lethal and nonlethal attack groups vs control group. * P < 0.05, ** P < 0.01, *** P < 0.001.
Path: analysis direct effects, standardized estimates
| . | Threat (M) . | CAP (Y ) . | COP (Y ) . | CPP (Y ) . |
|---|---|---|---|---|
| . | Beta (S.E.) [95% CI] . | Beta (S.E.) [95% CI] . | Beta (S.E.) [95% CI] . | Beta (S.E.) [95% CI] . |
| 0.058***(0.035)[0.088, 0.262] | 0.249***(0.030) [0.151, 0.275] | 0.273*** (0.032)[0.193, 0.335] | ||
| ) | ||||
| 0.163***(0.034)[0.077, 0.221] | –0.070*(0.036)[–0.164, –0.012] | –0.073*(0.036)[–0.168, –0.017] | –0.043(0.037)[0.030, 0.077] | |
| ) | ||||
| 0.207***(0.033)[0.123, 0.258] | –0.140***(0.035)[–0.230, –0.080] | –0.024(0.034)[–0.105, 0.035] | –0.015(0.035)[–0.101, 0.046] | |
| 0.109***(0.031)[0.028, 0.164] | –0.012(0.030)[–0.088, 0.036] | –0.005(0.030)[–0.083, 0.035] | 0.016(0.030)[–0.063, 0.064] | |
| 0.200***(0.030)[0.125, 0.254] | 0.072*(0.032)[–0.011, 0.126] | 0.010(0.031)[–0.070, 0.060] | 0.050(0.031)[–0.030, 0.095] | |
| 0.034 (0.031)[–0.051, 0.085] | –0.044(0.036)[–0.137, 0.013] | 0.088**(0.031)[0.004, 0.137] | 0.015(0.033)[–0.075, 0.066] | |
| –0.049 (0.032)[–0.131, 0.097] | –0.028(032)[–0.124, –0.028] | –0.027(0.031)[–0.104, 0.022] | –0.033(0.033)[–0.117, 0.017] | |
| 0.035 (0.033)[–0.045, 0.097] | 0.050(0.032)[–0.025, 0.106] | 0.027(0.033)[–0.063, 0.082] | –0.040(0.033)[–0.127, 0.024] | |
| 0.093***(0.017) | 0.047***(0.014) | 0.074***(0.015) | 0.087***(0.018) |
| . | Threat (M) . | CAP (Y ) . | COP (Y ) . | CPP (Y ) . |
|---|---|---|---|---|
| . | Beta (S.E.) [95% CI] . | Beta (S.E.) [95% CI] . | Beta (S.E.) [95% CI] . | Beta (S.E.) [95% CI] . |
| 0.058***(0.035)[0.088, 0.262] | 0.249***(0.030) [0.151, 0.275] | 0.273*** (0.032)[0.193, 0.335] | ||
| ) | ||||
| 0.163***(0.034)[0.077, 0.221] | –0.070*(0.036)[–0.164, –0.012] | –0.073*(0.036)[–0.168, –0.017] | –0.043(0.037)[0.030, 0.077] | |
| ) | ||||
| 0.207***(0.033)[0.123, 0.258] | –0.140***(0.035)[–0.230, –0.080] | –0.024(0.034)[–0.105, 0.035] | –0.015(0.035)[–0.101, 0.046] | |
| 0.109***(0.031)[0.028, 0.164] | –0.012(0.030)[–0.088, 0.036] | –0.005(0.030)[–0.083, 0.035] | 0.016(0.030)[–0.063, 0.064] | |
| 0.200***(0.030)[0.125, 0.254] | 0.072*(0.032)[–0.011, 0.126] | 0.010(0.031)[–0.070, 0.060] | 0.050(0.031)[–0.030, 0.095] | |
| 0.034 (0.031)[–0.051, 0.085] | –0.044(0.036)[–0.137, 0.013] | 0.088**(0.031)[0.004, 0.137] | 0.015(0.033)[–0.075, 0.066] | |
| –0.049 (0.032)[–0.131, 0.097] | –0.028(032)[–0.124, –0.028] | –0.027(0.031)[–0.104, 0.022] | –0.033(0.033)[–0.117, 0.017] | |
| 0.035 (0.033)[–0.045, 0.097] | 0.050(0.032)[–0.025, 0.106] | 0.027(0.033)[–0.063, 0.082] | –0.040(0.033)[–0.127, 0.024] | |
| 0.093***(0.017) | 0.047***(0.014) | 0.074***(0.015) | 0.087***(0.018) |
Standard error in parentheses; * P < 0.05, ** P < 0.01, *** P < 0.001. NLC = non-ethal cyberattack; LC = lethal cyberattack.
Direct effects
Table 1 presents the results of the standardized estimates (beta coefficients) of each experimental group vis-à-vis the control group (i.e. NLC vs control, and LC vs control), perceptions of threat, past exposure to cyberattacks and socio demographic variables—gender, religiosity, education and political ideology—with the three dimensions of cybersecurity policies as the dependent variables. In the pairwise comparison of the experimental groups, which compares the lethal and nonlethal conditions to the control group, we find a larger direct effect in the LC (lethal) group compared with the NLC (nonlethal) group in predicting support for CAP.
A follow-up that compared the two regression weights further confirmed the stronger relative effect of the lethal exposure over the nonlethal exposure (H 2 : NLC-LC = −0.21 (0.10), P = 0.047). This demonstrates support for our second hypothesis. People who were exposed to lethal cyberattacks tended to support cybersecurity policies that compel the government and security forces to alert citizens if they have evidence of citizens’ computers being hacked or if an act cyberattack is discovered (CAP) at higher levels than people who were exposed to nonlethal/economic cyberattacks compared with people in the control group.
Interestingly, this trend was reversed for the oversight policies (COP) form of cybersecurity regulation. Here, we identified a significant direct effect wherein exposure to nonlethal cyberattacks led to support for oversight policies (COP) at higher levels than respondents who were exposed to the lethal cyberattacks manipulation or the control group. However, the difference between the two treatment conditions was not significant (NLC-LC = 0.11(0.08), P = 0.16). This indicates that exposure to any kind of cyberattack, lethal or nonlethal, predicts greater support for oversight regulation policies (COP) to the same extent. No direct effect was found between exposure to cyberattacks and support for prevention regulation policies (CPP). By breaking apart this analysis into different dimensions of cybersecurity polices our results reveal how exposure to different forms of cyberattacks contribute to support for distinct types of policy that emphasize oversight or intervention.
Most importantly, results indicate a significant direct effect of threat perceptions on all three dimensions of cybersecurity policy and higher levels of threat perception in the lethal cyber manipulation group compared with the nonlethal cyber manipulation group and the control group.
Mediating effects
Table 2 presents the indirect effects of each of the two treatment conditions in comparison to the control group for the three dimensions of cybersecurity policies—with threat perception as a mediator. The indirect effects are pathways from the independent variable to the policy variables through threat perceptions. In the path analysis model, each dependent variable, i.e. support for particular cybersecurity policies, could have two potential paths, one from the nonlethal condition and the one from the lethal condition. Altogether, six mediation pathways were tested. These indirect outcomes are illustrated in Fig. 1 . In the LC group we see a complete mediation effect of threat perceptions and no significant direct effect of exposure on COP support. This means that for those participants who were exposed to the lethal condition, the actual exposure was not as strong a predictor of policy support as the threat perception associated with the attacks.
Path: analysis mediation effects, standardized estimates
| . | Independent . | Mediation . | Outcome . | Indirect effect (coefficient; S.E. [95% CI]) . |
|---|---|---|---|---|
| Mediation 1 | NLC/Control (X ) | Threat | CAP | 0.026***; 0.008 [0.010, 0.042] |
| Mediation 2 | LC/Control (X ) | Threat | CAP | 0.033***; 0.009 [0.015, 0.050] |
| Mediation 3 | NLC/Control (X ) | Threat | COP | 0.041***; 0.010 [0.020, 0.060] |
| Mediation 4 | LC/Control (X ) | Threat | COP | 0.052***; 0.011 [0.028, 0.071] |
| Mediation 5 | NLC/Control (X ) | Threat | CPP | 0.045***; 0.011 [0.021. 0.066] |
| Mediation 6 | LC/Control (X ) | Threat | CPP | 0.056***; 0.011 [0.030, 0.077] |
| . | Independent . | Mediation . | Outcome . | Indirect effect (coefficient; S.E. [95% CI]) . |
|---|---|---|---|---|
| Mediation 1 | NLC/Control (X ) | Threat | CAP | 0.026***; 0.008 [0.010, 0.042] |
| Mediation 2 | LC/Control (X ) | Threat | CAP | 0.033***; 0.009 [0.015, 0.050] |
| Mediation 3 | NLC/Control (X ) | Threat | COP | 0.041***; 0.010 [0.020, 0.060] |
| Mediation 4 | LC/Control (X ) | Threat | COP | 0.052***; 0.011 [0.028, 0.071] |
| Mediation 5 | NLC/Control (X ) | Threat | CPP | 0.045***; 0.011 [0.021. 0.066] |
| Mediation 6 | LC/Control (X ) | Threat | CPP | 0.056***; 0.011 [0.030, 0.077] |
Standard error in parentheses; * P < 0.05, ** P < 0.01, *** P < 0.001. In squared brackets 95% confidence interval with bias correction bootstrapping ( n = 2000).
In our models predicting CAP, we see a partial mediation effect for both treatment groups, in addition to the direct effect that we described above. We see a larger indirect effect in the LC group than in the NLC group and this was confirmed by a test of difference. This indicates that people who were exposed to lethal cyberattacks reported higher levels of cyber threat perception as compared with people who were exposed to the nonlethal condition, and this heightened threat perception in turn led to more support for various cybersecurity polices.
Support for CAP (i.e. cybersecurity policies whereby the government or relevant organizations are expected to alert citizens if they have evidence of citizens’ computers being hacked or an act of cyberattack being detected) was predicted both by a direct effect of level of exposure to cyberattacks (NLC, LC) and by the mediation of threat perceptions.
Yet our models predicting support for oversight polices (COP) showed a different picture. In the NLC group we see a partial mediation of threat perceptions in addition to the direct effect that we found in the models shown in Table 2 . Support for COP (i.e. cybersecurity policies whereby the state should protect the country, organizations, and citizens from cyberattacks through direct government action) was predicted by a direct effect of NLC exposure and by the mediation of threat perceptions in both LC and NLC groups. In the LC group versus the control group, support of COP was predicted only through the mediation perceptions of threat. These results support our third hypothesis regarding the mediating role played by threat perception in predicting COP.
Our models predicting support for prevention policies (CPP) showed a complete mediation effect of threat perception in both experimental treatment groups. No direct effect of exposure on CPP was found, indicating that the mediating mechanism is the best predictor for CPP. Support for CPP (i.e. cybersecurity policies whereby the state compels commercial enterprises to install minimum thresholds of cybersecurity) was predicted by the indirect effect of threat perception.
These results emphasize the central role played by threat perception in predicting support for adopting stringent cybersecurity policies. What is especially noteworthy is that threat perception overrides past experience as the full mediation models indicate. For example, we found that when people are exposed to destructive cyberattacks, the level of perceived threat predicted support for adopting cybersecurity policies that required the state to protect citizens and organizations (COP). Similarly, we found that when it comes to predicting support for prevention policies—threat is the driving force.
In order to complement the indirect effect analyses and test the relative strength of the mediation pathways, we contrasted the indirect effects of the various groups on each policy option. According to the outcome estimates in Table 2 , model 3 has a significantly larger mediation effect compared with model 1 (difference = –0.014; 0.024 P < 0.001) 2 , which indicates that within the NLC group, the mediation model is a stronger predictor of support for COP than CAP. In other words, participants who were exposed to the nonlethal condition were more likely to support oversight polices than alert policies.
Our findings draw on an experimental design that suggests that exposure to different types of cyberattacks intensifies perceptions of cyber threats and shifts political attitudes in support of stringent cybersecurity policies. We find that exposure to lethal cyberattacks affects individual-level political behavior in a manner akin to conventional terrorism [ 68–71 ]. This research was motivated by a desire to better understand what drives individuals to support strong or hardline cybersecurity policies, using Israel as a case study. The findings contribute to this research direction in a number of important ways.
First, exposure to lethal cyberattacks heightens perceptions of cyber threat to a greater degree than nonlethal/economic cyberattacks. Second, as a result of exposure to cyberattacks, respondents were willing to forfeit civil liberties and privacy in exchange for more security. Like conventional terrorism, cyberattacks with lethal consequences harden political attitudes, as individuals tend to support more government oversight, greater regulation of cybersecurity among commercial businesses, and the implementation of strategies to increase public awareness following cyberattacks. Third, our data suggest that in some cases the mere exposure to cyberattack, either lethal or nonlethal, affects the level of support for specific types of cybersecurity polices (stronger support of cybersecurity alert policies among participants in the lethal cyberattack manipulation, and stronger support of cybersecurity oversight policy among participants in the nonlethal cyberattack treatment group). In other cases, threat perception, rather than the exposure to the cyber-events themselves, drive the cognitive effects of cyberattacks on attitudes toward policy (A strong support for COP among the LC group was predicted only through the mediating role of threat perception, and support of CPP, in both manipulation groups was predicted only through a mediated pathway). Finally, we observed differences in the way our mediation model works in relation to different cybersecurity policies. The mediation model for the nonlethal condition group participants predicted greater support for cybersecurity policies focusing on oversight rather than policies focusing on alerting the public.
Our study examined public support for three distinct types of cybersecurity policies that we described as prevention policies, alert policies, and oversight policies. Each of these play a role in securing cyberspace, where the uncertainty regarding the form and nature of potential threats calls for a varied array of preventive actions [ 36 , 37 ]. Each of these policies raises questions about the delicate balancing act between privacy and security demands. In reality, policy approaches are likely to combine several of these elements—yet it behooves us to first consider each of them independently since very little is known about the public knowledge and familiarity with different cybersecurity policies. While preliminary research has looked at public support for cybersecurity preferences in general [ 41 ], these have yet to consider the varied approaches to cybersecurity. To that end, in the current paper we tried to simplify the different cybersecurity polices as much as possible based on real-world policies.
Overall, the study provides evidence that exposure to cyberattacks predicts support for cybersecurity policies through the mediating effect of threat perception. Yet our discovery of differential effects depending on the type of cybersecurity policy being proposed adds a new level of nuance that should be probed further in subsequent studies. More so, results indicate that the public worry and concern in the aftermath of cyberattacks leads directly to calls for governmental intervention. This information sheds light on public opinion processes and helps inform our understanding how individuals will likely respond to new cyber threats. It may also help policymakers understand the complex emotions and cognitions evoked by attacks, which can improve policy formulations that respond to the needs of the public.
Future studies should also investigate how fear appeals intervene in this mechanism, and how to motivate people to take cyber threats more seriously in a way that leads to positive behavioral change.
Participants who were exposed to the lethal manipulation supported cybersecurity policies that focus on alerting the public in cases of cyberattacks more than participants in the two other groups. On the other hand, participants who were exposed to the nonlethal manipulation tended to support cybersecurity policies that call for state oversight of cybersecurity. We found no evidence that any type of exposure has a direct effect on support for polices mandating minimum thresholds of cybersecurity in the commercial arena.
One possible explanation for these results is that thus far, cyberattacks have caused economic damage, but lethal cyberattacks that vividly resemble terrorism are a significantly rarer phenomenon. Hence, participants who were exposed to lethal terror cyberattacks supported cybersecurity policies that would alert them and keep them informed about impending cyber threats. Policies that focus on oversight are perceived as less important during violent terror attacks. On the other hand, exposure to nonlethal cyberattacks, which are typically focused on economic gain, is more common. The economic damage caused by cyberattacks is estimated to reach $6 trillion by 2021 [ 72 ]. As such, participants in the nonlethal manipulation may have regarded cyberattacks causing economic damage as more likely and therefore supported polices that will bolster digital protections.
We note a key condition about the temporal nature of these findings. In analyzing the effect of exposure to cyberattacks, this study focuses on people's immediate response following exposure to cyber threats. Assessing people's short-term responses is valuable as the responses speak to the direction of the political and psychological effects. Yet what is missing from this picture (and beyond the scope of our research design), is the longevity of the response, which speaks to the strength of the effect. If the measured distress and political outcomes swiftly dissipate, then the policy relevance of our findings comes into question.
The literature is split on the question of the temporal durability of attitudinal shifts in the aftermath of major attacks. There is one school of thought that holds that most political effects stemming from political violence or terrorism are fleeting, and that the public is broadly desensitized to political violence [ 73–75 ]. Yet a second school of thought suggests that exposure to attacks can trigger prolonged effects and lasting shifts in political and psychological attitudes. Brandon & Silke [ 76 ] assert that while the distress triggered by exposure dissipates over time, this is not an instantaneous process. Several longitudinal studies following the Oklahama bombing and 9/11 found lingering harms, with exposed individuals reporting elevated levels of psychological distress and altered political attitudes for months or years following the event [ 77–79 ].
In applying this to the case of cyberattacks, there is insufficient evidence to positively determine the longevity of the political and psychological effects that we identified in our study. We anticipate that the effects will be more than fleeting, since the novelty of cyber threats means that people have yet to undergo any cognitive or emotional desensitization to cyberattacks [ 80 ]. However, we acknowledge that this this position requires further empirical substantiation in future research.
A central conclusion of this study is that the implementation of cybersecurity regulations should take account of public perception of cyber threats and public exposure to cyberattacks. This position challenges two unspoken yet ubiquitous notions in the field of cybersecurity. First, the formulation of cybersecurity policies—in a manner akin to national security and espionage discussions—has typically taken place without public input due to the perception that it is a question best left to experts with engineering or national security expertise [ 81 ]. Scholars argue that this complete abdication of cybersecurity policy to specialists is a profound mistake, since excluding “the general public from any meaningful voice in cyber policymaking removes citizens from democratic governance in an area where our welfare is deeply implicated” [ 82 ]. Functional cybersecurity relies on good practices by the ordinary public, and the failure of cybersecurity awareness campaigns to effectively change behavior may well be linked to the lack of public input in its regulation [ 81 ]. Our findings indicate that growing civilian exposure to cyberattacks leads to more defined attitudes toward specific cybersecurity regulations through the mechanism of heightened threat perception. Governments will increasingly need to engage the public as one of the stakeholders in effecting new cyber regulations.
A second conceptual dilemma about the role of public exposure and opinion has to do with the question of whether cybersecurity is a public good deserving of government investment and regulation at all. Much of the field of cybersecurity is dominated by private enterprise, with government involvement taking place in limited ways. Support for government intervention in the realm of cybersecurity is premised on the astronomical public costs of cybercrime, the threat of cyberterror attacks, and the claim of a market failure in the provision of cybersecurity whose negative externalities in the absence of government involvement would cause substantial national damage [ 83 ]. A prominent counter-school of thought, resting on a belief that the private market is the most efficient system of allocating economic resources, claims that there is no need for government intervention in the cybersecurity market [ 84 ]. These proponents of private sector cybersecurity suggest that the private sector can more effectively achieve cybersecurity outcomes, an assertion that is backed up by the fact that private spending on cybersecurity in 2018 reached USD $96 billion [ 85 ]. This raises the question of how civilian exposure to cyberattacks and the subsequent support for cybersecurity regulation can translate to real outcomes if the market responds to both public and private interests, which take account of public opinion and civilian threat perception in different ways.
Seeing that cyber threats are continuously evolving, there are opportunities to expand and consolidate this research in future studies. In the current article, we focus on the effect of exposure to lethal and nonlethal cyberattacks on support for different types of cybersecurity policies among Israeli participants. Yet despite this singular geographic focus, the results offer lessons that can be applied widely. Like several other Western countries, Israel has been repeatedly exposed to publicly reported cyberattacks on critical infrastructure. And, similarly to American and some European countries, Israel has high levels of Internet penetration and publicly renowned levels of cybersecurity readiness to deal with such attacks. Past studies that examined public perceptions of cyber threats have replicated the findings across multiple countries. Shandler et al . [ 80 ] found that psychological responses to internalized reports of cyberattacks explains support for military retaliation, and that this mechanism applies similarly in Israel, the United States, and England. Though requiring additional research, the evidence suggests that cyber threats operate via an underlying psycho-political mechanism that transcends national borders. In fact, the effects of cyberattacks may prove weaker in Israel than elsewhere as the constant exposure among Israelis to political violence places digital violence in the context of a political struggle that has, in many ways, fixed and acceptable costs [ 34 ]. Therefore, we believe that an Israeli sample offers major advantages in understanding the effects of cyberattacks among other Western nations. Nonetheless, we encourage future studies to corroborate these findings in different settings.
A second area where our findings could benefit from additional research relates to the nature of the media exposure. In this study, we exposed respondents to "initial" media reports about major cyberattacks where there is minimal information pertaining to the identity of the attacker and the type of attack that was conducted. While this in many ways reflects the reality of media reports about cyberattacks, it does not discount that journalists will sometimes make inferences about the details of an attack, and that later reports in the days and weeks following an attack will include far more detailed information. More so, this article bears implications for a wide literature beyond the political violence discipline. The public discussion regarding digital privacy and surveillance has spurred crucial new research on the dynamics of digital insecurity. In communications and media studies, for example, scientists are focusing on information-age warfare via different social media platforms, and early results show that citizens are as active in correcting disinformation online as they are in spreading disinformation [ 86 , 87 ]. The debate in the field of business management is also developing as it focuses on consumer expectations surrounding information technology and big data, as well as on the roles and responsibilities of public and private actors in securing personal data [ 88 , 89 ].
Cyber threats are a critical and growing component of national security. As this threat continues to grow all over the world, both in its public perception and in the true scope of the threat, the need to implement strong cybersecurity regulations will grow as well. Our findings indicate that particular forms of exposure to cyberattacks can contribute to support for various types of cybersecurity legislation and contribute to their public legitimacy. This is especially important since the introduction of these regulations constitutes a sacrifice of civil liberties, a sacrifice that citizens are prone to support only under particular conditions.
Though a DDoS attack, e.g. may not trigger physical casualties, its crippling of emergency services and telecommunications could catastrophically amplify the second- and third-order damage during a physical attack; for more, see Catherine A. Theohary and John W. Rollins, Cyberwarfare and cyberterrorism: In brief (Washington, DC: Congressional Research Service, 2015).
We also see a marginal significant effect between mediation 1 and 5 and 2 and 6. The differences between mediation 1 and mediation 5 show mediation 5 (NLC/control-threat-CPP) has a marginal significant larger mediation effect compared with mediation 1 (NLC/control-threat-CAP) (difference = –0.035; 0.035 P = 0.073). This means that within the NLC group the mediation model predicts stronger predicting CPP than CAP. In other words, participants who were exposed to the nonlethal (NLC) condition were more likely to support CPP than CAP. We saw that the CAP is stronger in the LC group. Another marginal significant effect was found between mediation 2 and mediation 6. The differences between mediation 2 and mediation 6 show mediation 6 (LC/control-threat-CPP) has a marginal significant larger mediation effect compared with mediation 2 (LC/control-threat-CAP) (difference = −0.044; 0.024 P = 0.062). This means that within the LC group the mediation model predicts stronger predicting CPP than CAP. In other words, participants who were exposed to the lethal (LC) condition were more likely to support CPP than CAP. We saw a direct effect of LC on CAP.
Geller E , Matishak M . A federal government left ‘completely blind’ on cyberattacks looks to force reporting . Politico . 2021 . https://www.politico.com/news/2021/05/15/congress-colonial-pipeline-disclosure-488406 (10 August, 2021, date last accessed) .
Google Scholar
Cybersecurity legislation 2020. NCSL . https://www.ncsl.org/research/telecommunications-and-information-technology/cybersecurity-legislation-2020.aspx (17 October 2020, date last accessed).
US state cybersecurity regulation more than doubled in 2017, while federal regulation waned. BusinessWire . https://www.businesswire.com/news/home/20180129005238/en/State-Cybersecurity-Regulation-Doubled-2017-Federal-Regulation (29 January 2018, last accessed) .
Kasper A . EU cybersecurity governance: stakeholders and normative intentions towards integration . In: Harwood M , Moncada S , Pace R (eds). The Future of the European Union: Demisting the Debate . Msida : Institute for European Studies , 2020 , 166 – 85 .
Google Preview
Israel National Cyber Directorate (INCD) . https://www.gov.il/en/departments/about/newabout (1 February 2021, date last accessed) .
Ochoa CS , Gadinger F , Yildiz T . Surveillance under dispute: conceptualizing narrative legitimation politics . Eur J Int Secur . 2021 ; 6 : 210 – 32 ..
Flyverbom M , Deibert R , Matten D . The governance of digital technology, big data, and the internet: new roles and responsibilities for business . Bus Soc . 2019 ; 58 : 3 – 19 ..
Rosenzweig P . The alarming trend of cybersecurity breaches and failures in the U.S. government . The Heritage Foundation. https://www.heritage.org/defense/report/the-alarming-trend-cybersecurity-breaches-and-failures-the-us-government-continues (17 April 2020, last accessed) .
Lee JK , Chang Y , Kwon HY et al. Reconciliation of privacy with preventive cybersecurity: the bright internet approach . Inf Syst Front . 2020 ; 22 : 45 – 57 .
Nye JS . Nuclear lessons for cyber security? . Strateg Stud Q . 2011 ; 5 : 18 – 38 .
Annual number of data breaches and exposed records in the United States from 2005 to 2018 (in millions) . Statista . https://www.statista.com/statistics/273550/data-breaches-recorded-in-the-united-states-by-number-of-breaches-and-records-exposed (26 February 2019, last accessed) .
For big banks, it's an endless fight with hackers The Business Times , 30 July 2019 . https://www.businesstimes.com.sg/banking-finance/for-big-banks-it%E2%80%99s-an-endless-fight-with-hackers
Nye JS Jr . Cyber Power . Cambridge : Harvard Kennedy School, Belfer Center for Science and International Affairs , 2010 .
Stohl M . Cyber terrorism: a clear and present danger, the sum of all fears, breaking point or patriot games? . Crime Law Soc Change . 2006 ; 46 : 223 – 38 .
Lawson ST . Cybersecurity Discourse in the United States: Cyber-Doom Rhetoric and Beyond . New York : Routledge , 2019 .
Valeriano B , Maness RC . Cyber War Versus Cyber Realities: Cyber Conflict in the International System . New York : Oxford University Press , 2015 .
Lawson S . Beyond cyber-doom: Assessing the limits of hypothetical scenarios in the framing of cyber-threats . J Inf Technol Polit . 2013 ; 10 : 86 – 103 .
Israeli cyber chief: Major attack on water systems thwarted. Washington Post. https://www.washingtonpost.com/world/middle_east/israeli-cyber-chief-major-attack-on-water-systems-thwarted/2020/05/28/5a923fa0-a0b5-11ea-be06-af5514ee0385_story.html (28 May 2020, last accessed) .
Panetta warns of dire threat of cyberattack on U.S. New York Times. (October 11, 2012). https://www.nytimes.com/2012/10/12/world/panetta-warns-of-dire-threat-of-cyberattack.html
Choi SJ , Johnson ME , Lehmann CU . Data breach remediation efforts and their implications for hospital quality . Health Serv Res . 2019 ; 54 : 971 – 80 .
Zetter K . A cyber attack has caused confirmed physical damage for the second time ever . Wired . 2015 . http://www.wired.com/2015/01/german-steel-mill-hack-destruction . (April 2020, date last accessed) .
Hobfoll SE , Canetti-Nisim D , Johnson RJ . Exposure to terrorism, stress-related mental health symptoms, and defensive coping among Jews and Arabs in Israel . J Consult Clin Psychol . 2006 ; 74 : 207 – 18 .
Halperin E , Canetti-Nisim D , Hirsch-Hoefler S . The central role of group-based hatred as an emotional antecedent of political intolerance: Evidence from Israel . Polit Psychol . 2009 ; 30 : 93 – 123 .
Bar-Tal D , Halperin E , de Rivera J . Collective emotions in conflict situations: societal implications . J Soc Issues . 2007 ; 63 : 441 – 60 .
Hirsch-Hoefler S , Canetti D , Rapaport C et al. Conflict will harden your heart: exposure to violence, psychological distress, and peace barriers in Israel and Palestine . Br J Polit Sci . 2016 ; 46 : 845 – 59 .
Bonanno GA , Jost JT . Conservative shift among high-exposure survivors of the September 11th terrorist attacks . Basic Appl Soc Psychol . 2006 ; 28 : 311 – 23 .
Canetti-Nisim D , Ariely G , Halperin E . Life, pocketbook, or culture: the role of perceived security threats in promoting exclusionist political attitudes toward minorities in Israel . Polit Res Q . 2008 ; 61 : 90 – 103 .
Zeitzoff T . Anger, exposure to violence, and intragroup conflict: a “lab in the field” experiment in southern Israel . Polit Psychol . 2014 ; 35 : 309 – 35 .
Schmitt N . Tallinn Manual 2.0 on the International Law Applicable to Cyber Operations . Cambridge : Cambridge University Press , 2017 .
Russian hackers appear to shift focus to U.S. power grid. The New York Times, 27 July 2018 . 2018 ;
Aucsmith D . Disintermediation, Counterinsurgency, and Cyber Defense . 2016 , Available at SSRN 2836100 . doi: 10.1093/cybsec/tyw018 , (10 August, 2021 last accessed) .
Gartzke E , Lindsay JR . Thermonuclear cyberwar . J Cybersecur . 2017 ; 3 : 37 – 48 .
Gross ML , Canetti D , Vashdi DR . Cyberterrorism: its effects on psychological well-being, public confidence and political attitudes . J Cybersecur . 2017 ; 3 : 49 – 58 .
Backhaus S , Gross ML , Waismel-Manor I et al. A cyberterrorism effect? Emotional reactions to lethal attacks on critical infrastructure . Cyberpsychol Behav Soc Netw . 2020 ; 23 : 595 – 603 ..
Gross ML , Canetti D , Vashdi DR . The psychological effects of cyber-terrorism . Bull At Sci . 2016 ; 72 : 284 – 91 .
Canetti D , Gross ML , Waismel-Manor I . Immune from cyber-fire? The psychological & physiological effects of cyberwar . In: Allhoff F , Henschke A , Strawser BJ (eds). Binary Bullets: The Ethics of Cyberwarfare . Oxford : Oxford University Press , 2016 , 157 – 76 .
Canetti D , Gross ML , Waismel-Manor I et al. How cyberattacks terrorize: Cortisol and personal insecurity jump in the wake of cyberattacks . Cyberpsychol Behav Soc Netw . 2017 ; 20 : 72 – 7 .
Shandler R , Gross MG , Backhaus S et al. Cyber terrorism and public support for retaliation: a multi-country survey experiment . Br J Polit Sci . 1 – 19 ., 2021 . DOI: 10.1017/S0007123420000812 .
Rosenzweig P . Cybersecurity and public goods, The public/private ‘partnership’ . In: Berkowitz P (ed). Emerging Threats in National Security and Law . Stanford : Hoover Institution, Stanford University , 2011 , 1 – 36 .
Cheung-Blunden V , Cropper K , Panis A et al. Functional divergence of two threat-induced emotions: fear-based versus anxiety-based cybersecurity preferences . Emotion . 2017 ; 19 : 1353 – 65 .
Jardine E , Porter N . Pick your poison: the attribution paradox in cyberwar. 2020 , https://osf.io/preprints/socarxiv/etb72/ .
Rid T , Buchanan B . Attributing cyber attacks . J Strateg Stud . 2015 ; 38 : 4 – 37 .
Clark DD , Landau S . Untangling attribution . Harvard National Secur J . 2011 ; 2 : 323 – 52 .
Alraddadi W , Sarvotham H . A comprehensive analysis of WannaCry: technical analysis, reverse engineering, and motivation . https://docplayer.net/130787668-A-comprehensive-analysis-of-wannacry-technical-analysis-reverse-engineering-and-motivation.html , (17 April 2020, last accessed).
Romanosky S , Boudreaux B . Private-sector attribution of cyber incidents: benefits and risks to the US government . Int J Intell CounterIntelligence . 2020 ; 0 : 1 – 31 .
Baezner M . Iranian cyber-activities in the context of regional rivalries and international tensions . ETH Zurich . 2019 : 1 – 37 .
Macdonald S , Jarvis L , Nouri L . State cyberterrorism: a contradiction in terms? . J Terrorism Res . 2015 ; 6 : 62 – 75 .
Canetti D , Gubler J , Zeitzoff T . Motives don't matter? Motive attribution and counterterrorism policy . Polit Psychol . 2021 ; 42 : 483 – 99 .
Liberman P , Skitka LJ . Revenge in US public support for war against Iraq . Public Opin Q . 2017 ; 81 : 636 – 60 .
Liberman P , Skitka LJ . Vicarious retribution in US public support for war against Iraq . Secur Stud . 2019 ; 28 : 189 – 215 .
Kostyuk N , Wayne C . The microfoundations of state cybersecurity: cyber risk perceptions and the mass public . J Glob Secur Stud . 2021 ; 6 : ogz077 .
Gomez MA . Past behavior and future judgements: seizing and freezing in response to cyber operations . J Cybersecur . 2019 ; 5 : 1 – 19 .
Gomez MA , Villar EB . Fear, uncertainty, and dread: cognitive heuristics and cyber threats . Polit Gov . 2018 ; 6 : 61 – 72 .
Harrell E , Langton L . The Victims of Identity Theft, 2012 . US Department of Justice, Office of Justice Programs, Bureau of Justice Statistics , 2013 . https://www.bjs.gov/content/pub/pdf/vit12.pdf
Sinclair SJ , Antonius D . The Psychology of Terrorism Fears . Oxford : Oxford University Press , 2012 .
Quillian L . Prejudice as a response to perceived group threat: population composition and anti-immigrant and racial prejudice in Europe . Am Sociol Rev . 1995 ; 60 : 586 – 611 .
Ben-Nun Bloom P , Arikan G , Lahav G . The effect of perceived cultural and material threats on ethnic preferences in immigration attitudes . Ethn Racial Stud . 2015 ; 38 : 1760 – 78 .
Shoshani A , Slone M . The drama of media coverage of terrorism: emotional and attitudinal impact on the audience . Stud Confl Terror . 2008 ; 31 : 627 – 40 ..
Huddy L , Smirnov O , Snider KL et al. Anger, anxiety, and selective exposure to terrorist violence . J Confl Resolut . 2021 : 00220027211014937 .
Greenberg J , Pyszczynski T , Solomon S . The causes and consequences of a need for self-esteem: a terror management theory . In: Public Self and Private Self . New York, NY : Springer , 1986 , 212 – 189 .
Hall BJ , Hobfoll SE , Canetti D et al. The defensive nature of benefit finding during ongoing terrorism: an examination of a national sample of Israeli Jews . J Soc Clin Psychol . 2009 ; 28 : 993 – 1021 ..
Canetti D , Hall BJ , Rapaport C et al. Exposure to political violence and political extremism . Eur Psychol . 2013 ; 18 : 263 – 72 .
McCallister E . Guide to Protecting the Confidentiality of Personally Identifiable Information . Darby : Diane Publishing , 2010 .
Graves J , Acquisti A , Anderson R . Experimental measurement of attitudes regarding cybercrime . In: 13th Annual Workshop on the Economics of Information Security . 2014 ; Pennsylvania State University.
Huddy L , Feldman S , Capelos T et al. The consequences of terrorism: disentangling the effects of personal and national threat . Polit Psychol . 2002 ; 23 : 485 – 509 .
Hefetz A , Liberman G . The factor analysis procedure for exploration: a short guide with examples . Cult Educ . 2017 ; 29 : 526 – 62 .
Muthén LK , Muthén BO . MPlus: Statistical Analysis with Latent Variables: User's Guide . Muthén & Muthén , Los Angeles, CA , 2012 .
Galea S , Ahern J , Resnick H et al. Psychological sequelae of the September 11 terrorist attacks in New York City . N Engl J Med . 2002 ; 346 : 982 – 7 .
Canetti-Nisim D , Halperin E , Sharvit K et al. A new stress-based model of political extremism: personal exposure to terrorism, psychological distress, and exclusionist political attitudes . J Confl Res . 2009 ; 53 : 363 – 89 .
Canetti D , Snider KLG , Pedersen A et al. Threatened or threatening? How ideology shapes asylum seekers’ immigration policy attitudes in Israel and Australia . J Refug Stud . 2016 ; 29 : 583 – 606 .
Morgan S . Cybersecurity Ventures predicts cybercrime will cost the world in excess of $6 trillion annually by 2021. Cybercrime Magazine . 2017 ; https://cybersecurityventures.com/hackerpocalypse-cybercrime-report-2016/ (11 May 2020, date last accessed) .
Yakter A , Harsgor L . Long-term change in conflict attitudes: a dynamic approach . 2021 . http://liran.harsgor.com/wp-content/uploads/2021/07/YakterHarsgor_2021_Long-term-conflict.pdf
Brouard S , Vasilopoulos P , Foucault M . How terrorism affects political attitudes: France in the aftermath of the 2015–2016 attacks . West Eur Polit . 2018 ; 41 : 1073 – 99 .
Castanho Silva B . The (non)impact of the 2015 Paris terrorist attacks on political attitudes . Pers Soc Psychol Bull . 2018 ; 44 : 838 – 50 .
Brandon SE , Silke AP . Near- and long-term psychological effects of exposure to terrorist attacks . In: Bongar B , Brown LM , Beutler LE , al. et (eds). Psychology of Terrorism . Oxford: Oxford University Press 2007 , 175 – 93 .
Pfefferbaum B , Nixon SJ , Krug RS et al. Clinical needs assessment of middle and high school students following the 1995 Oklahoma City bombing . Am J Psychiatry . 1999 ; 156 : 1069 – 74 ..
Galea S , Vlahov D , Resnick H et al. Trends of probable post-traumatic stress disorder in New York City after the September 11 terrorist attacks . Am J Epidemiol . 2003 ; 158 : 514 – 24 ..
Landau MJ , Solomon S , Greenberg J et al. Deliver us from evil: the effects of mortality salience and reminders of 9/11 on support for President George W. Bush . Pers Soc Psychol Bull . 2004 ; 30 : 1136 – 50 ..
Nussio E . Attitudinal and emotional consequences of Islamist terrorism. Evidence from the Berlin attack . Polit Psychol . 2020 ; 41 : 1151 – 71 ..
Bada M , Sasse AM , Nurse JRC . Cyber security awareness campaigns: why do they fail to change behaviour? In: International Conference on Cyber Security for Sustainable Society , Global Cyber Security Capacity Centre. 2015 , 1 – 11 .
Shane PM . Cybersecurity policy as if ‘ordinary citizens’ mattered: the case for public participation in cyber policy making . SSRN Electron J . 2012 ; 8 : 433 – 62 .
Shandler R . White paper: Israel as a cyber power . 2019 , DOI: 10.13140/RG.2.2.15936.07681 .
Gartner forecasts worldwide security spending will reach $96 billion in 2018, up 8 percent from 2017. Gartner. https://www.gartner.com/newsroom/id/3836563 (1 August 2019, date last accessed) .
Shandler R , Gross ML , Canetti D . A fragile public preference for using cyber strikes: evidence from survey experiments in the United States, United Kingdom and Israel . Contemp Secur Policy . 2021 ; 42 : 135 – 62 .
Prier J . Commanding the trend: social media as information warfare . Strateg Stud Q . 2017 ; 11 : 50 – 85 ..
Golovchenko Y , Hartmann M , Adler-Nissen R . State, media and civil society in the information warfare over Ukraine: citizen curators of digital disinformation . Int Aff . 2018 ; 94 : 975 – 94 ..
Belk RW . Extended self in a digital world . J Consum Res . 2013 ; 40 : 477 – 500 .
West SM . Data capitalism: redefining the logics of surveillance and privacy . Bus Soc . 2019 ; 58 : 20 – 41 .
Cahane A . The new Israeli cyber draft bill: a preliminary overview . CSRCL . 2018 . https://csrcl.huji.ac.il/news/new-israeli-cyber-law-draft-bill . (10 August, 2021, date last accessed) .
Supplementary data
| Month: | Total Views: |
|---|---|
| October 2021 | 1,060 |
| November 2021 | 1,171 |
| December 2021 | 742 |
| January 2022 | 658 |
| February 2022 | 455 |
| March 2022 | 444 |
| April 2022 | 527 |
| May 2022 | 576 |
| June 2022 | 512 |
| July 2022 | 410 |
| August 2022 | 416 |
| September 2022 | 556 |
| October 2022 | 669 |
| November 2022 | 639 |
| December 2022 | 443 |
| January 2023 | 344 |
| February 2023 | 372 |
| March 2023 | 482 |
| April 2023 | 464 |
| May 2023 | 525 |
| June 2023 | 375 |
| July 2023 | 355 |
| August 2023 | 318 |
| September 2023 | 658 |
| October 2023 | 1,190 |
| November 2023 | 1,584 |
| December 2023 | 1,169 |
| January 2024 | 1,232 |
| February 2024 | 1,266 |
| March 2024 | 1,357 |
| April 2024 | 1,519 |
| May 2024 | 1,447 |
| June 2024 | 1,021 |
| July 2024 | 471 |
Email alerts
Citing articles via, affiliations.
- Online ISSN 2057-2093
- Print ISSN 2057-2085
- Copyright © 2024 Oxford University Press
- About Oxford Academic
- Publish journals with us
- University press partners
- What we publish
- New features
- Open access
- Institutional account management
- Rights and permissions
- Get help with access
- Accessibility
- Advertising
- Media enquiries
- Oxford University Press
- Oxford Languages
- University of Oxford
Oxford University Press is a department of the University of Oxford. It furthers the University's objective of excellence in research, scholarship, and education by publishing worldwide
- Copyright © 2024 Oxford University Press
- Cookie settings
- Cookie policy
- Privacy policy
- Legal notice
This Feature Is Available To Subscribers Only
Sign In or Create an Account
This PDF is available to Subscribers Only
For full access to this pdf, sign in to an existing account, or purchase an annual subscription.

Research Topics & Ideas: Cybersecurity
50 Topic Ideas To Kickstart Your Research

If you’re just starting out exploring cybersecurity-related topics for your dissertation, thesis or research project, you’ve come to the right place. In this post, we’ll help kickstart your research by providing a hearty list of cybersecurity-related research topics and ideas , including examples from recent studies.
PS – This is just the start…
We know it’s exciting to run through a list of research topics, but please keep in mind that this list is just a starting point . These topic ideas provided here are intentionally broad and generic , so keep in mind that you will need to develop them further. Nevertheless, they should inspire some ideas for your project.
To develop a suitable research topic, you’ll need to identify a clear and convincing research gap , and a viable plan to fill that gap. If this sounds foreign to you, check out our free research topic webinar that explores how to find and refine a high-quality research topic, from scratch. Alternatively, consider our 1-on-1 coaching service .
Cybersecurity-Related Research Topics
- Developing machine learning algorithms for early detection of cybersecurity threats.
- The use of artificial intelligence in optimizing network traffic for telecommunication companies.
- Investigating the impact of quantum computing on existing encryption methods.
- The application of blockchain technology in securing Internet of Things (IoT) devices.
- Developing efficient data mining techniques for large-scale social media analytics.
- The role of virtual reality in enhancing online education platforms.
- Investigating the effectiveness of various algorithms in reducing energy consumption in data centers.
- The impact of edge computing on the performance of mobile applications in remote areas.
- The application of computer vision techniques in automated medical diagnostics.
- Developing natural language processing tools for sentiment analysis in customer service.
- The use of augmented reality for training in high-risk industries like oil and gas.
- Investigating the challenges of integrating AI into legacy enterprise systems.
- The role of IT in managing supply chain disruptions during global crises.
- Developing adaptive cybersecurity strategies for small and medium-sized enterprises.
- The impact of 5G technology on the development of smart city solutions.
- The application of machine learning in personalized e-commerce recommendations.
- Investigating the use of cloud computing in improving government service delivery.
- The role of IT in enhancing sustainability in the manufacturing sector.
- Developing advanced algorithms for autonomous vehicle navigation.
- The application of biometrics in enhancing banking security systems.
- Investigating the ethical implications of facial recognition technology.
- The role of data analytics in optimizing healthcare delivery systems.
- Developing IoT solutions for efficient energy management in smart homes.
- The impact of mobile computing on the evolution of e-health services.
- The application of IT in disaster response and management.
Cybersecurity Research Ideas (Continued)
- Assessing the security implications of quantum computing on modern encryption methods.
- The role of artificial intelligence in detecting and preventing phishing attacks.
- Blockchain technology in secure voting systems: opportunities and challenges.
- Cybersecurity strategies for protecting smart grids from targeted attacks.
- Developing a cyber incident response framework for small to medium-sized enterprises.
- The effectiveness of behavioural biometrics in preventing identity theft.
- Securing Internet of Things (IoT) devices in healthcare: risks and solutions.
- Analysis of cyber warfare tactics and their implications on national security.
- Exploring the ethical boundaries of offensive cybersecurity measures.
- Machine learning algorithms for predicting and mitigating DDoS attacks.
- Study of cryptocurrency-related cybercrimes: patterns and prevention strategies.
- Evaluating the impact of GDPR on data breach response strategies in the EU.
- Developing enhanced security protocols for mobile banking applications.
- An examination of cyber espionage tactics and countermeasures.
- The role of human error in cybersecurity breaches: a behavioural analysis.
- Investigating the use of deep fakes in cyber fraud: detection and prevention.
- Cloud computing security: managing risks in multi-tenant environments.
- Next-generation firewalls: evaluating performance and security features.
- The impact of 5G technology on cybersecurity strategies and policies.
- Secure coding practices: reducing vulnerabilities in software development.
- Assessing the role of cyber insurance in mitigating financial losses from cyber attacks.
- Implementing zero trust architecture in corporate networks: challenges and benefits.
- Ransomware attacks on critical infrastructure: case studies and defence strategies.
- Using big data analytics for proactive cyber threat intelligence.
- Evaluating the effectiveness of cybersecurity awareness training in organisations.
Recent Cybersecurity-Related Studies
While the ideas we’ve presented above are a decent starting point for finding a research topic, they are fairly generic and non-specific. So, it helps to look at actual studies in the cybersecurity space to see how this all comes together in practice.
Below, we’ve included a selection of recent studies to help refine your thinking. These are actual studies, so they can provide some useful insight as to what a research topic looks like in practice.
- Cyber Security Vulnerability Detection Using Natural Language Processing (Singh et al., 2022)
- Security for Cloud-Native Systems with an AI-Ops Engine (Ck et al., 2022)
- Overview of Cyber Security (Yadav, 2022)
- Exploring the Top Five Evolving Threats in Cybersecurity: An In-Depth Overview (Mijwil et al., 2023)
- Cyber Security: Strategy to Security Challenges A Review (Nistane & Sharma, 2022)
- A Review Paper on Cyber Security (K & Venkatesh, 2022)
- The Significance of Machine Learning and Deep Learning Techniques in Cybersecurity: A Comprehensive Review (Mijwil, 2023)
- Towards Artificial Intelligence-Based Cybersecurity: The Practices and ChatGPT Generated Ways to Combat Cybercrime (Mijwil et al., 2023)
- ESTABLISHING CYBERSECURITY AWARENESS OF TECHNICAL SECURITY MEASURES THROUGH A SERIOUS GAME (Harding et al., 2022)
- Efficiency Evaluation of Cyber Security Based on EBM-DEA Model (Nguyen et al., 2022)
- An Overview of the Present and Future of User Authentication (Al Kabir & Elmedany, 2022)
- Cybersecurity Enterprises Policies: A Comparative Study (Mishra et al., 2022)
- The Rise of Ransomware: A Review of Attacks, Detection Techniques, and Future Challenges (Kamil et al., 2022)
- On the scale of Cyberspace and Cybersecurity (Pathan, 2022)
- Analysis of techniques and attacking pattern in cyber security approach (Sharma et al., 2022)
- Impact of Artificial Intelligence on Information Security in Business (Alawadhi et al., 2022)
- Deployment of Artificial Intelligence with Bootstrapped Meta-Learning in Cyber Security (Sasikala & Sharma, 2022)
- Optimization of Secure Coding Practices in SDLC as Part of Cybersecurity Framework (Jakimoski et al., 2022)
- CySSS ’22: 1st International Workshop on Cybersecurity and Social Sciences (Chan-Tin & Kennison, 2022)
As you can see, these research topics are a lot more focused than the generic topic ideas we presented earlier. So, for you to develop a high-quality research topic, you’ll need to get specific and laser-focused on a specific context with specific variables of interest. In the video below, we explore some other important things you’ll need to consider when crafting your research topic.
Get 1-On-1 Help
If you’re still unsure about how to find a quality research topic, check out our Research Topic Kickstarter service, which is the perfect starting point for developing a unique, well-justified research topic.

Submit a Comment Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.
- Print Friendly
List of 78 Top Cyber Security Topics for Research
Table of contents
- 1 How To Choose The Best Cyber Security Research Topics
- 2 📚10 Cyber Security Topics For Research Paper
- 3 📱Mobile Cyber Security Research Paper Topics
- 4 🕵Top 10 Cyber Security Topics
- 5 👨💻Cyber Security Research Topics 2023
- 6 🔎Best Cyber Security Research Topics
- 7 👨🔬Cyber Security Future Research Topics
- 8 📑Cyber Security Topics For Research Paper
- 9 👩💻Cyber Security Topics on Computer and Software
There are many reasons to choose cyber security research topics for writing purposes. First, cyber security is a growing field, with many new and exciting developments happening all the time. This makes it an ideal topic to write about, as there is always something new to learn and discuss. Second, cyber security research can be used to improve the security of your own computer systems. By understanding the latest threats and vulnerabilities, you can make your systems more secure and less likely to be compromised. Third, writing about cyber security can help raise awareness about the importance of cyber security. By educating others about the dangers of cyber attacks and the importance of protecting their computers, you can help make the internet a safer place for everyone.
How To Choose The Best Cyber Security Research Topics
When it comes to choosing research paper topics on cyber security, there are a few things to consider. First, it is important to make sure that the topic is relevant and timely. Cyber security is an ever-changing field, so it is important to choose a topic that will be relevant for years to come. Second, it is important to choose a topic that is interesting and engaging. Cybersecurity can be a dry topic, so it is important to choose a topic that will keep readers engaged. Finally, it is important to choose a topic that is researchable. There are a lot of cyber security topics out there, but not all of them are easy to research. Make sure to choose a topic that has plenty of information available.
- Identify your audience.
- Define your research goals.
- Choose a topic that is both interesting and relevant to your audience.
- Do some preliminary research to make sure there is enough information available on your chosen topic.
- Make sure your topic is narrow enough to be covered in a single research paper.
📚10 Cyber Security Topics For Research Paper
- The Importance of Cyber Security
- The Evolution of Cyber Security
- The Future of Cyber Security
- The Impact of Cyber Security on Business
- The Role of Cyber Security in National Security
- The Challenges of Cyber Security
- The Costs of Cyber Security
- The Benefits of Cyber Security
- The Risks of Cyber Security
- The Implications of Cyber Security
📱Mobile Cyber Security Research Paper Topics
- Mobile device security: How to protect your mobile device from cyber attacks.
- The rise of mobile malware: How to protect your device from malicious software.
- Mobile phishing attacks: How to protect your device from being scammed.
- The dangers of public Wi-Fi: How to protect your device from being hacked.
- How to keep your data safe on your mobile device: Tips for keeping your personal information secure.
🕵Top 10 Cyber Security Topics
- Cybersecurity threats and attacks
- Cybersecurity risks and vulnerabilities
- Cybersecurity best practices
- Cybersecurity awareness and training
- Cybersecurity tools and technologies
- Cybersecurity policy and compliance
- Cybersecurity incident response
- Cybersecurity governance
- Cybersecurity risk management
- Cybersecurity strategy
👨💻Cyber Security Research Topics 2023
- The future of cyber security: what trends will shape the field in the coming years?
- The impact of AI and machine learning on cyber security
- The role of quantum computing in cyber security
- The challenges of securing the IoT
- The evolving threat landscape: what new threats are emerging and how can we defend against them?
- The role of data in cyber security: how can we better protect our data?
- The importance of user education in cyber security
- The challenges of securing mobile devices
- The future of cyber warfare: what trends are emerging?
- The role of cryptography in cyber security
🔎Best Cyber Security Research Topics
- The Impact of Cybersecurity on Businesses and Consumers
- The Evolution of Cybersecurity Threats and Attacks
- The Role of Cybersecurity in National Security
- The Economics of Cybersecurity
- The Psychology of Cybersecurity
- The Sociology of Cybersecurity
- The Ethics of Cybersecurity
- The History of Cybersecurity
- Cybersecurity threats and attacks.
- Cybersecurity policies and procedures.
- Cybersecurity awareness and training.
- Cybersecurity technologies and solutions.
- Cybersecurity risk management.
- Cybersecurity incident response.
- Cybersecurity governance.
- Cybersecurity compliance.
- Cybersecurity standards.
- Cybersecurity best practices.
👨🔬Cyber Security Future Research Topics
- Developing more effective methods for detecting and responding to cyber attacks
- Investigating the role of social media in cyber security
- Examining the impact of cloud computing on cyber security
- Investigating the security implications of the Internet of Things
- Studying the effectiveness of current cyber security measures
- Identifying new cyber security threats and vulnerabilities
- Developing more effective cyber security policies
- Examining the ethical implications of cyber security
📑Cyber Security Topics For Research Paper
- Cyber security threats and vulnerabilities.
- Cyber security incident response and management.
- Cyber security risk management.
- Cyber security awareness and training.
- Cyber security controls and countermeasures.
- Cyber security governance.
- Cyber security standards.
- Cyber security insurance.
- Cyber security and the law.
- The future of cyber security.
👩💻Cyber Security Topics on Computer and Software
- Cyber security risks associated with computer software
- The importance of keeping computer software up to date
- How to protect your computer from malware and other threats
- The best practices for securing your computer and software
- The different types of cyber security threats and how to avoid them
- The importance of cyber security awareness and education
- The role of cyber security in protecting critical infrastructure
Readers also enjoyed

WHY WAIT? PLACE AN ORDER RIGHT NOW!
Just fill out the form, press the button, and have no worries!
We use cookies to give you the best experience possible. By continuing we’ll assume you board with our cookie policy.
IEEE Account
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
- How It Works
- PhD thesis writing
- Master thesis writing
- Bachelor thesis writing
- Dissertation writing service
- Dissertation abstract writing
- Thesis proposal writing
- Thesis editing service
- Thesis proofreading service
- Thesis formatting service
- Coursework writing service
- Research paper writing service
- Architecture thesis writing
- Computer science thesis writing
- Engineering thesis writing
- History thesis writing
- MBA thesis writing
- Nursing dissertation writing
- Psychology dissertation writing
- Sociology thesis writing
- Statistics dissertation writing
- Buy dissertation online
- Write my dissertation
- Cheap thesis
- Cheap dissertation
- Custom dissertation
- Dissertation help
- Pay for thesis
- Pay for dissertation
- Senior thesis
- Write my thesis
128 High Quality Cybersecurity Research Topics Ideas List

The internet is a global village full of different people. Some people have malicious motives. Once they stumble upon your sensitive data, they will use it to harass you. This also occurs in social media accounts. You may post something and then get some bad or hurtful comments.
That’s a form of cyberbullying that is not acceptable. Therefore, you need to be careful when dealing with people on the internet. Also, try to reduce the data that you expose on your different user profiles. A person may even steal your online identity in a blink of an eye.
Case Situations To Write Cybersecurity Research Paper
Thereby cybersecurity comes in with the motive of defending computers, servers, mobiles, electronic systems, networks, and much more from those malicious attacks. You may need to write a cybersecurity research paper for:
Your final paper, project, thesis, or dissertation. When you are proposing a new strategy to use in your company to prevent cyber-attacks. When you want to bring into light some vulnerabilities being ignored. When you want to do more research and get a better understanding of harassment on the internet.
How To Write Cybersecurity Research Paper
This is the procedure you can use when writing a research paper.
Consult your professor – You will first need to get insights from your professor or teacher on the best way to go about it. You can provide a list of topics you may want to write on for his approval. Brainstorm – Discuss with some like-minded people the best cybersecurity topics to try. You need to be careful to ensure that you choose a topic that you can easily do. Research – Once you settle on a good topic, you can start your research on books, scholarly articles, documentaries, and films to get legit information on your cybersecurity research topic. Jot them down as a draft. Start your paper – Once you are settled with the research, you can use your draft to write a viable research paper. Ensure you follow the right procedure. Proofread the work – Once you are satisfied with your work, consider proofreading it before submitting it.
If you don’t feel like writing research paper yourself, you can get cheap dissertation help from our experts.
Cybersecurity Research Topics
When in high school or college, you need to strive to get good grades. You can use any of these cybersecurity research topics for your paper. Just ensure to do enough research on the concepts.
- The significance of a firewall in the protection of the network.
- Discuss the process of authentication.
- The loss and restoration of data.
- The best data encryption algorithms.
- The best methods to protect your network.
- Evaluate digital piracy and security.
- The significance of social engineering.
- The significance of software updates in devices.
- The major causes of cybersecurity.
- The safety of biometrics.
- The worst cases of IoT hacking.
Cybersecurity Research Paper Topics
Cybersecurity is wide and inexhaustible. Each day, cybercrime are occurring, leading to research on better ways to protect ourselves online. You can use any of these topics for your research paper or project.
- The advantages and disadvantages of unified user profiles.
- The relation between bots and cybersecurity.
- The major cybersecurity vulnerabilities.
- Evaluate digital piracy and its effects on creativity.
- How has automotive hacking grown over the years?
- Evaluate ethical hacking.
- Evolution of phishing over time.
- The best antivirus software currently being used.
- The trends in cybersecurity technology.
- How biometrics is helping in cybersecurity?
- The occurrence of cybersecurity in spoofing.
Cybersecurity Research Topics For Research Papers
Are you in the IT profession? Have you done your project yet? Then you can consider using any of these cybersecurity research topics. They are all ideal and based on current matters.
- The rise of identity theft on the internet.
- Why are more people getting into computer forensics?
- The major threats found using digital forensic techniques.
- The best VPNs in the world that will hide your IP on the internet.
- The disadvantages of exposure of your IP address to the public.
- The major A.I. security systems.
- The centralization of data storage.
- How to identify malicious activity on your devices.
- The safety of a network.
- The applications of network segmentation.
- The major challenges in IT risk management.
PhD Research Topics In Cybersecurity
Are you currently doing your Ph.D.? You can use any of these cybersecurity topics for your paper. They are all based on current matters. There are available resources that you can use to get data.
- The best approach for connected autonomous vehicles.
- The best methods for cognitive cybersecurity.
- The most innovative methods being used to determine the viability of deep learning based on the cybersecurity log analytics system.
- The significance of not sharing sensitive data on social media networks.
- Evaluate cookies on privacy.
- The different types of hackers.
- The disadvantages of Wi-Fi hacking apps on mobile phones.
- The major cyber-attack concepts.
- The best way to develop credible internet security software.
- How to scan malware on your pc.
- Evaluate twitter’s access control policy.

Research Topics In Cybersecurity
You can use any of these research topics in cybersecurity for your papers. You can derive data from some other scholarly articles, documentaries, films, and books. Information about cybersecurity gets updated daily.
- The attack of ransomware.
- The effects of RSA on any network’s security.
- The significance of cloud security.
- How do data leaks occur on mobile apps?
- The effects of a black hole on a network system.
- The significance of applications logging.
- How to detect malicious activities on Google Play apps.
- The best way to check security protocols.
- How does network security deal with cybercrime?
- The network security monitoring process.
- The dangers and flaws of the internet.
Best Research Topics In Cybersecurity
How confident are you about your knowledge of cybersecurity? Then you can consider using any of these topics to test your knowledge capacity. Give it your best to get top grades.
- Initiatives that can be taken to check the growth of cyber hackers.
- The difference between white and black hat hackers.
- How does network intrusion occur and its prevention?
- The authentication processes.
- The most common vulnerabilities.
- The different types of cybercrime.
- The major pandemics caused by cyber viruses.
- The significance of software updates and patches.
- The common laws against cybercrime in the world.
- The best way to suppress the ransomware attack rate.
- The significance of a keylogger.
Hot Topics Cybersecurity Research
These are some of the hottest topics in cybersecurity. You just need to find an ideal topic, do research, jot down the points, and start your research paper.
- The best way to ensure you are safe when downloading files on the internet.
- The best device synchronization and protection methods.
- How can you detect bots on the internet?
- The relation between internet cookies with cybersecurity.
- How are IOS-based apps less prone to ransomware attacks?
- Is it possible for computer hardware to face a cyber-attack?
- The algorithms of data encryption.
- The significance of investing in a strong anti-malware.
- How do encrypting viruses work?
- How do the reverse engineering and vulnerabilities analysis work?
Great Topics For Cybersecurity Research Papers
There are a lot of vulnerabilities on the internet. These great topics for cybersecurity can make you more knowledgeable about the current trends.
- Risk management in computing.
- The most common causes of a data breach in the 21 st
- The best way to protect your device and synchronize the data.
- The significance of computer forensics in the current digital era.
- The major implications of ethical hacking.
- The motivations behind cybercrimes like identity theft.
- The major components of IT and data governance.
- The most secure user authentication methods.
- The threats of digital piracy.
- The significance of device synchronization.
Cybersecurity And Law Research Topics
Did you know that certain laws govern cybersecurity? Then you can use these cybersecurity and law research topics to get a deeper understanding.
- Data and cybersecurity in IoT.
- The correlation between big data analysis with IoT.
- Evaluate Software Defined Network.
- The best tools for excellent email security.
- How to prevent cybercrimes.
- How do phishing scams occur?
- The significance of using strong passwords.
- The worst data breaches of all time.
- How do malicious people use other people’s identities to their benefit?
- How to remove malware from a computer.
Research Topics On Cybersecurity
There are different internet vulnerabilities in the world. Thereby, you can use these research topics on cybersecurity to understand how your security can be compromised on the internet.
- Evaluate botnets in the current world.
- Evaluate a brute force attack.
- The risks of connecting your device to a public wireless network.
- How to secure removable media.
- The occurrence of credit card fraud.
- The most recent cloud security threats.
- The significance of implementing multifactor authentication.
- How is online slandering a cybercrime?
- Email sender spoofing process.
- Stress is caused by periodic cyberbullying.
Cybersecurity Research Topic
Have you ever faced any cyber-attack? How was the experience? These are great topics that can help you become more knowledgeable.
- How to protect yourself from cyberbullying.
- The best security measures to input on Windows, macOS, and Linux.
- How dangerous is cyberstalking?
- Can cyber harassment be termed a crime?
- The major dangers of public Wi-Fi networks.
- Is it possible to identify a phishing attack?
- The best mobile protection methods on your smartphone.
- Malware and how it occurs.
- The best practices to secure your Home Wi-Fi.
- The advantages and disadvantages of antivirus software.
Topic On Cybersecurity
As a student, you need to up your game, to ensure you provide custom work that your teacher or professor will be happy about. Just try any of these topics on cybersecurity.
- The endpoint attacks on devices.
- The dangers posed by tracking cookies.
- The role of backups on your device’s data.
- Evaluate security patches.
- Is it important to read the software terms and conditions?
- Are there any malicious apps on the Google Play Store and Apple Store?
- Evaluate SQL injection attacks.
- The best way to keep your personal information safe.
- The vulnerabilities found in multifactor authentication.
- How to protect your computer.
- How to authenticate on your devices.
Paper Writing Assistance In Cybersecurity Research Paper
Are you busy and wondering how you will do your research paper, project, or thesis? Look no further, you can pay for dissertation and be sure to get perfect result. You just need to order by choosing a topic of your preference and buy it at a cheap price.
You don’t have to worry about not meeting the deadline. With us, you will be sorted. All the best in your research paper.
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Comment * Error message
Name * Error message
Email * Error message
Save my name, email, and website in this browser for the next time I comment.
As Putin continues killing civilians, bombing kindergartens, and threatening WWIII, Ukraine fights for the world's peaceful future.
Ukraine Live Updates
cyber attacks Recently Published Documents
Total documents.
- Latest Documents
- Most Cited Documents
- Contributed Authors
- Related Sources
- Related Keywords
Analysis of Trending Topics and Text-based Channels of Information Delivery in Cybersecurity
Computer users are generally faced with difficulties in making correct security decisions. While an increasingly fewer number of people are trying or willing to take formal security training, online sources including news, security blogs, and websites are continuously making security knowledge more accessible. Analysis of cybersecurity texts from this grey literature can provide insights into the trending topics and identify current security issues as well as how cyber attacks evolve over time. These in turn can support researchers and practitioners in predicting and preparing for these attacks. Comparing different sources may facilitate the learning process for normal users by creating the patterns of the security knowledge gained from different sources. Prior studies neither systematically analysed the wide range of digital sources nor provided any standardisation in analysing the trending topics from recent security texts. Moreover, existing topic modelling methods are not capable of identifying the cybersecurity concepts completely and the generated topics considerably overlap. To address this issue, we propose a semi-automated classification method to generate comprehensive security categories to analyse trending topics. We further compare the identified 16 security categories across different sources based on their popularity and impact. We have revealed several surprising findings as follows: (1) The impact reflected from cybersecurity texts strongly correlates with the monetary loss caused by cybercrimes, (2) security blogs have produced the context of cybersecurity most intensively, and (3) websites deliver security information without caring about timeliness much.
Adaptive distributed Kalman-like filter for power system with cyber attacks
Designing and evaluating an automatic forensic model for fast response of cross-border e-commerce security incidents.
The rapid development of cross-border e-commerce over the past decade has accelerated the integration of the global economy. At the same time, cross-border e-commerce has increased the prevalence of cybercrime, and the future success of e-commerce depends on enhanced online privacy and security. However, investigating security incidents is time- and cost-intensive as identifying telltale anomalies and the source of attacks requires the use of multiple forensic tools and technologies and security domain knowledge. Prompt responses to cyber-attacks are important to reduce damage and loss and to improve the security of cross-border e-commerce. This article proposes a digital forensic model for first incident responders to identify suspicious system behaviors. A prototype system is developed and evaluated by incident response handlers. The model and system are proven to help reduce time and effort in investigating cyberattacks. The proposed model is expected to enhance security incident handling efficiency for cross-border e-commerce.
Designing and Evaluating an Automatic Forensic Model for Fast Response of Cross-Border E-Commerce Security Incidents
Spi: automated identification of security patches via commits.
Security patches in open source software, providing security fixes to identified vulnerabilities, are crucial in protecting against cyber attacks. Security advisories and announcements are often publicly released to inform the users about potential security vulnerability. Despite the National Vulnerability Database (NVD) publishes identified vulnerabilities, a vast majority of vulnerabilities and their corresponding security patches remain beyond public exposure, e.g., in the open source libraries that are heavily relied on by developers. As many of these patches exist in open sourced projects, the problem of curating and gathering security patches can be difficult due to their hidden nature. An extensive and complete security patches dataset could help end-users such as security companies, e.g., building a security knowledge base, or researcher, e.g., aiding in vulnerability research. To efficiently curate security patches including undisclosed patches at large scale and low cost, we propose a deep neural-network-based approach built upon commits of open source repositories. First, we design and build security patch datasets that include 38,291 security-related commits and 1,045 Common Vulnerabilities and Exposures (CVE) patches from four large-scale C programming language libraries. We manually verify each commit, among the 38,291 security-related commits, to determine if they are security related. We devise and implement a deep learning-based security patch identification system that consists of two composite neural networks: one commit-message neural network that utilizes pretrained word representations learned from our commits dataset and one code-revision neural network that takes code before revision and after revision and learns the distinction on the statement level. Our system leverages the power of the two networks for Security Patch Identification. Evaluation results show that our system significantly outperforms SVM and K-fold stacking algorithms. The result on the combined dataset achieves as high as 87.93% F1-score and precision of 86.24%. We deployed our pipeline and learned model in an industrial production environment to evaluate the generalization ability of our approach. The industrial dataset consists of 298,917 commits from 410 new libraries that range from a wide functionalities. Our experiment results and observation on the industrial dataset proved that our approach can identify security patches effectively among open sourced projects.
Cyber Security Frameworks
Abstract: In this paper we attempt to explain and establish certain frameworks that can be assessed for implementing security systems against cyber-threats and cyber-criminals. We give a brief overview of electronic signature generation procedures which include its validation and efficiency for promoting cyber security for confidential documents and information stored in the cloud. We strictly avoid the mathematical modelling of the electronic signature generation process as it is beyond the scope of this paper, instead we take a theoretical approach to explain the procedures. We also model the threats posed by a malicious hacker seeking to induce disturbances in the functioning of a power transmission grid via the means of cyber-physical networks and systems. We use the strategy of a load redistribution attack, while clearly acknowledging that the hacker would form its decision policy on inadequate information. Our research indicate that inaccurate admittance values often cause moderately invasive cyber-attacks that still compromise the grid security, while inadequate capacity values result in comparatively less efficient attacks. In the end we propose a security framework for the security systems utilised by companies and corporations at global scale to conduct cyber-security related operations. Keywords: Electronic signature, Key pair, sequence modelling, hacker, power transmission grid, Threat response, framework.
Information Security in Medical Robotics: A Survey on the Level of Training, Awareness and Use of the Physiotherapist
Cybersecurity is becoming an increasingly important aspect to investigate for the adoption and use of care robots, in term of both patients’ safety, and the availability, integrity and privacy of their data. This study focuses on opinions about cybersecurity relevance and related skills for physiotherapists involved in rehabilitation and assistance thanks to the aid of robotics. The goal was to investigate the awareness among insiders about some facets of cybersecurity concerning human–robot interactions. We designed an electronic questionnaire and submitted it to a relevant sample of physiotherapists. The questionnaire allowed us to collect data related to: (i) use of robots and its relationship with cybersecurity in the context of physiotherapy; (ii) training in cybersecurity and robotics for the insiders; (iii) insiders’ self-assessment on cybersecurity and robotics in some usage scenarios, and (iv) their experiences of cyber-attacks in this area and proposals for improvement. Besides contributing some specific statistics, the study highlights the importance of both acculturation processes in this field and monitoring initiatives based on surveys. The study exposes direct suggestions for continuation of these types of investigations in the context of scientific societies operating in the rehabilitation and assistance robotics. The study also shows the need to stimulate similar initiatives in other sectors of medical robotics (robotic surgery, care and socially assistive robots, rehabilitation systems, training for health and care workers) involving insiders.
Challenges, Trends and Solutions for Communication Networks and Cyber-Security in Smart Grid.
Abstract: Power grid is one of the most important manifestations of the modern civilization and the engine of it where it is described as a digestive system of the civil life. It is a structure has three main functions: generation, transmission lines, distribution. This concept was appropriate for a century. However, the beginning of the twenty-first century brought dramatic changes on different domains: media, human growth, economic, environmental, political, and technical etc. Smart grid is a sophisticated structure including cyber and physical bodies hence it reinforces the sustainability, the energy management, the capability of integration with microgrids, and exploiting the renewable energy resources. The quantum leap of smart grid is related to the advanced communication networks that deal with the cyber part. Moreover, the communication networks of smart grid offer attractive capabilities such as monitoring, control, and protection at the level of real time. The wireless communication techniques in integration frame are promised solution to compensate the requirements of smart grid designing such as wireless local area networks, worldwide interoperability for microwave access, long term evolution, and narrowband- internet of things. These technologies could provide high capacity, flexibility, low-cost maintenance for smart grid. However, the multi-interfaces in smart grid may exploit by persons or agencies to implement different types of cyber-attacks may lead to dangerous damage. This research paper reviews the up-to-date researches in the field of smart grid to handle the new trends and topics in one frame in order to offer integration vision in this vital section. It concentrates on the section of communication networks the mainstay of smart grid. This paper discusses the challenging and requirements of adopting the wireless communication technologies and delves deeply into literature review to devise and suggest solutions to compensate the impairments efficiently. Moreover, it explores the cyber security that representing the real defiant to implement the concept of smart grid safely.
Application of Bayesian network in risk assessment for website deployment scenarios
Abstract—The rapid development of web-based systems in the digital transformation era has led to a dramatic increase in the number and the severity of cyber-attacks. Current attack prevention solutions such as system monitoring, security testing and assessment are installed after the system has been deployed, thus requiring more cost and manpower. In that context, the need to assess cyber security risks before the deployment of web-based systems becomes increasingly urgent. This paper introduces a cyber security risk assessment mechanism for web-based systems before deployment. We use the Bayesian network to analyze and quantify the cyber security risks posed by threats to the deployment components of a website. First, the deployment components of potential website deployment scenarios are considered assets, so that their properties are mapped to specific vulnerabilities or threats. Next, the vulnerabilities or threats of each deployment component will be assessed according to the considered risk criteria in specific steps of a deployment process. The risk assessment results for deployment components are aggregated into the risk assessment results for their composed deployment scenario. Based on these results, administrators can compare and choose the least risky deployment scenario. Tóm tắt—Sự phát triển mạnh mẽ của các hệ thống trên nền tảng web trong công cuộc chuyển đổi số kéo theo sự gia tăng nhanh chóng về số lượng và mức độ nguy hiểm của các cuộc tấn công mạng. Các giải pháp phòng chống tấn công hiện nay như theo dõi hoạt động hệ thống, kiểm tra và đánh giá an toàn thông tin mạng được thực hiện khi hệ thống đã được triển khai, do đó đòi hỏi chi phí và nhân lực thực hiện lớn. Trong bối cảnh đó, nhu cầu đánh giá rủi ro an toàn thông tin mạng cho các hệ thống website trước khi triển khai thực tế trở nên cấp thiết. Bài báo này giới thiệu một cơ chế đánh giá rủi ro an toàn thông tin mạng cho các hệ thống website trước khi triển khai thực tế. Chúng tôi sử dụng mạng Bayes để phân tích và định lượng rủi ro về an toàn thông tin do các nguồn đe dọa khác nhau gây ra trên các thành phần triển khai của một website. Đầu tiên, các thành phần triển khai của các kịch bản triển khai website tiềm năng được mô hình hoá dưới dạng các tài sản, sao cho các thuộc tính của chúng đều được ánh xạ với các điểm yếu hoặc nguy cơ cụ thể. Tiếp đó, các điểm yếu, nguy cơ của từng thành phần triển khai sẽ được đánh giá theo các tiêu chí rủi ro đang xét tại mỗi thời điểm cụ thể trong quy trình triển khai. Kết quả đánh giá của các thành phần triển khai được tập hợp lại thành kết quả đánh giá hệ thống trong một kịch bản cụ thể. Căn cứ vào kết quả đánh giá rủi ro, người quản trị có thể so sánh các kịch bản triển khai tiềm năng với nhau để lựa chọn kịch bản triển khai ít rủi ro nhất.
A Hybrid Framework for Intrusion Detection in Healthcare Systems Using Deep Learning
The unbounded increase in network traffic and user data has made it difficult for network intrusion detection systems to be abreast and perform well. Intrusion Systems are crucial in e-healthcare since the patients' medical records should be kept highly secure, confidential, and accurate. Any change in the actual patient data can lead to errors in the diagnosis and treatment. Most of the existing artificial intelligence-based systems are trained on outdated intrusion detection repositories, which can produce more false positives and require retraining the algorithm from scratch to support new attacks. These processes also make it challenging to secure patient records in medical systems as the intrusion detection mechanisms can become frequently obsolete. This paper proposes a hybrid framework using Deep Learning named “ImmuneNet” to recognize the latest intrusion attacks and defend healthcare data. The proposed framework uses multiple feature engineering processes, oversampling methods to improve class balance, and hyper-parameter optimization techniques to achieve high accuracy and performance. The architecture contains <1 million parameters, making it lightweight, fast, and IoT-friendly, suitable for deploying the IDS on medical devices and healthcare systems. The performance of ImmuneNet was benchmarked against several other machine learning algorithms on the Canadian Institute for Cybersecurity's Intrusion Detection System 2017, 2018, and Bell DNS 2021 datasets which contain extensive real-time and latest cyber attack data. Out of all the experiments, ImmuneNet performed the best on the CIC Bell DNS 2021 dataset with about 99.19% accuracy, 99.22% precision, 99.19% recall, and 99.2% ROC-AUC scores, which are comparatively better and up-to-date than other existing approaches in classifying between requests that are normal, intrusion, and other cyber attacks.
Export Citation Format
Share document.

- Google Meet
- Mobile Dialer

Resent Search

Management Assignment Writing

Technical Assignment Writing

Finance Assignment Writing

Medical Nursing Writing

Resume Writing

Civil engineering writing

Mathematics and Statistics Projects

CV Writing Service

Essay Writing Service

Online Dissertation Help

Thesis Writing Help

RESEARCH PAPER WRITING SERVICE

Case Study Writing Service

Electrical Engineering Assignment Help

IT Assignment Help

Mechanical Engineering Assignment Help

Homework Writing Help
Science Assignment Writing

Arts Architecture Assignment Help

Chemical Engineering Assignment Help
Computer Network Assignment Help

Arts Assignment Help

Coursework Writing Help

Custom Paper Writing Services

Personal Statement Writing

Biotechnology Assignment Help
C Programming Assignment Help

MBA Assignment Help

English Essay Writing
MATLAB Assignment Help

Narrative Writing Help

Report Writing Help
Get Top Quality Assignment Assistance

Online Exam Help

Macroeconomics Homework Help
Change Management Assignment Help

Operation management Assignment Help

Strategy Assignment Help

Human Resource Management Assignment Help

Psychology Assignment Writing Help
Algebra Homework Help

Best Assignment Writing Tips

Statistics Homework Help
CDR Writing Services

TAFE Assignment Help

Auditing Assignment Help

Literature Essay Help

Online University Assignment Writing

Economics Assignment Help

Programming Language Assignment Help

Political Science Assignment Help

Marketing Assignment Help

Project Management Assignment Help

Geography Assignment Help

Do My Assignment For Me

Business Ethics Assignment Help

Pricing Strategy Assignment Help
The Best Taxation Assignment Help

Finance Planning Assignment Help

Solve My Accounting Paper Online

Market Analysis Assignment

4p Marketing Assignment Help
Corporate Strategy Assignment Help

Project Risk Management Assignment Help

Environmental Law Assignment Help

History Assignment Help

Geometry Assignment Help

Physics Assignment Help

Clinical Reasoning Cycle

Forex Assignment Help

Python Assignment Help

Behavioural Finance Assignment Help

PHP Assignment Help
Social Science Assignment Help

Capital Budgeting Assignment Help

Trigonometry Assignment Help

Java Programming Assignment Help

Corporate Finance Planning Help

Sports Science Assignment Help

Accounting For Financial Statements Assignment Help

Robotics Assignment Help

Cost Accounting Assignment Help
Business Accounting Assignment Help

Activity Based Accounting Assignment Help

Econometrics Assignment Help

Managerial Accounting Assignment Help

R Studio Assignment Help

Cookery Assignment Help

Solidworks assignment Help
UML Diagram Assignment Help

Data Flow Diagram Assignment Help

Employment Law Assignment Help

Calculus Assignment Help

Arithmetic Assignment Help

Write My Assignment

Business Intelligence Assignment Help

Database Assignment Help

Fluid Mechanics Assignment Help

Web Design Assignment Help

Student Assignment Help

Online CPM Homework Help

Chemistry Assignment Help

Biology Assignment Help

Corporate Governance Law Assignment Help
Auto CAD Assignment Help

Public Relations Assignment Help

Bioinformatics Assignment Help
Engineering Assignment Help
Computer Science Assignment Help

C++ Programming Assignment Help

Aerospace Engineering Assignment Help

Agroecology Assignment Help

Finance Assignment Help

Conflict Management Assignment Help

Paleontology Assignment Help

Commercial Law Assignment Help

Criminal Law Assignment Help

Anthropology Assignment Help

Biochemistry Assignment Help

Get the best cheap assignment Help

Online Pharmacology Course Help

Urgent Assignment Help

Paying For Assignment Help

HND Assignment Help

Legitimate Essay Writing Help

Best Online Proofreading Services
Need Help With Your Academic Assignment

Assignment Writing Help In Canada

Assignment Writing Help In UAE

Online Assignment Writing Help in the USA

Assignment Writing Help In Australia

Assignment Writing Help In the UK

Scholarship Essay Writing Help

University of Huddersfield Assignment Help

Ph.D. Assignment Writing Help

Law Assignment Writing Help

Website Design and Development Assignment Help

University of Greenwich Assignment Assistance in the UK
130 New Research Paper Topics for Cybersecurity
In today's society, where everything is online, including photos, videos, important documents, and private information, cybersecurity is vital. Safeguarding our data can be challenging, and since we don't understand cybersecurity, it's more difficult to prevent cybercrimes. Learning about cybersecurity is a fantastic method to avoid it, which is why today's young people are becoming interested in and studying cybersecurity. Computer security, digital security, and many other terms are used to refer to cybersecurity. Cyber security is defending the network and computer from online threats and crimes that expose confidential data or steal it through computer hacking. So, in this blog, we will talk about cybersecurity and the 130 cybersecurity research paper questions that might help you with your research paper.
What Is Cybersecurity?
The kind of security known as computer security is used to safeguard computer networks, systems, and other items that are vulnerable to cyberattacks. and as far as we are aware, the widespread usage of the internet explains this. therefore the primary objective of cybersecurity is to protect the availability and confidentiality of vital information as well as big databases like the financial and private data of any nation. All of these require a safety measure to keep them all secure. To protect the systems, cyber security utilises a variety of techniques and technologies. Furthermore, there are other sorts of cybersecurity, such as application security, cloud security, data security, mobile security, and many more.
Since the development of the internet and subsequent waves of digital change in recent years, cybersecurity has not had a very long history. Moreover, cybersecurity has grown in popularity in the online community. Furthermore, the 1970s marked the beginning of cybersecurity and the cyber threat. When the internet first began to expand, computer security was primarily restricted to academic settings. As a result, additional things became available, and online cybersecurity became recognised. Nowadays, cybersecurity is a delicate topic since cyber threats are so common. In the past, there weren't many different kinds of cyber threats, but attackers were also evolving and trying to obtain access to systems to make money. and the popularity of cyber security began to grow.
Studying cyber security has many advantages, the primary one being that it's an extremely difficult field of work. It's also a very sensible job choice because you can apply your practices to the current work. You can use them right away in real projects after earning your degree. additionally, you'll pick up a lot of talents and build a solid career.
Cybersecurity Research Paper Topics
- What are zero-day vulnerabilities and how do they affect cybersecurity?
- Explain ransomware attacks and defense mechanisms.
- How to recognize attacks that are phishing?
- How does the transaction security feature of blockchain technology operate?
- Explain the concepts of cloud security and data protection.
- Describe the importance of cybersecurity for vital infrastructure.
- Explain the healthcare system's cybersecurity.
- Describe the various forms of cyberattacks.
- The significance of cybersecurity in self-driving cars.
- The 5G network: is it safe? Explain.
- Explain the security issues with remote employment.
- Understanding cybersecurity is crucial for e-commerce.
- Explain the significance of cybersecurity for online transactions.
- Talk about how secure smart home technology is.
- Explain the efficient ransomware defense.
- Information access management: what is it?
- Describe safe Wi-Fi practices in detail.
- Explain industrial control's cybersecurity.
- What are the insider threats and staff training?
- Describe the procedures for protecting voter data and the electoral system.
- Describe end-to-end encryption and discuss the issues around it.
- What is cybersecurity crucial for businesses?
- What standards and procedures are in place for secure communication?
- Talk about the weaknesses in mobile apps and the security of mobile devices.
- Explain the security factors to be taken into account while using AI and machine learning.
- Talk about cybersecurity in the field of education.
- Explain the dangers of social networking as well as the privacy concerns.
- Describe the defence system and the security system to the government.
- Describe the ransomware and the system's impact.
- Describe the attacks by the "man in the middle."
- Phishing: What is it? Explain.
- Explain how the cyberattacks got started.
- What does a denial of service attack entail?
- Eavesdropping: What is it? Explain.
- The side channel attack: what is it? Explain.
- Describe how to protect yourself from online threats.
- Explain the definition of spoofing and its various forms.
- What is smuggling HTML? Explain.
- How are the financial systems maintained? Explain.
- ways to use cyber security to help healthcare providers maintain secure patient records.
- Describe the safety precautions.
- Describe the protective methods for hardware.
- What is digital hygiene in cybersecurity?
- Explain the many security and privacy measures.
- Describe the various kinds of breaches in computer security.
- Cyber Law: What Is It? Explain.
- Tell me about cloud security.
- Describe what constitutes a cyberbully.
- How can mental health be impacted by cyberbullying?
- Catfishing: What is it? Explain.
- Cybercrime inside the IT sector.
- Cybersecurity in the utilities and energy industries.
- Why is a cybersecurity system necessary for a smart city?
- Explain the distributed denial of service defences.
- Explain the security in the age of quantum computing.
- Why is drone cybersecurity important?
- Why is cybersecurity crucial for autonomous vehicles?
- Explain the voice-activated smart assistants' security.
- Explain the cyber threats that the travel industry faces.
- Explain the cyber threats facing the aerospace sector.
- Explain how e-learning platforms are secure.
- ways to safeguard private information when doing virtual meetings.
- describe virtual private network security.
- What does the financial services industry mean by secure communication?
- Are apps for mobile banking safe to use? Explain.
- ways to safeguard intellectual property in the modern world.
- Threats from cyberspace to the legal sector? Explain.
- Explain the cyber threats facing the fashion sector.
- What part does cyber threat detection play in machine learning?
- What is a social engineering attack?
- You may protect your files and private data with a strong password.
- What role does data backup play?
- How to create a safe hybrid cloud infrastructure.
- What is security in a blockchain? Explain.
- Why is it critical to provide cyber security awareness training to your employees?
- How can code be secured?
- Explain Internet of Things security.
- In what way is the wireless network secure? Explain.
- Which deception strategies are used in cyber security?
- Why is it that small businesses need to know about cybersecurity?
- What cyber security issues does the gaming sector need to address?
- What part does national security play in cybersecurity?
- Which algorithms are used in data encryption?
- Which computer viruses are the best known?
- What risks come with utilising free public wifi?
- ways to make a household Wi-Fi connection secure.
- Define cyberterrorism.
- Why is it crucial to teach students about cyber etiquette?
- Explain the ways to use online platforms safely.
- What does it mean to be cyberstalked?
- How is the advancement of technology impacting and elevating cybercrime?
- What is faking a website? Explain.
- How do forgery attacks work?
- Is the number of hackers increasing due to social media? Explain.
- Explain the methods for protecting your machine against online threats.
- On what basis does the ghostNet function?
- In cybercrimes, what does whistleblowing mean?
- reasons for knowing about advanced cybersecurity.
- How does the advancement of technology impact and heighten cybercrime?
- Are hackers becoming more prevalent on social media? Explain.
- What is the operating system of ghostNet?
- Is allowing apps a security risk? Describe.
- Explain the ethical hacking.
- What is digital piracy? Explain.
- What kinds of attacks use SQL injection?
- Is it deemed safe to use two-factor authentication?
- Is cryptography defined?
- What is hacking in cars? Explain.
- What does computer risk management entail?
- What role does a software update play?
- How does the business ensure the security of its network? Explain.
- What systems are in place to avoid data loss?
- Is it safe to share information online? Explain.
- What role do cookies and privacy play?
- Ways to guarantee data accuracy.
- Explain the viruses that encrypt.
- Physical data security: what is it?
- how to stop mobile data leaks.
- How to protect your Google Play apps from unwanted behaviour.
- Explain the significance of using a strong password.
- Ways to guarantee email security.
- Quantum technologies: what are they? Explain.
- What are the data breaches? Explain.
- A brute force attack is what? Explain.
- What is hacking a car? Explain.
- How can fraud with credit cards occur? Explain.
- Periodic cyberbullying: what is it?
- How can lost data be recovered? Explain.
- How to detect an effort at phishing.
- Why is cybersecurity important in online communication?
We've talked about cybersecurity on this blog and its various forms. We have also spoken about the various forms of cybersecurity that can assist you in writing your research paper and provide you with ideas for writing one. Additionally, AHEC is available to assist you with all of your assignment help needs if you require it.
Frequently asked questions
What are some research topics in cyber security .
2022's Top 08 Cybersecurity Topics
Are portable media a danger?
flaws in the blockchain's security.
Why should you stay away from free WiFi?
how to stop phishing scams.
Banks have physical security measures.
Violations of remote working security.
What is the process of two-factor authentication?
how to stop attempts at social engineering.
What are current trending topics in cybersecurity ?
What are the main cyber threats of 2022 , what are the 3 major threats to cyber security today .
Here are the top five online dangers that people face today:
- Attacks using social engineering (or phishing)
- Ransomware.
- assaults on mobile security.
- Risks of working remotely.
Is cybersecurity a good research topic ?
What is the #1 cybersecurity threat today , what is the biggest cybersecurity issue , how do i write a research paper for cyber security .
How to Choose the Best Cybersecurity Research Paper Topics: Four Tips
- Brainstorm. Brainstorming ideas is the initial step in choosing the finest heading for your cybersecurity assignment article.
- Understanding the history
- Write about just one subject.
- Be adaptable.
What is the big 4 in cyber security ?
What are the top 5 emerging cyber security challenges .
The top 5 issues that the cybersecurity sector is now experiencing are as follows:
- Working remotely The COVID-19 epidemic has permanently altered the workplace and the security measures in place.
- Cloud-based attacks.
- Phishing Schemes.
- Attacks on the blockchain and cryptocurrencies.
- Attacks on the Internet of Things (IoT).

Top 10 Best Universities Ranking list in India 2022

Generic Conventions: Assignment Help Services

Research Paper Topics For Medical

Top 5 Resources for Writing Excellent Academic Assignments

How to Write a Literature Review for Academic Purposes

Tips for Writing a killer introduction to your assignment

How To Write A Compelling Conclusion For Your University Assignment

Research Papers Topics For Social Science

Best 150 New Research Paper Ideas For Students

7 Best Plagiarism Checkers for Students And Teachers in 2024
Enquiry form.
Custom Essay, Term Paper & Research paper writing services
- testimonials
Toll Free: +1 (888) 354-4744
Email: [email protected]
Writing custom essays & research papers since 2008
154 exceptional cybersecurity research topics for you.

If you are studying computer science or IT-related course, you will encounter such a task. It is one of the most technical assignments, primarily in the era of advanced digital technologies. Students may not have the muscles to complete such papers on their own. That is why we provide expert help and ideas to make the process easier.
Do you want to excel in your cybersecurity paper? Here is your number one arsenal!
What You Need To Know About Cyber Security Research Topics
A cybersecurity paper deals with the practices of protecting servers, electronic systems, computers, and networks from malicious attacks. Although most students think this only applies to computers, it also applies to mobile computing and other business models.
There are various categories in cybersecurity, including:
Network security Application security Information security Operational security Disaster recovery and business continuity
Therefore, your cybersecurity topics for research should:
Examine the common security breaches in systems and networks Offer practical ways of protecting computers from such attacks Highlight the legal and ethical implications of hacking and other related practices Point out the challenges encountered in combating cybercrime
Since this is a technical paper, you should endeavor to do your research extensively to prevent rumors and unverified facts. The topics should also inform and educate people who are not conversant with cybersecurity in simple terms. Avoid using jargon at all costs, as this will make the paper difficult to read and understand.
Are you worried about where you can get professional cybersecurity topics and ideas? Well, here are a few of the most reliable sources that can furnish you with top-rated issues.
- Government legislation on cybersecurity (Acts of Parliament)
- The UN Office of Counter-Terrorism (Cybersecurity initiatives)
- The CISCO magazine
- Forbes also has excellent coverage on cybersecurity
You can find impressive topic ideas from these sources and more. Furthermore, news headlines and stories on cybersecurity can also help you gather many writing ideas. If all these prove futile, use our tip-top writing prompts below:
Quality Cyber Security Thesis Topics
- Impacts of coronavirus lockdowns on cybersecurity threats in the US
- Why ethical hacking is contributing to more harm than good
- The role of computer specialists in combating cyber threats before they occur
- Technological trends that are making it difficult to manage systems
- Are passwords reliable when protecting computer systems?
- Effects of having more than one systems administrator in a company
- Can the government shut down the dark web once and for all?
- Why should you bother about the security of your mobile device?
- Evaluate reasons why using public WIFI can be harmful to your security
- The role of cybersecurity seminars and conferences
- How universities can produce ethical computer hackers who can help the society
- How to counter-terrorism with advanced cybersecurity measures
- Impacts of teaching children how to use computers at a tender age
- Latest innovations that are a threat to cybersecurity
- The role of monitoring in combating frequent cyber attacks
- How social media is contributing to cyber attacks
- Discuss the relationship between cyberbullying and cybersecurity
- Why fingerprints may be the best method of protecting devices
- The role of YouTube in contributing to the rising number of hackers
Top Research Topics For Cyber Security For Master Thesis
- Impact of cyber threats on attaining the sustainable development goals
- Why websites are becoming easy to hack in the 21 st century
- Effects of not having an SSL certificate for a website
- Discuss the security threats associated with WordPress websites
- Impacts of frequent maintenance while the website is still running
- How computer colleges can contribute to a safe cyberspace
- Latest cyber threats to business and financial websites
- Discuss the implications of cyber threats on privacy
- The role of Facebook in advancing cyberbullying and hacking
- Is hacking becoming a global epidemic in the digital world?
- Why using Cyber Cafes may be detrimental to your digital security
- The role of systems analysts in responding to data breaches
- How cybersecurity movies are contributing to cyber threats
- Should hackers face lifetime jail imprisonment when found guilty?
- Loopholes in cyber laws that make the practice challenging to curtail
Good Thesis Topics For Cyber Security
- The relationship between privacy and data security in computing
- Why cloud computing offers a haven for computer hackers
- The role of character and human-based behavior in cybersecurity
- How to determine safe organizational security management and policy
- How the Internet of Things is promoting cyber attacks
- Effects of using cracked computer software
- Are biometrics in cybersecurity able to put off hackers?
- The role of studying mobile platform security
- Why companies should frequently monitor their firewalls
- The role of antimalware in curbing cyber attacks
- Why is Ransomware a headache to most companies handling big data?
- How does antivirus software improve the security of your computer?
- Compare and contrast between the security of UNIX and Ubuntu
- The role of data encryption technologies in ensuring system security
- Is the process of encrypting viruses safe?
Top-Grade Thesis Topics For Cyber Security
- Describe the effectiveness of cybersecurity audits on company systems
- Is it proper to conduct device synchronization?
- Why is it difficult to manage the security of an intranet?
- Discuss the effects of logging in to many devices at the same time
- Evaluate the significance of computer forensics
- How are hackers inventing new ways of breaching the systems of companies?
- Why it is necessary to review the data protection laws
- Practices that increase the vulnerability of a system to cyber attacks
- Can organizations implement impenetrable network systems?
- Why administrators should check the background of users before giving them rights and privileges
- The role of risk management cybersecurity
- Discuss the impact of reverse engineering on computing systems
- Effects of a cyber-attack on a company’s economic performance
- What legal frameworks work best for a computer company?
- The role of social engineering in cybersecurity
Information Security Research Topics
- The implication of the proliferation of the internet globally
- Innovative technologies used in keeping off hackers
- The role of information communication technologies in maintaining the security
- Are online courses on informative security practical?
- Why should people avoid sharing their details on Facebook?
- Effects of using your image on social media
- The role of pseudo names and nicknames on social media
- Discuss the implications of Wi-Fi hacking apps on mobile phones
- How to detect malicious activity on a system
- Evaluate the potential threats of conduct self-hacking on a system
- The impact of sharing personal details with hiring agencies
- How con artists lure unsuspecting applicants into giving out their details
- Effects of frequent maintenance on systems
- How to strengthen the firewall of an information system
- The role of the media in propagating security breaches to information systems
Latest Computer Security Research Topics
- Tricks that black hat hackers use to infiltrate company systems
- How children learn about cybersecurity from their parents
- The impact of watching hacking movies and TV series
- How various companies are protecting themselves from cyber attacks
- Why every company should have a systems security consultant
- Discuss the implication of digital piracy
- Threats that biometrics are bringing to digital systems
- How to block a network intrusion before it causes any effect
- Why MacOS is challenging to infiltrate, unlike Windows
- Results of two-step authentication security measures for login systems
- The role of updating computer systems during working days
- Evaluate times of the year when hackers infiltrate systems the most
- Why it isn’t easy to manage big data on the cloud
- What happens during a system breakdown and maintenance?
- Discuss the role of data synchronization in creating a backup
Network Security Research Paper Topics
- The impact of having self-configuring and decentralized network systems
- Effects of ad-hoc networks for large companies
- Discuss the role of wireless sensor networks in contributing to security breaches
- How malicious nodes join a network
- Why it is difficult to detect a passive network attack
- How active network attacks reduce a network’s performance
- Evaluate the various parameters used in network security
- Analyze how a black hole affects a network system
- Describe techniques used in detecting malicious nodes on networks
- How to improve the safety of a company network
- The role of data encryption in maintaining the security of a network
- Describe the various channels of establishing secure algorithms in a network
- How does RSA increase the safety of a particular network?
- Effective policies and procedures for maintaining network security
- The role of a unique ID and Password in securing a website
Computer Security Research Topics
- Why it is challenging to maintain endpoint security
- The role of a critical infrastructure cybersecurity
- How to create secure passwords for your computer network
- The part of scanning for malware often on your PC
- How to detect apps that invade your privacy unknowingly
- Why ordering software from the black market is a threat to security
- Safe computing techniques for first-time computer users
- The role of digital literacy in preventing hacking
- Why most online users fall to online scams
- The role of smartphones in enhancing cybersecurity threats
- Evaluate the mobile landscape concerning data security
- The implication of private email accounts in data breaches
- Sites that contain a barrel of internet criminals
- How to develop comprehensive internet security software
- How children can navigate the internet safely
Impressive Cyber Crime Research Topics
- Why cyber currencies are a threat to online security
- Why cyberbullying is rampant in the 21 st century unlike in any other time
- The impact of online persuasion campaigns on cybersecurity
- Why teenagers are victims of cyberbullying than adults
- Discuss the effects of technology evolution on cybercrime
- How online hackers collect information without the knowledge of the victim
- Traits of a robust cybersecurity system
- Practices that can help reduce cybercrime in institutions of higher learning.
- Effects of global coordinated cyber attacks
- The penalties of cyber-attack in the First Amendment
- Why the world is experiencing increased cyber attacks
- Critical concepts of cyber attacks
- Cybercriminals and enterprises
- Role of NGOs in combating cyber terrorism
- Cyberbullying in campus
World-Class Cyber Security Thesis Ideas
- Effects of the cyber-attack on Sony in 2014
- The role of globalization in enhancing cybersecurity
- How to prevent automotive software from malicious cyber attacks
- The role of cyber technology in changing the world since the 1990s
- How the private sector is essential in combating cyber threats
- Computer infrastructure protection against cyber attacks
- Impact of social networking sites on cybersecurity
- Threats that cyber-attacks pose the national security of a country
- How cyber monitoring affects ethical and legal considerations
- Factors leading to the global nature of cyber attacks
- Analyze law enforcement agencies that deal with cyber attacks
- Evaluate cyber-crime court cases
- Evolution of the cybersecurity industry
- Cyber terrorism in the US
- Implementing adequate data protection strategies
We offer paper writing help on any cybersecurity topic. Try us now!
Top 111+ Stunning Cybersecurity Research Topics For 2023

Are you confused about cybersecurity and its research topics? So here, in this blog, we will discuss cybersecurity research topics. This article is important If you are studying computer science or a cybersecurity course.
If you want good grades in cybersecurity research topics, you should pick the latest cybersecurity research topics for your academic exam or test. Here, you can choose the good and latest cybersecurity research topics.
You know that cybercrime is increasing day by day because millions of people use the internet. Several applications deal with the internet, and people normally use the internet for bank transactions, food delivery, online shopping, social media, gaming, etc. Attackers can steal your information, data, and money with the help of malicious software, So we need cybersecurity services.
What is Cybersecurity?
Table of Contents
Cybersecurity is a process of preventing unauthorized access or protecting networks, devices, and data from digital attacks. Cybersecurity is also known as IT(Information Technology)Security which is designed to prevent threats against network systems, applications, and other platforms. In simple words, It prevents or protects any information, data, and others.
Here Are Some of the Best Writing Tips From Statanalytica’s Expert
As you might already know that a well-planned action and a set of useful tools will also help you write a high-quality research paper. On the other hand, remaining motivated throughout the process.
- By choosing an interesting topic for your research paper.
- Conduct some research to find reputable sources.
- Clearly state your cybersecurity thesis.
- A rough plan should be created.
- Finish your paper by drafting it.
- Make sure your content is properly formatted.
- Make sure you understand the assignment before you begin writing your research paper.
Let’s Discuss the 111+ Stunning Cybersecurity Research Topics
Below we listed 111+ cybersecurity research topics that can be used in 2023:
Top 10 Cyber Security Topics of 2023
Here are the top 10 cyber security topics of 2023:
- Can strong passwords protect information?
- Is security in critical infrastructure important?
- The importance of end-user education
- Cloud security posture management
- How does malware work?
- The principle of zero trust access
- 3 phases of application security
- Should removable media be encrypted?
- The importance of network security
- Do biometrics ensure the security of iPhones?
Latest Cybersecurity Research Topics of 2023
- Is removable media a threat?
- Cybersecurity standards for automotive
- How to prevent social engineering attacks
- Security breaches of remote working
- How to prevent phishing attacks
- Physical security measures in banks
- Privacy settings of social media accounts
- Blockchain security vulnerabilities
- Why should you avoid public Wi-Fi?
- How does two-factor authentication work?
- Cryptography
- Discuss the importance of intranet security
- Rise of Automotive Hacking
- What is ethical hacking?
- The evolution of phishing and how it is becoming more sophisticated
- Which antivirus software is the best in the world?
- The most up-to-date and trending cybersecurity technology
- How can organizations prevent network attacks?
- What is Digital Piracy?
- Application of biometrics in cyber security?
- Identity theft on the Internet
- Risk management in computing
- Rise of computer forensics
- Threats are analyzed using digital forensic techniques
- What is a Remote Access VPN?
- Digital security and Social Networks
- The risks of using public Wi-Fi networks
- Popular online scams in 2022
- Artificial intelligence security systems
Network Security Research Topics
- Data storage centralization
- Identify Malicious activity on a computer system.
- Importance of keeping updated Software
- wireless sensor network
- What are the effects of ad-hoc networks
- How can a company network be safe?
- What are Network segmentation and its applications?
- Discuss Data Loss Prevention systems
- Discuss various methods for establishing secure algorithms in a network.
- Talk about two-factor authentication
Topics for Application Security Research
- Discuss SQL injection attacks.
- Inadequately configured security protocols.
- Talk about data leaks in mobile apps.
- Backend access control is critical.
- Logging has many advantages for applications.
- Malicious apps are available on Google Play.
- AI applications: ethical constraints and opportunities.
- What is the effect of insecure deserialization?
- The most effective application security testing practices.
- Apps are vulnerable to XSS attacks.
Information Technology Security Research Topics
- Why should people avoid sharing their details on Facebook?
- What is the importance of unified user profiles?
- Discuss Cookies and Privacy
- White hat and black hat hackers
- What are the most secure methods for ensuring data integrity?
- Talk about the implications of Wi-Fi hacking apps on mobile phones
- Analyze the data breaches in 2022
- Discuss digital piracy in 2022
- critical cyber-attack concepts
- Social engineering and its importance
Operational Security Research Topics In 2023
- Securing containerized applications in cloud environments.
- Implementing secure remote access policies for remote workers.
- Evaluating the effectiveness of endpoint protection solutions.
- Protecting against DNS tunneling attacks.
- Securing cloud-based storage solutions.
- Developing secure mobile device management policies.
- Analyzing the effectiveness of honeypots in detecting attacks.
- Securing software supply chains against attacks.
- Investigating the effectiveness of deception technologies in cybersecurity.
- Developing secure network segmentation strategies.
- Evaluating the effectiveness of network traffic analysis solutions.
- Analyzing the effectiveness of two-factor authentication in securing systems.
- Securing critical infrastructure against cyber threats.
- Developing secure email policies to prevent phishing attacks.
- Investigating the use of artificial intelligence in cybersecurity.
- Developing secure DevOps practices.
- Analyzing the effectiveness of security information and event management (SIEM) solutions.
- Securing the Internet of Things (IoT) devices.
- Evaluating the effectiveness of password management solutions.
- Developing secure incident response strategies.
Topics for a Research Paper on CyberCrime Prevention
- Criminal Specialization.
- Drug Courts.
- Capital Punishment.
- Criminal Courts.
- Crime Prevention.
- Community Corrections.
- Criminal Law.
- Criminal Justice Ethics.
Computer and Software Security Research Topics
- Learn algorithms for data encryption.
- Concept of risk management security.
- How to develop the best internet security software.
- What are Encrypting viruses- How does it work?
- How does a Ransomware attack work?
- Scanning of malware on your PC.
- Infiltrating a Mac OS X operating system.
- What are the effects of RSA on network security?
- How do encrypting viruses work?
- DDoS attacks on IoT devices.
Computer and Software Cyber Security Topics
- The importance of updating computer software.
- How to safeguard your computer against malware and other threats.
- The best security practices for your computer and software.
- The various types of cyber security threats and how to avoid them.
- The significance of cyber security education and awareness.
- The importance of cyber security in protecting critical infrastructure.
Data Security Research Topics
- Importance of backup and recovery.
- Benefits of logging for applications.
- Understand physical data security.
- Importance of Cloud Security.
- In computing, the relationship between privacy and data security.
- Discuss the effects of a black hole on a network system.
Application Security Topics
- Detect Malicious Activity on Google Play Apps.
- Dangers of XSS attacks on apps.
- Insecure Deserialization Effect.
- Check Security protocols.
CyberSecurity Law Research Paper Topics
- Strict cybersecurity laws in China.
- Importance of the Cybersecurity Information Sharing Act.
- USA, UK, and other countries cybersecurity laws.
- Discuss The Pipeline Security Act in the United States.
If you are interested in criminal research topics, then here are the best criminal justice research topics for you.
How to Choose The Best Cybersecurity Research Topics in 2023
There are a few factors to consider when selecting cybersecurity research topics. The first and main thing to consider is to ensure that the topic is current and relevant. Because cyber security is a changing field. As a result, it is very crucial to select a topic that will be relevant for a few months.
On the other hand, the second thing to consider is to select an interesting and engaging topic. Because cyber security can be a dry subject, it is critical to select a topic that will keep readers interested.
Finally, it is very important to select a researchable topic. There are several cybersecurity topics available, but not all of them are simple to research. Choose a topic about which there is a lot of information.
- Determine your target audience
- Define your research objectives
- Choose a topic that your audience will find both interesting and relevant
- Conduct preliminary research to ensure that there is sufficient information available on your chosen topic
- Make sure your topic is focused enough to fit into a single research paper
Research Area in Cyber Security
Cybersecurity is extensive, and constantly evolving field. On the other hand, its research takes place in many areas:

- Quantum & Space
- Data Privacy
- Criminology & Law
- AI & IoT Security
Get More Cybersecurity Research Topics
In this blog, we have covered the 111+ best cybersecurity research topics. These cybersecurity topics help in your exam or test. If you have any difficulty with cybersecurity research topics, you can take cybersecurity research paper help or research paper assignment help at a very affordable price.
Here are some of the benefits of taking cybersecurity research topics help from us.
- 24 Hours Availability
- On-time Delivery
- Free Corrections
- Money-Back Guarantee
- Affordable Deals
- Professional Experts
You can contact us any time and impress your teacher by choosing a good cybersecurity research topic.
This is the end of the post, which is about cybersecurity research topics. On the other hand, we mentioned 111+ stunning cybersecurity research topics for 2023 offer an excellent opportunity for researchers to explore and address critical cybersecurity challenges. However, the ever-evolving technological landscape presents new security challenges every day, and it is essential to keep up with the latest trends to stay ahead of cyber threats.
On the other hand, these research topics provide many areas to explore, from network security, the internet of things, and software security to network security, cryptography, and data security. I hope you like this post.
Q1. What are the types of cyber security threats?
There are several different types of cyber security threats. More popular are Trojan horses, worms, ransomware, and phishing scams. These types of threats can be very dangerous for the cyber system.
Q2. What are the most controversial topics in criminal justice?
1. Prisoners being granted the right to work 2. Carrying a concealed weapon 3. Prison rape and violence 4. Plea agreement/bargain 5. Rehab vs. reform. 6. Is an eyewitness testimony effective? 7. Enforcement and effectiveness of stalking laws. 8. Rape culture and the victim’s rights
Q3. What are the main cyber threats of 2023?
There are multiple cyber security threats, but the main social threats of 2023 are email impersonation and phishing. On the other hand, email impersonation is a phishing technique in which a fake email address that appears to be legitimate is used.
Related Posts

Step by Step Guide on The Best Way to Finance Car

The Best Way on How to Get Fund For Business to Grow it Efficiently
- Write my thesis
- Thesis writers
- Buy thesis papers
- Bachelor thesis
- Master's thesis
- Thesis editing services
- Thesis proofreading services
- Buy a thesis online
- Write my dissertation
- Dissertation proposal help
- Pay for dissertation
- Custom dissertation
- Dissertation help online
- Buy dissertation online
- Cheap dissertation
- Dissertation editing services
- Write my research paper
- Buy research paper online
- Pay for research paper
- Research paper help
- Order research paper
- Custom research paper
- Cheap research paper
- Research papers for sale
- Thesis subjects
- How It Works
50 Great Cybersecurity Research Paper Topics

Students are required to write papers and essays on cyber security topics when pursuing programs in cyber security disciplines. These topics are technical and they require learners to inherently understand this subject. What’s more, students should have impeccable research and writing skills.
Additionally, students should choose cyber security topics to write their papers and essays carefully. As a science field, cyber security is developing rapidly and constantly. As such, learners can always find interesting topics to write papers and essays about.
Pick Cyber Security Topics From Our List
Software and computer administration cyber security topics.
- Cyber Security Research Paper Topics on Data Protection
- Cyber Security Awareness Topics
Network Security Topic Ideas
- Current and Interesting Topics in Cyber Security
Nevertheless, selecting cybersecurity topics for research shouldn’t be a rushed process. That’s because the chosen topics will influence the experience of students while writing and the grades they will score. Therefore, learners should focus on choosing topics that they will be comfortable researching and writing about.
If you’re having a hard time choosing the topics to research and write about, here are categories of some of the best cybersecurity paper topics that you can consider. We also advise you to check out capstone project topics .
The cyber security of a company can be compromised in many ways when it comes to software and computer administration. As such, software and computer administration is a great sources of cybersecurity research paper topics. Here are some of the best topics in this category.
- Evaluation of the operation of antimalware in preventing cyber attacks
- How does virus encryption work
- Is countering malware difficult because of the fast evolution of technology?
- Why should companies train their staff on cyber security?
- Why should people worry about identity theft?
- How important are software updates when it comes to cyber security?
- What causes cyber crimes?
- What are the major threats to the cyber security of social media users?
- What are the most effective methods of preventing phishing?
- What is the major threat to cyber security today and why?
These topics address issues that affect anybody or any organization that uses a computer or any device to access the internet and exchange information. As such, most people, including teachers and professors, will be impressed by papers and essays written about them.
CyberSecurity Research Paper Topics on Data Protection
Individuals and companies send and receive a lot of data every day. As such, this category has some of the best cybersecurity topics for presentation. That’s because they address issues that affect many people and organizations. Here are some of the best information security topics to consider when writing papers and essays or preparing a presentation.
- The best security measures for protecting your data
- How third-party applications can be used to access and acquire data without permission
- How to prevent the loss of data from a computer
- Can biometrics be used to prevent unauthorized data access?
- Can you protect yourself from cyber crimes by keeping personal data private?
- What should you do in case of a data breach?
- How can you secure your data with a 2-steps authentication process?
- How can public Wi-Fi or the internet be used to steal personal data?
- What information can be accessed by unauthorized persons if they hack an account?
- Can software updates help in protecting personal data?
Every computer or internet user wants to be sure that their data is safe and protected. Papers and essays that are written on these topics address issues of data protection. As such, many people will find them worth reading.
CyberSecurity Awareness Research Paper Topics
The best cyber security topics for research papers do more than just address a single issue. They also inform the readers. Here are some of the best cyber security topics for research papers that also focus on creating awareness.
- What is reverse engineering?
- How efficient are RFID security systems?
- How does the dark web propagate organized cyber crimes?
- How can steganalysis be applied?
- Analyze the best authorization infrastructures today
- How important is computer forensics in the current digital era?
- What strategies have been proven effective in preventing cyber-attacks?
- Which forensic tools are the best when it comes to detecting cyber threats?
- Can changing the password regularly help in predicting a cyber attack?
- How can you tell that you’re at risk of online identity theft?
Many people are not aware of many things that affect their cyber security. These topics are relevant because they enhance the awareness of the internet and computer users.
Most organizations today have networked systems that enhance their operations. Unfortunately, criminals have learned to target those networked systems with their criminal activities. As such, students can address some of these issues with their cyber security thesis topics. Here are interesting topics that learners can research and write about in this category.
- Evaluation of the cyber security legal framework in the U.S
- Analysis of the most difficult aspect of the administration of cyber security
- How can the possibilities of multiple threats be managed effectively?
- How does data backup help when it comes to cyber security?
- How effective is two-factor authentication?
- How should a company respond to hacking in its system?
- Which are the best cyber security protection approaches for a multinational company?
- What are the pros and cons of unified user profiles?
- What are the most important components of effective data governance?
- What motivates individuals to commit cybercrimes?
These computer security topics can be used to write papers and essays for college or even commissioned by organizations and used for presentation purposes.
Current and Interesting Topics in CyberSecurity
Some computer security research topics seek to address issues that affect society at the moment. Here are examples of such topics.
- How phishing is evolving and getting more sophisticated
- Explain the evolution of Ransomware strategies
- Explain how the cryptocurrency movement affects cybersecurity
- Cyber-Physical Attacks: How do they work?
- What are state-sponsored attacks and how do they affect cyber security at a global level?
- Discuss cyber security risks when it comes to third-party vendor relationships
- How digital advertisements are being used to collect user characteristics
- How can a person sync all their devices while ensuring their protection
- Why it’s advisable to avoid downloading files from sites that are not trusted
- Why consumers should read the terms and conditions of software before they decide to install it
Such technology security topics are trendy because they address issues that affect most people in modern society. Nevertheless, students should conduct extensive research to draft solid papers and essays on these topics.
This cyber security topic list is not exhaustive. You can contact our thesis writers if you need more ideas or help. Students have many topics to consider depending on their academic programs, interests, and instructions provided by educators or professors. Nevertheless, students should focus on choosing topics that will enable them to come up with informative and comprehensive papers. Thus, every student should choose an information security topic for which they can find relevant and supporting data.
Leave a Reply Cancel reply
Mon - Sat 9:00am - 12:00am
- Get a quote
Unlock Your Insights and Excellence in Cyber Security Research Topics
Welcome to your gateway to unparalleled academic success in Cyber Security research topics. Are you ready to delve into the dynamic world of digital defence and safeguarding sensitive information? Look no further! Our research department is designed to empower you on your journey toward mastering cyber security research topics.
Is Research A Prompt Effort for Every Student?
Researching dissertation topics for cyber security can be challenging due to the constantly evolving nature of technology and the complex landscape of cybersecurity threats. Here are some challenges that students might face during their research on Cyber Security topics:
1. Rapid Technological Advancements:
The field of Cyber Security is fast-paced, with new technologies and vulnerabilities emerging frequently. Staying updated with the latest trends and developments can be a challenge, as what is relevant today might be outdated in a short span of time.
2. Diverse Range of Topics:
Cyber Security is a broad field encompassing various sub-disciplines such as network security, cryptography, malware analysis, digital forensics, and more. Students might struggle to choose a specific focus area for their research topics for cyber security due to the overwhelming range of topics.
3. Complexity of Technical Concepts:
Cyber Security research often involves complex technical concepts related to encryption, protocols, network architectures, and programming. Students without a strong technical background might find it challenging to grasp and communicate these concepts effectively.
4. Lack of Standardization:
The field lacks standardized methodologies for certain aspects of research, such as evaluating the effectiveness of security measures or assessing the impact of new attack vectors. This can lead to varied approaches in research for cyber security thesis topics which makes it challenging to compare and replicate results.
Get an Immediate Response
Discuss your requirments with our writers
Get 3 Customize Research Topic within 24 Hours
Undergraduate Masters PhD Others
Why Choose Us for Your Cyber Security Dissertation Topics?
Students resort to our services for dealing with their Cybersecurity dissertation topics due to the following reasons.
- Our team of experts brings a wealth of knowledge, real-world experience, and up-to-the-minute insights to ensure your research is both relevant and impactful.
- We offer personalized support and help you refine your research objectives, develop robust methodologies, and tackle intricate challenges specific to your dissertation Cyber Security
- We have easy access to a treasure trove of resources ranging from peer-reviewed journals and industry reports to cutting-edge tools and software. By harnessing the latest advancements in Cyber Security research topics 2023 we stay ahead of the curve.
- Our experts specialize in dissecting complex problems and offering innovative solutions that push the boundaries of the field.
- Our researchers meticulously craft research papers, case studies, and presentations to empower you to produce high-quality work that stands out in academia and beyond.
- All interactions and information shared with us are treated with the utmost confidentiality and integrity.
Free List of Cyber Security Research Topics 2023
Our professionals have created a well-researched and interesting list of cyber security research paper topics with aims and objectives. Please check the list and pick the most suitable topic for you. Moreover, you can also contact us to order customized topics free of cost.
How “The Research Guardian” Can Help You A lot!
Our top thesis writing experts are available 24/7 to assist you the right university projects. Whether its critical literature reviews to complete your PhD. or Master Levels thesis.
Cyber Threat Intelligence for the Enhancement of Early Warning and Response
To design the techniques to analyse and share threat intelligence for the improvement in early warning and responding abilities.
Objectives:
- To examine the methodologies for the collection and aggregation of data from different sources.
- To develop algorithms to analyse and prioritise threat intelligence for identifying new threats.
- To assess the effectiveness of cyber threat intelligence on different platforms along with their impact on the responding times and strategies.
Security of Software Development
To study the techniques necessary for the integration of security in the software development for the production of secure software applications.
- To investigate the coding techniques that are secure and best for the identification of common software problems.
- To design plans to incorporate security requirements, review codes and test application security during the development of software.
- To examine the importance of software development with security for preventing risks of data leaks and breaching of security.
Get Help from Expert Thesis Writers!
TheresearchGuardian.com providing expert thesis assistance for university students at any sort of level. Our thesis writing service has been serving students since 2011.
Security of Internet of Things (IoT)
To investigate the challenges related to security for developing solutions for the protection of devices data from cyber threats.
- To identify the exposure and attack routes to IoT networks and devices.
- To design protected protocols for the communication and authentication of the devices of IoT.
- To examine the importance of security solution of IoT for the prevention of unauthorized access and violations of privacy.
Machine learning for the Detection of advanced Persistent Threats
To investigate the importance of techniques of machine learning in the detection of persistent threats and cyber-attacks.
- To design the algorithms that can detect any kind of interruption or threat to protect the system.
- To assess the techniques for adversarial machine learning for the detection and prevention of threats.
- To examine the performance of the APT detection and mitigation systems based on machine learning.
Looking For Customize Thesis Topics?
Take a review of different varieties of thesis topics and samples from our website TheResearchGuardian.com on multiple subjects for every educational level.
Cloud Security for Privacy and Security of Data
To study the risks related to security for the protection of data and privacy in cloud computing environment.
- To identify the threats and vulnerabilities specifically for cloud services.
- To develop protection by enabling encryption and access control for the security of cloud storage systems.
- To examine the effectiveness of solutions related to cloud security in protecting data and privacy.
Protection of critical Infrastructure systems from Cyber threats
To study the challenges in cybersecurity and design approaches for the protection of critical infrastructure systems from cyber threats.
- To examine the risks linked with critical infrastructure systems and their dependence on each other.
- To design the system for the detection of threat or cyber-attack to prevent it from entering in critical infrastructure databases.
- To examine the resistance of critical infrastructure systems to cyber-attacks.
Healthcare Cybersecurity
To study the problems related to cybersecurity in healthcare systems to protect privacy and integrity of patients in medical devices and systems.
- To identify the risks in the IT systems of healthcare sector, the electronic health records and the devices used.
- To develop security protocols for communication and mechanisms for encryption for the safety of patient data.
- To assess the effectiveness of practices of cybersecurity in healthcare sector and its impact on the privacy and security of patients.
Security of Mobile Devices for the Protection of Data and Privacy of User
To study the development of strategies for the security of user data and privacy in mobile devices.
- To investigate the risks and vulnerabilities linked with mobile devices, applications and networks
- To design the mechanisms for the authentication, data encryption and security of practices for mobile applications development.
- To examine the efficiency of the solutions for the mobile security in the prevention of unauthorized data access and violations of privacy.
Cybersecurity for Social Engineering and Human Factors
To study the techniques of social engineering and human factors in cyber-attacks.
- To study the aspects of psychology of human behaviour that can encourage the acts of social engineering attacks.
- To develop programs for awareness training and interventions of security education for educating the users against social engineering.
- To assess the efficiency of the practices of security of users to minimize the social engineering attack incidents.
Governance and Policy of Cybersecurity
To investigate the governance and policy outcomes of cybersecurity.
- To assess the laws, standards and regulations of cybersecurity at national and international level.
- To examine the considerations related to ethics and implications of privacy of practices and policies of cybersecurity
- To analyse the efficiency of cybersecurity governance in the promotion of compliance, responsibility and risk management.
Let’s Secure Knowledge on Your Cyber Security Research!
Embark on your journey to becoming a Cyber Security research maven. Our research paper help services are your companions in conquering challenges, unearthing insights, and making a lasting impact in the world of Cyber Security thesis topics. Contact us now and join us in shaping a safer digital future today.
Meet Our Professionals Ranging From Renowned Universities
Related topics.
- Sports Management Research Topics
- Special Education Research Topics
- Software Engineering Research Topics
- Primary Education Research Topics
- Microbiology Research Topics
- Luxury Brand Research Topics
- Cyber Security Research Topics
- Commercial Law Research Topics
- Change Management Research Topics
- Artificial intelligence Research Topics
- SUGGESTED TOPICS
- The Magazine
- Newsletters
- Managing Yourself
- Managing Teams
- Work-life Balance
- The Big Idea
- Data & Visuals
- Reading Lists
- Case Selections
- HBR Learning
- Topic Feeds
- Account Settings
- Email Preferences
When Cyberattacks Are Inevitable, Focus on Cyber Resilience
- Keri Pearlson

Preparing for an attack that breaches your defenses is the best way to minimize the damage it can do.
Cybersecurity experts and the companies that employ need to let go of their prevention mindset and adopt one focused on resilience. A prevention mindset means doing all you can to keep the bad guys out. A resilience mindset adds a layer: while you do all you can to prevent an attack, you also work with the expectation that they still might break through your defenses and invest heavily preparing to respond and recover when the worst happens. Companies that have successfully built resilience have done a few things differently: built a culture of cybersecurity, prepared and practiced their responses to cyber attacks, embraced “secure by design” principles, and put in place communication processes so they can respond no matter what happens.
There’s a common — but serious — mistake cybersecurity experts make: they focus all their resources on keeping malicious actors out of our system. It’s an understandable misstep. Protecting ourselves from potential cyber breaches is a critical part of the job. Even so, it’s impossible to be completely protected from every vulnerability. That’s because the good guys must protect against every possible vulnerability, while the bad guys only need one small crack in a company’s armor to get in.
- KP Keri Pearlson is the executive director of the research consortium Cybersecurity at MIT Sloan (CAMS). Her research investigates organizational, strategic, management, and leadership issues in cybersecurity. Her current focus is on the board’s role in cybersecurity.
Partner Center

- Advanced Search
Automatic decision tree-based NIDPS ruleset generation for DoS/DDoS attacks
New citation alert added.
This alert has been successfully added and will be sent to:
You will be notified whenever a record that you have chosen has been cited.
To manage your alert preferences, click on the button below.
New Citation Alert!
Please log in to your account
Information & Contributors
Bibliometrics & citations, view options, graphical abstract, recommendations, machine learning combating dos and ddos attacks.
In recent years, technology is booming at a breakneck speed as so the need of security. Vulnerabilities in the layers of the OSI model and the networks are paving new ways for intruders and hackers to steal the confidential information. Security attacks ...
Dual-Level Attack Detection, Characterization and Response for Networks Under DDoS Attacks
DDoS attacks aim to deny legitimate users of the services. In this paper, the authors introduce dual-level attack detection D-LAD scheme for defending against the DDoS attacks. At higher and coarse level, the macroscopic level detectors MaLAD attempt to ...
Tracking DDoS attacks: insights into the business of disrupting the web
Known for a long time, Distributed Denial-of-Service (DDoS) attacks are still prevalent today and cause harm on the Internet on a daily basis. The main mechanism behind this kind of attacks is the use of so called botnets, i.e., networks of compromised ...
Information
Published in.
Elsevier Science Inc.
United States
Publication History
Author tags.
- Distributed denial of service
- Network-based intrusion detection prevention system
- Decision tree
- Suricata/snort
- Hyperparameter tuning
- Automatic rule generation
- Research-article
Contributors
Other metrics, bibliometrics, article metrics.
- 0 Total Citations
- 0 Total Downloads
- Downloads (Last 12 months) 0
- Downloads (Last 6 weeks) 0
View options
Login options.
Check if you have access through your login credentials or your institution to get full access on this article.
Full Access
Share this publication link.
Copying failed.
Share on social media
Affiliations, export citations.
- Please download or close your previous search result export first before starting a new bulk export. Preview is not available. By clicking download, a status dialog will open to start the export process. The process may take a few minutes but once it finishes a file will be downloadable from your browser. You may continue to browse the DL while the export process is in progress. Download
- Download citation
- Copy citation
We are preparing your search results for download ...
We will inform you here when the file is ready.
Your file of search results citations is now ready.
Your search export query has expired. Please try again.
Information
- Author Services
Initiatives
You are accessing a machine-readable page. In order to be human-readable, please install an RSS reader.
All articles published by MDPI are made immediately available worldwide under an open access license. No special permission is required to reuse all or part of the article published by MDPI, including figures and tables. For articles published under an open access Creative Common CC BY license, any part of the article may be reused without permission provided that the original article is clearly cited. For more information, please refer to https://www.mdpi.com/openaccess .
Feature papers represent the most advanced research with significant potential for high impact in the field. A Feature Paper should be a substantial original Article that involves several techniques or approaches, provides an outlook for future research directions and describes possible research applications.
Feature papers are submitted upon individual invitation or recommendation by the scientific editors and must receive positive feedback from the reviewers.
Editor’s Choice articles are based on recommendations by the scientific editors of MDPI journals from around the world. Editors select a small number of articles recently published in the journal that they believe will be particularly interesting to readers, or important in the respective research area. The aim is to provide a snapshot of some of the most exciting work published in the various research areas of the journal.
Original Submission Date Received: .
- Active Journals
- Find a Journal
- Proceedings Series
- For Authors
- For Reviewers
- For Editors
- For Librarians
- For Publishers
- For Societies
- For Conference Organizers
- Open Access Policy
- Institutional Open Access Program
- Special Issues Guidelines
- Editorial Process
- Research and Publication Ethics
- Article Processing Charges
- Testimonials
- Preprints.org
- SciProfiles
- Encyclopedia

Article Menu

- Subscribe SciFeed
- Recommended Articles
- Google Scholar
- on Google Scholar
- Table of Contents
Find support for a specific problem in the support section of our website.
Please let us know what you think of our products and services.
Visit our dedicated information section to learn more about MDPI.
JSmol Viewer
Research on power cyber-physical cross-domain attack paths based on graph knowledge.

1. Introduction
2. electric power cyber-physical coupling characteristics, 3. method for constructing attack graph of electric power cyber-physical fusion system, 3.1. define the attack graph.
- ∵ ∀ G ( V , A ) , V ≠ φ , A ≠ φ , leaf node ⇔ some kind of cyber-physical cross-domain attack, intermediate node ⇔ power secondary equipment node failure and transient stable node disturbance, root node ⇔ attack target. ∴ ∃ leaf node → a Its adjacent intermediate node or root node . d G + ( v ) , d G − ( v ) are proportional to the frequency with which vertex v is exploited by various cyber-physical cross-domain attack pathways, and b i , b j reflect the importance of nodes i, j in effective attack paths.
- ∃ leaf node → a Other leaf nodes or intermediate nodes or root nodes => condition 1 and condition 2 are true. The geodesic distance d i j reflects the sum of the minimum edge weights in the attack path. The shorter the geodesic distance, the higher the probability of successful attack.
3.2. Attack Graph Building Process
- b i is the betweenness of node i, which represents the ratio of the number of shortest paths passing through node i to the total number of shortest paths in the shortest path from leaf node j to attack target root node k of various attacks. The betweenness of a node is defined in Formula (3): b i = ∑ j ≠ k δ jk ( i ) δ j k (3) δ j k is the number of shortest paths from node j to node k, and δ jk ( i ) is the number of shortest paths from node j to node k passing through node i.
- I i + and I i − respectively represent the degree probability distribution of each vertex in the upper layer L l + 1 and lower layer L l − 1 of the set L layer corresponding to the vertex v i , as shown in Formula (4). In Formula (4), T ( L l + 1 ) and T ( L l − 1 ) represent the number of vertices contained in the L l + 1 and L l − 1 layers respectively. Here, the source set X is composed of all leaf nodes with in-degree 0, and the collection set Y is composed of all root nodes with out-degree 0. Therefore, I i − of the vertices in the source set X and I i + of the vertices in the sink set Y are 0. I i + = d G + ( v i ) T ( L l + 1 ) , I i − = d G − ( v i ) T ( L l − 1 ) (4)
- α i indicates whether vertex v i will trigger each vertex in vertex set L l + 1 under different external conditions, as shown in Formula (5): α i = ∑ k = 1 s P k ⋅ R k , ∑ k = 1 s p k = 1 , k ∈ [ 1 , s ] (5) where s is the total number of external condition categories, P k represents the occurrence probability of the kth external condition, and R k represents whether the attack path through vertex v i can affect the vertices in the next layer set L l + 1 when the kth external condition occurs. If it can have an impact, the value of R k is 1, otherwise it is 0. It is defined here that the v i value of each vertex in the collection Y is 1.
- β i represents the probability of the attack event represented by vertex v i occurring. β i calculation method can refer to the Bayesian network or Markov model method in [ 21 ] for calculation. Define β i of each vertex in the source set X to be 1.
- First, give the definition of edge weights. Let ∆ = ∆ s ∪ ∆ a represent the weight of the directed edge. Among them, ∆ s corresponds to the directed edge E s , which refers to the one-step transition probability from the previous node to the current node, indicating the probability of the current node occurring when the previous state satisfies the conditions, which is called the previous transition probability. ∆ a corresponds to the directed edge E a , which represents the probability that the current node reaches the subsequent node state, which is called the posterior transition probability here.
- Therefore, from the definition of edge weights in (1), it can be seen that in the attack graph of the power cyber-physical fusion system, the pre-transition probability of the leaf nodes representing various cyber-physical cross-domain attacks is consistent with the probability of occurrence of various attacks. The weight of the edge connected to the root node representing the attack target is consistent with the post-transition probability of the preceding node. The weight of the edge connected to the intermediate vertex is determined by the forward and backward transition probabilities of the vertex.
- Let the element ∆ s i j be the weight of the directed edge E s = ( a i , a j ), which represents the probability of node a j occurring if node a i is satisfied, Δ s i j = P ( a j | a i ) . The pre-transition probability and the post-transition probability of the edges connected to intermediate nodes such as control master station, measurement and control equipment failure, transient stable node disturbance, etc., will be affected by factors such as the node’s own functional attribute GN, the scene attribute CJ, and the edge JO between cyber-physical networks. The influence can be used as the basis for determining the weight value ∆ s of the directed edge.The directed edge weight can be defined as Formula (6). Δ s = 2 G N + C J + J O (6)
3.3. Cascading Failure Analysis
3.4. cascading fault vulnerability assessment indicators, 3.5. attack path hazard assessment, 4. experimental simulation analysis.
- It can be seen from Table 6 that each attack path conducts security risks across the cyber-physical space and can cause cascading failures of the power physical system. At the same time, the risk of attack paths propagating across space is related to the load rate of the power system, the average load rate of the line, and the line load fluctuation coefficient. When the system load rate is low, the three attack paths <v1,v10,v11,v17>, <v2,v5,v12,v17>, and <v2,v8,v15,v17> have very little load loss. The risk of cascading failure in the physical space system of the power grid is low. As the system load rate increases, the average line load rate and the line load fluctuation coefficient are important factors to measure the impact of each attack path on the cascading failure of the power grid’s physical space system. When the average load ratio of the line is 0.236, 0.246, and 0.319, the load loss of the physical space system of the power grid caused by the cross-space conduction of security risks through the attack path is small. The possibility of cascading failures in the physical space system of the power grid is unlikely. When the system load ratio is 0.787, 0.879, and 0.96, due to the large line load fluctuation coefficient, security risks are transmitted across space through various attack paths, causing high load losses in the physical space system of the power grid. Cyber-physical cross-domain attacks increase the possibility of cascading failures in the power grid’s physical space system. When the system load factor has little difference and takes values of 0.879 and 0.96, the average load factor of the line is 0.39 and 0.436, and the line load fluctuation coefficient is 1.6387 and 1.427. When the system load rate is relatively consistent, the average load rate of the line has a greater impact on the load loss of the power grid physical system caused by the cross-space propagation of security risks through various attack paths than the fluctuation coefficient of the line. The risk of cascading failures in the physical space system of the power grid caused by attacks is also relatively high.
- After the risk of cyber-physical cross-domain attacks is transmitted across space through various attack paths, the risk of cascading failures caused by different operating statuses of the power grid’s physical space system is also completely different. For example, when the system load ratio is 0.375 or 0.467, attack path 1 <v1,v10,v11,v17> has the largest load loss and the highest risk of cascading failures. It can be seen that after the protection equipment suffers a cyber-physical cross-domain attack, the risk of cascading failure caused by the failure of the power grid’s physical space system to respond to switching/speculative operation instructions in a timely manner is the greatest. As the system load rate increases, for example, when the system load rate is 0.525, 0.617, and 0.689, the load loss of attack path 3 <v2,v8,v15,v17> is the highest. That is, at this stage, the protection equipment settings are maliciously tampered with, and the risk of cascading failures caused by misoperation or refusal to operate the load switching operation is the greatest. When the system load rate continues to increase, for example, when the system load rate is 1.4478 or 1.6387, the attack path 2 <v2,v5,v12,v17> has the highest load loss. The attack causes the control device to issue wrong instructions, causing the power regulation parameters to be maliciously changed, resulting in the greatest risk of cascading failures.
- When the system load rate is low, such as 0.6896, as shown in Figure 6 , the overall cascading fault scale distribution of the power grid physical space system presents the characteristics of a ladder distribution. When a cascading failure of the same scale occurs in the physical space system of the power grid, the cyber-physical cross-domain attack risk is transmitted through the attack path 3 <v2,v8,v15,v17>, and the resulting loss of load in the physical space system of the power grid plays a dominant role.
- When the system load rate is high, such as 0.879, as shown in Figure 7 and Figure 8 , under the same system load rate, the physical space system load loss situation tends to be consistent. After cyber-physical cross-domain attack risks are transmitted across space through different attack paths, the probability of causing cascading failures of the same scale is basically the same. The figure shows that there are jump points at the end of the power grid physical space system load loss distribution chart, indicating that when the cascading failure of the physical space system develops to a certain scale, the entire network will collapse. This is determined by the network scale and structure of the system. For this simulation system, the internal lines and transmission sections of the two interconnected subsystems will be affected by the disconnection of certain lines, causing a large-scale collapse of the power physical system.
5. Discussion
6. conclusions, author contributions, institutional review board statement, informed consent statement, data availability statement, conflicts of interest.
- Liang, G.; Zhao, J.; Luo, F.; Weller, S.R.; Dong, Z.Y. A Review of False Data Injection Attacks Against Modern Power Systems. IEEE Trans. Smart Grid 2016 , 8 , 1630–1638. [ Google Scholar ] [ CrossRef ]
- Soltan, S.; Mihalis, Y.; Gil, Z. REACT to cyber attacks on power grids. IEEE Trans. Netw. Sci. Eng. 2018 , 6 , 459–473. [ Google Scholar ] [ CrossRef ]
- Dai, Q.; Shi, L.; Ni, Y. Risk Assessment for Cyberattack in Active Distribution Systems Considering the Role of Feeder Automation. IEEE Trans. Power Syst. 2019 , 34 , 3230–3240. [ Google Scholar ] [ CrossRef ]
- Cai, X.; Wang, Q.; Tang, Y.; Zhu, L. Review of Cyber-attacks and Defense Research on Cyber Physical Power System. In Proceedings of the 2019 IEEE Sustainable Power and Energy Conference (iSPEC), Beijing, China, 21–23 November 2019; pp. 487–492. [ Google Scholar ] [ CrossRef ]
- Ou, X.; Boyer, W.F.; McQueen, M.A. A scalable approach to attack graph generation. In Proceedings of the 13th ACM conference on Computer and communications security, Alexandria, VA, USA, 30 October–3 November 2006; pp. 336–345. [ Google Scholar ]
- Liu, X. A network attack path prediction method using attack graph. J. Ambient. Intell. Humaniz. Comput. 2020 , 1–8. [ Google Scholar ] [ CrossRef ]
- Nadeem, A.; Verwer, S.; Moskal, S.; Yang, S.J. Alert-driven attack graph generation using s-pdfa. IEEE Trans. Dependable Secur. Comput. 2021 , 19 , 731–746. [ Google Scholar ] [ CrossRef ]
- Lippmann, R.P.; Ingols, K.W. An Annotated Review of Past Papers on Attack Graphs ; Citeseer: Princeton, NJ, USA, 2005. [ Google Scholar ]
- Sun, L.; Dou, Y.; Yang, C.; Zhang, K.; Wang, J.; Philip, S.Y.; Li, B. Adversarial attack and defense on graph data: A survey. IEEE Trans. Knowl. Data Eng. 2022 , 35 , 7693–7711. [ Google Scholar ] [ CrossRef ]
- Wang, L.; Singhal, A.; Jajodia, S. Measuring the overall security of network configurations using attack graphs. In IFIP Annual Conference on Data and Applications Security and Privacy ; Springer: Berlin/Heidelberg, Germany, 2007; pp. 98–112. [ Google Scholar ]
- Noel, S.; Jajodia, S.; Wang, L.; Singhal, A. Measuring security risk of networks using attack graphs. Int. J. Next-Gener. Comput. 2010 , 1 , 135–147. [ Google Scholar ]
- Sun, X.; Dai, J.; Liu, P.; Singhal, A.; Yen, J. Using Bayesian Networks for Probabilistic Identification of Zero-Day Attack Paths. IEEE Trans. Inf. Forensics Secur. 2018 , 13 , 2506–2521. [ Google Scholar ] [ CrossRef ]
- Kavallieratos, G.; Katsikas, S. Attack path analysis for cyber physical systems. In Proceedings of the Computer Security: ESORICS 2020 International Workshops, CyberICPS, SECPRE, and ADIoT, Guildford, UK, 14–18 September 2020; Revised Selected Papers 6. Springer International Publishing: Berlin/Heidelberg, Germany, 2020; pp. 19–33. [ Google Scholar ]
- Dai, F.; Hu, Y.; Zheng, K.; Wu, B. Exploring risk flow attack graph for security risk assessment. IET Inf. Secur. 2015 , 9 , 344–353. [ Google Scholar ] [ CrossRef ]
- Chen, L.; Yue, D.; Dou, C.; Chen, J.; Cheng, Z. Study on attack paths of cyber attack in cyber-physical power systems. IET Gener. Transm. Distrib. 2020 , 14 , 2352–2360. [ Google Scholar ] [ CrossRef ]
- Wang, B.; Gong, N.Z. Attacking graph-based classification via manipulating the graph structure. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security, London, UK, 11–15 November 2019; pp. 2023–2040. [ Google Scholar ]
- Starke, A.; Nagaraj, K.; Ruben, C.; Aljohani, N.; Zou, S.; Bretas, A.; Zare, A. Cross-layered distributed data-driven framework for enhanced smart grid cyber-physical security. IET Smart Grid 2022 , 5 , 398–416. [ Google Scholar ] [ CrossRef ]
- Qiu, S.; Fei, J.; Wang, J. Cross-Space Conduction Assessment Method of Network Attack Risk under the Strong Coupling Characteristics of Electric Power Cyber Physics. IET Inf. Secur. 2023 , 2023 , 9006166. [ Google Scholar ] [ CrossRef ]
- Schneier, B. Attack trees. Dr. Dobb’s J. 1999 , 24 , 21–29. [ Google Scholar ]
- Kaynar, K.; Sivrikaya, F. Distributed attack graph generation. IEEE Trans. Dependable Secur. Comput. 2015 , 13 , 519–532. [ Google Scholar ] [ CrossRef ]
- Zhang, Y.; Xiang, Y.; Wang, L. Power system reliability assessment incorporating cyber attacks against wind farm energy management systems. IEEE Trans. Smart Grid 2016 , 8 , 2343–2357. [ Google Scholar ] [ CrossRef ]
- Guo, H.; Zheng, C.; Iu, H.H.C.; Fernando, T. A critical review of cascading failure analysis and modeling of power system. Renew. Sustain. Energy Rev. 2017 , 80 , 9–22. [ Google Scholar ] [ CrossRef ]
- Song, J.; Cotilla-Sanchez, E.; Ghanavati, G.; Hines, P.D. Dynamic modeling of cascading failure in power systems. IEEE Trans. Power Syst. 2015 , 31 , 2085–2095. [ Google Scholar ] [ CrossRef ]
- Yang, Y.; Motter, A.E. Cascading failures as continuous phase-space transitions. Phys. Rev. Lett. 2017 , 119 , 248302. [ Google Scholar ] [ CrossRef ] [ PubMed ]
- Zeng, J.; Wu, S.; Chen, Y.; Zeng, R.; Wu, C. Survey of attack graph analysis methods from the perspective of data and knowledge processing. Secur. Commun. Netw. 2019 , 2019 , 1–16. [ Google Scholar ] [ CrossRef ]
- Tomasson, E.; Söder, L. Improved importance sampling for reliability evaluation of composite power systems. IEEE Trans. Power Syst. 2016 , 32 , 2426–2434. [ Google Scholar ] [ CrossRef ]
- Grigg, C.; Wong, P.; Albrecht, P.; Allan, R.; Bhavaraju, M.; Bilinton, R.; Chen, Q.; Fong, C.; Haddad, S.; Hurguanty, S.; et al. The IEEE reliability test system-1996. A report prepared by the reliability test system task force of the application of probability methods subcommittee. IEEE Trans. Power Syst. 1999 , 14 , 1010–1020. [ Google Scholar ] [ CrossRef ]
- Subcommittee, P.M. IEEE reliability test system. IEEE Trans. Power Appar. Syst. 1979 , 6 , 2047–2054. [ Google Scholar ] [ CrossRef ]
Click here to enlarge figure
| Index | Comprehensive Assessment | ||
|---|---|---|---|
| Attack impact | GN | Constant value, 0.257, interval fixed value, 0.598, flexible fixed value, 0.892. | 2GN + CJ + JO |
| CJ | Control, 0.327, acquisition, 0.654, transparent transmission, 0.132. | ||
| JO | One-to-many, 0.172, many-to-one, 0.814, many-to-many, 0.743. | ||
| Number of fault occurrences | Less than 7 times a week | 0.2 | |
| Less than 15 times a week | 0.5 | ||
| More than 21 times a week | 0.7 | ||
| Levels | Vertices | Vertex Objects |
|---|---|---|
| L1 | v1 | Resource exhaustion attack |
| v2 | Exploitation attack | |
| L2 | v3 | Measuring instrument measurement deviation |
| v4 | Control system error action | |
| v5 | Control and signaling devices issue incorrect instructions | |
| v6 | Control and signaling devices refuse to execute instructions | |
| v7 | Control and signaling equipment out of service | |
| v8 | Protection equipment setting value modification—malfunction | |
| v9 | Protection equipment setting value modification-refuse to move | |
| v10 | Protection equipment stops operating | |
| L3 | v11 | Generator connected to the grid or off-grid |
| v12 | Adjust power operating parameters | |
| v13 | Close/open power transmission and transformation equipment | |
| v14 | Adjust operating parameters of power transmission equipment | |
| v15 | Load switching | |
| v16 | Load regulation operating parameters | |
| L4 | v17 | Physical space system cascading failures |
| Vertex | Level | ||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| v1 | L1 | 4 | 0 | 0.5 | 0 | 1 | 1 | 0.4 | 0.2 | v10 | L2 | 3 | 1 | 0.5 | 0.17 | p | 1 | 0.075 | 0.05p |
| v2 | L1 | 4 | 0 | 0.5 | 0 | 1 | 1 | 0.6 | 0.3 | v11 | L3 | 1 | 8 | 1 | 1 | 1 | 1 | 0.2 | 0.4 |
| v3 | L2 | 1 | 1 | 0.17 | 0.5 | 1 | 1 | 0.025 | 0.02 | v12 | L3 | 1 | 6 | 1 | 0.75 | 1 | 1 | 0.15 | 0.26 |
| v4 | L2 | 6 | 1 | 1 | 0.17 | 1 | 1 | 0.15 | 0.18 | v13 | L3 | 1 | 7 | 1 | 0.88 | 1 | 1 | 0.175 | 0.33 |
| v5 | L2 | 6 | 1 | 1 | 0.17 | p | 1 | 0.15 | 0.18 p | v14 | L3 | 1 | 6 | 1 | 0.75 | 1 | 1 | 0.15 | 0.26 |
| v6 | L2 | 6 | 1 | 1 | 0.17 | p | 1 | 0.15 | 0.18 p | v15 | L3 | 1 | 7 | 1 | 0.88 | 1 | 1 | 0.15 | 0.28 |
| v7 | L2 | 6 | 1 | 1 | 0.17 | 1 | 1 | 0.15 | 0.18 | v16 | L3 | 1 | 6 | 1 | 0.75 | 1 | 1 | 0.15 | 0.26 |
| v8 | L2 | 6 | 1 | 1 | 0.17 | 1 | 1 | 0.15 | 0.18 | v17 | L4 | 0 | 0 | 0 | 0 | 1 | 1 | 1 | 0 |
| v9 | L2 | 6 | 1 | 1 | 0.17 | p | 1 | 0.15 | 0.18 p | / | / | / | / | / | / | / | / | / | / |
| Attack Path | Risk | Attack Path | Risk | Attack Path | Risk | Attack Path | Risk |
|---|---|---|---|---|---|---|---|
| <v1,v3,v11,v17> | 2.73 p | <v1,v7,v14,v17> | 2.85 p | <v2,v4,v15,v17> | 2.68 | <v2,v8,v13,v17> | 1.62 p |
| <v1,v6,v11,v17> | 2.73 p | <v1,v7,v15,v17> | 3.71 p | <v2,v4,v16,v17> | 2.11 | <v2,v8,v14,v17> | 2.11 p |
| <v1,v6,v12,v17> | 2.97 p | <v1,v7,v16,v17> | 2.84 p | <v2,v5,v11,v17> | 2.68 | <v2,v8,v15,v17> | 1.62 p |
| <v1,v6,v13,v17> | 1.66 | <v1,v10,v11,v17> | 3.9 p | <v2,v5,v12,v17> | 2.11 | <v2,v8,v16,v17> | 2.28 p |
| <v1,v6,v14,v17> | 1.66 | <v1,v10,v13,v17> | 2.85 p | <v2,v5,v13,v17> | 3.12 | <v2,v9,v11,v17> | 1.62 p |
| <v1,v6,v15,v17> | 1.9 | <v1,v10,v15,v17> | 3.71 p | <v2,v5,v14,v17> | 2.33 | <v2,v9,v12,v17> | 2.11 p |
| <v1,v6,v16,v17> | 1.77 | <v2,v4,v11,v17> | 2.84 p | <v2,v5,v15,v17> | 2.49 | <v2,v9,v13,v17> | 1.63 p |
| <v1,v7,v11,v17> | 1.86 | <v2,v4,v12,v17> | 3.71 p | <v2,v5,v16,v17> | 1.59 p | <v2,v9,v14,v17> | 2.11 p |
| <v1,v7,v12,v17> | 2.51 p | <v2,v4,v13,v17> | 2.85 p | <v2,v8,v11,v17> | 1.59 p | <v2,v9,v15,v17> | 1.62 p |
| <v1,v7,v13,v17> | 3.63 p | <v2,v4,v14,v17> | 2.21 | <v2,v8,v12,v17> | 1.78 p | <v2,v9,v16,v17> | 2.28 p |
| Number | Attack Path | Risk | Attack Process Description | System Status |
|---|---|---|---|---|
| 1 | <v1,v10,v11,v17> | 3.9 p | The protection equipment was attacked and shut down, and the power cutoff action did not take effect in time. | Cascading failures |
| 2 | <v2,v5,v12,v17> | 2.11 | The attack control device issues erroneous instructions, causing malicious changes in power supply adjustment parameters. | Overvoltage |
| 3 | <v2,v8,v15,v17> | 1.62 p | The setting value of the protection equipment has been maliciously tampered with, and the load switching operation malfunctions or refuses to operate. | Load fluctuation |
| Total Load/MW | Load Rate | Line Average Load Rate | Line Load Fluctuation Coefficient | Attack Path 1 Load Loss/MW | Attack Path 2 Load Loss/MW | Attack Path 3 Load Loss/MW |
|---|---|---|---|---|---|---|
| 1070 | 0.375 | 0.259 | 1.132 | 0.2384 | 0.0787 | 0.0001 |
| 1330 | 0.467 | 0.237 | 0.9707 | 0.1579 | 0.0201 | 0.0137 |
| 1496 | 0.525 | 0.232 | 1.4775 | 0.296 | 2.7159 | 1.9685 |
| 1761 | 0.617 | 0.236 | 1.2631 | 0.5435 | 0.6402 | 0.932 |
| 1965 | 0.689 | 0.246 | 1.3751 | 0.8876 | 0.8923 | 1.026 |
| 2245 | 0.787 | 0.319 | 1.4478 | 0.899 | 0.7995 | 1.33 |
| 2506 | 0.879 | 0.39 | 1.6387 | 8.382 | 9.878 | 9.759 |
| 2736 | 0.96 | 0.436 | 1.427 | 21.496 | 28.74 | 21.07 |
| 2850 | 1 | 0.33 | 1.238 | 3.8166 | 1.866 | 0.816 |
| 3050 | 1.07 | 0.305 | 0.9611 | 0.5917 | 0.481 | 0.5714 |
| 3310 | 1.161 | 0.39 | 1.2582 | 4.64 | 4.357 | 5.862 |
| Attack Path 1 | Attack Path 2 | Attack Path 3 | |||
|---|---|---|---|---|---|
| Line | Line Disconnect Times | Line | Line Disconnect Times | Line | Line Disconnect Times |
| 10–11 | 213 | 10–12 | 227 | 3–24 | 232 |
| 10–12 | 189 | 10–11 | 120 | 10–11 | 146 |
| 3–24 | 110 | 3–24 | 128 | 10–12 | 126 |
| 4–9 | 86 | 9–11 | 64 | 9–11 | 87 |
| 6–10 | 77 | 9–12 | 47 | 9–12 | 37 |
| 5–10 | 76 | 4–9 | 39 | 6–10 | 20 |
| 9–11 | 55 | 1–2 | 29 | 21–22 | 19 |
| 9–12 | 34 | 1–3 | 20 | 1–3 | 16 |
| 13–23 | 18 | 12–13 | 17 | 8–10 | 15 |
| 17–22 | 17 | 5–10 | 16 | 14–16 | 15 |
| The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
Share and Cite
Qiu, S.; Shao, Z.; Wang, J.; Xu, S.; Fei, J. Research on Power Cyber-Physical Cross-Domain Attack Paths Based on Graph Knowledge. Appl. Sci. 2024 , 14 , 6189. https://doi.org/10.3390/app14146189
Qiu S, Shao Z, Wang J, Xu S, Fei J. Research on Power Cyber-Physical Cross-Domain Attack Paths Based on Graph Knowledge. Applied Sciences . 2024; 14(14):6189. https://doi.org/10.3390/app14146189
Qiu, Shenjian, Zhipeng Shao, Jian Wang, Shiyou Xu, and Jiaxuan Fei. 2024. "Research on Power Cyber-Physical Cross-Domain Attack Paths Based on Graph Knowledge" Applied Sciences 14, no. 14: 6189. https://doi.org/10.3390/app14146189
Article Metrics
Article access statistics, further information, mdpi initiatives, follow mdpi.

Subscribe to receive issue release notifications and newsletters from MDPI journals
- Choose your language...
- English (English)
- Spanish (Español)
- French (Français)
- German (Deutsch)
- Italian (Italiano)
- Portuguese (Português)
- Japanese (日本語)
- Chinese (中文)
- Korean (한국어)
- Taiwan (繁體中文)
- Organization Size
- Hybrid Cloud
- Zero Trust & Least Privilege
- Developer Security & Operations
- IoT Security Solutions
- Anti-Ransomware

See how use cases come to life through Check Point's customer stories.
- Financial Services
- Federal Government
- State & Local Government
- Telco Service Provider
- Small & Medium Business
- Infinity Platform
- Secure the Network
- Secure the Cloud
- Secure the Workspace
- Security Operations and AI
- Platform Overview
- Infinity Core Services
- Infinity Portal Access Infinity Portal
- Infinity Platform Agreement Predictable cyber-security environments through a platform agreement

AI-Powered Threat Prevention
- Next Generation Firewall (NGFW) Security Gateway Industry-leading AI powered security gateways for modern enterprises
- SD-WAN Software Defined Wide Area networks converging security with networking
- Security Policy and Threat Management Manage firewall and security policy on a unified platform for on-premises and cloud networks
- Operational Technology and Internet of Things (IoT) Autonomous IoT/OT threat prevention with zero-trust profiling, virtual patching and segmentation
- Remote Access VPN Secure, seamless remote access to corporate networks
- Cloud Network Security Industry-leading threat prevention through cloud-native firewalls
- Cloud Native Application Protection Platform Cloud native prevention first security
- Code Security Developer centric code security
- Web Application and API Security Automated application and API security
- Email and Collaboration Security Email security including office & collaboration apps
- Endpoint Security Comprehensive endpoint protection to prevent attacks & data compromise
- Mobile Security Complete protection for the mobile workforce across all mobile devices
- SASE Unifying security with optimized internet and network connectivity
- Managed Prevention & Response Service SOC operations as a service with Infinty MDR/MPR
- Extended Prevention & Response AI-Powered, Cloud-Delivered Security Operations with Infinity XDR/XPR
- Secure Automation and Collaboration Automate response playbooks with Infinity Playblocks
- Unified Security Events and Logs as a Service Infinity Events cloud-based analysis, monitoring and reporting
- AI Powered Teammate Automated Security Admin & Incident Response with AI Copilot
- ThreatCloud AI The Brain behind Check Point’s threat prevention
- Cyber Security Risk Assessment Assess cyber security maturity and plan actionable goals
- Penetration Testing Evaluate security defenses against potential cyber attacks and threats
- Security Controls Gap Analysis (NIST CIST) Analyze technology gaps and plan solutions for improved security and ROI
- Threat Intelligence Analyzed data on cyber threats, aiding proactive security measures
- See All Infinity Global Services >

Learn hackers inside secrets and beat them at their own game
- Security Deployment & Optimization Strategic deployment and refinement of security for optimal protection
- Advanced Technical Account Management Proactive service delivered by highly skilled Cyber Security professionals
- Lifecycle Management Services Effectively maintain the lifecycle of security products and services
- Certifications & Accreditations Comprehensive cyber security training and certification programs
- CISO Training Globally recognized training for Chief Information Security Officers
- Security Awareness Empower employees with cyber security skills for work and home
- Cyber Range Simulated gamification environment for security training
- Mind Check Point Cyber Security and Awareness Programs training hub
- Incident Response Manage and mitigate security incidents with systematic response services
- Managed Detection and Response Prioritize prevention, delivering comprehensive SOC operations as a service
- Digital Forensics Comprehensive investigation and analysis of cyber incidents and attacks
- MXDR with Managed SIEM
- Managed Firewalls
- EDR with Agent Management
- Managed CNAPP
- Managed CSPM
- Support Programs Programs designed to help maximize security technology utilization
- Check Point PRO Proactive monitoring of infrastructure program offerings
- Contact Support
- Infinity Portal
- Infinity Platform Agreement
- Next Generation Firewall (NGFW) Security Gateway
- Security Policy and Threat Management
- Operational Technology and Internet of Things (IoT)
- Remote Access VPN
- Cloud Network Security
- Cloud Native Application Protection Platform
- Code Security
- Web Application and API Security
- Email and Collaboration Security
- Endpoint Security
- Mobile Security
- Managed Prevention & Response Service
- Extended Prevention & Response
- Secure Automation and Collaboration
- Unified Security Events and Logs as a Service
- AI Powered Teammate
- ThreatCloud AI
- Cyber Security Risk Assessment
- Penetration Testing
- Security Controls Gap Analysis (NIST CIST)
- Threat Intelligence
- Security Deployment & Optimization
- Advanced Technical Account Management
- Lifecycle Management Services
- Certifications & Accreditations
- CISO Training
- Security Awareness
- Cyber Range
- Incident Response
- Managed Detection and Response
- Digital Forensics
- Support Programs
- Check Point PRO
- Find a Partner
- Channel Partners
- Technology Partners
- MSSP Partners
- Azure Cloud
- Partner Portal

Check Point is 100% Channel. Grow Your Business with Us!
- Investor Relations
- Resource Center
- Customer Stories
- Events & Webinars
- Check Point Research
- Cyber Talk for Executives
- CheckMates Community

Check Point Research Reports Highest Increase of Global Cyber Attacks seen in last two years – a 30% Increase in Q2 2024 Global Cyber Attacks

Check Point Research (CPR) releases new data on Q2 2024 cyber attack trends. The data is segmented by global volume, industry and geography. These cyber attack numbers were driven by a variety of reasons, ranging from the continued increase in digital transformation and the growing sophistication of cybercriminals using advanced techniques like AI and machine learning. Economic motivation for income from attacks like ransomware and phishing as well as attacks fueled by geopolitical tensions and supply chain vulnerabilities continues to heavily impact this rise in the numbers.
This increase in global cyberattacks also stems from hacker interest in Education and Research, which saw the largest increase in cyber attacks in Q2 2024, when compared to all other industries. CPR warns that these factors can continue to accelerate the number of cyber attacks in 2024, driving the need for robust cyber security across all industries.
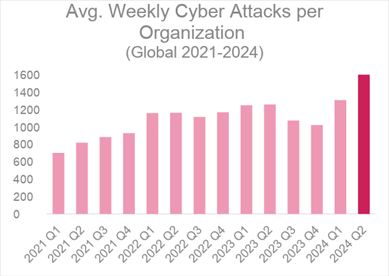
Key Statistics:
- In Q2 2024, Check Point Research saw a 30% YoY increase in cyber attacks globally, reaching 1,636 attacks per organization per week.
- Top 3 most attacked industries were Education/Research (3,341 attacks per week), Government/Military (2,084 attacks per week) and Healthcare (1,999 attacks per week).
- Latin America, (+53%), Africa (+37%), and Europe (+35%) showed the largest increases in cyber attacks in Q2 2024, compared YoY.
- Africa experienced the highest volume of attacks with 2,960 weekly attacks per organization, followed by Latin America with 2,667 weekly attacks per organization.
- North America accounted for 58% of publicly extorted ransomware attacks victims. The Manufacturing sector represented 29% of the published ransomware victims globally, marking a 56% year-over-year increase.
Cyber-attacks are increasing world-wide, with a 30% increase in weekly attacks on corporate networks in in Q2 2024 compared to Q2 2023, and a 25% rise compared to Q1 2024 . With an average of 1,636 attacks per organization per week, the relentless onslaught of attacks underscores the growing sophistication and persistence of threat actors. Several cyber threat trends are all happening at once.
For instance, the education and research industry has consistently been a prime target for cyber criminals due to its wealth of sensitive information and often inadequate cyber security measures made further complex by multiple groups of online users within and outside of the network expanding the attack vector surface. In fact, the education/research sector was the number one most attacked industry globally, seeing a 53% increase in Q2 2024 compared to Q2 2023, with an average of 3,341 attacks per organization every week.
Government/Military was the second most attacked sector with 2,084 attacks per week, reflecting the high stakes involved in state-level cyber espionage and disruption.
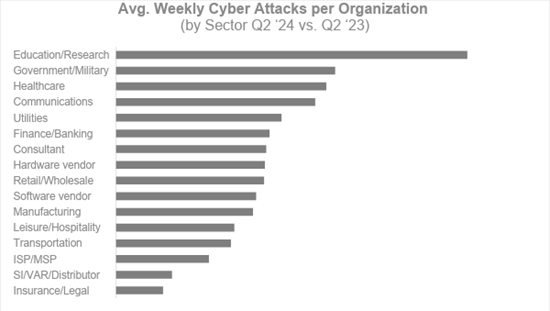
Looking back at cyber attacks for the Healthcare sector in Q2, healthcare organizations saw an average of 1,999 weekly attacks per organization, which was 15% higher than last year. Hackers like to target hospitals because they perceive them as short on cyber security resources with smaller hospitals particularly vulnerable, as they are underfunded and understaffed to handle a sophisticated cyber attack.
Ranking third out of all sectors for the most cyber attacks globally, healthcare is so lucrative to hackers because they aim to retrieve health insurance information, medical records numbers and, sometimes, even social security numbers.
Furthermore, the Hardware Vendor industry experienced largest increase in attacks, with a dramatic rise of 183%. This surge underscores the expanding target range of cyber criminals as they seek to exploit vulnerabilities across various sectors.
Regional Analysis of Cyber Attacks
Regionally, Africa experienced the highest average weekly cyber attacks per organization in Q2 2024 , with an average of 2,960 attacks, marking a 37% increase compared to the same period in 2023. Latin America saw the most significant rise, with attacks increasing by 53% year-over-year to an average of 2,667 per week. The Asia-Pacific (APAC) region followed with a 23% increase, highlighting the global spread of cyber threats.
| Africa | 2960 | +37% |
| Latin America | 2667 | +53% |
| APAC | 2510 | +23% |
| Europe | 1367 | +35% |
| North America | 1188 | +17% |
Ransomware Attacks per Region and Industry
In Q2 2024, ransomware attacks that involved public extortion were reported showing a 13% year-over-year increase, totaling approximately 1,200 incidents. North America was the hardest hit, comprising 58% of all reported ransomware attacks, despite a slight 3% decrease from the previous year. Europe experienced 19% of the incidents, marking a notable 28% decrease, while the APAC region saw the largest increase with a 38% surge, accounting for 16% of the attacks.
| North America | 58% | -3% |
| Europe | 19% | -28% |
| APAC | 16% | +38% |
| Latin America | 6% | +1% |
| Africa | 1% | -55% |
In terms of industry impact, the Manufacturing sector was the most affected, representing 29% of publicly extorted ransomware attacks’ victims globally, with a significant 56% year-over-year increase. The Healthcare sector followed, accounting for 11% of the attacks and experiencing a 27% increase. The Retail/Wholesale industry saw 9% of the attacks, with a notable 34% decrease from the previous year. Notably, the Communications and Utilities sectors experienced dramatic rises in ransomware incidents, with increases of 177% and 186%, respectively.
| Manufacturing | 29% | +56% |
| Healthcare | 11% | +27% |
| Retail/Wholesale | 9% | -34% |
| Finance/Banking | 7% | -8% |
| Education/Research | 6% | -3% |
| Software vendor | 6% | -57% |
| Government/Military | 6% | +31% |
| Transportation | 6% | +40% |
| Insurance/Legal | 5% | -25% |
| Communications | 5% | +177% |
| Leisure/Hospitality | 3% | +0% |
| Consultant | 2% | -76% |
| Utilities | 2% | +186% |
| Energy | 1% | -25% |
(*) This data draws from ransomware “shame sites” operated by double-extortion ransomware groups, which publicly disclose victim information. While these sources have inherent biases, they provide valuable insights into the ransomware landscape.
Tips for Prevention and Mitigation
Organizations must take proactive steps to safeguard their data and systems. Here are some strategies inspired by best practices from Check Point Software:
- Enhance Security Posture : Regularly update and patch systems to close vulnerabilities. Multi-layered security measures, including firewalls and endpoint protection, are essential.
- Employee Training and Awareness : Regular training sessions can educate employees about the latest cyber threats and phishing tactics, fostering a culture of vigilance.
- Advanced Threat Prevention : Utilize technologies such as sandboxing and anti-ransomware tools to detect and block sophisticated attacks.
- Adopt Zero Trust Architecture : Implement strict identity verification for every person and device attempting to access network resources.
- Regular Backups and Incident Response Planning : Ensure regular backups of critical data and develop comprehensive incident response plans to quickly address and mitigate the impact of attacks.
- Network Segmentation : Isolate critical systems to limit the spread of attacks and protect sensitive information.
- Vulnerability Management : Conduct regular vulnerability assessments and penetration testing, prioritizing remediation efforts based on potential impact.
The dramatic rise in cyber-attacks globally, particularly ransomware incidents, signals an urgent need for robust cyber security frameworks. Organizations must prioritize cyber security, adopting customized strategies to effectively combat the evolving threat landscape. By implementing advanced security measures, fostering a culture of awareness, and preparing for potential incidents, businesses can better defend against the relentless tide of cyber threats. The time to act is now, before the next wave of attacks strikes.
You may also like

MuddyWater Threat Group Deploys New BugSleep Backdoor

June 2024’s Most Wanted Malware: RansomHub Takes Top Spot as Most Prevalent Ransomware Group in Wake of LockBit3 Decline
Cpr warns threat actors are leveraging internet explorer in new zero-day spoofing attack (cve-2024-38112), cve-2024-6387 – regresshion remote code execution vulnerability seen in openssh.
Project 2025 Explained: What To Know About The Controversial Right-Wing Policy Map For Trump—As He Speaks At RNC
- Share to Facebook
- Share to Twitter
- Share to Linkedin
Former President Donald Trump will speak at the Republican National Convention on Thursday after he formally clinched the party’s nomination , bringing renewed attention to Project 2025, a conservative think tank’s wide-ranging blueprint for a potential second Trump term that covers everything from recruiting like-minded personnel to eliminating entire agencies—a platform assembled partly by ex-Trump staffers, though the former president has tried to distance himself.
Then-President Donald Trump gives a speech at the Heritage Foundation's President's Club Meeting on ... [+] October 17, 2017, in Washington D.C.
Project 2025, spearheaded by the Heritage Foundation with help from more than 100 other conservative groups , is a multi-part plan for the next conservative administration—namely a Trump presidency—which includes a LinkedIn-style database for presidential personnel hopefuls, training programs for executive branch positions and an as-yet-unreleased “playbook” laying out what Trump should do in his first 180 days.
Though the project is led by the Heritage Foundation and other private third-party groups and is not formally tied to Trump, who has tried to distance himself from the operation, its proposals were developed in part by former members of his administration and other Trump allies, and the ex-president has previously praised Heritage for its policy work.
The project has drawn the most attention for its “Mandate for Leadership,” a 900-page proposed policy agenda that describes itself as a “plan to unite the conservative movement and the American people against elite rule and woke culture warriors,” laying out plans for all aspects of the executive branch.
Personnel: Project 2025 broadly proposes to insert far more political appointees who are ideologically aligned with the president into the executive branch—replacing many of the nonpartisan career civil servants who serve in it now—proposing an executive order that would put political appointees into any “confidential, policy-determining, policymaking, or policy-advocating positions” (which Trump previously did at the end of his presidency, but President Joe Biden then overturned it).
Federal Agencies: It proposes a scaled-down federal government, including the abolishment of multiple agencies—including the Department of Education, Department of Homeland Security, National Oceanic and Atmospheric Administration and Consumer Financial Protection Bureau—whose remaining departments would be folded into other agencies or privatized, including the Transportation Security Administration.
Transgender Rights: Transgender rights and gender identity beyond biological sex are roundly rejected, with such steps as reinstating the ban on transgender Americans serving in the military, prohibiting public school educators from referring to students by anything other than their birth name and pronouns without parental permission, and ensuring no federal funds are used to provide gender-affirming care.
DEI and LGBTQ Rights: Project 2025 seeks to eliminate diversity, equity and inclusion programs from throughout the federal government and in universities, and while it doesn’t outlaw same-sex marriage, it supports “nuclear families” that include a “married mother, father, and their children,” and calls for restricting laws that bar discrimination on the basis of sex to exclude sexual orientation and gender identity.
Climate Change: The proposal would undo much of the federal government’s climate work, including by leaving the Paris Climate Agreement, overhauling the Department of Energy to promote oil and natural gas and deemphasize green energy sources, removing the Department of Agriculture’s focus on sustainability and curtailing climate research.
Abortion: While Project 2025 doesn’t explicitly call for an abortion ban, it would take many steps to restrict the procedure, including directing the Food and Drug Administration to revoke its approval of abortion drug mifepristone, using the Comstock Act to block any abortion equipment or medication from being mailed—which abortion rights advocates have said would be a “backdoor” way to ban abortion—barring federal funds being used to provide healthcare coverage for abortion and requiring states to report all abortions that take place there to the federal government.
Education: Project 2025 emphasizes a “school choice” policy that directs public funds to be used for students to attend private or religious schools, bars “critical race theory” from being taught in federally funded schools and advocates for legislation that would allow parents to sue schools they feel have acted improperly—such as by teaching controversial subjects or requiring students to disclose information about their religious beliefs.
Student Loans: Student loan relief efforts would come to an end—including the public service loan forgiveness program and income-driven repayment plans—as the proposal states “borrowers should be expected to repay their loans.”
Big Tech: TikTok would be banned, and the proposal calls for reforming Section 230 —which shields tech companies and social media networks from being sued over content on their platforms—and allowing laws like those passed in Florida and Texas that seek to punish social media companies who ban or suspend users based on their “viewpoints.”
Justice Department: Project 2025 calls for a “top-to-bottom overhaul” of the DOJ and FBI that gets rid of what it calls an “unaccountable bureaucratic managerial class and radical Left ideologues,” proposing an agency that would be more focused on violent crime and filing litigation that’s “consistent with the President’s agenda” and filled with far more political appointees; it also proposes prohibiting the FBI from investigating misinformation or making “politically motivated” moves against U.S. citizens.
Taxes: Project 2025 would seek to get rid of current tax rates and most deductions and credits, instead proposing a 15% rate for anyone under the Social Security wage base ( $168,000 in 2024) and 30% for taxpayers earning more than that—which means the lowest-income taxpayers will now pay more and some higher earners will pay less, and it would also lower the corporate income tax rate to 18%.
Federal Reserve: The project seeks to reform the Federal Reserve by “tak[ing] the monetary steering wheel out of [its] hands and return[ing] it to the people,” which the authors propose could be done by getting rid of the government’s control over the nation’s money entirely—instead leaving it up to banks—or returning to the gold standard, in which the dollar’s value would be tied to a specific weight of gold.
Foreign Relations: Project 2025 emphasizes opposing China, which it describes as “a totalitarian enemy of the United States,” and directs the U.S. to pull out of international organizations when they don’t serve the administration’s interests, including the World Health Organization and various United Nations agencies.
Healthcare: Project 2025 does not seek to overturn the Affordable Care Act, but would make significant cuts to Medicaid and impose work requirements to receive coverage, as well as reform Medicare—including by making Medicare Advantage, a paid supplement to Medicare, the default option for patients.
Get Forbes Breaking News Text Alerts: We’re launching text message alerts so you'll always know the biggest stories shaping the day’s headlines. Text “Alerts” to (201) 335-0739 or sign up here .
Is Trump Involved With Project 2025?
Trump has denied any connection to Project 2025, claiming on Truth Social last week that he has “nothing to do with them,” has “no idea” who’s behind the plan and finds some of its ideas “absolutely ridiculous and abysmal.” But many aren’t buying his claims: The team behind Project 2025 includes 140 people who worked for Trump in his administration, according to CNN , including six former Cabinet secretaries and four people he nominated as ambassadors. The ex-president has also seemingly endorsed the project in the past, saying at a 2022 dinner for the Heritage Foundation that the group was “going to lay the groundwork and detail plans for exactly what our movement will do … when the American people give us a colossal mandate.”
What Impact Could Project 2025’s Policies Have?
Experts have warned Project 2025’s proposals could have seismic impacts on how the federal government operates if carried out. In an article for Justia , criminal defense attorney and former prosecutor John May suggested Project 2025’s language endorsing the executive branch being able to “restrain the excesses” of the judicial branch and Congress means “if the President wants to, the President can defy any decision of the Supreme Court, any legislation by Congress, maybe even the act of impeachment and removal from office.”
Who’s Behind Project 2025?
The main team behind Project 2025 includes Heritage Foundation director Paul Gans and former Trump White House personnel leaders Spencer Chretien (who also served as Trump’s special assistant) and Troup Hemenway, according to the project’s website. Other groups listed as participating in the project include ex-Trump adviser Stephen Miller’s America First Legal, legal group Alliance Defending Freedom, Liberty University, Susan B. Anthony Pro-Life America and Turning Point USA. The 900-page policy agenda was co-authored by a series of conservative figures, with chapters penned by such Trump allies as former Housing Secretary Dr. Ben Carson, former Deputy Homeland Security Secretary Ken Cuccinelli, former HHS Civil Rights Director Roger Severino and former Trump advisor Peter Navarro, who went to prison in March for contempt of Congress.
Will Trump Have To Follow Project 2025’s Plans?
Trump will not be under any obligation to follow Project 2025’s proposals if he wins the presidency, though history suggests he’ll listen to at least some of them. The Heritage Foundation made a similar policy proposal for Trump ahead of his presidency in 2016, and boasted two years into his tenure that Trump had already followed 64% of its recommendations, CBS News notes .
Would Project 2025 Change Social Security?
One area that Project 2025 doesn’t touch on is Social Security benefits and any potential cuts to the program, even as proposals outline changes to numerous other government “entitlements.” Changing Social Security and making cuts to its spending has been a priority for the GOP for decades, though the American public has long opposed slashing benefits. Republicans’ efforts have waned under Trump, however, and the ex-president publicly claimed in March he “will never do anything that will jeopardize or hurt Social Security or Medicare,” after he came under fire for suggesting otherwise in an interview with CNBC.
Surprising Fact
While much of Project 2025’s policy agenda concerns federal agencies, the proposal has also gotten attention for its call to outlaw all pornography, which it claims is tied to “the omnipresent propagation of transgender ideology and sexualization of children” and is not protected under the First Amendment. Project 2025 calls not only for pornography to be made illegal, but also for anyone involved with its production and distribution to be imprisoned, for any librarians or educators who “purvey it” to be registered as sex offenders and for telecommunications and technology firms that facilitate its distribution to be shut down.
Key Background
The Heritage Foundation’s practice of laying out a policy roadmap for a future Republican administration actually dates back to the Reagan era, founder Edwin J. Feulner noted in the afterword of the 2025 edition. The organization first laid out a blueprint in 1981 that President Ronald Reagan ultimately adopted, fulfilling half of its recommendations by the end of his first year in office. The Heritage Foundation has continued to come out with blueprints for potential conservative presidents each election since, it notes, and its 2025 Mandate for Leadership was published in 2023. While it came out last year, Project 2025 gained new attention in the past week since Trump disavowed it—sparking a wave of reports highlighting his ties to the figures behind the project that debunk his claims. Democrats have also used the controversial proposal as a key talking point and argument for why the left should unite behind President Joe Biden and focus on defeating Trump, particularly as Biden’s candidacy has come under widespread scrutiny in the wake of the president’s poor debate performance in June.
Further Reading

- Editorial Standards
- Reprints & Permissions
Join The Conversation
One Community. Many Voices. Create a free account to share your thoughts.
Forbes Community Guidelines
Our community is about connecting people through open and thoughtful conversations. We want our readers to share their views and exchange ideas and facts in a safe space.
In order to do so, please follow the posting rules in our site's Terms of Service. We've summarized some of those key rules below. Simply put, keep it civil.
Your post will be rejected if we notice that it seems to contain:
- False or intentionally out-of-context or misleading information
- Insults, profanity, incoherent, obscene or inflammatory language or threats of any kind
- Attacks on the identity of other commenters or the article's author
- Content that otherwise violates our site's terms.
User accounts will be blocked if we notice or believe that users are engaged in:
- Continuous attempts to re-post comments that have been previously moderated/rejected
- Racist, sexist, homophobic or other discriminatory comments
- Attempts or tactics that put the site security at risk
- Actions that otherwise violate our site's terms.
So, how can you be a power user?
- Stay on topic and share your insights
- Feel free to be clear and thoughtful to get your point across
- ‘Like’ or ‘Dislike’ to show your point of view.
- Protect your community.
- Use the report tool to alert us when someone breaks the rules.
Thanks for reading our community guidelines. Please read the full list of posting rules found in our site's Terms of Service.
Nursing aide turned sniper: Thomas Crooks' mysterious plot to kill Trump

BUTLER, Pa. – Donald Trump and would-be assassin Thomas Crooks started on their violent collision course long before the former president's political rally ended in gunshots and death.
Crooks, 20, was a one-time registered Republican, a nursing home worker with no criminal record, shy in school, and living in a decent middle-class neighborhood in suburban Pennsylvania with his parents. Trump, 78, was eyeing Crooks' state as a key battleground – but not in the way that anyone envisioned on Saturday.
Riding high on polls showing that he's got a strong chance of toppling President Joe Biden, the former president had been campaigning for reelection in swing states, and Pennsylvania is a key prize. Trump won the state in 2016 but lost it four years later.
And on July 3, Trump's campaign announced he would hold a rally at the Butler Farm Show grounds, about 30 miles north of Pittsburgh.
"Pennsylvania has been ravaged by monumental surges in violent crime as a direct result of Biden’s and Democrats’ pro-criminal policies," Trump's campaign said in announcing the event, noting that when he's elected, he'll "re-establish law and order in Pennsylvania!"
The Saturday attack on Trump turned the heated rhetoric of the 2024 presidential campaign freshly violent. Authorities said bullets fired from Crooks' AR-15 style rifle about 150 yards away grazed Trump's ear, killed a rally attendee as he dove to protect his family, and critically wounded two others. Secret Service agents killed Crooks moments later.
Attack planned well in advance
Investigators are still seeking Crooks' motive – despite his Republican leanings, he had donated recently to a progressive voter-turnout campaign in 2021 – but indicated he'd planned the attack well in advance.
The shooting marks the first assassination attempt against a former or current U.S. president since President Ronald Reagan was injured in a March 1981 shooting at a Washington, D.C., hotel.
There are many questions about why Crooks turned into a would-be presidential assassin, firing indiscriminately into hordes of political supporters.
FBI special agent Kevin Rojek said on a call with media that law enforcement located "a suspicious device" when they searched Crooks' vehicle and that it's being analyzed at the FBI crime lab.
"As far as the actions of the shooter immediately prior to the event and any interaction that he may have had with law enforcement, we're still trying to flesh out those details now," Rojek said.
None of Crooks' shocked neighbors or high school classmates described him as violent or that he in any way signaled he was intent on harming Trump. Sunday morning, reporters and curious locals swarmed the leafy streets of the home where Crooks lived with his parents in Bethel Park, about 50 miles from the shooting scene.
Those who knew him described a quiet young man who often walked to work at a nearby nursing home. One classmate said he was bullied and often ate alone in high school.
Sunday morning, neighbor Cathy Caplan, 45, extended her morning walk about a quarter mile to glimpse what was happening outside Crooks’ home.“It came on the morning news and I was like ‘I know that street,’” said Caplan, who works for the local school district. "It feels like something out of a movie.”
Dietary aide turned deadly killer
Authorities say they are examining Crooks' phone, social media and online activity for motivation. They said he carried no identification and his body had to be identified via DNA and biometric confirmation.
Although no possible motive has yet been released, Crooks nevertheless embodies the achingly familiar profile of an American mass shooter: a young white man, isolated from peers and armed with a high-powered rifle. His attack was one of at least 59 shootings in the United States on Saturday, according to the Gun Violence Archive.
According to records and online posts of the ceremony, Crooks graduated from Bethel Park High School, about 42 miles from Butler County, on June 3, 2022. That same day, Trump met briefly with investigators at his Mar-a-Lago club in Florida as they examined whether he improperly took classified documents with him when he left the White House.
A classmate remembered Crooks as a frequent target of bullies. Kids picked on him for wearing camouflage to class and his quiet demeanor, Jason Kohler, 21, said. Crooks usually ate lunch alone, Kohler said.
Crooks worked as a dietary aide at the Bethel Park Skilled Nursing and Rehabilitation, less than a mile from his home. In a statement provided to USA TODAY on Sunday, Marcie Grimm, the facility's administrator, said she was "shocked and saddened to learn of his involvement."
Neighbor Dean Sierka, 52, has known Crooks and his parents for years. The families live a few doors apart on a winding suburban street, and Sierka’s daughter, who attended elementary, middle and high school with Crooks, remembers him as quiet and shy. Sierka said they saw Crooks at least once a week, often when he was walking to the nursing home from his parents' three-bedroom brick house.
"You wouldn’t have expected this," Sierka said. "The parents and the family are all really nice people."
"It's crazy," he added.
Secret Service role: Did they do enough?
Founded in 1865, the Secret Service is supposed to stop this kind of attack, and dozens of agents were present Saturday. As the former president and presumptive Republican presidential nominee, Trump's public appearances are managed by the Secret Service, which works with local law enforcement to develop security plans and crowd-management protocols.
In the days before the event, the agency's experts would have scouted the location, identified security vulnerabilities, and designed a perimeter to keep Trump and rally attendees safe. Congress and the Secret Service are now investigating how Crooks was able to get so close to the former president, and several witnesses reported seeing him in the area with the gun before Trump took the stage.
As the event doors opened at 1 p.m., the temperature was already pushing close to 90, and ticketed attendees oozed through metal detectors run by members of the Secret Service's uniformed division. Similar to airport security screenings, rallygoers emptied their pockets to prove they weren't carrying guns or other weapons.
Media reports indicate the Secret Service had in place, as usual, a counter-sniper team scanning the surrounding area for threats.
In an exclusive interview, former Secret Service Director Julia Pierson told USA TODAY that maintaining such a sniper security perimeter is part of the agency's responsibility for safeguarding protectees like Trump from harm. She said agents typically consider 1,000 yards to be the minimum safe distance for sniper attacks.
The Secret Service has confirmed that it is investigating how Crooks got so close to Trump, who took the stage shortly after 6 p.m. Officials say Crooks' rifle was legally obtained but have not yet released specifics.
Outside the venue at that time, Greg Smith says he tried desperately to get the attention of police. He told the BBC that he and his friends saw a man crawling along a roof overlooking the rally. Other witnesses said they also saw a man atop the American Glass Research building outside the official event security perimeter, well within the range of a 5.56 rifle bullet.
"We noticed the guy bear-crawling up the roof of the building beside us, 50 feet away from us," Smith told the BBC. "He had a rifle, we could clearly see him with a rifle."
Smith told the BBC that the Secret Service eventually saw him and his friends pointing at the man on the roof.
"I'm thinking to myself, why is Trump still speaking, why have they not pulled him off the stage?" Smith said. "Next thing you know, five shots rang out."
From his nearby deck, Trump supporter Pat English watched as the former president took the stage to Lee Greenwood's "God Bless the U.S.A.," and attendees raised their cell phones to record.
English had taken his grandson to see the rally earlier but left when it got too hot. From his deck, they listened as Trump began speaking at 6:05 p.m., backed by a crown of red-hatted MAGA supporters waving "fire Joe Biden" signs.
And then gunfire began.
Boom, boom, boom
"I heard a 'boom, boom, boom' and then screams,” English said Sunday. "I could see people running and the police run in."
Trump was saying the word "happened" as the first pop rang out. He reached up to grab his ear as two more shots echoed, and the crowd behind him – and Trump himself – ducked. Plainclothes Secret Service agents piled atop the president as a fusillade of shots rang out, apparently the Secret Service killing Crooks.
The crowd screamed, and the venue's sound system picked up the agents atop Trump planning to move the former president to safety. One yelled, "shooter's down. Let's move, let's move."
The agents then helped Trump back to his feet as they shielded him on all sides.
The sound system then picked up Trump's voice: "Wait, wait," he said, before turning to the audience and triumphantly raising his fist to yell "fight, fight" as the crowd cheered, blood streaming down his face.
By 6:14 p.m. Trump's motorcade was racing from the scene, and in a later statement, Trump's campaign said he was checked out at a local medical facility.
"I was shot with a bullet that pierced the upper part of my right ear," Trump said in a statement. "I knew immediately that something was wrong in that I heard a whizzing sound, shots, and immediately felt the bullet ripping through the skin. Much bleeding took place, so I realized then what was happening."
Firefighter 'hero' gunned down
Outside of the Butler Township Administration Office Sunday afternoon, Pennsylvania Gov. Josh Shapiro identified the rally attendee killed by Crooks as Corey Comperatore, a firefighter, father of two and longtime Trump supporter.
“Corey died a hero,” Shapiro said. “Corey dove on his family to protect them last night at this rally. Corey was the very best of us. May his memory be a blessing.”
Two other Pennsylvanians are still undergoing treatment for their injuries, Shapiro said.
Pennsylvania State Police identified two wounded attendees David Dutch, 57, of New Kensington, and James Copenhaver, 74, of Moon Township. Both are hospitalized and listed in stable condition. Shapiro said he spoke with the family of one victim and received a message from the other.
Biden spoke briefly with Trump on Saturday night, and the president condemned the assassination attempt as “sick.” He said there’s no place for political violence in the U.S. and called on Americans to unite together to condemn it.
But earlier in the week, Biden told campaign donors in a private phone call it was time to stop talking about his own disastrous presidential debate performance and start targeting Trump instead.
"I have one job and that's to beat Donald Trump," Biden said. "We're done talking about the (June 27) debate. It's time to put Trump in the bullseye."
Republicans across the country have used similar language to attack their opponents over the years, and political scientists say violent rhetoric used worldwide almost invariably leads to physical violence.
On Sunday, someone parked a truck-mounted electronic billboard at the gates to the Butler Farm Show grounds reading "Democrats attempted assassination," along with a picture of Trump clutching an American flag, his face overlaid with a bullseye crosshairs.
Authorities say they have not yet determined a motive for Crooks' attack. But in a statement, Trump declared the shooting an act of evil and thanked God for preventing the unthinkable.
"We will fear not, but instead remain resilient in our faith and defiant in the face of wickedness," Trump said.
And he said he'd be back on the campaign trail for the Republican National Convention in Milwaukee, which starts Monday.
"Based on yesterday’s terrible events, I was going to delay my trip to Wisconsin, and the Republican National Convention, by two days," Trump said on his Truth Social account Sunday, "but have just decided that I cannot allow a 'shooter,' or potential assassin, to force change to scheduling, or anything else."
Contributing: David Jackson, Aysha Bagchi, Christopher Cann, Bryce Buyakie, Emily Le Coz, Josh Meyer, USA TODAY Network
How the assassination attempt unfolded : Graphics, maps, audio analysis show what happened

IMAGES
VIDEO
COMMENTS
Cyber-attacks are still rising, and more are waiting to harm their targeted systems and networks. Detecting Intrusions in cybersecurity has become challenging due to their Intelligence Performance. Therefore, it may negatively affect data integrity, privacy, availability, and security. ... A. Exciting Mobile Cyber Security Research Paper Topics ...
In addition, five scenarios can be considered for cyber warfare: (1) Government-sponsored cyber espionage to gather information to plan future cyber-attacks, (2) a cyber-attack aimed at laying the groundwork for any unrest and popular uprising, (3) Cyber-attack aimed at disabling equipment and facilitating physical aggression, (4) Cyber-attack as a complement to physical aggression, and (5 ...
In this blog post, we will explore some of the most pressing cybersecurity research topics, from the latest trends in cyber attacks to emerging technologies that can help prevent them. Whether you are a cybersecurity professional, a Master's or Ph.D. student, or simply interested in the field, this post will provide valuable insights into the ...
Cybercrime is estimated to have cost the global economy just under USD 1 trillion in 2020, indicating an increase of more than 50% since 2018. With the average cyber insurance claim rising from USD 145,000 in 2019 to USD 359,000 in 2020, there is a growing necessity for better cyber information sources, standardised databases, mandatory reporting and public awareness. This research analyses ...
Check out our free technology courses to get an edge over the competition.. 75 Cyber Security Research Topics in 2024. Here are some of the latest research topics in cyber security - . Emerging Cyber Threats and Vulnerabilities in 2024. Continual technological advancements lead to changes in cybersecurity trends, with data breaches, ransomware, and hacks becoming more prevalent.
Traditionally, cyber-attack detection relies on reactive, assistive techniques, where pattern-matching algorithms help human experts to scan system logs and network traffic for known virus or ...
There has been a tremendous increase in research in the area of cyber security to support cyber applications and to avoid key security threats faced by these applications.
In the current paper, we aim to add to this emerging body of research by examining the topic of cybersecurity preferences in the aftermath of lethal and nonlethal cyberattacks. ... six months and three years for authorities and private actors to publicly reveal the actors behind the 2017 WannaCry attacks, the 2016 cyber intrusion into the ...
The outcome of this segment is broken down into six stages of the cybersecurity kill chain, which include reconnaissance (AI-targeted attack), access and penetration (AI-aided attack), delivery (AI-concealment attack), exploitation (AI-automated malware), command on control (AI-multi-layered attack), action on objectives (AI-massive attack).
If you're just starting out exploring cybersecurity-related topics for your dissertation, thesis or research project, you've come to the right place. In this post, we'll help kickstart your research by providing a hearty list of cybersecurity-related research topics and ideas, including examples from recent studies.. PS - This is just the start…
Cyber attacks are increasing rapidly due to advanced digital technologies used by hackers. In addition, cybercriminals are conducting cyber attacks, making cyber security a rapidly growing field. ... including the potential research topics to improve several DL methodologies for cybersecurity applications. ... The remaining paper is structured ...
Cyber security safeguards the data and integrity of computing assets that are part of or connected to an organization's network, with the goal of defending such assets from all threat actors ...
By educating others about the dangers of cyber attacks and the importance of protecting their computers, you can help make the internet a safer place for everyone. ... When it comes to choosing research paper topics on cyber security, there are a few things to consider. First, it is important to make sure that the topic is relevant and timely ...
In this study, an overview of the concept of cyber security has been presented. The paper first explains what cyber space and cyber security is. Then the costs and impact of cyber security are discussed. ... Then a few common cyber-attacks and the ways to protect from them are specified. At last, a famous case study of Mirai's attack on a few ...
Cybersecurity Research Paper Topics. Cybersecurity is wide and inexhaustible. Each day, cybercrime are occurring, leading to research on better ways to protect ourselves online. You can use any of these topics for your research paper or project. The advantages and disadvantages of unified user profiles. The relation between bots and cybersecurity.
Cyber Research Papers Cyber Security Research Papers. Master's degree candidates at SANS.edu conduct research that is relevant, has real world impact, and often provides cutting-edge advancements to the field of cybersecurity, all under the guidance and review of our world-class instructors.
However, the multi-interfaces in smart grid may exploit by persons or agencies to implement different types of cyber-attacks may lead to dangerous damage. This research paper reviews the up-to-date researches in the field of smart grid to handle the new trends and topics in one frame in order to offer integration vision in this vital section.
Cybersecurity Research Paper Topics . What are zero-day vulnerabilities and how do they affect cybersecurity? ... computer systems, and data against cyber-attacks is an issue in advanced technology. It is a complicated and wide-ranging subject with many excellent study areas and subjects to choose from. What is the #1 cybersecurity threat today
Research Paper on Cyber Security. June 2021 ... alternative to generate a reliable defense before or after cyber-attacks ... from leading experts in Cyber Security and many other scientific topics.
What You Need To Know About Cyber Security Research Topics. A cybersecurity paper deals with the practices of protecting servers, electronic systems, computers, and networks from malicious attacks. Although most students think this only applies to computers, it also applies to mobile computing and other business models.
Get More Cybersecurity Research Topics. In this blog, we have covered the 111+ best cybersecurity research topics. These cybersecurity topics help in your exam or test. If you have any difficulty with cybersecurity research topics, you can take cybersecurity research paper help or research paper assignment help at a very affordable price.
Software and Computer Administration Cyber Security Topics. The cyber security of a company can be compromised in many ways when it comes to software and computer administration. As such, software and computer administration is a great sources of cybersecurity research paper topics. Here are some of the best topics in this category.
Get the Latest cyber security research topics in 2023 . Cyber Threat Intelligence . Security of Software Development . ... Our professionals have created a well-researched and interesting list of cyber security research paper topics with aims and objectives. ... To design the system for the detection of threat or cyber-attack to prevent it from ...
Cybersecurity experts and the companies that employ need to let go of their prevention mindset and adopt one focused on resilience. A prevention mindset means doing all you can to keep the bad ...
This paper proposes a new algorithm called ... A comprehensive review study of cyber-attacks and cyber security; emerging trends and recent developments, Energy Rep 7 (2021) 8176-8186. Google Scholar ... Ai-driven cybersecurity: An overview, security intelligence modeling and research directions, SN Comput Sci 2 (2021) 1-18. Google Scholar
Against the background of the construction of new power systems, power generation, transmission, distribution, and dispatching services are open to the outside world for interaction, and the accessibility of attack paths has been significantly enhanced. We are facing cyber-physical cross-domain attacks with the characteristics of strong targeting, high concealment, and cross-space threats ...
Check Point Research (CPR) releases new data on Q2 2024 cyber attack trends. The data is segmented by global volume, industry and geography. These cyber attack numbers were driven by a variety of reasons, ranging from the continued increase in digital transformation and the growing sophistication of cybercriminals using advanced techniques like AI and machine learning.
Project 2025 would severely restrict abortion pills, abolish federal agencies, block climate change research, end student loan forgiveness and more.
The Saturday attack on Trump turned the heated rhetoric of the 2024 presidential campaign freshly violent. Authorities said bullets fired from Crooks' AR-15 style rifle about 150 yards away grazed ...